When I first started exploring blockchain technology, the idea that fascinated me most was transparency. A system where transactions could be verified by anyone without relying on banks or centralized institutions felt like a major technological breakthrough. But as I continued studying the space more deeply, I began to notice a limitation that early discussions rarely addressed. Transparency can build trust, yet in many real-world systems it can also introduce risk. This realization is what eventually led me to research Midnight Network, a privacy-focused blockchain project designed to address this exact challenge.
As I explored the topic further, it became clear why privacy matters in decentralized infrastructure. Financial institutions manage confidential records. Healthcare systems protect sensitive patient data. Businesses operate with proprietary information and operational insights that cannot simply be placed on a public ledger. The deeper I examined blockchain adoption across industries, the more obvious it became that complete transparency can sometimes slow real-world integration rather than accelerate it.
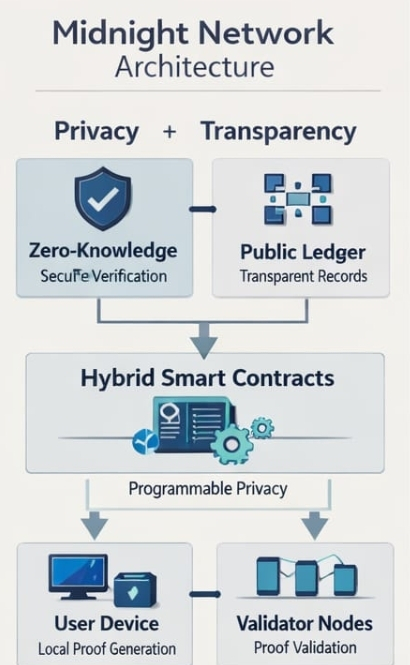
During my research, Midnight Network stood out because it approaches blockchain architecture from a different perspective. Instead of forcing developers to choose between transparency and privacy, the system attempts to combine both principles within the same framework. The project is being developed by Input Output Global, the engineering organization known for building the Cardano ecosystem, and its objective is to enable decentralized applications that can function securely while still protecting sensitive information.
Traditional public blockchains were designed around the principle that visibility creates trust. Every transaction is recorded on a ledger that anyone can inspect. This model works extremely well for digital currencies where transparency strengthens verification. However, when blockchain technology begins interacting with sectors such as finance, healthcare, identity systems, or enterprise logistics, the situation becomes more complicated. Organizations cannot expose confidential information simply to participate in decentralized networks.
Midnight Network attempts to address this structural challenge through the use of zero knowledge cryptography. When I first encountered the concept it sounded almost paradoxical. The idea that someone could prove something is true without revealing the underlying data felt difficult to imagine. But after studying how zero knowledge proofs function, the concept became surprisingly logical. These systems allow a participant to demonstrate that a statement is valid while keeping the supporting data completely private.
This capability creates a balance between verification and confidentiality. A financial application could confirm that a transaction meets the required conditions without revealing the exact balances involved. Identity systems could verify regulatory compliance without exposing personal information. Companies could demonstrate operational integrity or compliance outcomes without sharing internal business data. In each case the network verifies correctness while the sensitive details remain protected.
Another concept that caught my attention while studying the architecture is often described as programmable privacy. Instead of treating privacy as a simple switch that is either on or off, the system allows developers to define how privacy operates inside their applications. Certain pieces of information can remain confidential while other elements remain publicly verifiable on the blockchain. This flexibility allows developers to design systems where transparency and confidentiality coexist in a carefully structured way.

One additional architectural detail that stood out during my research involves how computation and verification occur within the network. In many blockchain systems sensitive information must be transmitted directly to the network where validators process it. Midnight approaches this differently. Users generate cryptographic proofs locally on their own devices, and the network verifies the proof rather than the underlying information. From a security perspective this approach significantly reduces the exposure of private data while still maintaining trust in the system.

After studying the architecture, development framework, and potential applications of Midnight Network, I began to see it as part of a broader evolution within the blockchain industry. Early blockchain systems proved that decentralized verification was possible. The next phase of development requires infrastructure capable of maintaining trust while also protecting information.
If privacy-preserving technologies continue to mature and become easier for developers to implement, networks like Midnight may quietly become foundational layers for decentralized applications across many industries. The real progress in blockchain may not always come from speculation or market noise. It may come from thoughtful engineering that solves practical challenges. Projects focused on balancing transparency with privacy remind us that innovation in Web3 is still unfolding, and the future of decentralized technology can be both secure and empowering for everyone involved.
