Think about that for a moment. In a world where every transaction can be traced, every wallet analyzed, and every business pattern exposed, what does it really mean to operate privately on a blockchain? For too long, the industry has treated transparency as an unmitigated virtue, assuming that public visibility is synonymous with security. Yet in practice, the very transparency that enables verification also opens the door to surveillance, business exposure, and subtle forms of coercion. This is the blind spot Midnight Network is quietly addressing.
The problem is deceptively simple: fully transparent blockchains reveal too much. A startup raising funds on Ethereum, for example, might inadvertently expose payroll flows, supplier agreements, or strategic allocations simply by conducting normal on-chain activity. Retail users can have their wallet habits profiled, often without realizing it. Even smart contracts, by design, expose their internal logic and state to anyone inspecting the chain. Privacy tools exist, but they are often patched-on solutions, clunky, or incompatible with complex logic.
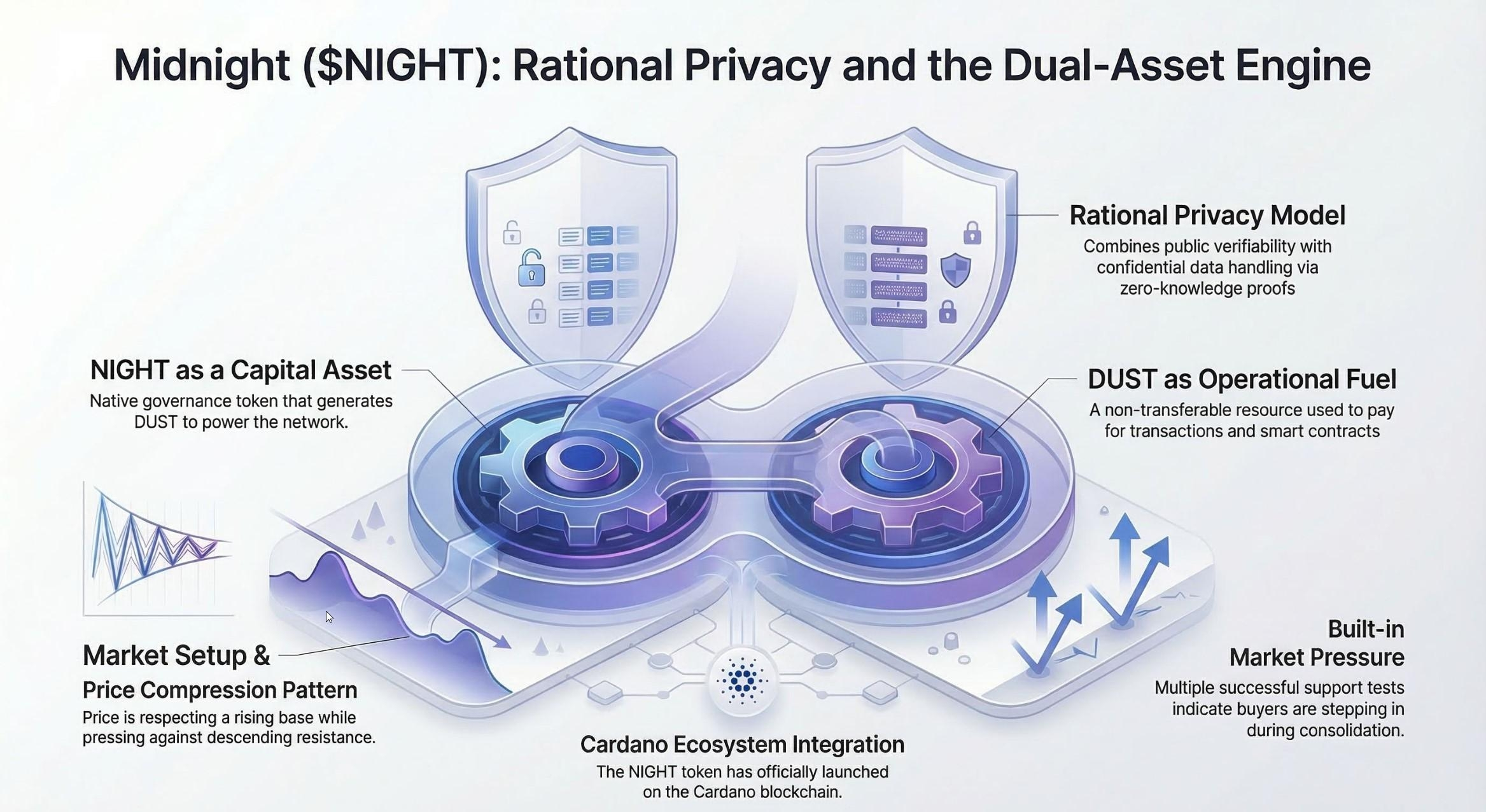
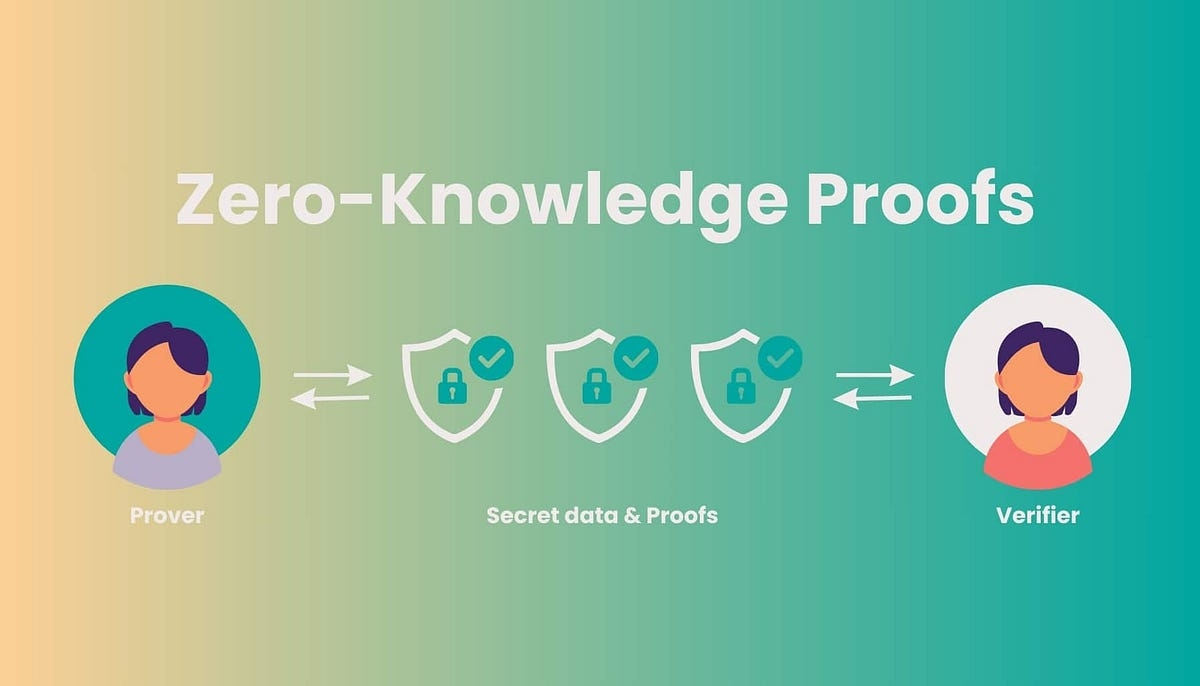
Enter Midnight Network. At its core, Midnight is not about hype, flashy launches, or marketing theatrics. It is about architecture — a deliberate, infrastructure-first approach to privacy. Using zero-knowledge proofs (ZK proofs), Midnight allows users to verify outcomes, confirm transactions, and demonstrate compliance without ever revealing the underlying data. Imagine proving your income bracket to access a service without ever disclosing the exact amount — that’s the type of capability Midnight enables. This is privacy without compromise.
