Saya ingat momen itu dengan cukup jelas.
@MidnightNetwork . Saya sedang menggali melalui transaksi di buku besar yang berfokus pada privasi, melakukan rutinitas biasa—memeriksa tanda tangan, melacak saldo, mengikuti logika yang biasanya mengungkapkan apa yang sebenarnya bergerak di dalam blok.
Segalanya terlihat normal pada awalnya.
Jaringan mengkonfirmasi transaksi tersebut.
Validator menerimanya.
Blok telah selesai.
Tapi ada sesuatu yang terasa tidak biasa.
Informasi yang saya harapkan untuk dilihat hanya… tidak ada di sana.
Pada awalnya terasa seperti sesuatu yang hilang, seperti sepotong data transaksi yang gagal dimuat. Hampir seperti sistem menyembunyikan sesuatu dari saya.
Dan kemudian itu terlintas.
Sistem ini menyembunyikan sesuatu — tetapi bukan karena itu rusak.
Karena itu dirancang untuk itu.
Momen kecil itu menangkap masalah yang lebih dalam yang coba diatasi oleh Midnight Network. Blockchain tradisional dibangun di atas transparansi radikal. Setiap node melihat segalanya. Setiap transaksi menjadi bagian dari sejarah yang selalu terlihat.
Model itu bekerja dengan indah ketika tujuannya adalah verifikasi tanpa kepercayaan. Tetapi saat blockchain mulai menyentuh data keuangan sensitif, infrastruktur perusahaan, atau sistem identitas, transparansi yang sama mulai menciptakan gesekan.
Midnight Network dimulai dari asumsi yang berbeda.
Mungkin transparansi dan privasi tidak harus saling membatalkan.
Alih-alih memaksa pengguna untuk memilih antara sistem publik sepenuhnya atau sepenuhnya tersembunyi, Midnight menjelajahi sesuatu yang lebih fleksibel: privasi yang dapat diprogram langsung ke dalam sistem itu sendiri.
Tidak statis.
Tidak dikendalikan oleh penjaga gerbang terpusat.
Tetapi ditulis ke dalam logika jaringan.
Dan setelah Anda mulai berpikir tentang sistem terdistribusi dengan cara itu, ruang desain tiba-tiba terlihat sangat berbeda.
Masalah Struktural Dengan Transparansi Radikal
Sebagian besar blockchain publik mengikuti aturan sederhana: semua orang dapat melihat segalanya.
Setiap node secara independen memverifikasi riwayat transaksi lengkap, yang merupakan apa yang memungkinkan sistem terdesentralisasi berfungsi tanpa perantara yang tepercaya.
Tetapi sifat yang sama juga menciptakan masalah eksposur yang cukup besar.
Transfer keuangan menjadi terlihat secara permanen.
Aktivitas bisnis dapat ditelusuri.
Data operasional bocor ke infrastruktur publik.
Di hari-hari awal cryptocurrency, ini tidak dianggap sebagai masalah serius. Pengguna Bitcoin bersifat pseudonim, dan ekosistemnya cukup kecil sehingga banyak peserta menerima transparansi sebagai biaya desentralisasi.
Tetapi teknologi blockchain tidak lagi terkurung dalam eksperimen hobi.
Hari ini menyentuh infrastruktur keuangan, sistem rantai pasokan, aset tokenisasi, kerangka identitas, dan alur kerja perusahaan yang semakin kompleks.
Dan dalam lingkungan tersebut, total visibilitas menjadi lebih sulit untuk dibenarkan.
Perusahaan tidak dapat mengekspos strategi keuangan internal kepada pesaing.
Regulator tidak dapat mengandalkan sistem di mana data kepatuhan sensitif menjadi terlihat oleh seluruh internet.
Dan pengguna biasa mulai menyadari bahwa riwayat transaksi permanen datang dengan implikasi privasi jangka panjang.
Solusi tradisional mencoba memperbaiki ketegangan ini dengan cara yang berbeda.
Blockchain pribadi membatasi akses.
Jaringan yang diizinkan memperkenalkan penjaga gerbang.
Lapisan privasi off-chain berusaha menyembunyikan data di luar buku besar.
Setiap pendekatan menyelesaikan sebagian dari masalah, tetapi sering kali dengan biaya desentralisasi atau jaminan verifikasi.
