We hear a lot about blockchain revolutionizing the world, but if we’re being honest, the conversation often gets stuck in a cycle of maximalism. It’s either "on-chain everything" or "privacy for the sake of anonymity." Lately, I’ve been diving deep into a project that I believe is asking a much more mature question: What if blockchain didn't force you to choose between transparency and secrecy? What if it could offer both, seamlessly?
I’m talking about Midnight. As I’ve been studying its architecture, its philosophy, and its tokenomics, I’ve realized that this isn't just another "privacy coin" or "layer-1" contender. It feels like a necessary evolution in how we think about data, trust, and the infrastructure of Web3. I want to share my perspective on why I think Midnight’s approach is so compelling, and why its native token, NIGHT, is designed to solve problems most people don't even see coming.
The "Layer of Privacy" Philosophy, Not a Walled Garden
The first thing that struck me about Midnight is its core philosophy. From what I’ve gathered, the team isn't trying to build a closed-off "privacy island." That’s a common mistake in our space. A project emerges, promises total anonymity, and expects enterprises and users to abandon all their existing infrastructure to come live in this new, secret garden. It never works. It creates friction and forces a migration that most are simply unwilling to make.
Midnight’s vision is different. I see it as a specialized "privacy layer" for the entire Web3 ecosystem, and even for traditional Web2 systems. The idea isn't to rebuild everything from scratch; the idea is to integrate.
Think of it like this: a large enterprise isn’t going to dismantle its entire customer database or supply chain management system just because a cool new privacy tech appears. That’s impractical and expensive. What they will do is look for the points of greatest pain—the "hot spots" where data exposure is a liability.
Midnight is designed to be the solution for those specific pain points. It’s the shield you put on the most sensitive part of your armor, not the entire fortress. You keep your existing CRM, your existing ERP systems, and your current financial ledgers. You only use Midnight to handle the parts that absolutely must remain confidential. This pragmatic, additive approach is, in my opinion, the only way we’re going to see real-world, mass adoption of privacy tech.
The Nuance of Private Computation: It's Not Just About Hiding Data
Okay, so Midnight lets you keep data private. That’s table stakes for a privacy-focused chain. But the real magic, and where things get truly interesting, is in managing the results of that private data.
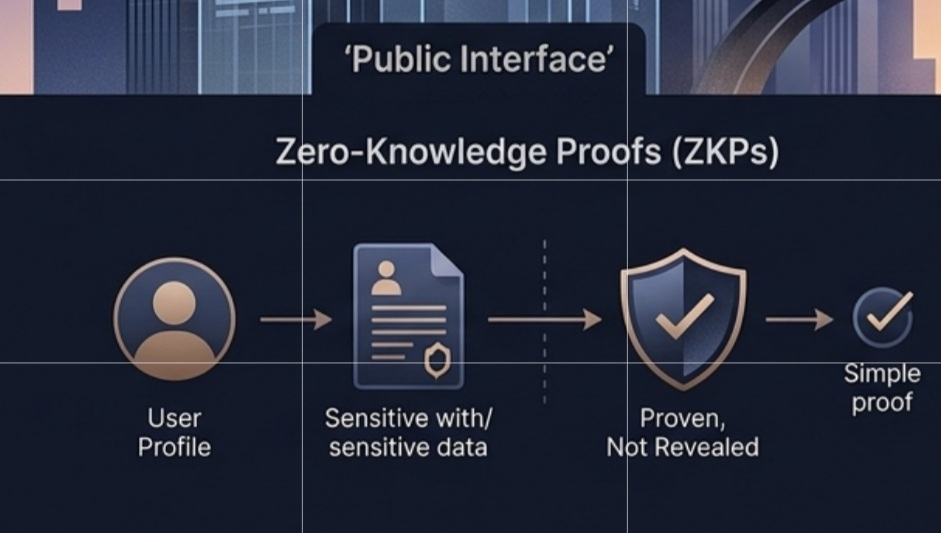
Midnight uses Zero-Knowledge Proofs (ZKPs). This allows an application—say, a DeFi protocol or a corporate treasury—to verify a specific condition without revealing the raw data underneath. Imagine you need to prove you have a credit score above 700, or that you’ve passed a KYC check, or that your treasury balance meets a certain threshold. With Midnight, you don't send your credit report, your passport scan, or your bank statement. You just generate a cryptographic proof that says, "Yes, this condition is true," and pass that proof along.
This is incredibly powerful. But as I was thinking about this workflow, I realized there’s a massive, often overlooked vulnerability here. It’s not a cryptographic failure; it’s a coordination failure.
The Gray Area of Interpretation
Here’s the scenario that keeps me up at night: A smart contract on Midnight verifies a condition. It spits out a proof. That proof is then passed to another system—maybe it’s a different blockchain, a traditional banking API, or an insurance settlement engine.
The problem? Every system interprets data differently.
