In the early days of blockchain, transparency was considered the ultimate advantage. Every transaction could be seen and verified by anyone. While this created trust, it also introduced a challenge: how can sensitive information remain private while still benefiting from blockchain verification?
This is where projects like @MidnightNetwork are drawing attention. The idea behind Midnight Network is not simply to hide information, but to create a system where data can remain confidential while still proving that certain conditions are true on-chain. This approach could help bridge the gap between privacy and accountability in decentralized systems.

For businesses, institutions, and even individuals, privacy is not just a preference it is often a requirement. Financial records, identity details, and contractual data cannot always be made public. Midnight Network is exploring ways to allow verification without revealing the underlying data, which could make blockchain technology more practical for real-world use.
The token NIGHT plays an important role in this ecosystem, supporting network activity and enabling participation in the broader Midnight infrastructure. As privacy technologies evolve, tokens like $NIGHT may become essential components of networks that prioritize both security and transparency.
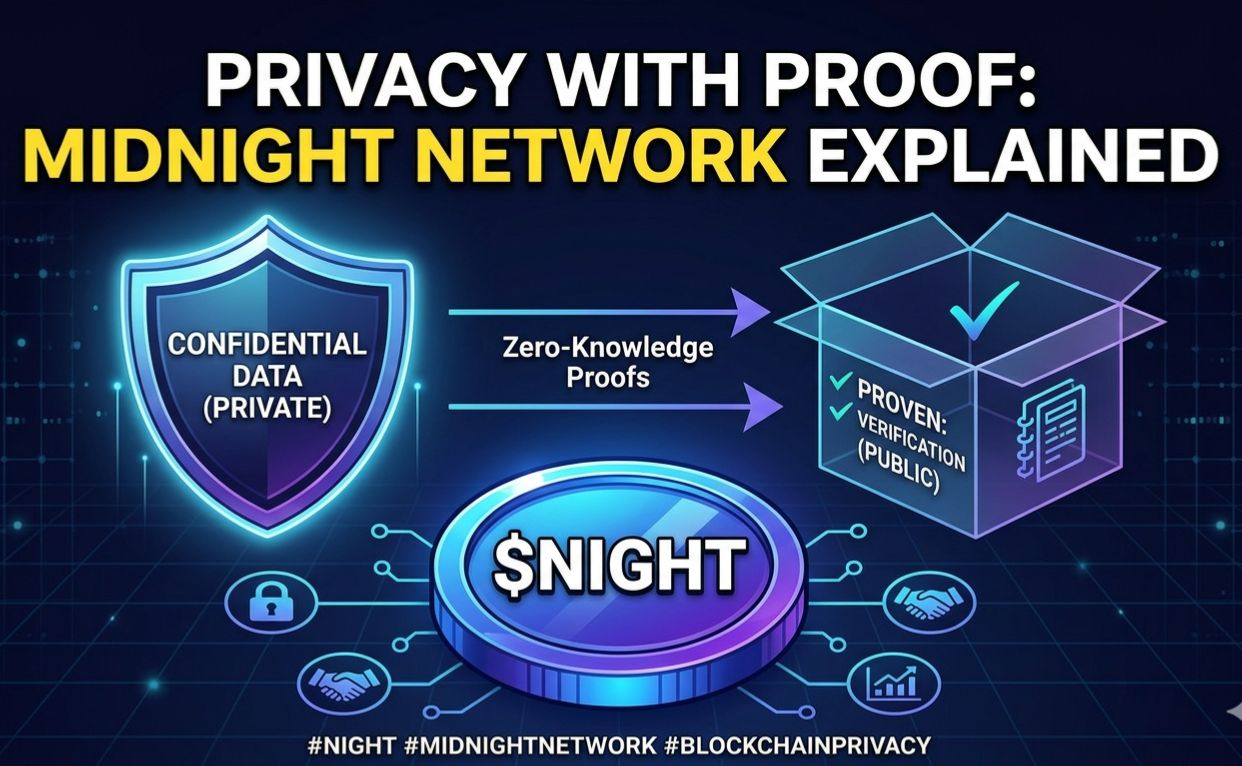
What makes this approach interesting is that it does not reject the core philosophy of blockchain. Instead, it refines it. By combining cryptographic privacy with verifiable transactions, @MidnightNetwork is contributing to a more balanced model where users can interact with decentralized systems without exposing sensitive information.
As the blockchain space matures, privacy-focused infrastructure will likely become a key part of the ecosystem. Projects building in this direction could help unlock new applications that were previously difficult to implement on fully transparent ledgers.
The progress of Midnight Network and the development of NIGHT token will be worth watching as the industry continues exploring how to protect data while maintaining trust in decentralized environments.#night