Midnight Network mendekati masalah ini dengan cara yang berbeda.
Alih-alih memindahkan privasi di luar buku besar, itu mengubah cara kerja visibilitas di dalam buku besar itu sendiri.
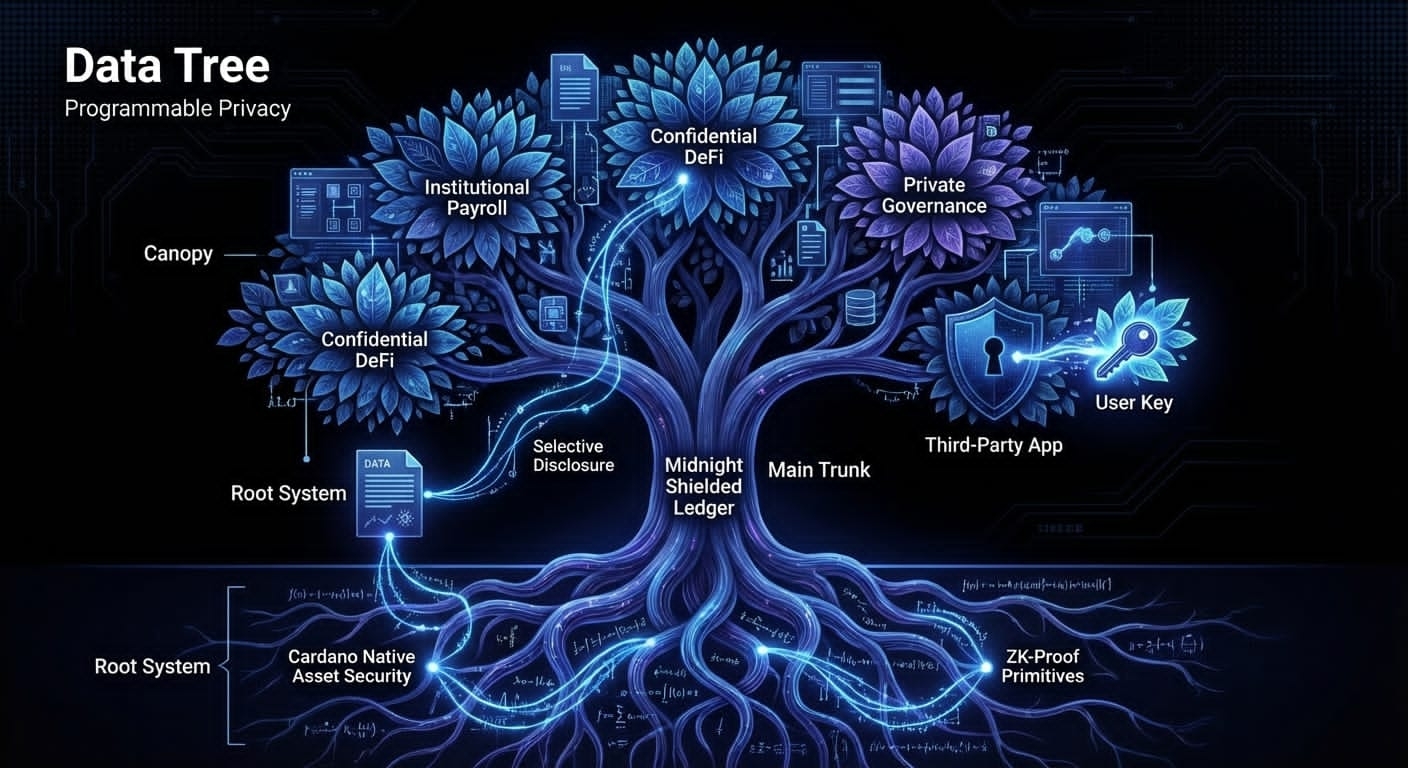
Privasi sebagai Properti yang Dapat Diprogram
Ide inti di balik Midnight Network cukup intuitif setelah Anda menghilangkan bahasa teknis.
Privasi tidak seharusnya menjadi pengaturan tetap.
Ia harus berperilaku lebih seperti perangkat lunak.
