Dock (DOCK) — Detailed Breakdown
What is this project about
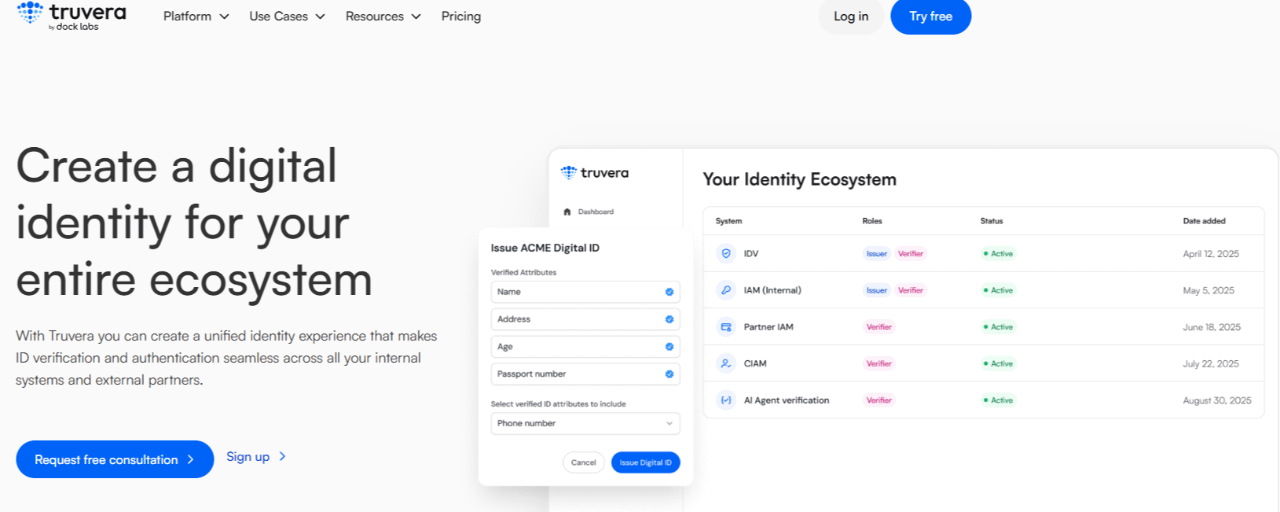
Dock is an infrastructure for digital identity (Web3 ID).
The core idea:
Replace paper-based and centralized documents with cryptographically verifiable data that the user fully controls.
Examples:
- diplomas
- certificates
- KYC / identity verification
- work experience
All of this can exist as verifiable credentials (VCs).
How it works (simple explanation)
There are 3 roles:
1. Issuer — e.g., a university or company
2. Holder — you
3. Verifier — employer or service
Process:
- A university issues you a digital diploma
- You store it yourself (not on a company’s server)
- An employer verifies its authenticity via blockchain
No intermediaries, no forgery
Dock Technology
Dock uses:
- Decentralized Identifiers (DID)
- Verifiable Credentials (VC)
- Blockchain for verification, not data storage
Important:
The actual data is not stored on-chain — only proofs of authenticity are.
DOCK Token — What is it used for
The DOCK token serves several purposes:
Payments:
- creating DIDs
- issuing credentials
- network transactions
Staking:
- validators secure the network
- earn rewards
Governance:
- participation in protocol decisions
Architecture (important point)
Initially:
DOCK was an ERC-20 token on Ethereum
Later:
migrated to its own blockchain (built with Substrate, similar to Polkadot)
This reduced fees and improved network flexibility
Use Cases
- education (diplomas)
- HR & recruiting
- healthcare (professional certifications)
- KYC/AML
- Web3 authentication
Pros and Cons
Pros:
- real use case (not a meme coin)
- growing Web3 identity trend
- strong focus on privacy and data ownership
Cons:
- weak marketing
- low hype → limited demand
- strong competition
- adoption still limited
Why the price isn’t skyrocketing
Dock is infrastructure, not a speculative hype asset.
Projects like this:
- grow slowly
- depend on adoption, not hype
- can stay stagnant for long periods
Conclusion
Dock (DOCK) is a project focused on the future of digital identity:
You own your data and decide who gets access to it.
This is a long-term play, not a quick “moonshot.”