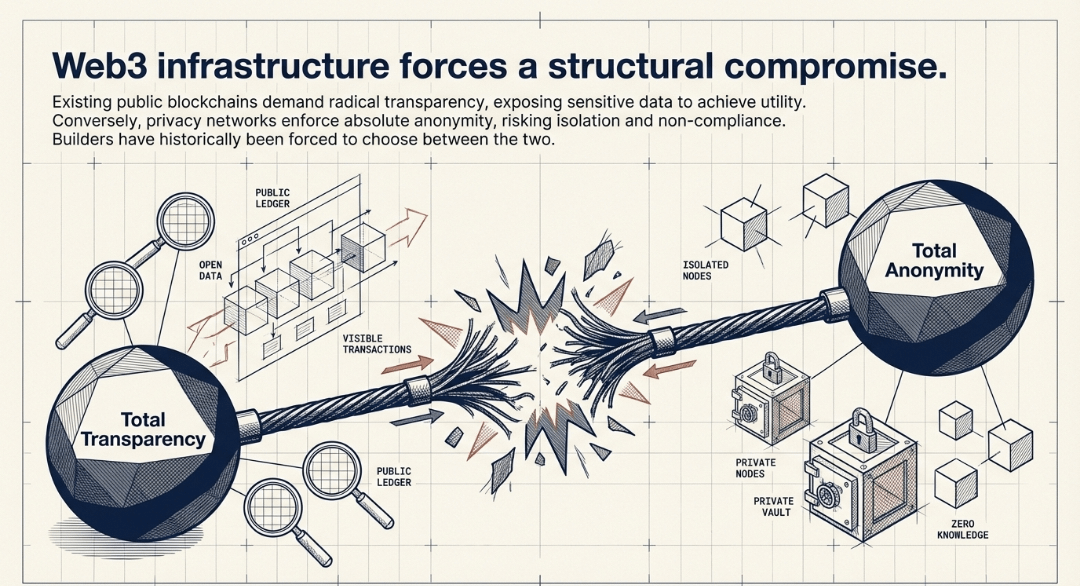
My report provides a comprehensive overview of the @MidnightNetwork | $NIGHT a privacy-first blockchain designed to address the limitations of existing public blockchains by offering rational privacy.
It delves into the network's core mission, key features, value proposition, and the intricate tokenomics involving its native utility token, NIGHT, and the shielded resource, DUST.
What is Midnight Network?
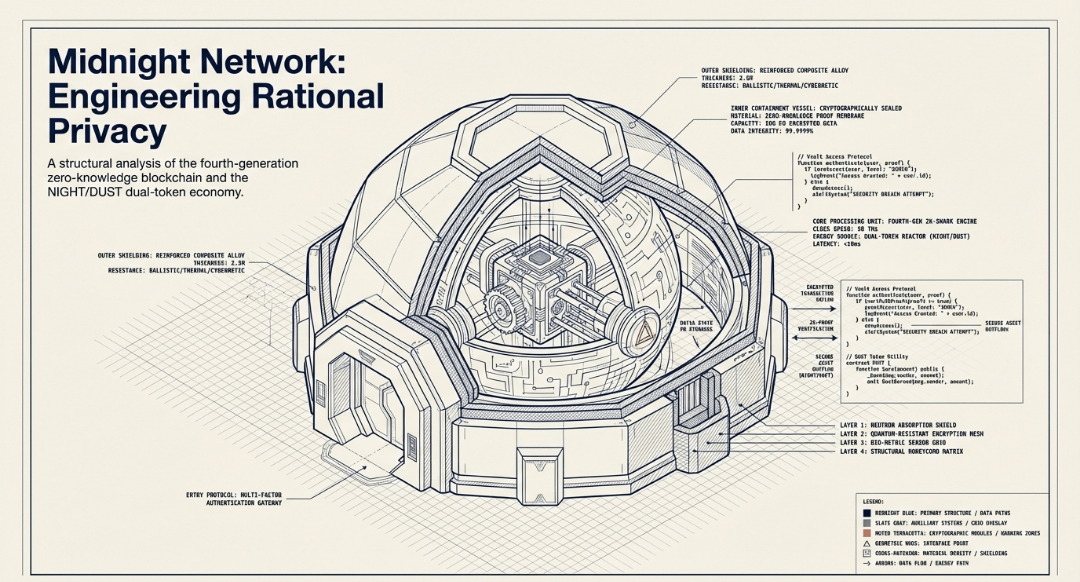
Midnight Network is a fourth-generation blockchain designed for rational privacy, aiming to provide users with control over their sensitive data while enabling verifiable operations.
