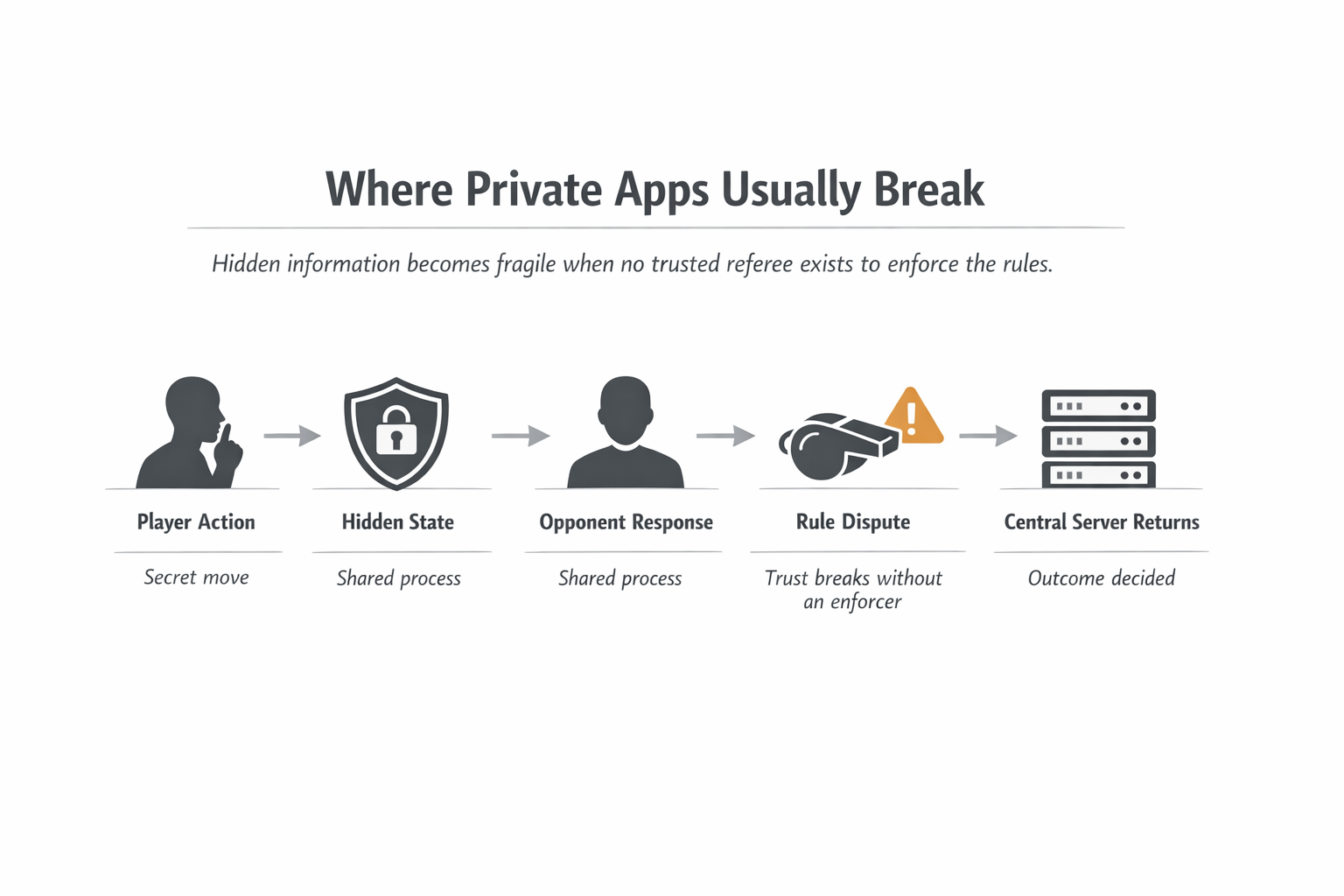
What altered this perception was the sheer number of other private apps which fail the minute no one is there to referee the under bits.
That is the part people skip.
Two people open the app. One commits first. The other responds. One action is meant to remain a secret, and another action is meant to come out in the open and the entire action will only work out when the two involved will have faith in the fact that the rules were perhaps adhered to even when one of the sides was still in the shadows of the state. That is where in most systems the silent central server creeps back in. It is not because centralization is preferred by the app team, but the reason as to why someone has to fix the hidden turns, verify the state transitions and preventing the game or workflow to become a trust contest.
