Recently, I found myself thinking about the concept of eligibility while organizing my professional files late at night. I was facing a system asking for detailed proof of financial and technical competence just to access a development opportunity that was not even public. It did not feel like a normal verification process; it felt more like voluntary data exposure. I paused for a long time before clicking approve. Why does proving competence often require exposing entire portfolios, financial history, and personal records to systems whose data boundaries we do not fully understand?
This is where Sign caught my attention. The core idea behind Sign is something I would describe as encrypted proof. The system focuses on generating attestations that confirm required information without exposing the underlying data itself. In simple terms, it allows verification without full disclosure. Instead of sharing all your documents, the system provides a cryptographic confirmation that the documents exist and meet the requirements.
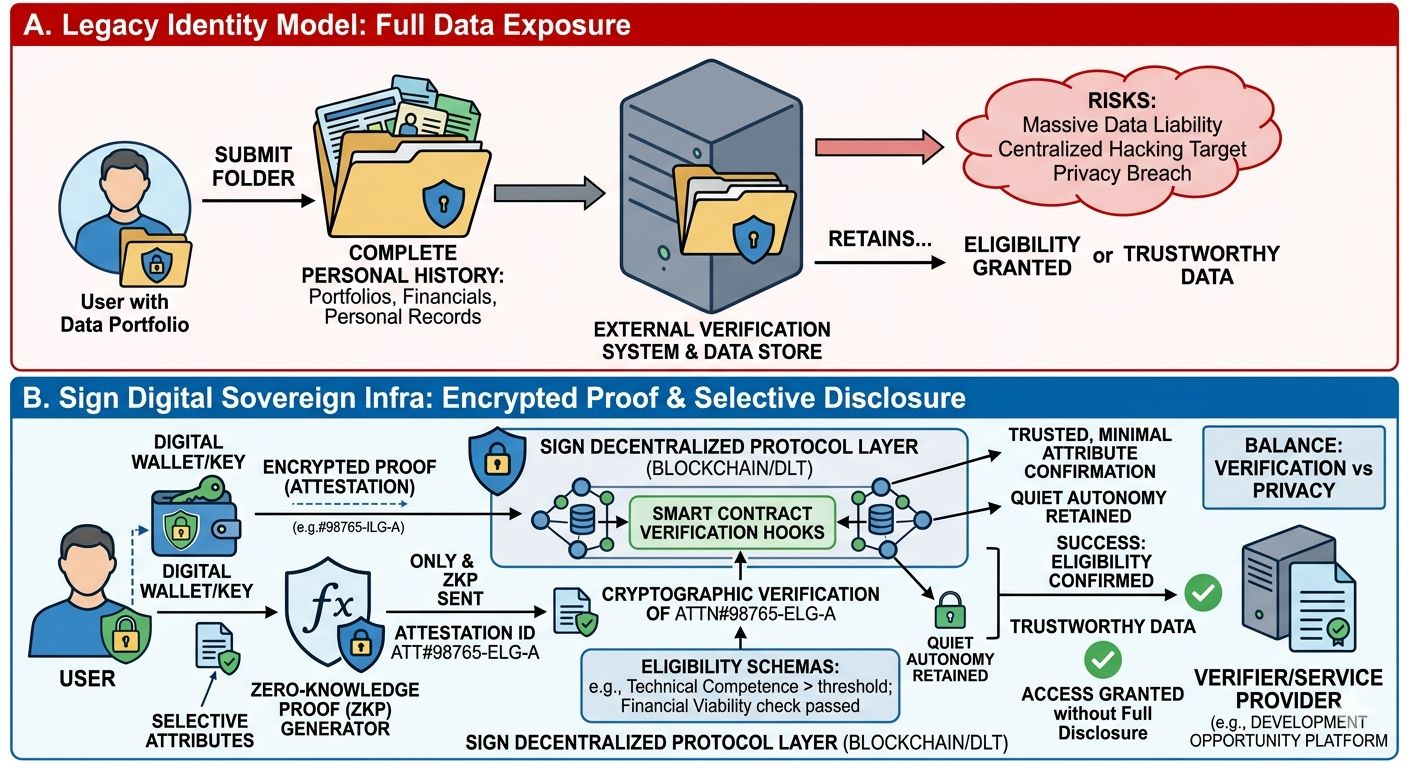
What makes this approach interesting is that it changes how identity works in digital systems. Identity is no longer a large file full of personal information; it becomes more like an encrypted key that opens specific doors when needed. You prove what is necessary, and nothing more.
This idea is becoming more relevant in the modern job market and digital services. Companies and platforms are slowly realizing that collecting excessive user data is not always the best way to build trust. In fact, the future seems to be moving toward minimum data verification, where systems verify authenticity instead of storing sensitive information.
We are moving away from the old model of “show everything to be trusted” toward a new model where cryptographic proof replaces data exposure. The system does not need to see your entire history; it only needs proof that you meet the requirement.
What interests me most about this approach is what I would call quiet autonomy. Users can prove their qualifications, identity, or eligibility without making their entire personal history visible. It creates a balance between verification and privacy, which is something the internet has struggled with for years.
Of course, this shift will not be easy. Many industries are still built around collecting and storing large amounts of user data. Moving toward selective proof and encrypted attestations requires a major change in mindset. But this change looks less like a disruption and more like a natural evolution in how we understand security and trust in digital systems.
For a long time, technology treated transparency as exposing everything. Now we are starting to understand that real trust is not built by exposing all data, but by proving truth without revealing secrets.
@SignOfficial
#SignDigitalSovereignInfra