It seeks to restore the original promise of crypto by allowing individuals to choose between utility and privacy without compromise.
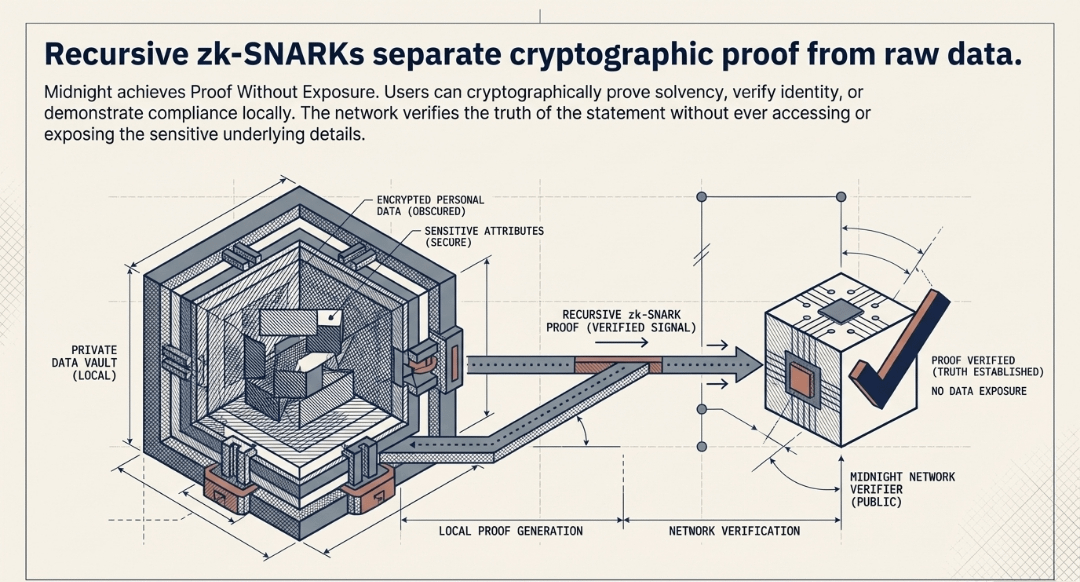
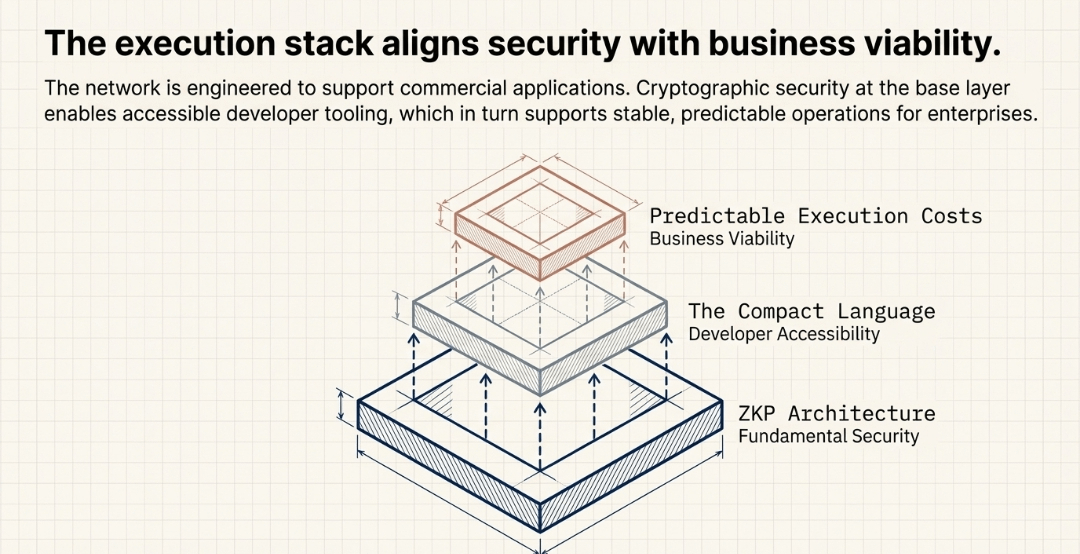
The network's architecture leverages zero-knowledge proofs (ZKPs) to ensure that truth can be verified without exposing underlying personal data
Key Features and Value Proposition
Midnight Network offers several key features and a strong value proposition centered around privacy, control, and developer-friendliness:
Rational Privacy
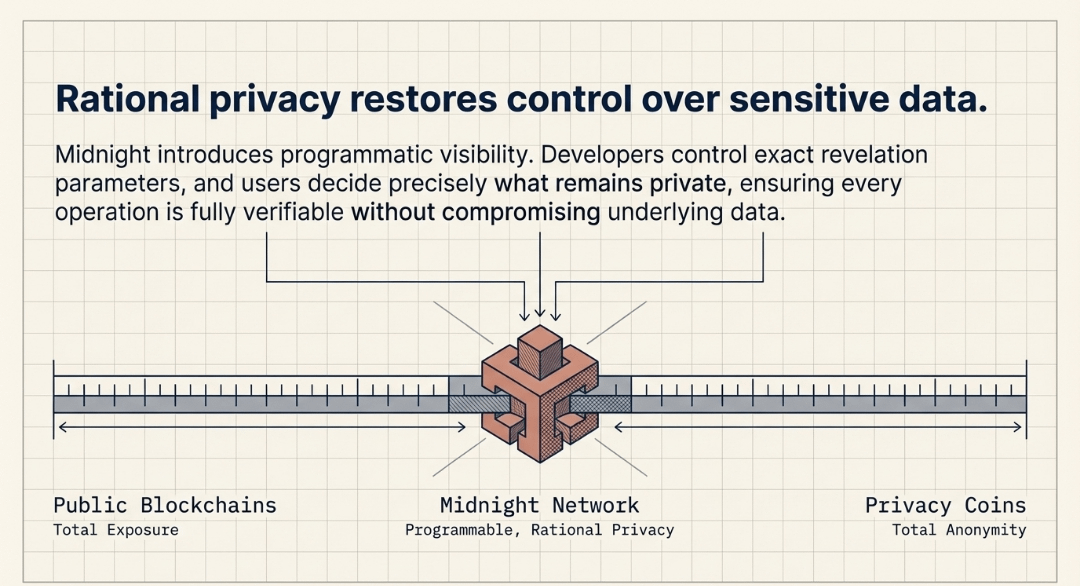
