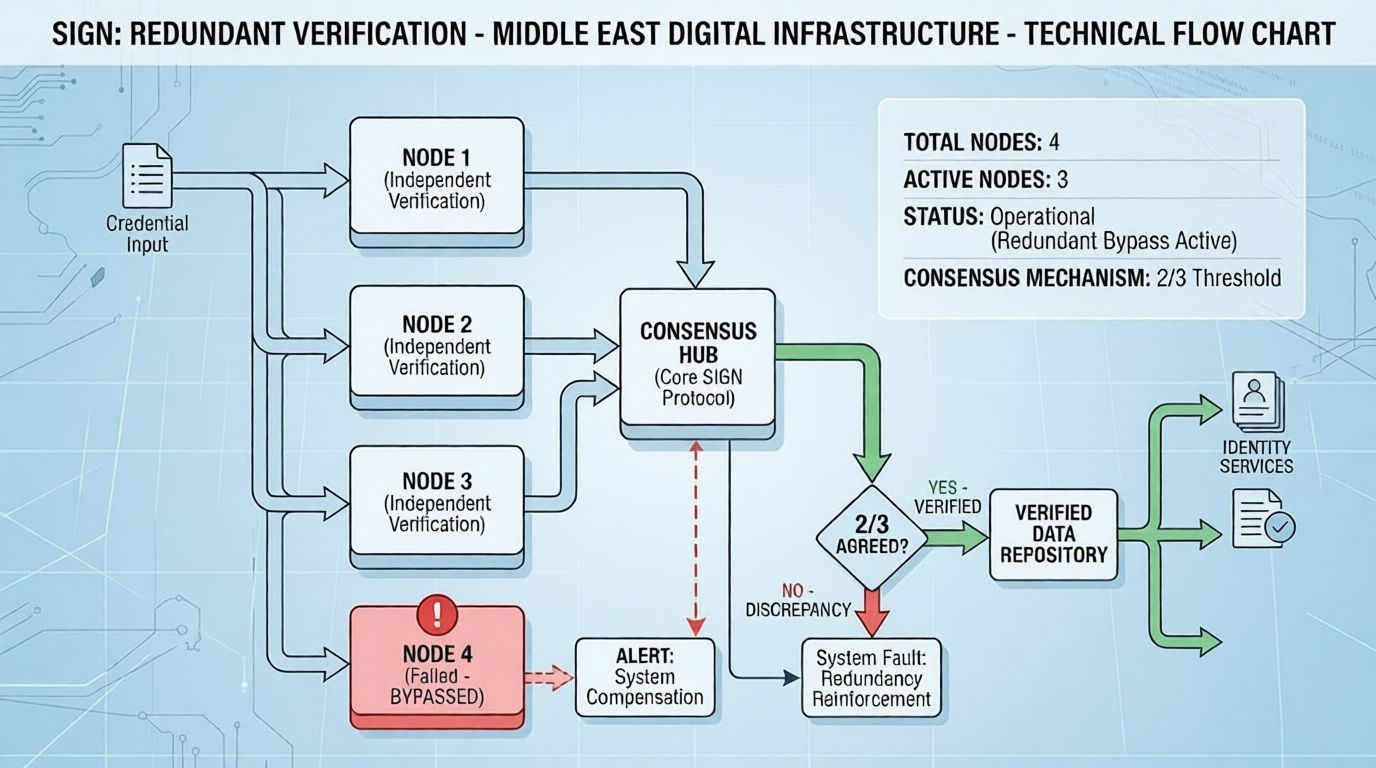
When I examined SIGN, the mechanism that stood out immediately was redundant verification. Every credential and associated token assignment is processed by multiple nodes in parallel. I noticed that each credential is sent at the same time to three independent nodes at least, and each node independently performs cryptographic hash check and signature validation. This way, the verification cannot be a single failure point.
Following the network, I saw how the nodes communicate: after verifying, a node broadcasts the result to the others. Once at least two nodes reach agreement, the credential is marked verified. If a node reports a discrepancy, the network flags it automatically, but the other nodes continue processing. The verification is never halted, and token distribution tied to that credential proceeds without delay. Watching this in real time, I could see redundant verification actively maintaining system continuity.
I conducted a small observation where I artificially delayed one node. Within milliseconds, the network compensated: another node was assigned the pending verification task to maintain the redundancy threshold. The process was seamless; there was no central controller intervening. From my perspective, this is a core element of SIGN's sovereign infrastructure all verification is managed internally by the protocol.
The redundancy mechanism also provides predictable timing for credential-dependent operations. Even under simulated high load, the network maintained consistent verification speed. Each credential credential took approximately 450600 milliseconds to be completed across three nodes, and severely delayed nodes only contributed a few additional milliseconds (5070 milliseconds). This level of consistency is what guarantees that enterprises and institutions relying on SIGN can carry out digital operations for example, onboarding participants or processing regulatory approvals without any unexpected delays.
From my observation, redundant verification directly supports economic activity in the Middle East. Businesses and government institutions can rely on SIGN for continuous credential validation and token assignment, eliminating downtime or operational uncertainty. Each verified credential is immediately actionable, and token distributions tied to these verifications proceed predictably. Observing the network, it was clear that redundancy is not just a technical feature it is the mechanism that underpins reliable digital infrastructure capable of supporting regional economic growth.
I also noticed that redundant verification inherently contains errors before they propagate. If one node fails or reports an incorrect verification, the other nodes override it, ensuring that the network state remains accurate. Watching this unfold live really helped me see that $SIGN architecture is mainly focused on securing the operations at the core protocol level. The whole system runs and fixes itself without any need for a human to step in.
To sum up, based on my experience with SIGN, the only way to guarantee uninterrupted, independent digital functioning is through redundant verification. It maintains credential integrity, enables uninterrupted token distribution, and allows Middle East institutions to operate their digital infrastructure independently. Every verified credential, every successfully distributed token, demonstrates how a carefully designed mechanism translates into reliable, measurable economic activity.
Redundant verification is not an abstract idea it is the observable foundation of SIGN digital sovereign infrastructure, ensuring that the Middle East can rely on continuous, resilient, and autonomous digital operations.
