I was on my third cup of coffee, lazily scrolling through blockchain updates, when Midnight Network caught my attention in a way most projects do not. There were no loud promises, no oversized claims, no desperate push for attention. It was quieter than that. The kind of quiet that makes you pause, look again, and wonder whether something serious is being built underneath the surface.
What first pulled me in was the strange balance Midnight seems to be trying to hold. It is working in a part of crypto where the usual rules feel upside down. Most networks are designed around visibility. Transactions are traceable. Activity is measurable. Trust, in many cases, comes from exposure. Midnight moves in the opposite direction. It asks whether a system can remain trustworthy even when it reveals far less. Not by hiding weakness, but by designing privacy as a core condition of how the network operates.
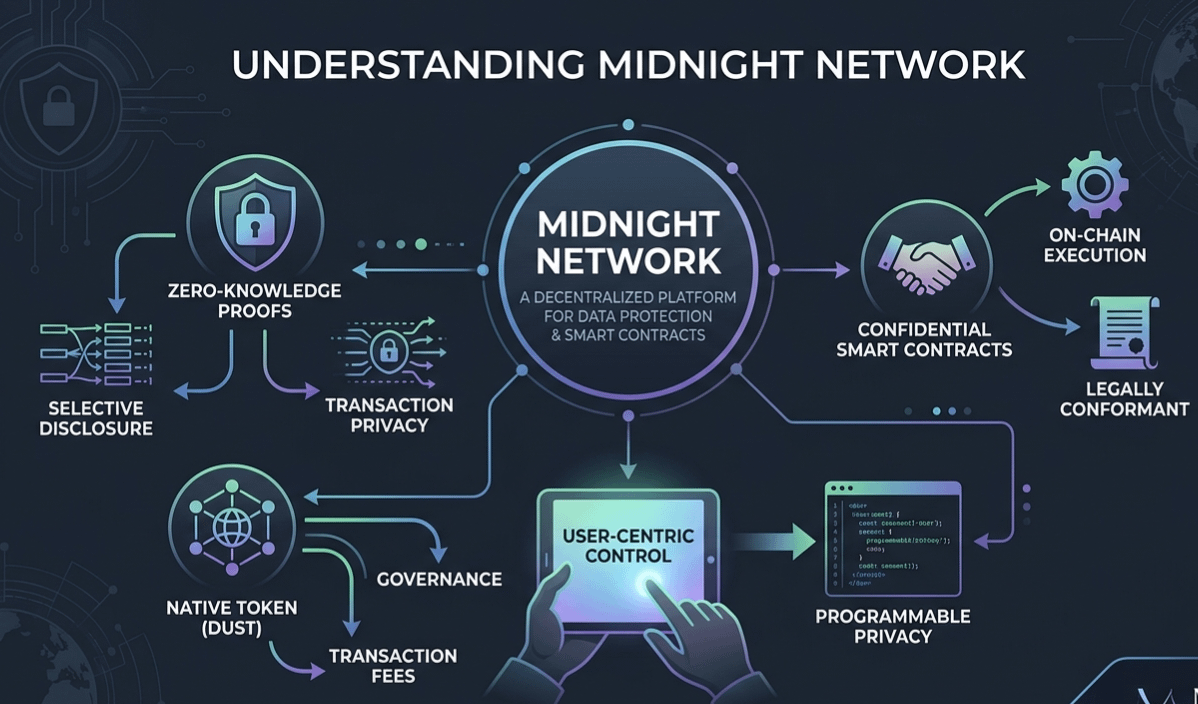
That is a difficult thing to attempt. A system built around confidential computation, private identity, and selective disclosure sounds elegant in theory, but fragile in practice. The obvious question is whether too much privacy eventually starts to weaken accountability. And yet Midnight’s structure suggests that it understands this tension. Instead of treating secrecy as a shortcut, it appears to use proofs, distributed validation, and constrained disclosure as a way to preserve integrity without forcing everything into public view. In other words, the network is not asking people to trust the invisible. It is trying to prove that invisible coordination can still produce verifiable outcomes.
That is where the project starts to become genuinely interesting. Midnight does not feel like it was designed for spectacle. It feels designed for function. The architecture gives the impression of something carefully negotiated rather than loosely assembled. Privacy is not being added as decoration after the fact. It looks embedded into the logic of the network itself. The ledger does not need to expose every detail to confirm that something valid happened. It only needs enough cryptographic assurance for participants to rely on the result. That design choice sounds simple when written out, but in practice it changes the entire social structure of a blockchain system.
The role of $NIGHT also seems more deliberate than cosmetic. Too many tokens in this industry feel like accessories attached to a system after the important decisions have already been made. Here, the token appears tied to incentives that matter. It helps coordinate validator behavior, supports network participation, and creates economic consequences around trust and performance without forcing privacy to collapse into transparency. That does not remove risk, of course. Incentives rarely behave perfectly once real pressure enters the system. But it does make the network feel more internally coherent.
What keeps me watching Midnight is not the promise of perfection. It is the uncertainty around how this design behaves once it leaves the comfort of theory. Every privacy-focused architecture looks compelling until real-world edge cases begin to gather around it. What happens when usage scales quickly. What happens when adversarial behavior becomes more sophisticated. What happens when regulators, enterprises, or developers ask the network to prove more than it originally expected to reveal. Those are the moments that test whether elegance is durable or merely attractive from a distance.
And that is probably the most honest way to look at Midnight Network right now. It is not a loud system asking for applause. It is a careful experiment in whether trust can exist without constant exposure, whether coordination can remain reliable without becoming fully visible, and whether privacy can function as infrastructure instead of just ideology. That is a much harder challenge than branding it as “private by design” and moving on.
There is something compelling about that restraint. Midnight is not trying to overwhelm the room. It is trying to build a room where sensitive interactions can happen without everything leaking into public view. If it works, the implications could stretch far beyond crypto-native users. Identity systems, enterprise workflows, regulated environments, and confidential applications all begin to look different when verification no longer depends on oversharing.
Still, subtle systems are often the hardest to evaluate because their strength is not always obvious until they are stressed. Midnight Network feels a bit like watching a blindfolded juggler who somehow keeps everything in motion through timing, structure, and discipline alone. You keep looking because part of you expects the pattern to break. And part of you suspects it may not.
#night @MidnightNetwork $NIGHT

