I’ve spent years watching crypto evolve, and I’ve noticed a familiar pattern: whenever a new blockchain project surfaces, the initial narrative often grabs more attention than the underlying reality. That was my first reaction to Midnight Network—not excitement, but curiosity. I’ve seen many privacy-focused projects before, some promising, some overhyped, but something about this one made me pause and really consider what it’s trying to do.
From the beginning, Midnight is built around zero-knowledge proofs. Unlike other projects that try to layer privacy on top of an existing blockchain, Midnight designs privacy into the foundation. In simple terms, zero-knowledge technology allows the network to verify that something is true without revealing the actual data. I’ve seen this concept in other privacy chains, but applying it effectively has always been a challenge. It’s one thing to understand the math behind it, and another to make it work reliably at scale in a live network.
What stands out is the network’s approach to privacy combined with verification. Instead of making all data completely opaque, Midnight introduces selective disclosure. That means a user can prove certain facts—like identity verification or eligibility—without revealing sensitive details. From my experience, this is exactly what has held other privacy chains back. Full anonymity can be attractive, but it limits real-world adoption. By allowing controlled proof without exposing data, Midnight seems to be aiming for practical applications that can work within regulatory frameworks.
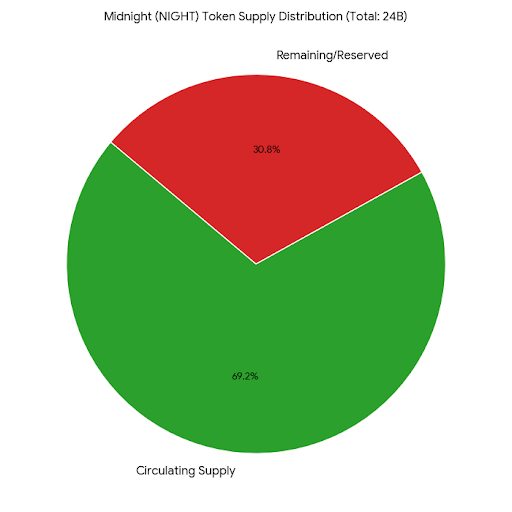
Another aspect that caught my attention is the way the network handles its token and transaction resources. Holding the main token generates a secondary resource that powers network activity, rather than paying fees directly for every action. I’ve seen attempts like this in the past, some successful, some not. The idea is to encourage long-term participation rather than purely transactional behavior. On paper, it’s clever, but it remains to be seen whether average users and developers will find it intuitive. Complexity can easily become a barrier.
Speaking of developers, Midnight is paying attention to them as well. Zero-knowledge systems are notoriously difficult to program for, so the team has introduced a smart-contract language designed to make building applications simpler while still leveraging the privacy infrastructure. If developers start experimenting and actually producing usable apps, it could create a slow but steady ecosystem growth. Yet, I’ve noticed in other projects that strong tools don’t automatically translate into engagement—there has to be both interest and demand for what’s being built.
The potential use cases here feel more grounded than many other crypto projects. Midnight isn’t just about trading, yield farming, or hype-driven speculation. Instead, the focus leans toward private identity verification, confidential data sharing, and secure transactions that are verifiable without exposing sensitive information. These are real-world applications where traditional blockchains have struggled because transparency, while great for security, conflicts with privacy needs. The design suggests the team is thinking beyond the short-term attention cycle and considering infrastructure-level problems.
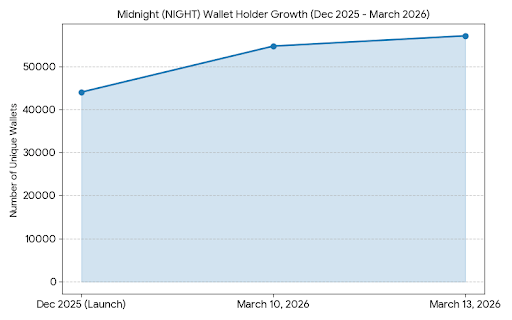
At the same time, I’ve learned over the years that technology alone doesn’t guarantee adoption. Liquidity, user behavior, and ecosystem gravity matter just as much. Early announcements generate buzz, but the real test comes months later when initial curiosity fades and we can see whether people are actually building, transacting, and experimenting on the network. Midnight seems to be in that early observation phase for now. It has an interesting architecture and a thoughtful approach to privacy, but the network’s long-term relevance will depend on real usage.
There’s also the question of market fit. Many technically strong projects have struggled because the market wasn’t ready, or because the applications didn’t solve urgent problems. Midnight is aiming at use cases that feel closer to enterprise or regulated environments, which could be a double-edged sword: it might slow initial adoption but, if successful, could carve out a niche where the network can sustain itself long-term.
Overall, my take is cautious but intrigued. The project demonstrates technical competence and a pragmatic approach to privacy, while also considering developer accessibility and real-world applications. But until we see sustained activity—developers building, users transacting, and applications proving their utility—the network remains a promising experiment rather than a proven ecosystem.
For now, I’m watching quietly. I’m not forming a strong opinion on whether it will succeed or fail. What matters is observing how it behaves once real usage starts to flow. In crypto, the difference between potential and reality usually becomes clear over time, and Midnight Network sits somewhere in that space, waiting to show whether it can turn its technical vision into lasting adoption.