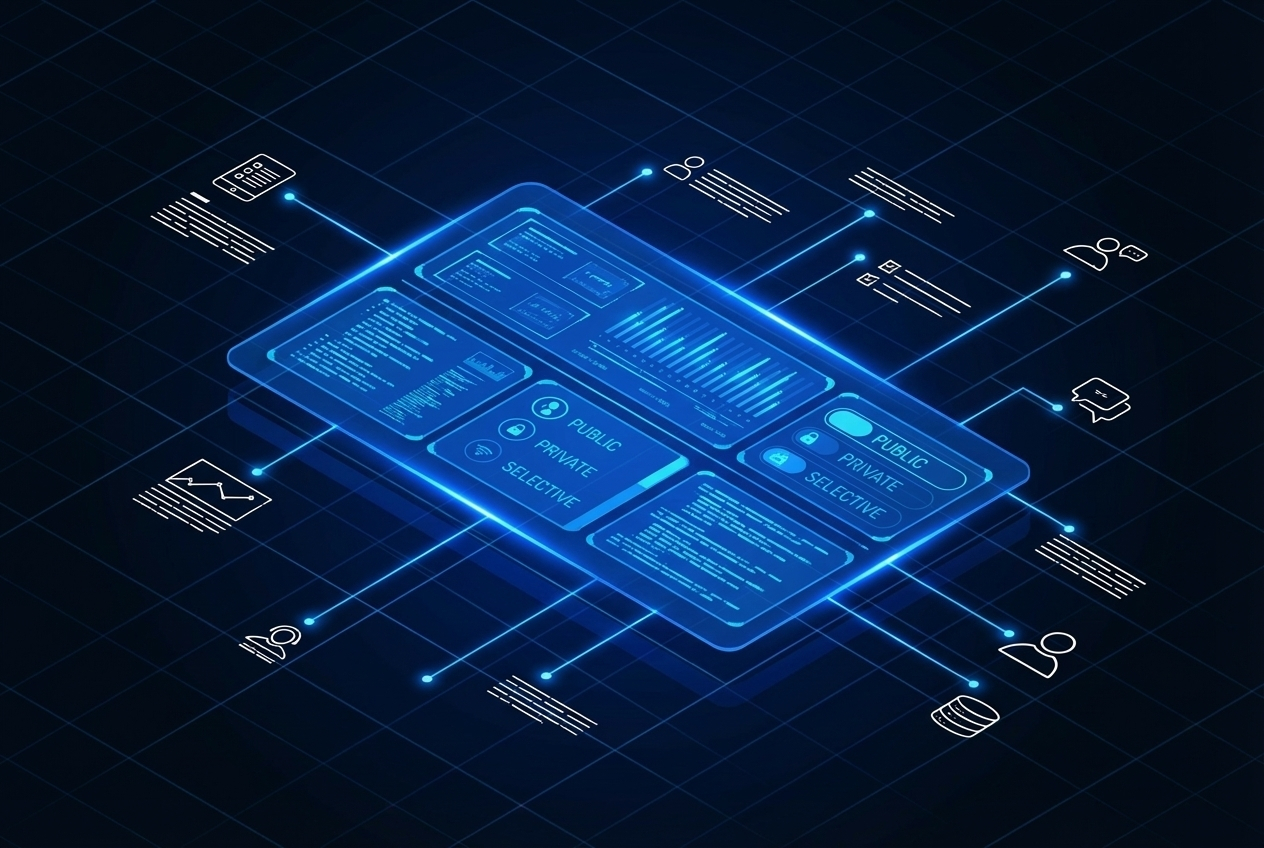
Alih-alih memutuskan bahwa informasi harus baik publik selamanya atau sepenuhnya tersembunyi, Midnight memungkinkan pengembang untuk mendefinisikan aturan yang mengatur siapa yang dapat melihat data tertentu dan dalam kondisi apa.
Anggap saja sebagai sistem izin yang tertanam langsung ke dalam infrastruktur blockchain, bukan hanya enkripsi yang menyembunyikan segalanya.
Beberapa peserta mungkin melihat detail transaksi lengkap.
Lainnya mungkin hanya melihat komitmen kriptografi.
Dan beberapa mungkin tidak melihat apa-apa kecuali bukti bahwa transaksi yang valid terjadi.
Apa yang membuat ini menarik adalah bahwa jaringan masih dapat memverifikasi kebenaran transaksi bahkan ketika data yang mendasarinya tetap tersembunyi.
Keseimbangan itu — verifikasi tanpa eksposur — adalah inti dari arsitektur Midnight.
