@MidnightNetwork . I still remember the first time I saw a blockchain transaction disappear in a way that felt… intentional. It wasn’t lost—far from it. It was verified, confirmed, and yet somehow hidden. That moment stuck with me. Privacy versus transparency. Control versus visibility. Midnight Network is attempting to thread that needle, offering programmable privacy at scale—a solution that feels as much philosophical as it is technical.
In today’s Web3 world, privacy isn’t optional anymore. Users are waking up to how exposed their financial and data footprints really are. Meanwhile, blockchains demand trust, auditability, and correctness. Midnight Network sits right in the middle of that tension. Its goal? Reconcile verification with selective concealment. Make privacy auditable, programmable, adaptable—without sugarcoating how hard that really is.
The Philosophy of Programmable Privacy
Traditionally, privacy has been binary: either everyone sees, or no one does. Crude, right? Midnight Network asks a different question: what if privacy could be flexible, programmable, and context-aware? What if it could live in code?
Think of it like a “privacy switchboard.” Users, smart contracts, network operators—everyone can define rules for who sees what, when, and under which conditions. No default transparency pushing you into a corner. No opaque central layer deciding what counts as private. Just rules, living in code, enforceable across the network.
At its core, this is about reclaiming control. Individuals and organizations get to decide what matters. And the ledger still guarantees correctness. But here’s the thing I keep thinking about: can a set of rules ever replace human judgment? Programmable privacy is promising—but messy, in the very human way of dealing with nuance.
The Architectural Stack
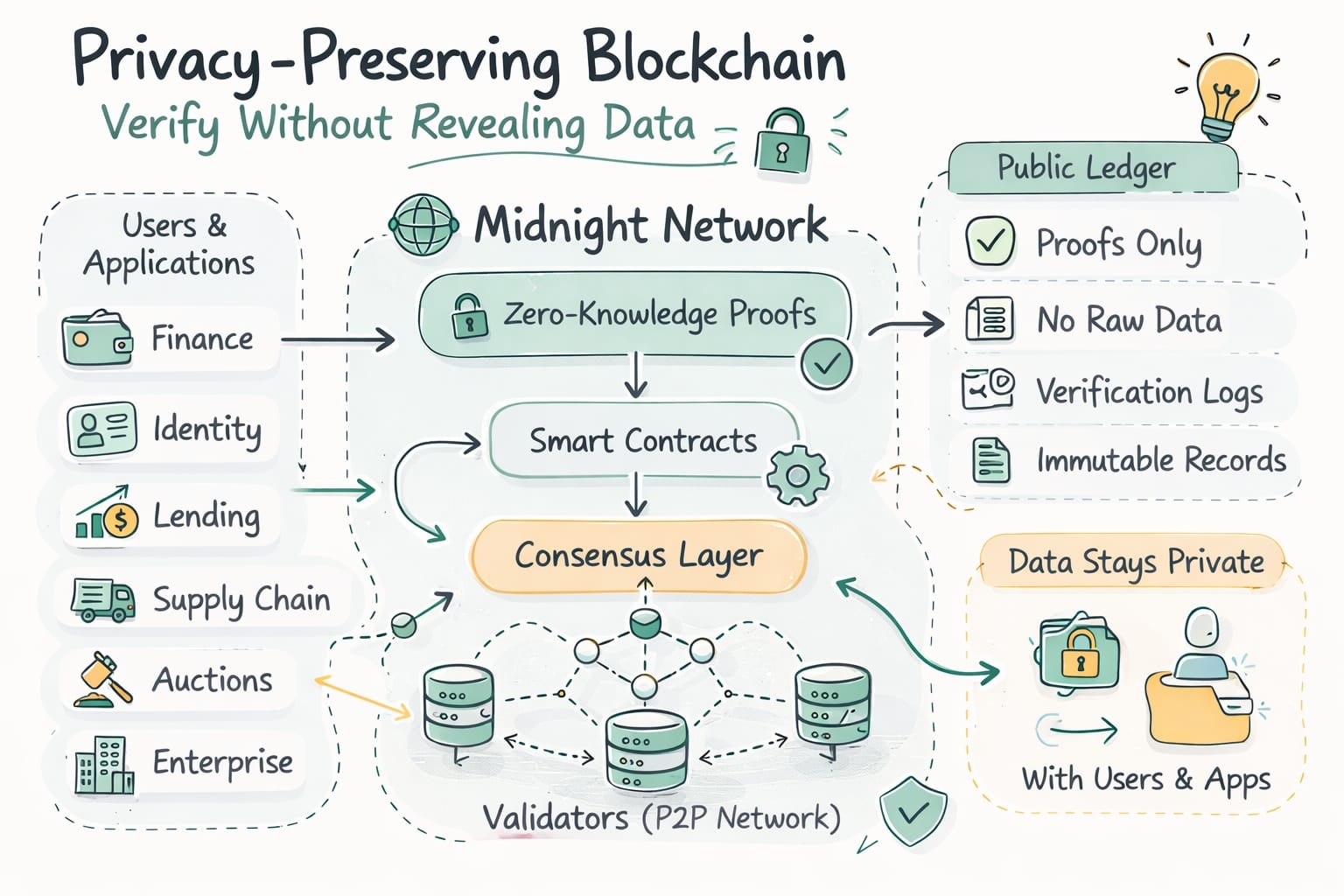
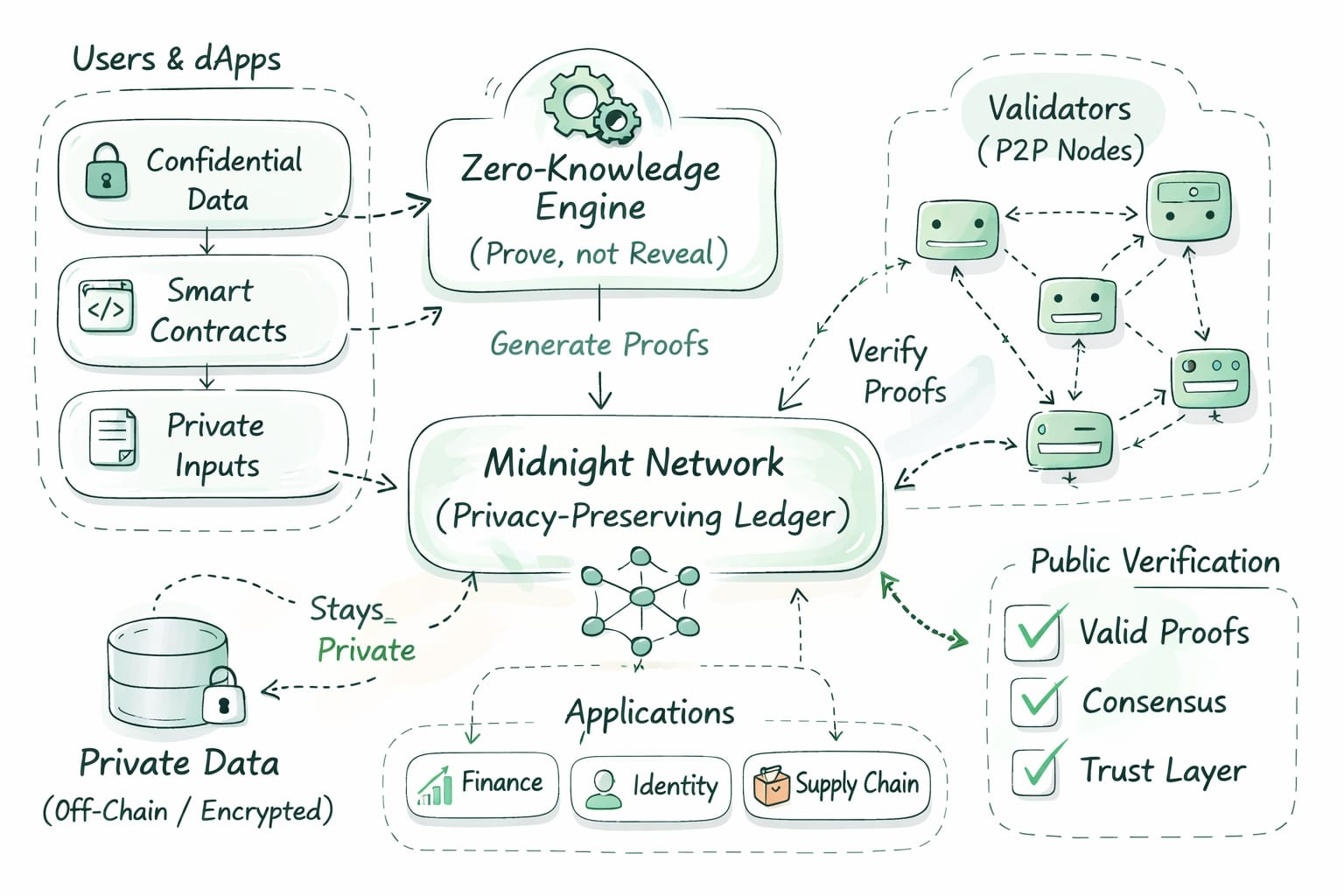
Midnight Network works through three intertwined layers: Policy, Cryptography, Consensus. Each layer leans on the others. Some layers shout, some whisper—but together, they enforce privacy without anyone ever touching the sensitive stuff.
