I remember one of the first times I tried analyzing blockchain activity seriously. At the time, many traders around me believed transparency was the biggest strength of crypto. Every transaction could be verified. Every wallet could be tracked. It felt like the perfect system for trustless finance.
I believed that narrative too.
But the more time I spent studying on-chain activity, the more I noticed a different side of the story. Transparency didn’t just allow verification it also exposed behavior. Large transfers, trading strategies, business payments, even wallet connections could be mapped by anyone willing to analyze the data.
For traders this sometimes created opportunities. But for businesses and long-term infrastructure, it raised a question.
If everything on-chain can be seen, how comfortable will organizations be building real services on public blockchains?
That realization changed how I evaluate blockchain projects today.
That experience is one reason Midnight Network caught my attention.
Not because of hype cycles or speculative narratives.
But because it raises a much deeper question about blockchain infrastructure.
Most networks treat transparency as a fixed rule. If something happens on-chain, it becomes visible forever.
Midnight approaches the problem from a different angle.
Instead of forcing all information into the open, it explores how networks can verify activity while protecting sensitive data.
So the real question becomes:
Can a blockchain system maintain trust and verification without exposing every detail of a transaction?
That question sits at the center of Midnight’s design.
According to the project’s documentation, Midnight is designed as a privacy-focused blockchain infrastructure built around zero-knowledge cryptography.
Zero-knowledge proofs allow a network to verify that certain conditions are true without revealing the underlying information.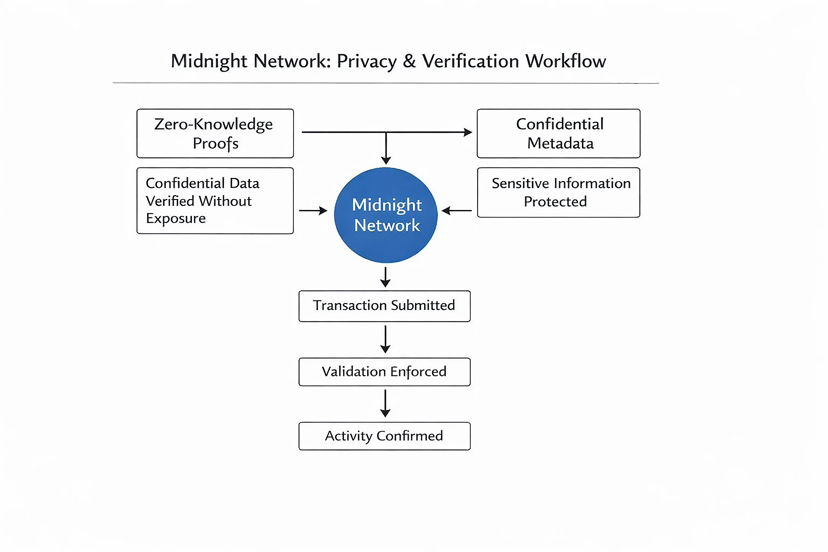
For example, imagine proving that a payment is valid without showing the full transaction details. The system confirms the rules are satisfied, but the sensitive data remains protected.
This approach allows applications to operate with confidential metadata, which is important for industries that handle sensitive information.
But Midnight doesn’t only introduce privacy technology. It also changes how network activity is powered.
The ecosystem uses a dual-component economic design built around the NIGHT token and a renewable resource called DUST.