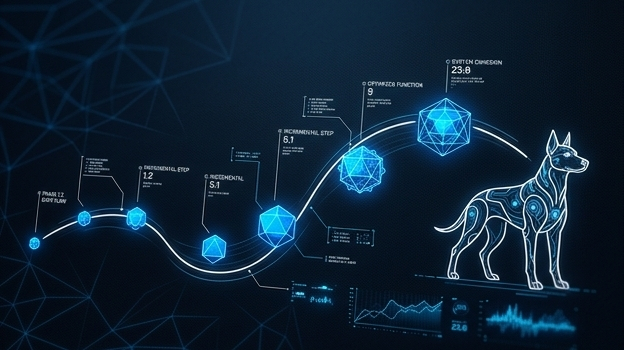
Arsitektur Di Balik Midnight
Untuk membuat privasi yang dapat diprogram menjadi mungkin, Midnight mengorganisir desainnya menjadi tiga lapisan yang saling berinteraksi:
Definisi kebijakan
Penegakan kriptografi
Validasi konsensus
Setiap lapisan menangani bagian yang berbeda dari masalah privasi.
Tetapi tidak ada dari mereka yang bisa bekerja sendiri.
Mereka saling bergantung satu sama lain.
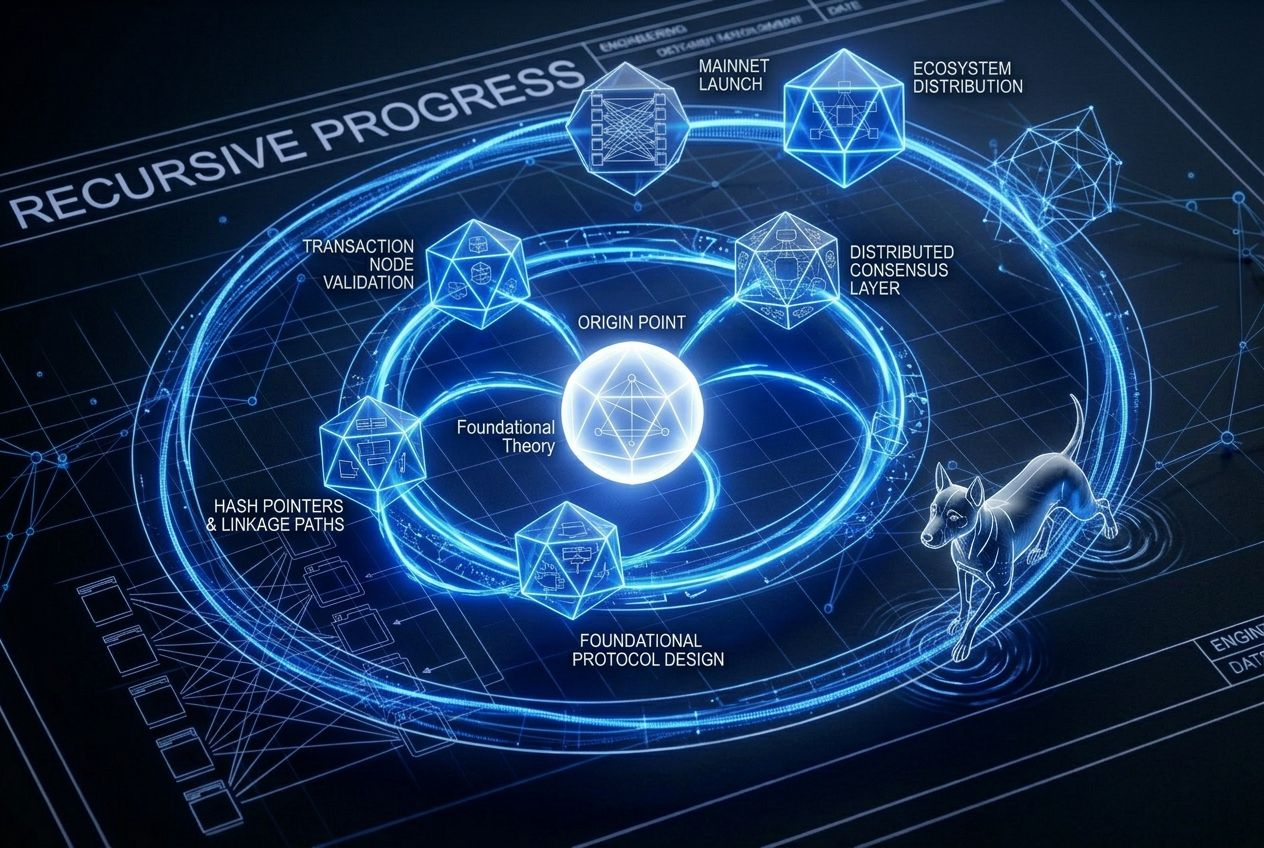
Lapisan Kebijakan: Memutuskan Siapa Melihat Apa
Lapisan kebijakan mengontrol bagaimana informasi mengalir di seluruh jaringan.