Midnight's core offering is rational privacy, which allows users to programmatically define the visibility of their data. Developers can control what is revealed, and users decide what remains private, all while ensuring everything is verifiable
Proof Without Exposure
Utilizing recursive zk-SNARKs, Midnight separates proof from data, enabling users to prove solvency, identity, and compliance without exposing sensitive information. This ensures that only necessary details are revealed
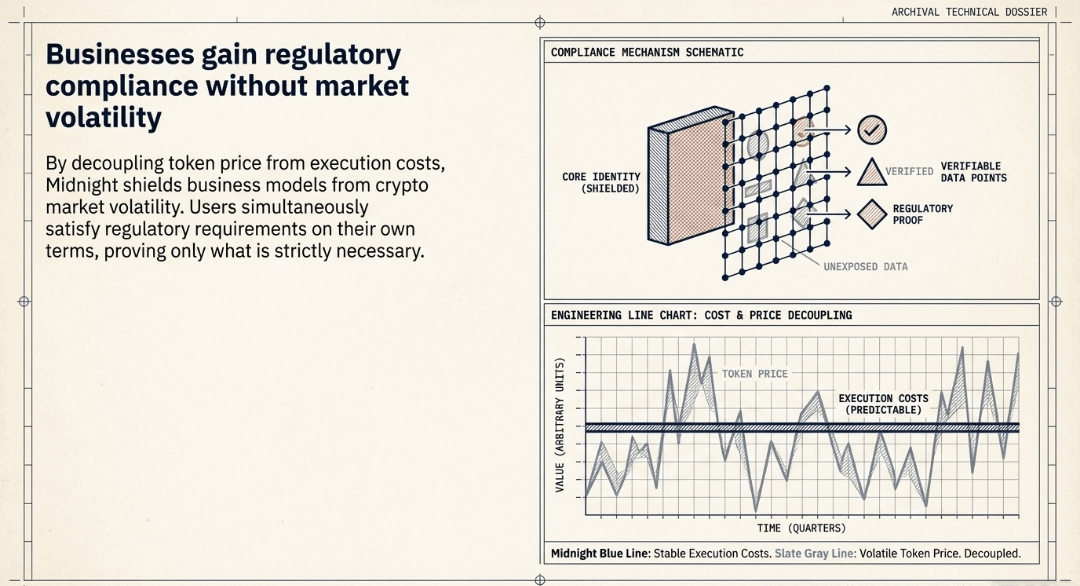
Predictable Costs
The network decouples token price from execution costs, providing predictable operational costs for businesses building on Midnight.