Instead of spending the main token for every transaction, holding NIGHT continuously generates DUST. DUST is what actually powers operations on the network, including smart contract execution and application interactions.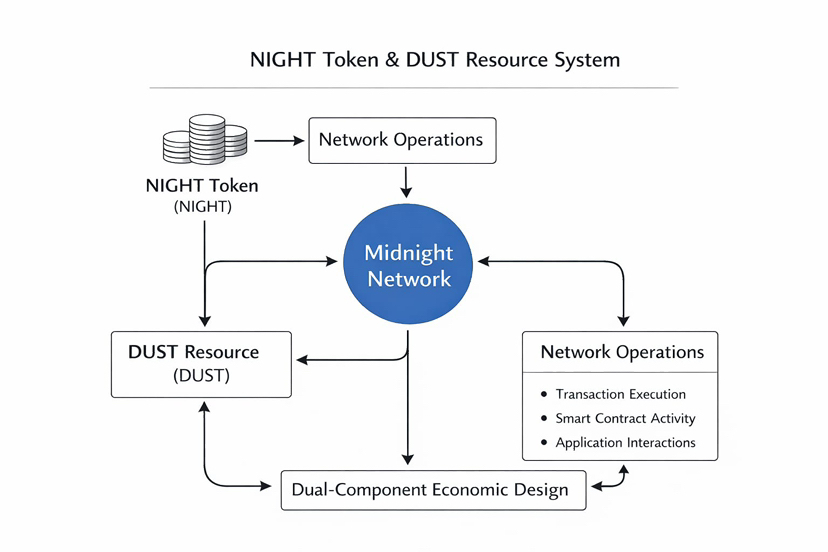
A simple analogy might help.
Think of NIGHT like owning a generator. The generator itself isn’t consumed each time you turn on a light. Instead, it produces electricity that powers the system.
In Midnight’s design:
• NIGHT acts like the generator
• DUST acts like the energy used for transactions
This separation helps stabilize network activity because transaction execution depends on generated resources rather than directly consuming the token.
From a design perspective, the goal is to combine verification, confidentiality, and predictable network usage in a single system.
The market has started paying attention to this infrastructure approach.
The NIGHT token has a total supply of 24 billion tokens, initially minted on the Cardano blockchain and mirrored on the Midnight network. Each NIGHT token can be divided into one million smaller units called STARs, allowing flexible usage within the ecosystem.
The project also introduced a distribution mechanism called the Glacier Drop, which aims to distribute tokens broadly across the Web3 community instead of concentrating them among early insiders.
This distribution strategy is important because token concentration has historically influenced governance and incentive structures in many blockchain ecosystems.
At the same time, the broader market narrative around privacy infrastructure is becoming more visible. Enterprises exploring blockchain solutions often hesitate to adopt fully transparent systems because operational data can become publicly traceable.
Projects that address this challenge are gradually gaining attention from developers, researchers, and infrastructure builders.
Midnight sits directly inside this emerging category.
But this is where the real test appears.
The biggest challenge for Midnight isn’t its privacy narrative or token design.
It’s developer adoption.
Privacy technology only becomes valuable when applications actually use it.
If developers begin building tools that rely on confidential transactions such as identity verification platforms, enterprise payment systems, or financial infrastructure the network’s architecture could support real demand.
But if developers struggle to integrate with the system, or if building applications proves too complex, adoption could slow down.
In other words, the success of Midnight depends less on speculation and more on application retention.
Because infrastructure projects live or die based on usage.
If developers continue building applications and users continue interacting with them, the system becomes stronger over time.
But if activity remains limited to experimentation, the economic model and privacy architecture may never reach their full potential.
So the key metric to watch isn’t just token distribution or network announcements.
It’s real application activity.
So what would make me more confident about Midnight’s long-term potential?
There are a few signals I would watch closely.
• A growing number of developers building privacy-focused applications
• Increasing interaction between users and those applications
• Partnerships or integrations that require confidential transaction infrastructure
Those signals would suggest that the network is solving real problems.
On the other hand, I would become more cautious if:
• developer activity slows significantly
• the majority of attention focuses only on token speculation rather than application usage
Because in blockchain infrastructure, usage tends to reveal the real value of a system over time.
So if you’re watching Midnight Network, don’t just watch the NIGHT token price.
Watch the developers and applications building on top of it.
Privacy infrastructure only becomes meaningful when people actually rely on it.
In markets like Web3, the difference between an interesting technology and a lasting system is usually simple:
Do developers keep building once the excitement fades?
@MidnightNetwork #night $NIGHT




