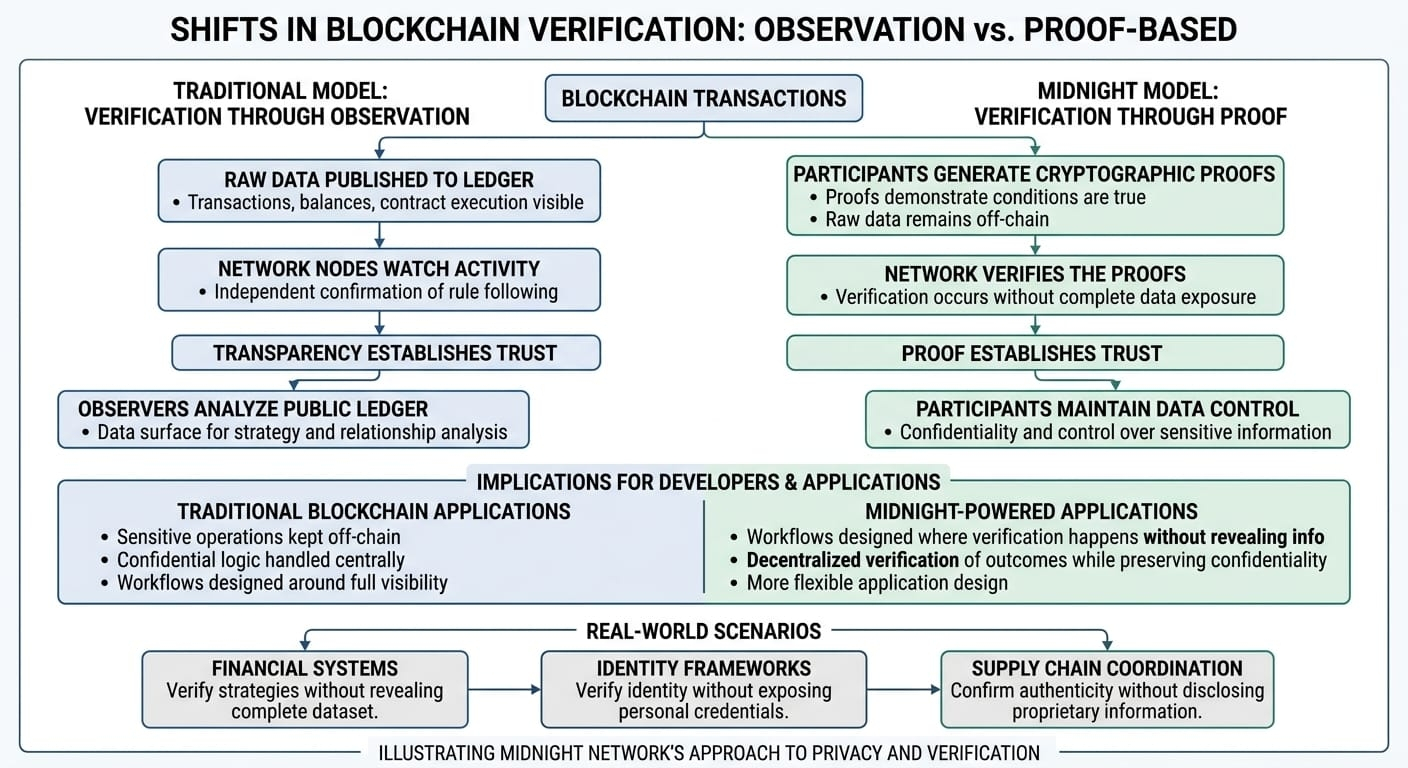
For most of blockchain’s history, verification has depended on observation.
The system works because anyone can watch it.
Transactions move across the ledger, balances change, contracts execute, and the entire process remains visible to anyone running a node or inspecting a block explorer. The network does not ask participants to trust hidden processes because everything necessary to verify the system is available in plain view.
That transparency solved one of the most important coordination problems in distributed systems.
If everyone can see the same ledger, everyone can independently confirm that the rules are being followed.
But over time another pattern has become harder to ignore.
Observation solves verification, yet it also changes how participants interact with the system.
Once activity becomes permanently observable, the ledger turns into more than a verification tool. It becomes a data surface where strategies, relationships, and patterns can be studied by anyone willing to analyze it.
In open financial experiments that level of visibility can be valuable. But in environments where coordination involves sensitive information, constant observation can discourage participation.
This is the tension Midnight Network appears to be examining.
Instead of asking participants to reveal everything so the network can verify correctness, Midnight explores an architecture where verification can occur without requiring complete observation of the underlying data.
The system still confirms that rules were followed. What changes is how much information must become publicly visible in order for that confirmation to happen.
This approach relies on a different mechanism for establishing trust.
Rather than asking observers to examine the raw data directly, participants generate cryptographic proofs demonstrating that certain conditions are true. The network verifies the proof itself, allowing the system to confirm correctness without exposing the underlying dataset.
At first glance this might sound like a purely technical improvement.
In practice, it changes how decentralized coordination works.
Most blockchain applications today assume that anything written to the ledger becomes visible forever. Developers design systems with that assumption in mind. Sensitive operations remain off-chain. Confidential logic is handled by centralized components. Entire workflows are built around the fact that the blockchain environment itself cannot protect internal data.
Midnight experiments with a different environment.
If the network can validate outcomes without requiring full observation, developers gain more flexibility in how systems are designed. Applications can still rely on decentralized verification while allowing participants to control which information becomes part of the public record.
This opens the door to a different kind of interaction with blockchain infrastructure.
Participants can demonstrate that they followed shared rules without revealing every operational detail behind those actions. The network remains verifiable, but the path to that verification changes.