Alih-alih menyematkan aturan privasi yang kaku langsung ke dalam protokol, Midnight memungkinkan akun, kontrak, dan transaksi untuk membawa definisi kebijakan mereka sendiri.
Kebijakan ini dapat mendefinisikan hal-hal seperti:
• siapa yang diizinkan mengakses detail transaksi
• kapan data tertentu menjadi terlihat
• apakah pengungkapan parsial diizinkan
• bagaimana verifikasi kepatuhan bekerja
Pengembang berinteraksi dengan kebijakan ini melalui bahasa domain khusus yang dirancang untuk membuat logika privasi dapat dikelola tanpa memerlukan keahlian kriptografi yang mendalam.
Fleksibilitas itu membuka kemungkinan menarik.
Sebuah lembaga keuangan mungkin mengizinkan regulator untuk memeriksa metadata transaksi sambil menyembunyikan strategi operasional dari pesaing.
Sebuah platform rantai pasokan dapat mengonfirmasi bahwa barang telah dikirim tanpa mengungkapkan data harga yang sensitif.
Sistem identitas terdesentralisasi dapat memverifikasi kredensial tanpa mengungkapkan informasi pribadi.
Alih-alih memperlakukan privasi sebagai saklar permanen, lapisan kebijakan menjadikannya dinamis.
Kriptografi yang Menegakkan Aturan
Tentu saja, kebijakan hanya penting jika sistem dapat menegakkannya.
Di situlah Midnight sangat bergantung pada alat kriptografi modern.
Bukti zero-knowledge berada di pusat desain.
Mereka memungkinkan satu pihak untuk membuktikan bahwa komputasi atau transaksi valid tanpa mengungkapkan input yang mendasarinya.
Dalam istilah praktis, jaringan dapat memverifikasi bahwa:
• saldo tetap konsisten
• transaksi mengikuti aturan protokol
• logika kontrak pintar dieksekusi dengan benar
Semua tanpa mengungkapkan data sensitif di belakang operasi tersebut.
Melengkapi bukti zero-knowledge adalah skema komitmen, yang memungkinkan informasi dikunci secara kriptografis ke dalam buku besar sambil tetap tersembunyi sampai diungkapkan secara selektif.
Beberapa bentuk enkripsi homomorfik juga memungkinkan komputasi terbatas pada data yang dienkripsi itu sendiri.
Bersama-sama, mekanisme ini memungkinkan Midnight untuk mempertahankan jaminan verifikasi yang kuat sambil mengontrol siapa yang dapat melihat informasi apa.
Ini adalah pendekatan yang sangat kuat — tetapi juga secara teknis menuntut.
Kesulitan itu adalah salah satu alasan mengapa blockchain yang menjaga privasi secara historis berjuang dengan kinerja dan skala.

Privasi Di Dalam Lapisan Konsensus
Bahkan kriptografi yang kuat tidak berarti jika mekanisme konsensus mengabaikannya.
Midnight mengintegrasikan penegakan privasi langsung ke dalam proses validasi transaksi.
Ketika node memverifikasi blok, mereka tidak hanya memeriksa tanda tangan digital atau saldo.
Mereka juga memverifikasi bukti kriptografi yang mengonfirmasi bahwa kondisi kebijakan terpenuhi.
Beberapa validator mungkin melihat detail transaksi lengkap.
Lainnya memvalidasi operasi yang sama murni melalui bukti.
Auditor atau regulator dapat diberikan saluran akses yang terkontrol yang mengungkapkan informasi tertentu saat diperlukan.
Jaringan tetap terdesentralisasi, tetapi visibilitas informasi menjadi bergantung pada konteks.