This stability helps avoid market volatility impacting business models
Compliance Without Compromise
Midnight allows users to satisfy regulatory requirements on their own terms, making privacy rational by proving what is required while protecting what is most important
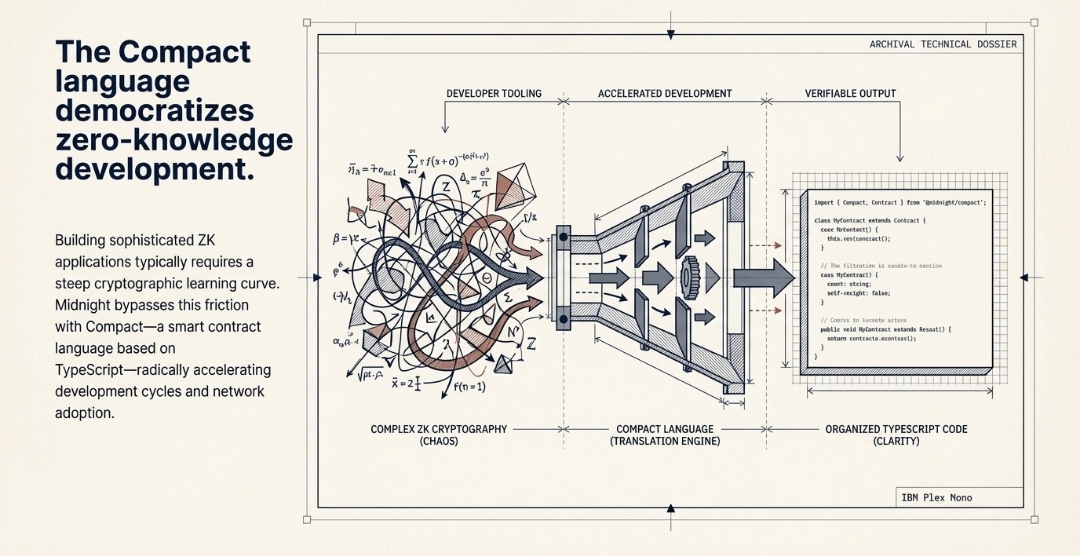
Democratizing Cryptography
With Compact, a smart contract language based on TypeScript, Midnight aims to simplify the development of sophisticated ZK applications. This reduces the steep cryptographic learning curve, accelerating development cycles and network adoption
Ecosystem Stewardship
The Midnight Network is stewarded by the Midnight Foundation, which focuses on long-term stability, decentralization, and making the technology open and accessible to everyone
Tokenomics: NIGHT and DUST
Midnight Network employs a dual-token model consisting of NIGHT and DUST, designed to ensure fair access, incentivize participation, and sustain network operations.