Layer 1: Programmable Privacy Policies
Privacy isn’t hard-coded. It’s a living set of instructions attached to accounts, transactions, and smart contracts. Developers can define rules like:
“Reveal this balance only to auditors.”
“Show this transaction only to a consortium of nodes.”
High-level enough to write quickly, strict enough to hold anyone accountable. Policies aren’t static—they evolve.
Layer 2: Advanced Cryptography
Beneath the surface, Midnight Network leans on zero-knowledge proofs (ZKPs), commitment schemes, and homomorphic encryption.
ZKPs: prove correctness without spilling secrets.
Commitments & hashes: anchor selectively revealed data to the ledger.
Homomorphic encryption: run logic on encrypted data—see the output, never the inputs.
Stacked together, it’s like building arcane Lego blocks. Trustless privacy enforcement, sometimes feeling more like wizardry than code.
Layer 3: Consensus Integration
Policies mean nothing without enforcement. Nodes validate proofs, enforce rules, and transition states—all without leaking sensitive info. Selective verification channels let auditors see just enough, while everyone else sees only blurred or masked views. Elegant… until edge cases creep in. Rogue auditors, misconfigured policies, or inconsistent nodes can still trip things up.
How Programmable Privacy Works
Picture a company issuing tokenized assets. Regulators get full access. Counterparties see relevant details. Everyone else? A blurred glimpse.
Privacy policies attach to every transaction. Nodes cryptographically validate, auditors confirm compliance, and general participants only glimpse commitment-based views.
Core Mechanisms:
Policy-Oriented Data Exposure: Different eyes, different slices. Some see whispers, some the full scream.
Zero-Knowledge Verification: Nodes prove computations are correct without revealing secrets.
Dynamic Access Control: Rules evolve; temporary or conditional exposure is possible.
Auditability & Compliance: Privacy for the public, keys in auditors’ hands—balancing confidentiality with accountability.
On Midnight Network, the ledger isn’t just recording history. It’s policing privacy, enforcing rules, and sometimes questioning its own boundaries. That tension—that uncertainty—is where the thinking gets interesting.
Midnight Network in Context
Private blockchains aren’t new. Programmable privacy is. Midnight stakes its claim in the flexible, modular, programmable camp.
Composability & Modularity
Privacy policies can layer over any contract or data flow. Lego-like interoperability. Cryptography, consensus, and policy dance together—but not always perfectly. Misaligned policies or unexpected interactions can trip nodes.
Enterprise-Ready Design
Unlike research chains buried in ZKPs, Midnight targets the real world: auditing, regulatory compliance, multi-party collaboration. Built for people, not papers.
Scalability through Policy Segmentation
By segmenting access and offloading heavy computation through selective verification, throughput remains high. Still… complexity grows, auditors may lag, nodes occasionally pause.
Community Governance
Modules evolve through contributor review. Privacy is living, breathing, sometimes mutating faster than anyone expects. A “feature” here is not a guarantee—it’s a conversation.
Challenges and Opportunities
Programmable privacy isn’t easy. Policies are tricky to write. ZKPs are expensive. Consensus across heterogeneous nodes is fragile. Regulatory frameworks are foggy.
But these challenges are opportunities. Midnight Network suggests privacy and transparency aren’t opposites. They can coexist—uneasily, creatively, pragmatically. Users, auditors, regulators—all can share the ledger without fully trusting one another.
This isn’t just a protocol; it’s a statement. Privacy can be dynamic, auditable, programmable. It reclaims control from centralized actors while preserving trustless foundations. Sometimes it works flawlessly. Sometimes it creaks. But that tension, that edge of uncertainty—that’s where innovation lives.
Midnight Network may define the next wave of distributed ledger evolution—where privacy isn’t just a feature, but a programmable principle.