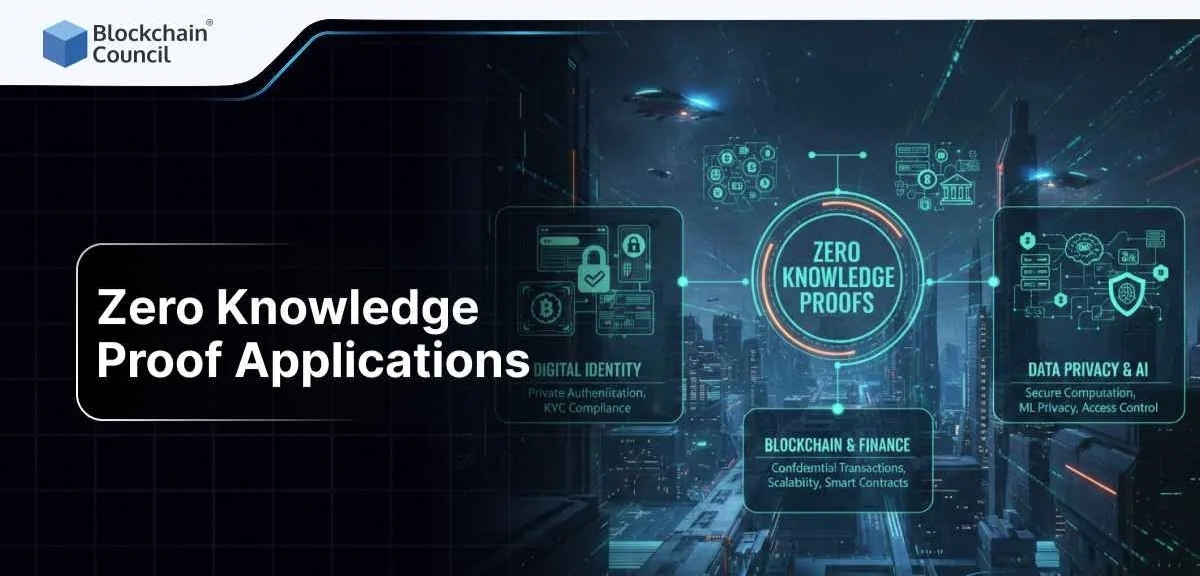
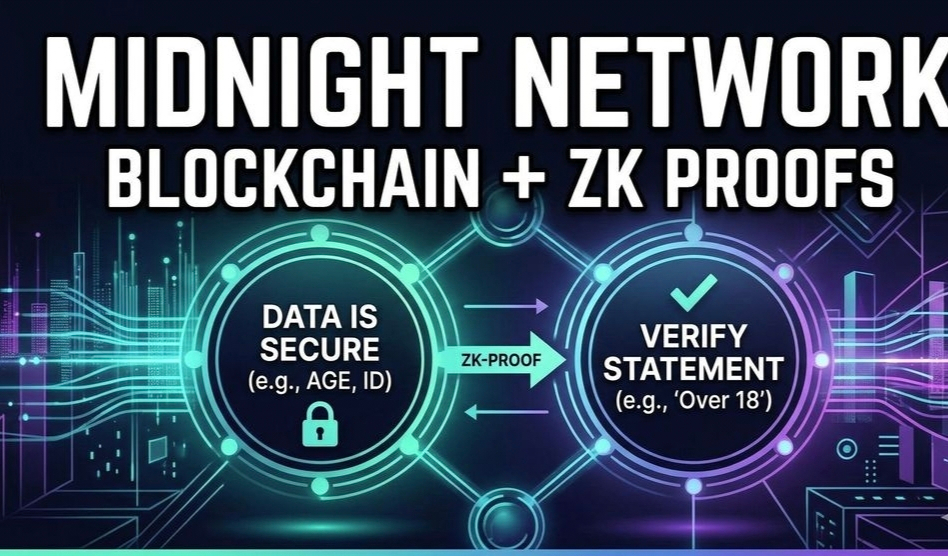
Zero-knowledge proofs have been discussed for years, but their true impact is often misunderstood. The essence is elegant: instead of exposing your inputs, you produce a proof that a certain statement is true. The blockchain validates the proof, not the sensitive information behind it. In other words, the network knows the math checks out without ever seeing the data. This subtle distinction changes everything: it enables private payments, confidential smart contracts, and even enterprise workflows where secrecy is paramount.