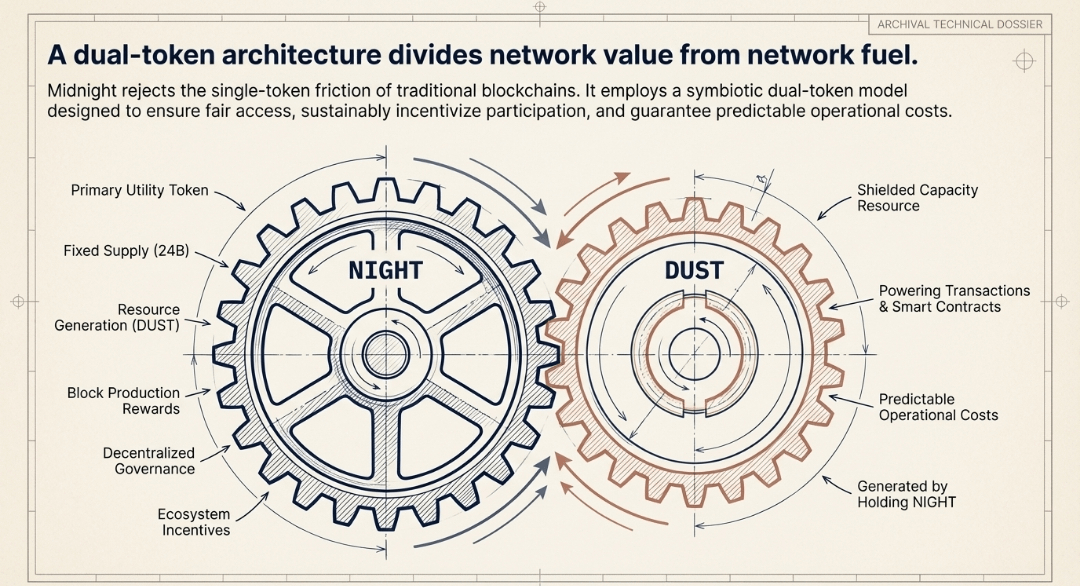
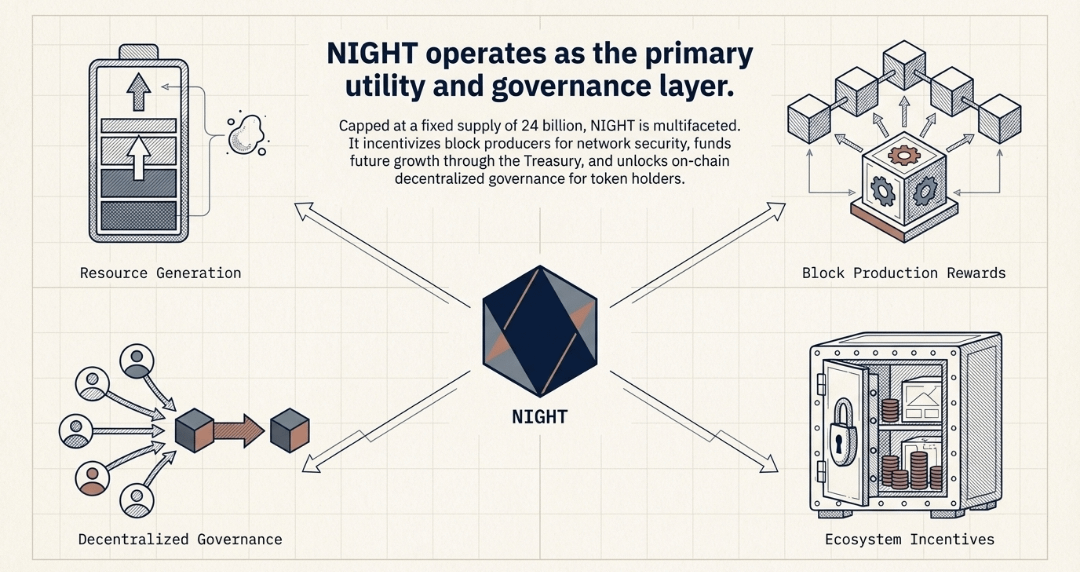
NIGHT: The Utility Token
NIGHT serves as Midnight’s primary utility token with a fixed supply of 24 billion tokens. Its functions are multifaceted, driving various aspects of the network’s economy.
