They already proved it once.
The next system still says do it again.
I keep coming back to that on Midnight network... it’s such a stupidly normal user request and the system still turns it into homework.
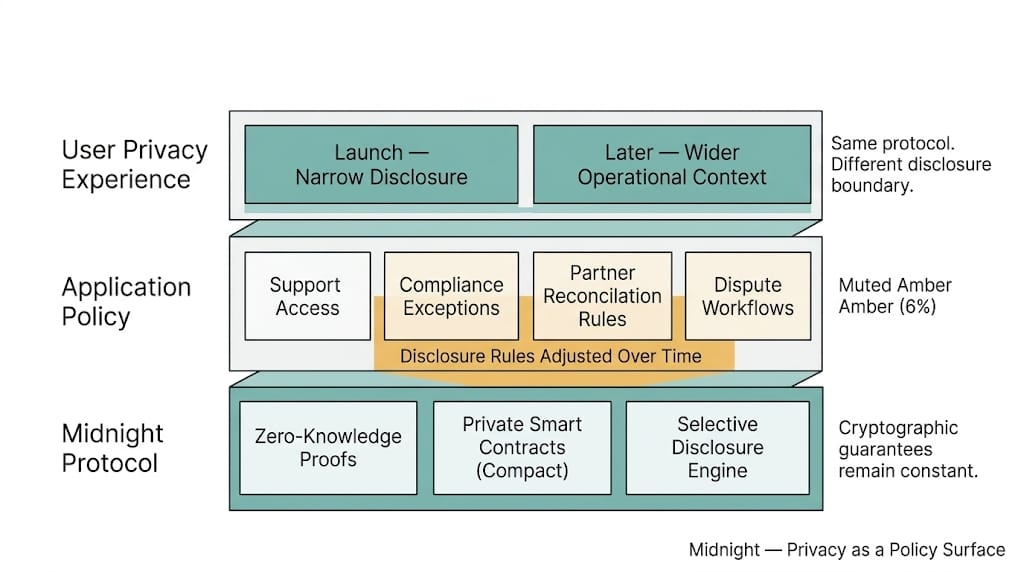
Midnight looks clean while the whole relationship stays inside the same app, the same rules, the same disclosure model, the same people pretending the boundaries were obvious all along. User proves what they need to prove. Sensitive data stays tucked away. Access opens. Credit clears. Some internal threshold gets met and nobody has to dump the whole file onto a public chain like a lunatic. Good. That part is real.
Then the user wants to move.
Not leave crypto. Just move.
Take a private onboarding or lending flow on Midnight. Someone proved eligibility. Maybe residency bucket. Maybe income band. Maybe some internal risk tier. Maybe a counterparty condition nobody wanted sitting in public forever. Fine. The app accepted it. The relationship exists now. Limit approved. Access granted. Account active.
Good there.
Then six weeks later the user wants to use that same standing somewhere else.
Another venue. Another lender. Another partner. Different product. Maybe they just want the next system to recognize that they already did the hard boring part once. Very unreasonable of them, apparently.
And thats where Midnight $NIGHT stops looking simple.
Midnight's Private state is easy to admire while it stays exactly where it was born. Same reveal paths. Same operators. Same assumptions about who can see what and why. Portability ruins that comfort fast. The second the user wants to export, reuse, verify elsewhere, or carry some piece of that private credibility into another system, you find out how much of the privacy model was local custom dressed up like infrastructure.
The user shows up with private standing and still gets treated like a stranger.
Thats the split.
The user thinks: I already proved this.
The second system thinks: prove it again.
The first system thinks: we can attest to it, sort of.
And now everybody is standing around a sealed relationship trying to figure out how much of it can travel without ripping the privacy boundary open in the process.
Midnight is strong inside the original workflow. Thats not the problem. Selective disclosure works when the surrounding app knows what it asked for, what it received, what its own reveal paths look like, what its own exception rules are. Nice controlled room. Very civilized.
The second the state needs to leave that room, though, the hidden thing gets awkward.
Can the user export a proof of standing without exporting the hidden logic behind it?
Can another system trust the result without trusting the first app’s whole policy stack?
Can some private score, tier, or credential be reused elsewhere without turning into a messy screenshot with better branding?
Can the second venue tell the difference between “this was valid there” and “this should be accepted here”?
That last one is where the whole thing starts costing the user again.
Because the second system is not just importing data. It’s importing somebody else’s rules, somebody else’s revocation logic, somebody else’s freshness assumptions, somebody else’s risk posture. That is where it gets sticky.
The proof can move.
The trust model usually doesn't.
Same scoped proof. Different reveal path. Different liability. Back to zero.
And that is a very Midnight problem.
A scoped proof on @MidnightNetwork that was good enough for the first app may not be carrying the refresh logic, revocation path, challenge rights, or liability structure the second app is willing to inherit. So the user gets dragged back into repetition.
Another form.
Another review.
Another wait.
Very portable. Just not for the user.
Great. The private standing exists. The portability mostly doesn’t.
And institutions are worse here, not better. Because the first partner might say the relationship is valid under its private rules. The next partner says sure, but validity there is not the same thing as reliance here. Who owns the stale claim if the status changes later? Who updates it? Who revokes it? Who tells the receiving system that the nice clean proof being carried over is already older than it looks?
Nobody wants to import someone else’s private certainty for free.
Thats not exactly privacy failing. It is the user getting pushed back into repetition while everybody still insists the privacy model worked.
Which, technically, maybe it did.
The privacy holds. The handoff doesn’t. The user still pays for it.
And if Midnight gets real adoption, this is going to matter a lot more than people think. Nobody wants private state for the romance of having private state. They want it to be usable. Reusable. Movable. They want the relationship they built in one place to count somewhere else without starting life over every time they touch a new app like some bureaucratic groundhog day.
That’s where the nice version starts falling apart a bit.
Not when the user proves something once.
When they ask, pretty reasonably, whether that private standing can travel without turning into either useless sealed context or a bigger disclosure event than the original system ever needed.
I keep coming back to that... its such a normal user instinct and such an awkward systems problem. Midnight can keep sensitive state private inside the room it was designed for.
Alright.
The harder question is what happens when the user wants to carry that state out of the room and the privacy model suddenly has to survive contact with another system’s rules, another partner’s liability, another operator’s trust threshold, another set of reveal paths nobody bothered aligning ahead of time. Confused?...
Then "private" is not the only question anymore.
Then itss...portable for whom,
portable under whose rules,
and portable how, exactly, without the user paying for it by slowly reopening the very thing they were told had finally been protected.