And there begins the tug of war.
Many privacy discourses are clean in that they discuss the protection of data within a vacuum. The more difficult issue is interactive secrecy. On the one hand, there is secrecy of information. It is far more difficult to allow some latent piece of information to actively influence an ongoing process without relinquishing any control to the middleman. That funnel is important as it narrows down the category silently. It stores entire lines of products which are weaker than they appear. Multi-player games, sealed logic, bidding flows, challenge response systems, and any application where incentives are modified based on the fact that one party knows something the opposing party does not know but all goes into the same wall. Assuming that the sole method of ensuring the honesty of the hidden state is to introduce a referee, then the product is not actually trustless. It is nothing but personal until the tough part comes in.
The more I sat by Midnight, the more that bottle neck was sticking out to me.
It is then that Midnight began to seem different to me.
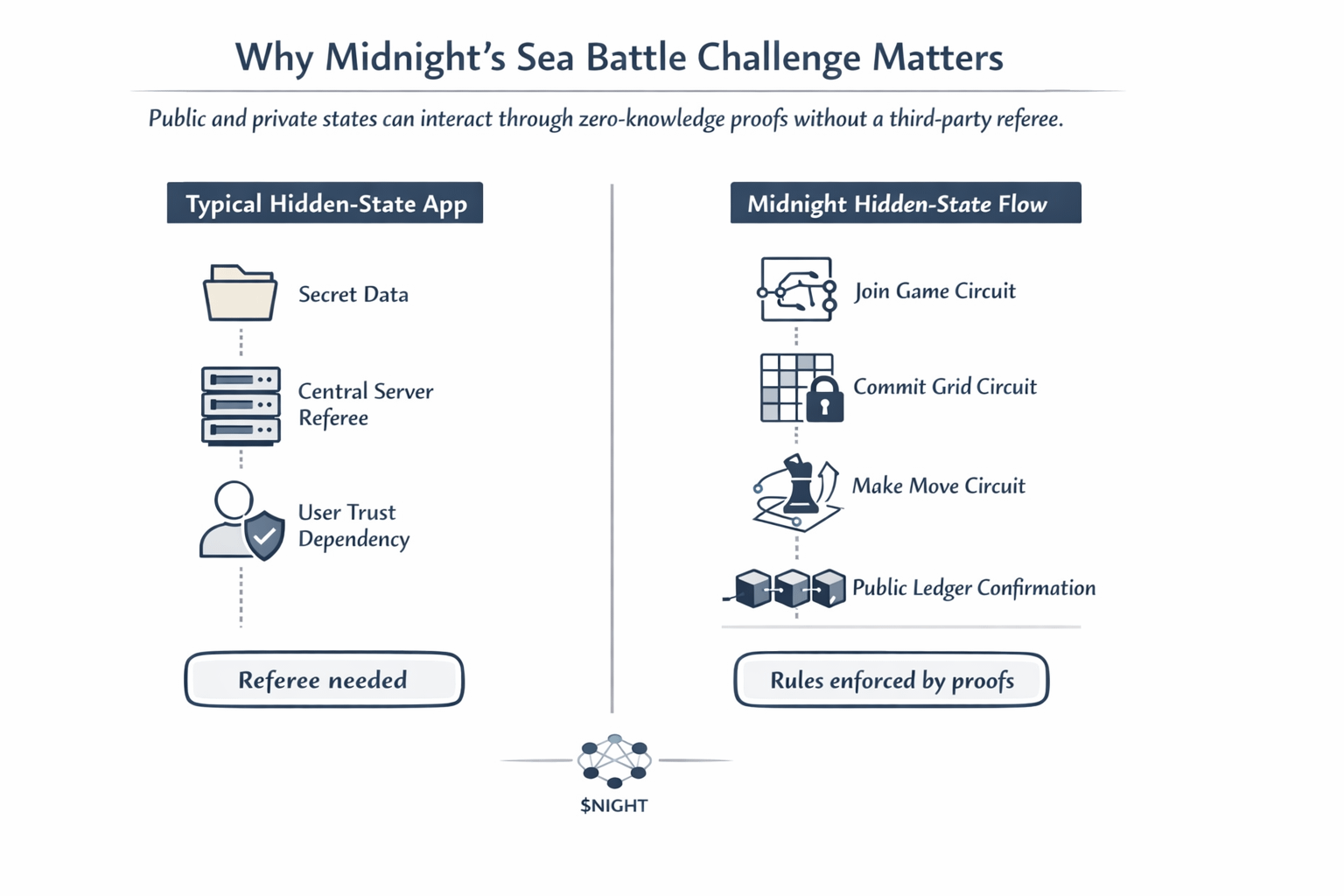
The challenge that resonated with me was that of the Sea Battle. Midnight has not selected a generic privacy demonstration. It decided to play a game where hidden information and turn-based pressure are central to its gameplay, and that is precisely the environment in which fake privacy is revealed very quickly. The write-up by Midnight states the challenge required the developers to execute smart contracts with both public and private states within a turn-taking format, and emphasizes the idea of trustless interaction, meaning cryptographic proofs, without having a third-party server.