• Resource Generation: Holding NIGHT tokens perpetually generates DUST, the shielded capacity resource essential for powering transactions and smart contract execution on the Midnight network.
• Block Production Rewards: NIGHT tokens are distributed as rewards to incentivize block producers, ensuring the continuous and secure operation of the network through a protocol-managed token Reserve.
• Decentralized Governance: Over time, NIGHT holders will gain the ability to participate in decentralized, on-chain governance, influencing the future development and direction of the protocol.
• Ecosystem Incentives: An on-chain NIGHT Treasury is anticipated to fund ecosystem growth activities and projects, selected through future on-chain governance mechanisms.
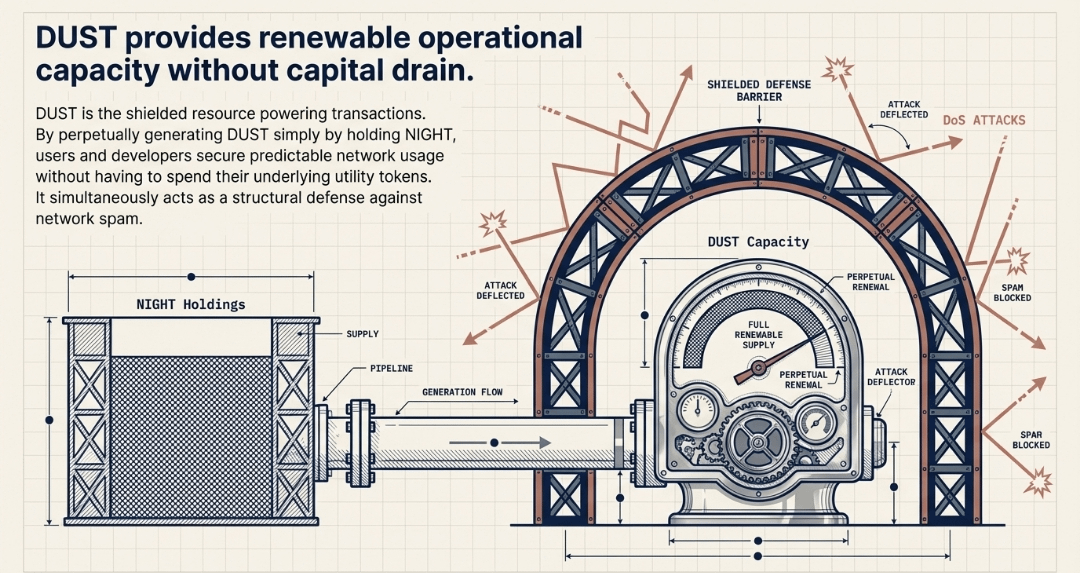
DUST: The Renewable Shielded Resource
DUST is the shielded resource that fuels transactions and smart contract execution within the Midnight Network.
It is continuously generated by holding NIGHT, offering users and developers predictable network usage costs without the need to spend their utility tokens directly for transactions.
DUST also plays a crucial role in preventing denial-of-service attacks.
The whitepaper details its generation, capacity, designation, transaction enablement, decay, and double-spending prevention mechanisms.
Cooperative Tokenomics and Distribution
Midnight’s tokenomics model is designed to support a multichain architecture, fostering interoperability across various networks.