Instead of visibility creating trust, proof becomes the mechanism that produces trust.
That shift becomes increasingly relevant as decentralized systems expand into more complex coordination environments.
Financial systems often involve strategies participants prefer not to reveal. Identity frameworks require verification without exposing personal credentials. Supply chain coordination may depend on confirming authenticity without disclosing proprietary information.
In all of these cases, participants need the system to verify outcomes without forcing them to expose the entire dataset behind those outcomes.
Midnight’s architecture appears designed around exactly this challenge.
Rather than treating privacy as an optional layer applied after the fact, the network integrates proof-based verification into the structure of how interactions occur. The system validates conditions without requiring every detail to become part of the shared ledger.
For developers, this changes the design boundaries of decentralized applications.
Instead of deciding which parts of a system must remain off-chain to protect confidentiality, developers can begin designing workflows where verification itself happens without revealing unnecessary information.
Applications can coordinate around shared rules while preserving control over sensitive data.
Of course, implementing this model introduces its own set of challenges.
Proof-based systems require sophisticated cryptographic infrastructure. Verification mechanisms must remain efficient enough to support real workloads. Developer tools must translate complex mathematics into usable application frameworks.
Infrastructure projects often succeed not because their ideas are novel, but because their tools become practical for builders.
For Midnight, the long-term question will likely revolve around adoption.
If developers find the network’s privacy architecture accessible and useful, applications will begin appearing that depend on these capabilities. Over time those applications become the real signal that the infrastructure is solving meaningful problems.
If adoption remains limited, the ideas may remain technically interesting but operationally narrow.
But the problem Midnight is exploring is unlikely to disappear.
As decentralized systems evolve, the challenge will not only be verifying that rules were followed.
It will also be deciding how much observation is actually necessary for that verification to occur.
Midnight represents one attempt to answer that question.
And if decentralized infrastructure continues moving toward more complex forms of coordination, the ability to verify outcomes without constant observation may become one of the defining design principles of the next generation of blockchain networks.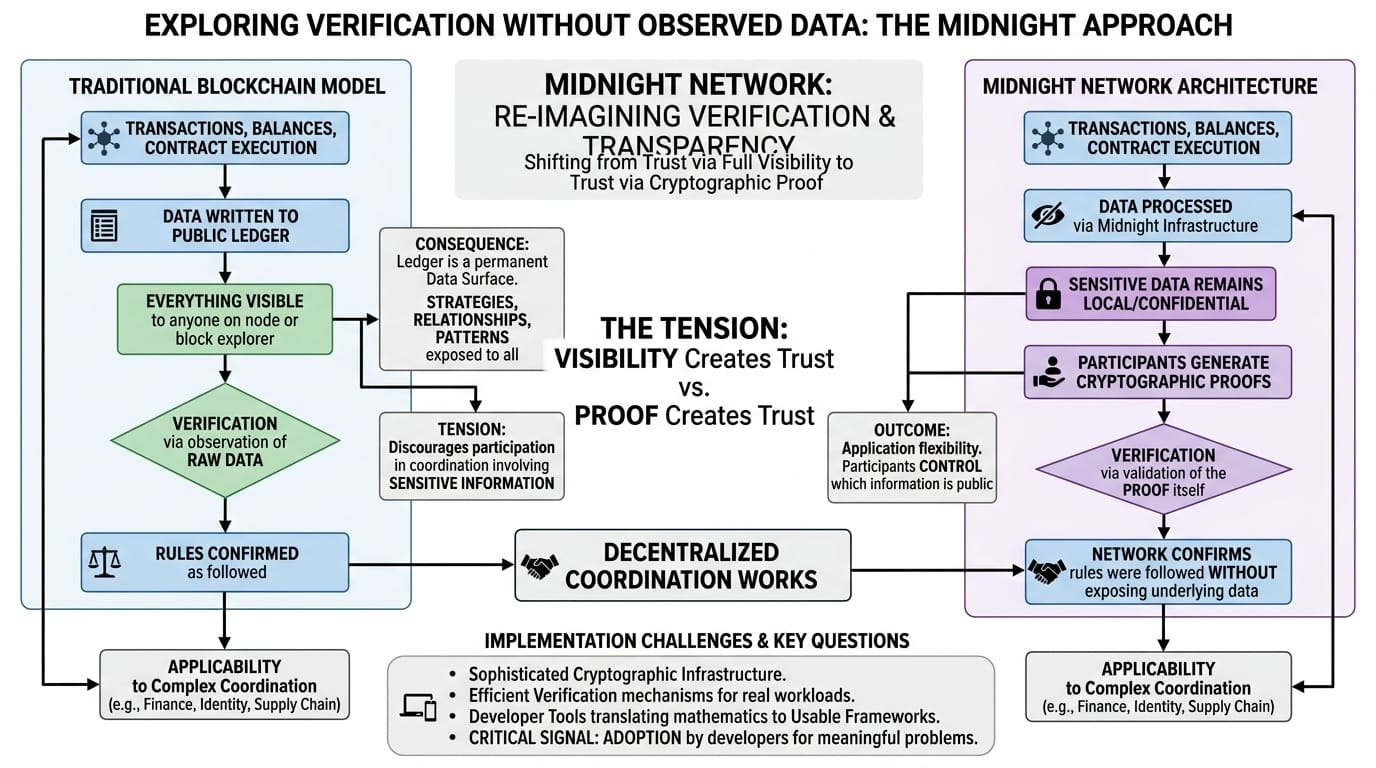
#night $NIGHT @MidnightNetwork #KATBinancePre-TGE #UseAIforCryptoTrading #AIBinance