Consider a practical scenario. A multinational company wants to execute a supply chain contract on-chain, ensuring that deliveries meet certain thresholds before triggering payments. On a traditional blockchain, the contract logic and business metrics are publicly visible. On Midnight, ZK proofs can validate the contract without exposing sensitive operational data, letting partners confirm outcomes without revealing underlying information. Developers can create sophisticated dApps that operate privately, while regulators or auditors still get the proofs they need to maintain trust.
The architecture of Midnight is equally deliberate. The $NIGHT token functions as a network incentive and governance instrument but is intentionally decoupled from private computation resources. This separation emphasizes that Midnight prioritizes utility and privacy over speculation-driven token dynamics. Builders focus on verifiable computation, secure protocol design, and developer ergonomics rather than social media optics. Think of Midnight as a foundation for privacy infrastructure, not a speculative playground.

From a builder’s perspective, the network’s design is intuitive yet robust. ZK proofs are integrated at the transaction and smart contract layer, allowing developers to opt-in to confidentiality without sacrificing interoperability. Enterprise systems, DeFi protocols, or even identity management solutions can leverage Midnight’s verifiable privacy to safeguard sensitive data while still participating in the public blockchain ecosystem. In essence, Midnight is creating a layer where proof and privacy coexist — a quiet revolution against the binary of transparency versus secrecy.
But why does this matter beyond developers and enterprises? It touches the very philosophy of digital ownership and autonomy. If utility requires exposing personal or corporate data, the concept of ownership becomes hollow. Midnight challenges this by asserting that real utility is possible without compromising control. Users can interact, transact, and prove without the cost of exposure. Reflect for a moment: the difference between having a private wallet and a verifiable one is not just technical — it is the difference between being surveilled and truly sovereign.

This approach also fosters sustainable ecosystem growth. By designing with privacy in mind from the outset, Midnight reduces the friction of adoption for privacy-sensitive sectors. Financial services, health data applications, and enterprise resource management systems all become viable on-chain without forcing participants to sacrifice confidentiality. The architecture doesn’t just protect individual users; it scales to complex systems where multiple parties require both validation and discretion.

The reflective angle here is profound. Midnight forces us to reconsider what blockchain utility should mean. Is a ledger useful only if it is fully transparent, or can it achieve broader adoption by being smartly private? How do we reconcile the need for verifiable outcomes with the fundamental right to data protection? Midnight suggests that the answer lies in thoughtful architecture, careful protocol design, and a focus on builders over hype.
Moreover, the network is designed to evolve with cryptography itself. Zero-knowledge techniques continue to advance, and Midnight’s modular architecture allows the integration of new proof schemes without disrupting existing applications. Builders are not locked into outdated models; they inherit a protocol that can adapt as the state-of-the-art in ZK research progresses. This dynamic ensures that the network remains relevant and robust long after the initial deployment.

For the Web3 community, the lesson is clear: privacy need not be an afterthought. Midnight demonstrates that the path to secure, verifiable, and private blockchain applications is achievable today. The project exemplifies an architecture-first ethos, where every design choice reinforces privacy, utility, and proof. By separating token mechanics from private computation, investing in developer ergonomics, and embracing verifiable computation, Midnight builds a network where trust is engineered into the system, not assumed from transparency.
Ultimately, Midnight Network invites reflection. As the blockchain space matures, the tension between exposure and utility becomes increasingly stark. Will networks continue to favor openness at the expense of privacy, or will builders embrace systems where verification and secrecy coexist? Midnight suggests the latter. It challenges builders, enterprises, and users to rethink the relationship between ownership, utility, and trust in digital systems. And in doing so, it quietly reshapes the landscape of Web3 privacy.
Follow @MidnightNetwork to explore how $NIGHT and ZK proofs are redefining what it means to operate privately on-chain. The implications extend beyond finance, beyond contracts, beyond speculation. They touch the very ethos of decentralized ownership, making #night more than a token — it is a blueprint for a private, verifiable digital future.
@MidnightNetwork $NIGHT #night #NIGHT
