When I first started reading about Midnight Network I had to slow myself down a bit because my first instinct was to place it inside the broad category of a privacy blockchain and move on. The more I read though the more that label felt too loose to be useful since Midnight is built around a simpler idea. Some facts need to be checked by a network but the raw data behind those facts does not always need to be shared with everyone who participates in that network.
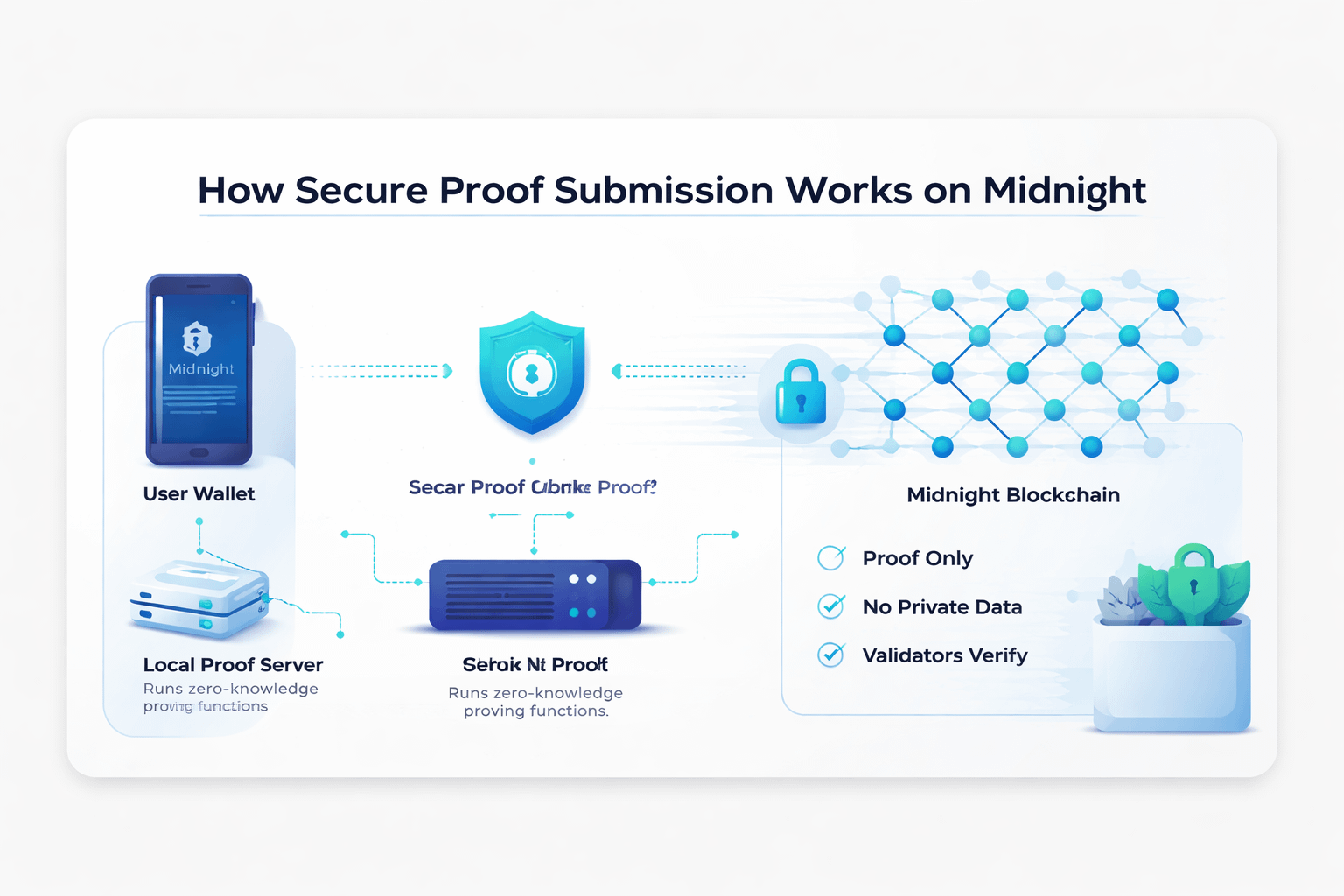
I find it helpful to think of secure proof submission as the difference between showing your work to the whole room and handing over a sealed answer that can still be checked. On Midnight the proof is not something added at the last second to make a transaction sound more advanced than it is. There is an actual proving layer involved and that matters because the wallet talks to a proof server to run the zero knowledge functions needed for a transaction and that server may receive private details such as token ownership or a DApp’s private state. Because of that Midnight’s own guidance treats proof generation as a real security concern and I think that is the right way to frame it since this is not only about elegant math. It is also about where sensitive information lives and who controls the machine handling it and how much exposure is created while the work is being done.
What continues to stand out to me is that the flow is more ordinary than people expect once the mystery falls away. A transaction can begin in an unproven state and the proof server is what turns it into something the network can accept which means the chain is not asking for your whole private context and is only asking for evidence that the transition follows the rules. That design goes back to the Kachina research behind Midnight which framed private smart contracts as a mix of public on chain state and private off chain state tied together by proofs instead of blind trust. A few years ago that kind of architecture still felt mostly academic and a bit distant from ordinary development work but now it is showing up in developer tools and runtime APIs and wallet connectors and example applications which makes the idea feel less abstract and more like something teams can actually work with.
That shift from theory to tooling is a big reason Midnight is drawing more attention now than it would have five years ago because what once sounded like a research promise is starting to look like an operating model. The surrounding ecosystem has become more concrete through test environments and version compatibility guidance and a clearer path for developers who want to build without leaking private data by default. None of that is glamorous and I think that is exactly why it matters because real adoption usually depends less on dramatic claims and more on whether the underlying system is understandable and repeatable and stable enough to trust in practice.
I used to think privacy focused networks were mostly trying to hide everything and that assumption now feels too blunt for what Midnight is actually trying to do. Its framing around selective disclosure and protected private state suggests a model where not all information needs to be public but not all of it needs to be permanently sealed away either which gives the whole project a narrower and more practical shape. That middle ground feels more relevant now than it did in earlier crypto cycles because as blockchains move closer to real world use cases such as financial reporting and identity checks and health related data and even private AI workflows the old choice between making everything public and keeping everything off chain starts to feel too crude. Midnight is trying to create room for something more measured and that is part of why the idea lands differently today.
I find that useful because it brings the conversation back to a simple question about what the network actually needs to know. In many cases the answer is less than people assume since it may only need proof that a rule was followed or that an asset is valid or that a state change is allowed without needing the private details that produced that result. Once I started looking at Midnight that way secure proof submission stopped sounding like an exotic feature and started looking more like a design discipline built around one practical instinct which is to keep the sensitive part close to the user and let the proof do the traveling.
That does not make the system effortless and it does not remove uncertainty because Midnight is still evolving and like any developing network some of its long term shape will only become clear with time. Even so the core idea already stands on its own because secure proof submission here is not about making trust disappear but about reducing how much trust you have to place in the wider environment. For me that is still the most grounded way to understand what Midnight is trying to do.
@MidnightNetwork #Night #night $NIGHT