The Application says: "I just trust Midnight."
Midnight says: "We just proved exactly what we were asked to prove."
The Other System says: "We just acted based on what we received."
So, where does the fault lie when something goes wrong? If the proof was valid, but the receiving system misinterpreted the context of that proof, whose responsibility is it? Did the DeFi protocol misunderstand the scope of a "KYC valid" proof? Did the insurance company misinterpret the terms of a "credit limit" proof?
This is what I call a "Trust Boundary" breakdown. The cryptography is sound, the smart contract executed perfectly, but the human and systemic interpretation across different platforms creates a gap. The failure isn't a privacy leak; it’s a logic leak.
This is the nuance that I think Midnight is uniquely positioned to address. The true test of its infrastructure won't just be how well it hides data, but how elegantly it manages the interpretation of that data’s proof across disparate systems. Can it create a standard for passing not just the result, but the context? This is the hard, unsexy work of infrastructure, and it’s what will determine if it can truly scale.
The NIGHT and DUST Economy: Stabilizing the Cost of Trust
Now, let's talk about the token, NIGHT, and its fascinating economic model. Most of us are used to the "gas" model on networks like Ethereum. You need ETH to pay for computation, and the cost fluctuates wildly based on network congestion and the market price of ETH itself. This creates massive uncertainty, especially for enterprise applications that need predictable operational costs.
Midnight has done something that, in my view, is incredibly forward-thinking. They’ve decoupled the asset from the resource.
We have NIGHT, the native token. Think of this as the asset, the investment, the store of value. It has a fixed total supply of 24 billion, with around 16.6 billion currently in circulation. It’s what you use for staking, governance, and as a long-term holder of network value.
Then, we have DUST. This is the "fuel" for the network. It’s what you spend to run transactions, execute smart contracts, and generate those ZK proofs. And here’s the brilliant part: DUST is generated by holding NIGHT, but it doesn't have a market price.
This model feels like a breath of fresh air. It mirrors how a computer works. You buy the hardware (the asset, like NIGHT), and then you have access to its processing power and memory (the resources, like DUST). The cost of the hardware might fluctuate, but the relative cost of using its CPU doesn't change based on the market. It’s based on actual usage.
Why This Matters for Privacy
This model is critical for the very applications Midnight is targeting. If you're a bank running confidential compliance checks, or a supply chain company verifying sensitive data, you need cost stability. You can’t have your operational budget blown out of the water by a crypto bull run that sends your gas fees to the moon. By using DUST as a stable internal resource, Midnight ensures that the cost of privacy is predictable. This lowers the barrier to entry for serious, risk-averse institutions. It transforms privacy from a speculative feature into a dependable utility.
With a market cap hovering in the 800–900 million range, NIGHT sits comfortably in the mid-cap zone. It has room to grow, but more importantly, its economic model is poised for a real-world test. If the DUST mechanism works as intended, providing stable and predictable fees, it could become a benchmark for how other networks structure their economies.
The Broader Vision: Balancing Transparency and Privacy
Zooming out, I see Midnight as a crucial piece of a much larger puzzle. For years, we’ve been told that blockchain’s killer feature is transparency. And it is! Transparency builds trust. But as we try to onboard the world, we’re hitting a wall. A world where every salary, every corporate balance sheet, and every supply chain contract is fully visible to everyone is not a realistic—or desirable—world.
Midnight’s answer is programmable privacy. It gives the user, the developer, or the enterprise the power to decide. What should be public? What must remain private? It’s not an all-or-nothing game. You can have a public-facing smart contract that governs the rules, while the sensitive data required to trigger those rules remains sealed behind a ZK-proof.
This balance is everything. It makes blockchain practical for finance, for healthcare, for identity, and for enterprise. It’s the difference between a technology that’s fascinating to speculate on and one that’s actually useful to build with.

My Conclusion: The Long Game of Infrastructure
When I look at Midnight and the role of NIGHT, I don't see a quick pump-and-dump. I see a long-term bet on infrastructure. I see a project that understands that privacy isn't just about encryption; it's about economics, coordination, and trust boundaries.
The success of Midnight won’t just be measured in Total Value Locked or transaction count. It will be measured by its ability to manage the gray areas—to ensure that when a proof passes from a private smart contract to a public system, the meaning isn’t lost in translation. It will be measured by whether its DUST model can provide the stability that serious applications demand.
For me, the conversation is shifting. I’m no longer asking, "Which chain is the most private?" I’m asking, "Which chain can make privacy a seamless, stable, and interoperable part of the Web3 experience?" From everything I’ve seen, Midnight is building the most compelling answer to that question. It’s not just about hiding data. It’s about making data usable, trustworthy, and confidential, all at the same time. And in the evolving landscape of Web3, that’s a vision I can get behind.
$NIGHT #night @MidnightNetwork #NIGHT



