The moment that made me rethink the limits of public blockchains was surprisingly ordinary.
I was looking at a transaction on a blockchain explorer. Within seconds, I could see not only the transaction itself but the entire activity history of the wallet involved previous transfers, contract interactions, token balances, and timing patterns. Anyone else could open the same explorer and see exactly the same information.
In the early years of cryptocurrency, this level of transparency was considered a breakthrough. Public blockchains replaced trust in institutions with trust in open verification. Instead of relying on a central authority, anyone could independently verify what happened on the network.
But the longer I study blockchain infrastructure, the more a tension becomes visible.
Transparency is powerful for trust. Yet it becomes problematic when blockchain begins interacting with real-world systems that depend on confidentiality.
A financial institution cannot publicly reveal internal settlement flows. A hospital cannot expose patient information. A company cannot publish every detail of its supply chain contracts.
In other words, the same transparency that gave early blockchains their credibility can become a structural limitation once those systems attempt to operate in sensitive environments.
That tension is what led me to examine Midnight Network, a privacy-focused system being developed within the broader Cardano ecosystem.
Rather than rejecting transparency entirely, Midnight appears to explore a different idea: what if blockchains could verify truth without exposing the underlying data?
The Privacy Gap in Traditional Blockchains
Most public blockchains follow a simple design philosophy. Every transaction is recorded on a shared ledger that anyone can inspect. This transparency ensures that no participant can secretly alter the system’s history.
For basic financial transfers, this model works extremely well.
However, when more complex applications appear identity systems, enterprise contracts, healthcare data flows the design begins to reveal limitations.
If every piece of data involved in a transaction must appear on-chain, then organizations are forced to choose between using blockchain and protecting sensitive information. In many cases, they simply avoid using blockchain altogether.
This is the privacy gap that many researchers have begun focusing on in recent years.
The question becomes: can we maintain the verification power of blockchains while limiting what information becomes public?
Midnight is one of the attempts to answer that question.
How Programmable Privacy Works
The central concept behind Midnight is something often called programmable privacy.
Instead of forcing all transaction data onto a public ledger, developers can decide which information should remain private and which elements should be visible for verification.
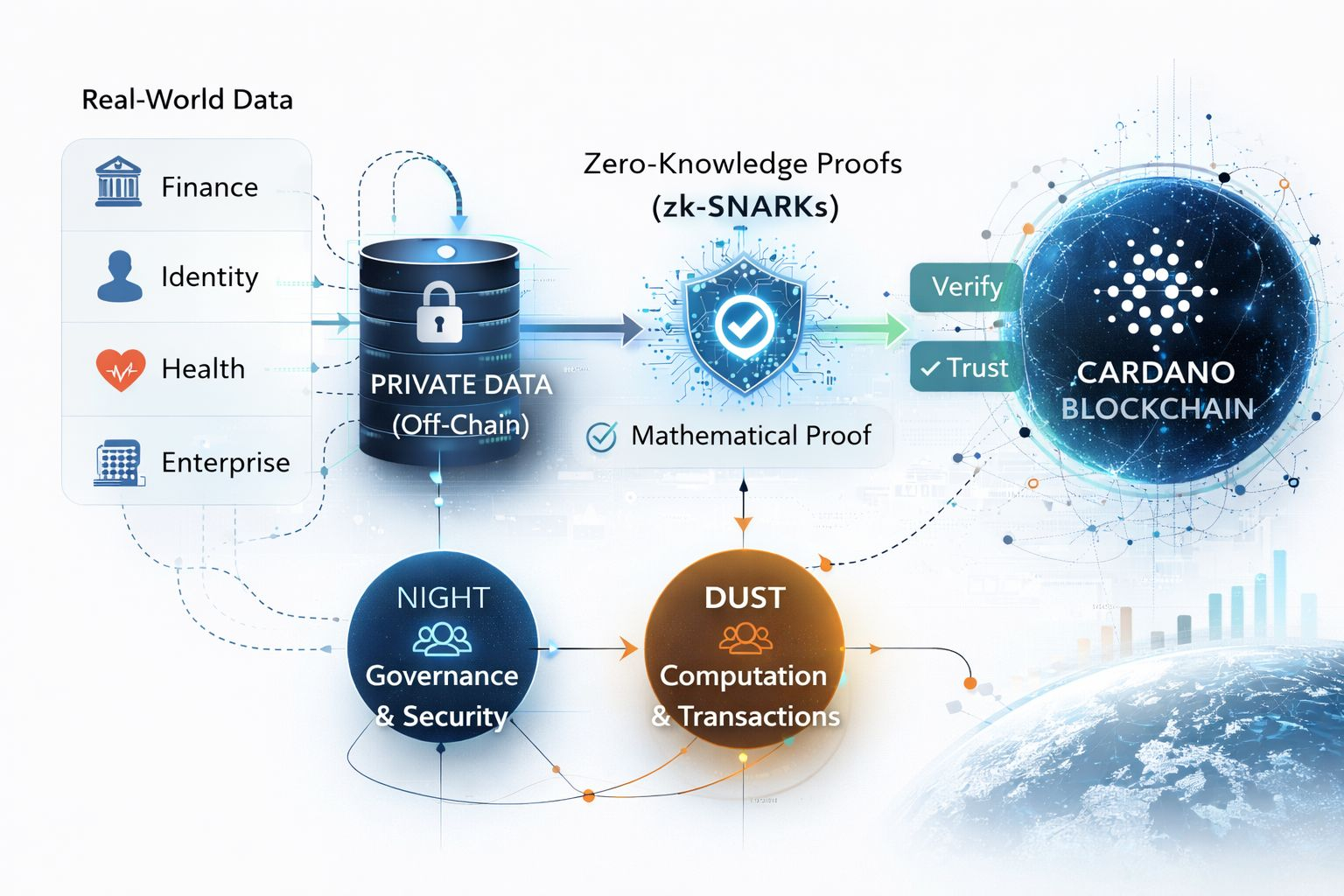
This approach relies heavily on cryptographic techniques known as zero-knowledge proofs, particularly forms like zk-SNARKs.