The given detail is important as it is not theoretical. It is architectural pressure.
As one of the most powerful submissions, Edda Labs designed four distinct circuits on which the game flow was placed: join game, commit grid, start game and make move. The recap of midnight states that each circuit produced a zero-knowledge proof that checked the rules and did not disclose any information about the privateness and that the contracts also attended the public ledger but did not uncover the information about the privateness of the game. This is where the project payoff worked with me. Midnight ceased to appear as a chain that just conceals state and began to appear as a network that is able to conceal state when under pressure of the rule.
After that, I could not actually revert to the simpler version of the narrative.
I no longer thought of privacy as a storage issue but as a referee issue. Reading in this category did not start the same way with me. It is only easy to conceive a lot of products that are considered private because people overlook the incidence when hidden information is required to interplay with another participant and remain enforced. At midnight I had to take care of the mechanism rather than the slogan. Recap of its own Sea Battle talks of decentralized state management as flexible management of both social and personal data in a trustless multiplayer economy, which is a far more precise indicator than general privacy branding.
The greater the glance I gave that challenge, the further I noticed why it was a tough test. Sea Battle is not attractive since it is a game. It is fascinating since it compels the network to demonstrate something more difficult: can personal information be the driver of an overall process without returning the power to a server? The winners of the midnight went about that. A full playable version constructed by Brick Towers using housekeeping and the Chrome browser with Lace wallet needed only shielded stakes and a secret payout to the winner. Edda Labs designed the reasoning using circuit-based verification of each major turn. Even the honorable mentions section by Midnight acknowledges some clever applications of wallet connection and matrix storage as a part of experimenting.
That altered my perspective of the project.
Midnight became not such a privacy chain but rather one that attempted to coordinate the hidden-state in a network. It is a far smaller and more satisfactory story. Any person may say that personal information is important. The more challenging inquiry is whether or not a private state can be engaged in a live, adversarial, multi-step process without disintegrating into trust repair. As soon as that resonated, the category began to seem to me thinner whenever it did not have a good answer.
I found the token more sensible after that.
The perceptions that I hadn't had until that point regarding $NIGHT were that it was exposure to a narrative about privacy, but I now read it as exposure to a network attempting to enforce a more specific bottleneck: how to enforce hidden state in products where other people are actively engaged. It is not a generic token story. It is a much harder one. With apps, in which no one just stores their private information, but in fact particular information powers a process that is shared out without a human referee, then $NIGHT is sitting in the middle of a far more interesting kind of thing than another confidentiality pitch. That is my inference, although it is based on the type of projects that Midnight is already running to stress its stack.
I still keep some doubt here.
A game challenge is not identical to the production market. A referee in a competitive process who has no knowledge of the actions is not the guarantee of the same smoothness in a less organized consumer or financial setting. And one can rightfully wonder whether such patterns remain clean when product complexity increases, actors increase or UX demands become more brutal. They are the appropriate questions to ask. But there is the reason why the challenge remained with me. The hidden-state problem is not avoided but made apparent by the choice of a setup made by Midnight.
When this hit, I could no longer be able to view the category in the same light.
The bottleneck that appeared real no longer appeared merely as a privacy issue but now appeared as a question of whether or not the hidden state could live in the absence of a referee.
Many of these projects are concerned with secrets.
I continue to observe to whom secrets act under the regulations where other individuals are concerned.
#night $NIGHT @MidnightNetwork
