I have been thinking about KYC more than I expected. Not because it is exciting, but because it is everywhere. Every exchange. Every fintech app. Every onboarding flow. The process is always similar: upload documents, wait for verification, repeat the same steps on the next platform. It feels inefficient and oddly outdated for a digital system that claims to be decentralized. That frustration is what made me look more closely at how Sign Protocol approaches identity verification. At first, the idea sounds simple. Instead of repeating KYC across multiple platforms, a user could complete verification once and carry that proof with them. Different services could check the proof rather than request the same documents again.
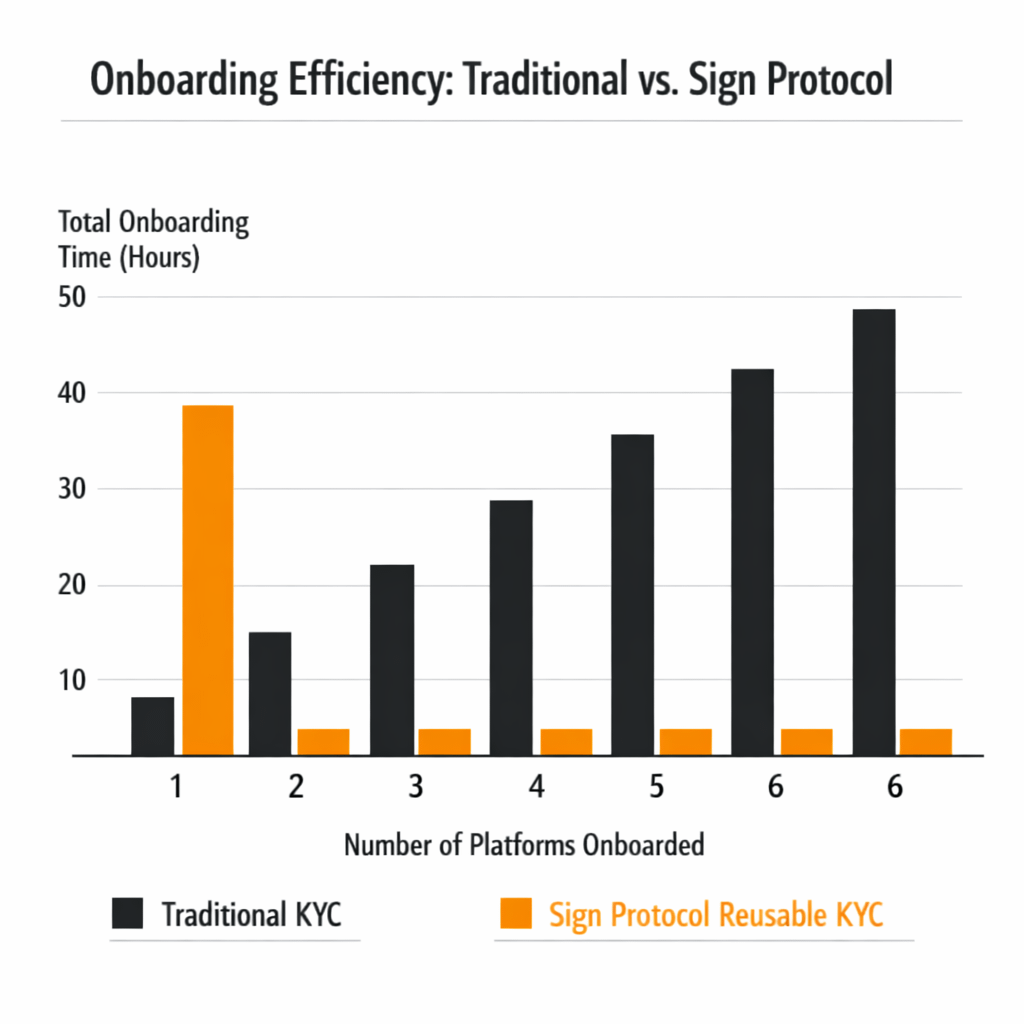
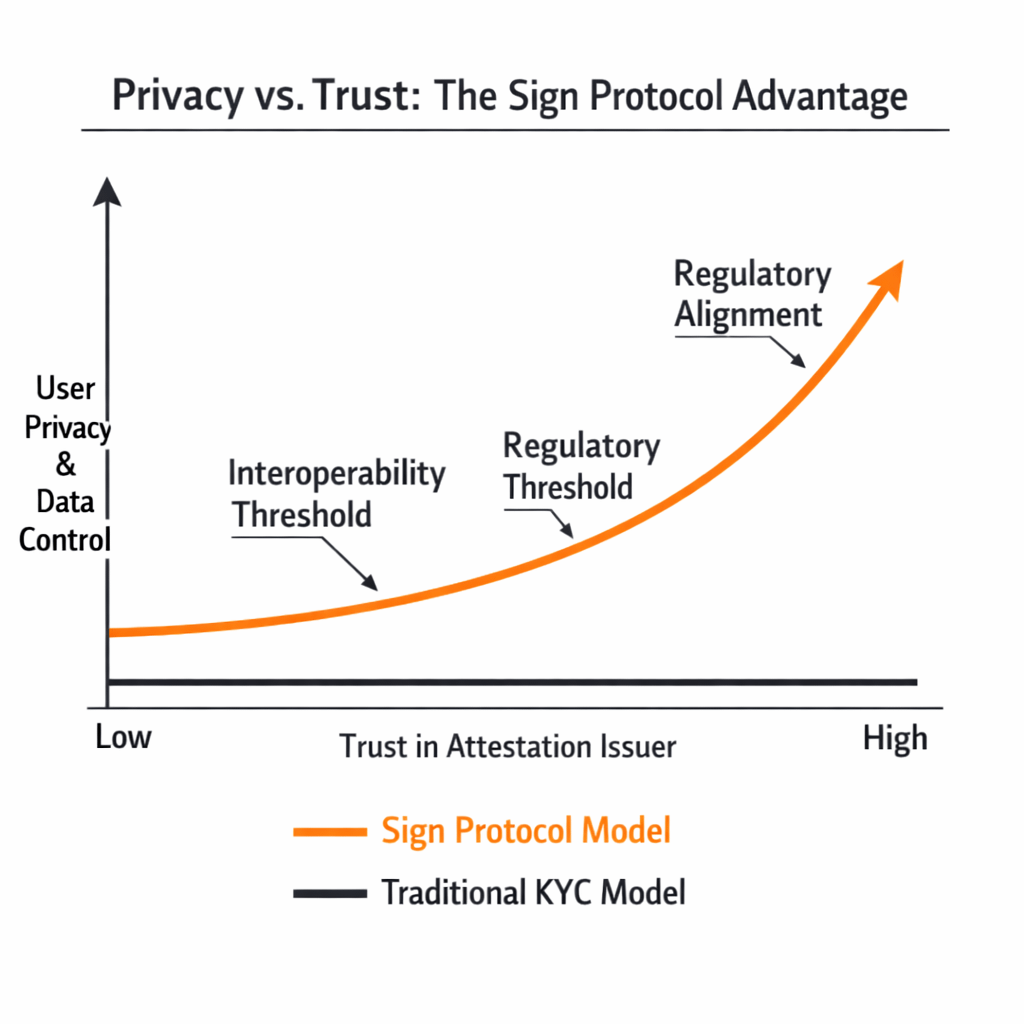
In theory, this would reduce friction and improve user experience. But the moment I think about it more carefully, the complexity becomes clear. KYC is not just a technical process; it is tied to regulation compliance and institutional responsibility. Platforms are required to verify users under specific rules. They cannot simply accept any external proof without trusting the issuer and ensuring it meets regulatory standards. This is where Sign Protocol starts to position itself differently. It focuses on attestations structured claims that can be issued by trusted entities. A verified KYC provider could issue an attestation confirming that a user has passed the required checks. Other platforms could then verify that attestation without accessing the underlying personal data. From my perspective, this introduces an interesting shift. The system separates verification from data exposure. Instead of sharing documents repeatedly, a user shares proof that verification has already happened. Sensitive information remains with the issuer while the network confirms that the requirements were met. In theory, this could make KYC both more efficient and more private.