The idea behind zero-knowledge proofs is subtle but powerful. A system can demonstrate that a statement is correct without revealing the information used to produce that statement.
For example, imagine proving that a person is over a required age limit without revealing their exact birthdate. Or confirming that a company meets certain regulatory conditions without exposing the internal data used to reach that conclusion.
In Midnight’s architecture, sensitive data stays off-chain. Instead of publishing raw information to the blockchain, the system submits a mathematical proof showing that the rules governing that data were satisfied.
The blockchain verifies the proof, not the data itself.
This small shift changes how the system functions. The blockchain becomes less like a transparent database and more like a cryptographic verification layer.
A Different Kind of Blockchain Architecture
Traditional blockchains store both data and transaction logic directly on-chain. Everything needed to verify a transaction must be visible to the network.
Midnight introduces a different architectural pattern.
The computation can occur privately, using confidential inputs. Once that computation finishes, the system generates a proof showing that the correct rules were followed. The blockchain only records and verifies this proof.
In other words, the network confirms that something happened correctly, without needing to see how it happened internally.
From a research perspective, this represents a shift in how blockchains can be designed. Rather than assuming maximum transparency, the system assumes selective disclosure.
Some information remains private by default, while only the verification layer becomes public.
The Logic Behind the Dual-Token System
Another element of Midnight that stood out during my research is its two-token economic model.
The network separates responsibilities between NIGHT and DUST, each serving a distinct role.
The NIGHT token acts as the governance and security component of the network. It allows participants to influence protocol decisions and participate in the broader operation of the system.
The second token, DUST, is used to pay for computation and transaction execution.
At first glance, this might resemble other multi-token designs in the crypto space. But in Midnight’s case, the separation appears to serve a deeper purpose.
By isolating the token used for governance from the token used for transaction execution, the system reduces the possibility that transactional activity could expose patterns tied directly to governance participants.
In other words, the economic layer itself becomes more privacy-aware.
This may seem like a small design decision, but it reflects a broader principle running through Midnight’s architecture: privacy should not only exist at the data layer, but throughout the system.
Potential Real-World Applications
If this type of privacy-preserving architecture works at scale, the range of possible applications expands significantly.
Financial institutions could execute contracts on-chain without revealing internal trade details. Identity systems could verify attributes without exposing full identity records. Healthcare infrastructure could prove compliance with protocols without exposing medical data.
Enterprise systems could automate agreements while keeping proprietary information confidential.
These kinds of applications are difficult to implement on traditional transparent blockchains because sensitive data would inevitably become public.
Midnight attempts to remove that barrier.
Midnight’s Role in the Cardano Ecosystem
From a strategic standpoint, Midnight appears to complement the broader goals of the Cardano ecosystem.
Cardano has long emphasized careful research and formal system design. Midnight extends that philosophy into privacy infrastructure.
Instead of replacing existing blockchain functionality, it adds a new layer focused on confidential computation.
Public transactions can still occur in open environments, while applications requiring stronger privacy guarantees can operate within Midnight’s framework.
This layered approach suggests a more flexible blockchain ecosystem one where transparency and confidentiality can coexist depending on the needs of the application.
A Question About the Future of Blockchain Privacy
Studying Midnight left me with a broader question about the direction of blockchain technology.
Transparency helped blockchain establish credibility in its early years. But large-scale adoption may require a different balance between openness and confidentiality.
If organizations cannot protect sensitive information, they simply will not move critical systems onto public infrastructure.
That raises an interesting possibility.
Projects like Midnight may not just be technical experiments. They could represent the type of privacy infrastructure needed for blockchain to move beyond purely financial use cases.
The real question is whether systems like this will remain specialized tools or whether privacy-preserving networks will become one of the key foundations that allow blockchain to integrate with real-world institutions.