Itu adalah pergeseran halus, tetapi penting.
Alih-alih menganggap bahwa setiap peserta harus melihat segalanya, buku besar memperlakukan visibilitas informasi sebagai sesuatu yang diatur oleh aturan.
Peran Sistem Zero-Knowledge
Kriptografi zero-knowledge telah mendapatkan perhatian di seluruh ekosistem blockchain, tetapi pendekatan Midnight menekankan pada adaptabilitas.
Banyak sistem ZK bergantung pada sirkuit yang telah ditentukan sebelumnya atau logika transaksi statis.
Midnight berusaha mendukung generasi bukti yang lebih fleksibel sehingga kebijakan privasi dapat berkembang seiring perubahan aplikasi.
Itu lebih penting daripada yang terlihat.
Sistem nyata jarang tetap statis.
Regulasi berkembang.
Kebutuhan bisnis berubah.
Aplikasi berkembang menjadi kasus penggunaan baru.
Jaringan privasi yang tidak dapat beradaptasi dengan kebijakan baru akhirnya menjadi kaku.
Midnight tampaknya mencoba menghindari perangkap itu dengan merancang privasi sebagai sesuatu yang dapat diprogram daripada tetap.
Apakah fleksibilitas itu bertahan dalam kondisi dunia nyata tetap menjadi salah satu pertanyaan terbuka yang lebih menarik di sekitar proyek ini.
Apa yang Ini Bisa Memungkinkan
Jika privasi yang dapat diprogram berfungsi seperti yang diharapkan, itu dapat membuka beberapa jenis aplikasi yang secara historis berjuang dengan infrastruktur blockchain publik.
Sistem keuangan perusahaan dapat berjalan di jaringan terdesentralisasi tanpa mengungkapkan data operasional yang sensitif.
Platform aset digital yang diatur dapat mempertahankan kepatuhan sambil melindungi informasi rahasia.
Sistem identitas terdesentralisasi dapat memverifikasi kredensial tanpa mengungkapkan catatan pribadi.
Bahkan lingkungan data kolaboratif mungkin memungkinkan organisasi untuk berbagi wawasan yang diperoleh dari dataset pribadi tanpa mengungkapkan data mentah itu sendiri.
Kemungkinan ini menjelaskan mengapa infrastruktur privasi telah menerima perhatian baru di seluruh industri.
Teknologi menjanjikan banyak.
Uji sebenarnya adalah keandalan operasional.
Tantangan di Depan
Privasi yang dapat diprogram juga memperkenalkan kompleksitas nyata.
Sistem kebijakan harus dirancang dengan hati-hati untuk menghindari kesalahan konfigurasi.
Generasi bukti zero-knowledge masih membawa biaya komputasi.
Sistem konsensus harus mengoordinasikan peserta yang tidak semuanya melihat data yang sama.
Dan regulasi tetap menjadi pertanyaan terbuka.
Pemerintah secara historis telah berhati-hati ketika berhadapan dengan teknologi yang menyembunyikan aktivitas keuangan.
Midnight tidak menghilangkan kekhawatiran ini.
Apa yang dicoba untuk dilakukan adalah menciptakan lingkungan di mana privasi dan pengawasan dapat berdampingan daripada bertentangan.
Arah yang Berbeda untuk Blockchain
Selama bertahun-tahun, industri blockchain bergantung pada keyakinan sederhana: transparansi menciptakan kepercayaan.
Midnight menyarankan bahwa ide itu mungkin tidak lengkap.
Kepercayaan mungkin tidak memerlukan visibilitas universal.
Ini mungkin hanya memerlukan kemampuan untuk memverifikasi bahwa aturan diikuti — bahkan ketika data yang mendasarinya tetap terlindungi.
Pembedaan itu membuka ruang desain yang sepenuhnya baru untuk sistem terdistribusi.
Apakah Midnight menjadi implementasi dominan dari privasi yang dapat diprogram masih belum pasti.
Tetapi arah arsitektur yang diwakilinya terasa semakin relevan saat teknologi blockchain bergerak ke lingkungan yang lebih kompleks dan sensitif.
Dan setelah Anda melihat transaksi dikonfirmasi tanpa mengungkapkan rahasianya, menjadi sulit untuk melihat blockchain tradisional dengan cara yang sama lagi.