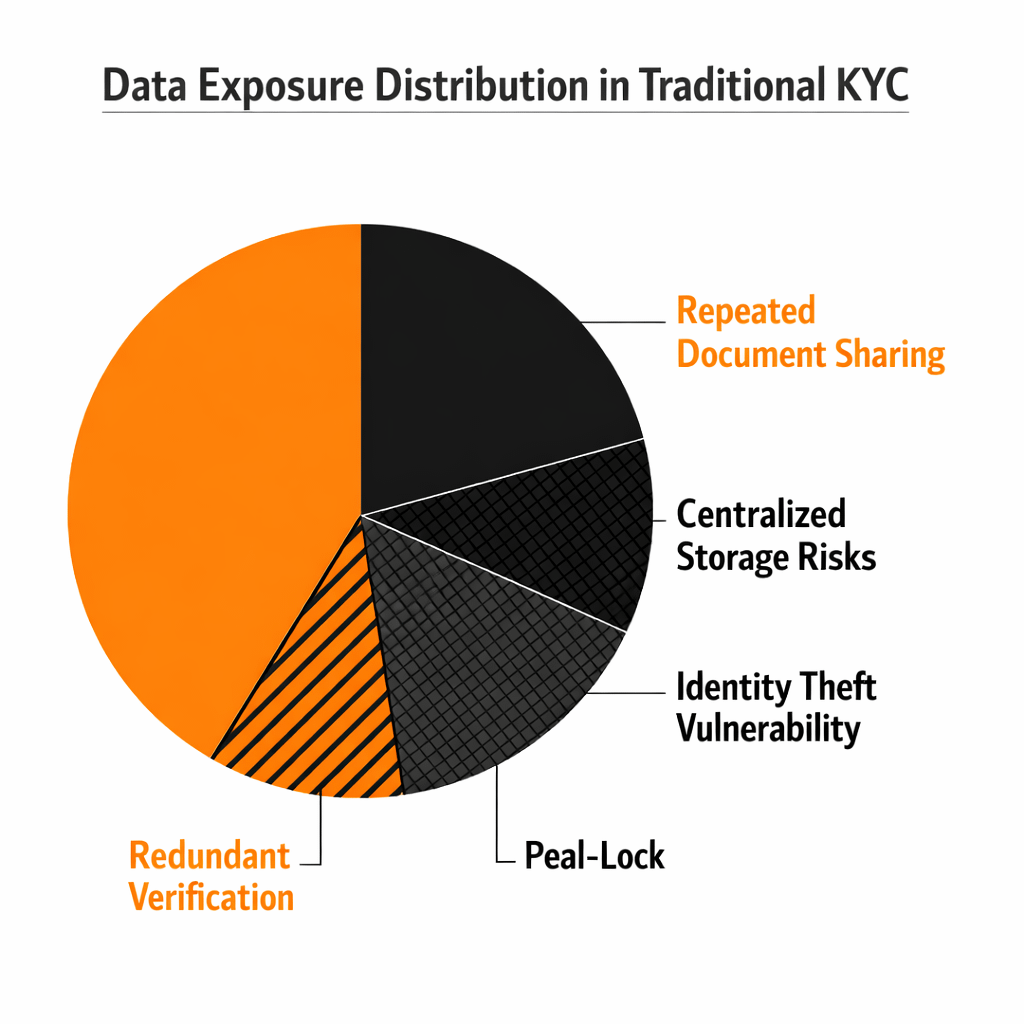
A user completes verification once. The result becomes reusable. Platforms reduce onboarding friction. Data exposure is minimized because personal documents are not constantly shared across services. Still, I remain cautious about how easily this model works in practice. Trust becomes the central issue. For a platform to accept an attestation, it must trust the issuer. Not all KYC providers operate under the same standards. Regulatory requirements differ across jurisdictions. A verification that is valid in one region may not satisfy rules in another. This means that interoperability is not just technical; it is also regulatory. Sign Protocol can provide a framework for sharing attestations, but the acceptance of those attestations depends on legal and institutional alignment. Without that alignment, platforms may still prefer to run their own verification processes. Another challenge is user control. While the system aims to protect privacy, it must also ensure that users can manage how their attestations are shared. If access control is not designed carefully, there is a risk of overexposure or misuse of verification data. Privacy is not only about hiding information; it is about controlling how it is revealed. There is also the question of revocation. KYC status can change. A user who passes verification today may not meet the same requirements later. The system must allow attestations to be updated or revoked reliably. Otherwise, outdated information could continue to circulate across platforms. From a technical perspective, the idea of reusable attestations makes sense. It reduces duplication, improves efficiency, and aligns with how digital systems should ideally operate. But the real challenge lies in building an ecosystem where issuers, regulators, and platforms agree on standards. What I find interesting about Sign Protocol is that it does not attempt to eliminate KYC. Instead, it tries to make it more portable and less invasive. That distinction matters because KYC is unlikely to disappear. Regulatory frameworks are becoming stricter, not looser. The goal is not to remove verification but to make it less repetitive and more privacy-preserving. Whether this approach becomes widely adopted remains uncertain. It requires coordination between multiple stakeholders. It requires trust in issuers. It requires systems that can handle updates and revocations. It requires developers to build applications that can interpret and use attestations effectively. For now, I see Sign Protocol as an attempt to rethink how identity verification fits into decentralized systems. Not by removing compliance, but by reshaping how it is handled. If it works, it could reduce one of the most frustrating parts of digital onboarding. If it does not, KYC will likely remain what it is today: necessary, repetitive, and far from seamless.