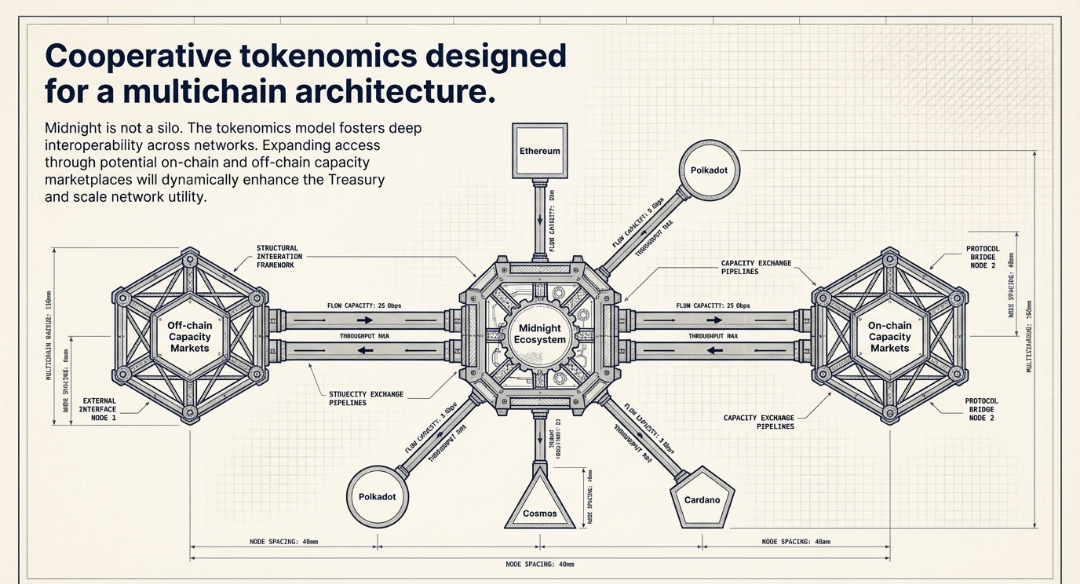
This includes mechanisms for expanding network access through potential capacity marketplaces, both off-chain and on-chain, which could also enhance the on-chain Treasury.
The distribution of NIGHT tokens is managed through a multi-phase framework called Glacier Drop, aimed at bootstrapping a diverse and resilient community.
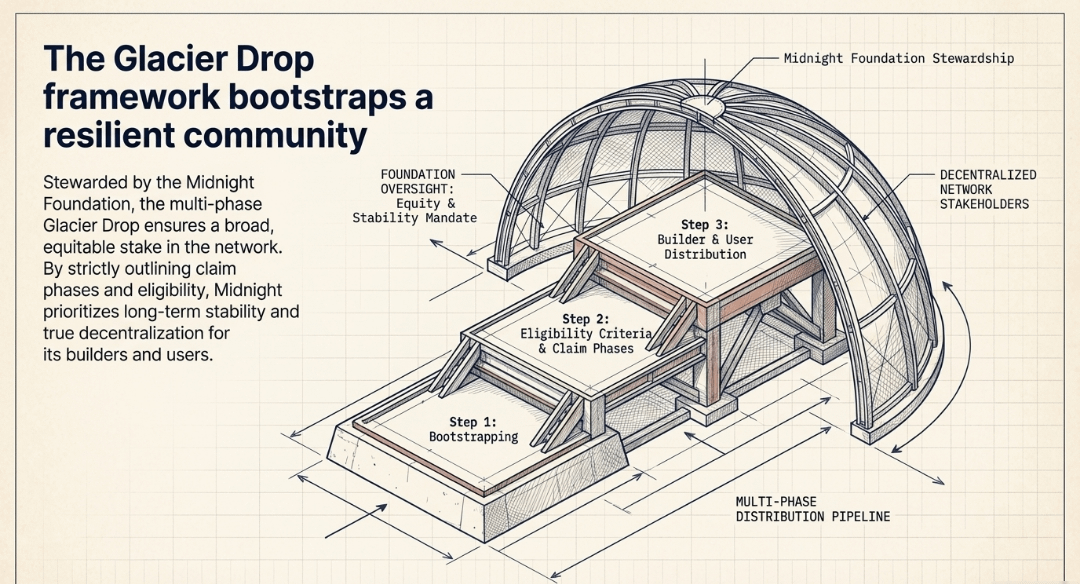
This framework outlines distinct claim phases, eligibility criteria, and a timeline for distribution, ensuring a broad stake in the network for builders and users.
Conclusion
Midnight Network presents a compelling vision for a privacy-first blockchain, offering a unique approach to data protection through rational privacy and zero-knowledge proofs. Its dual-token model, with NIGHT as the utility token and DUST as the shielded resource, is designed to create a sustainable and predictable ecosystem.
By focusing on developer-friendly tools and a fair distribution mechanism, Midnight aims to foster a broad and diverse community, ultimately contributing to a more interoperable and privacy-conscious Web3 future.
