The ugly part is not proving who you are. It is losing the device right before the thing you already qualified for is supposed to arrive.
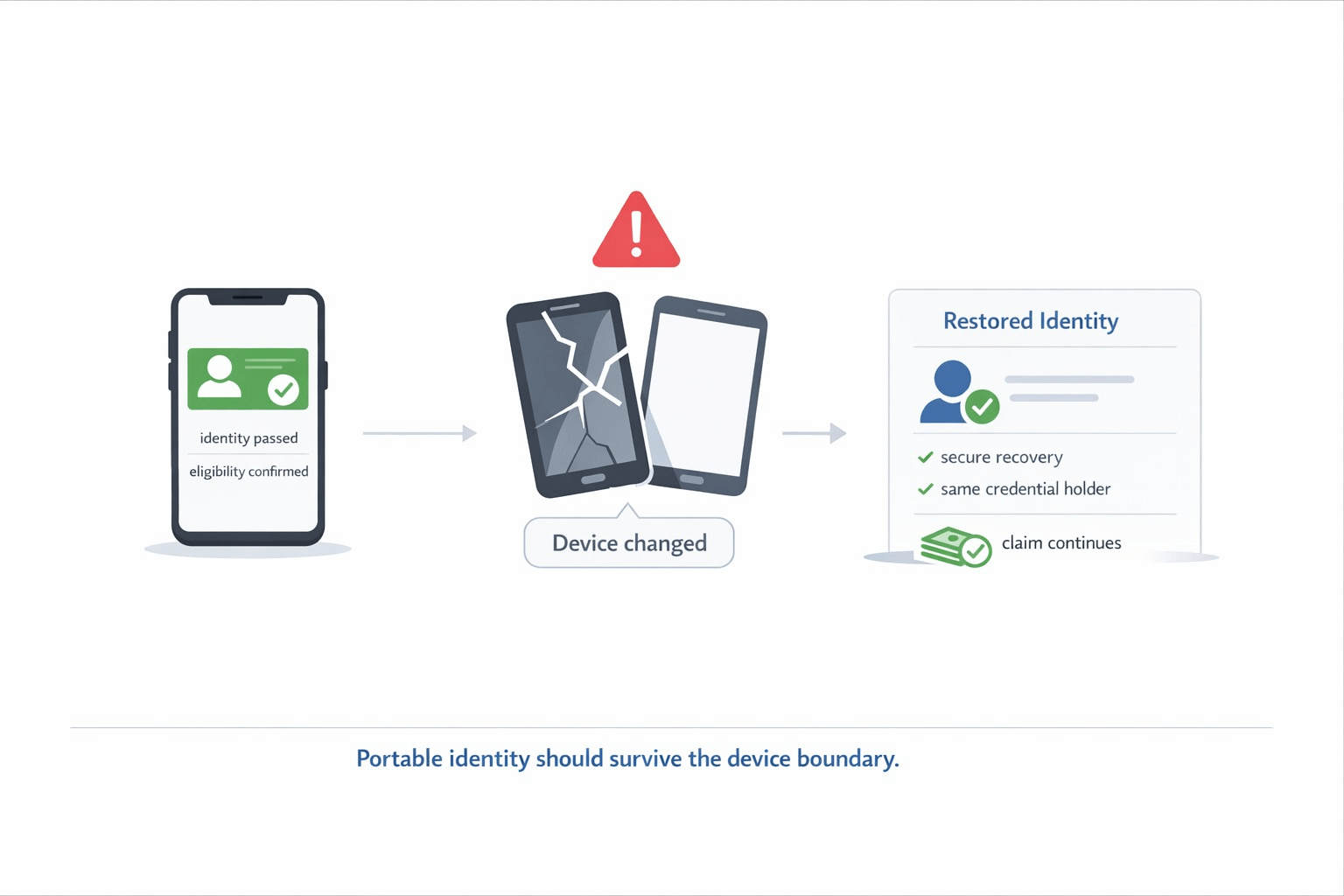
That was the moment I kept picturing with SIGN. You already passed the identity check. You already matched the eligibility rules. Your name is effectively in the program. Then your phone dies, gets replaced, or disappears, and suddenly the whole flow threatens to drag you back to zero like none of the earlier work counted. That is where a lot of digital identity talk still feels fake to me. Portability sounds great until it hits a device boundary.
What made SIGN feel more serious is that its identity layer is not framed like a one-time badge. The holder wallet is described as non-custodial, device protected, built for multi-credential management, offline QR and NFC presentation, and secure backup or recovery under approved policy. That matters because a credential system is not really reusable if a device swap turns into a full re-verification ritual. SIGN also makes verifiers check more than a signature. The verification step includes issuer legitimacy through the trust registry, schema compliance, and status or revocation at the time of use. So the real goal is not "show a file from your phone." The goal is "recover the same valid personhood and keep moving."
The reason this gets more painful than a normal wallet problem is that SIGN ties identity directly into money and capital flows. Its identity layer is meant to support one citizen and one verifiable identity layer across agencies and regulated operators. On top of that, the capital side uses eligibility evidence to gate access to benefits and subsidies, with identity linked targeting and duplicate prevention built into the distribution logic. In the welfare flow, the system verifies citizens through the ID layer, generates the allocation table, executes distributions, and anchors the ruleset hash and execution references for later review. That means a lost device is not just a login inconvenience. It can become a delayed payment, a blocked subsidy, or a second round of proving the same thing to a system that should already know you passed.
That is the visible consequence that matters to me. A user should not lose access to a legitimate claim because the container changed while the person did not. If the rails are good, recovery should preserve the right to act without reopening the whole trust file from scratch. If the rails are weak, the user gets hit twice. First by the device problem. Then by the administrative reset. SIGN feels more interesting exactly at that pressure point because it is trying to keep identity evidence reusable enough to survive into the next action, not just into the next login.
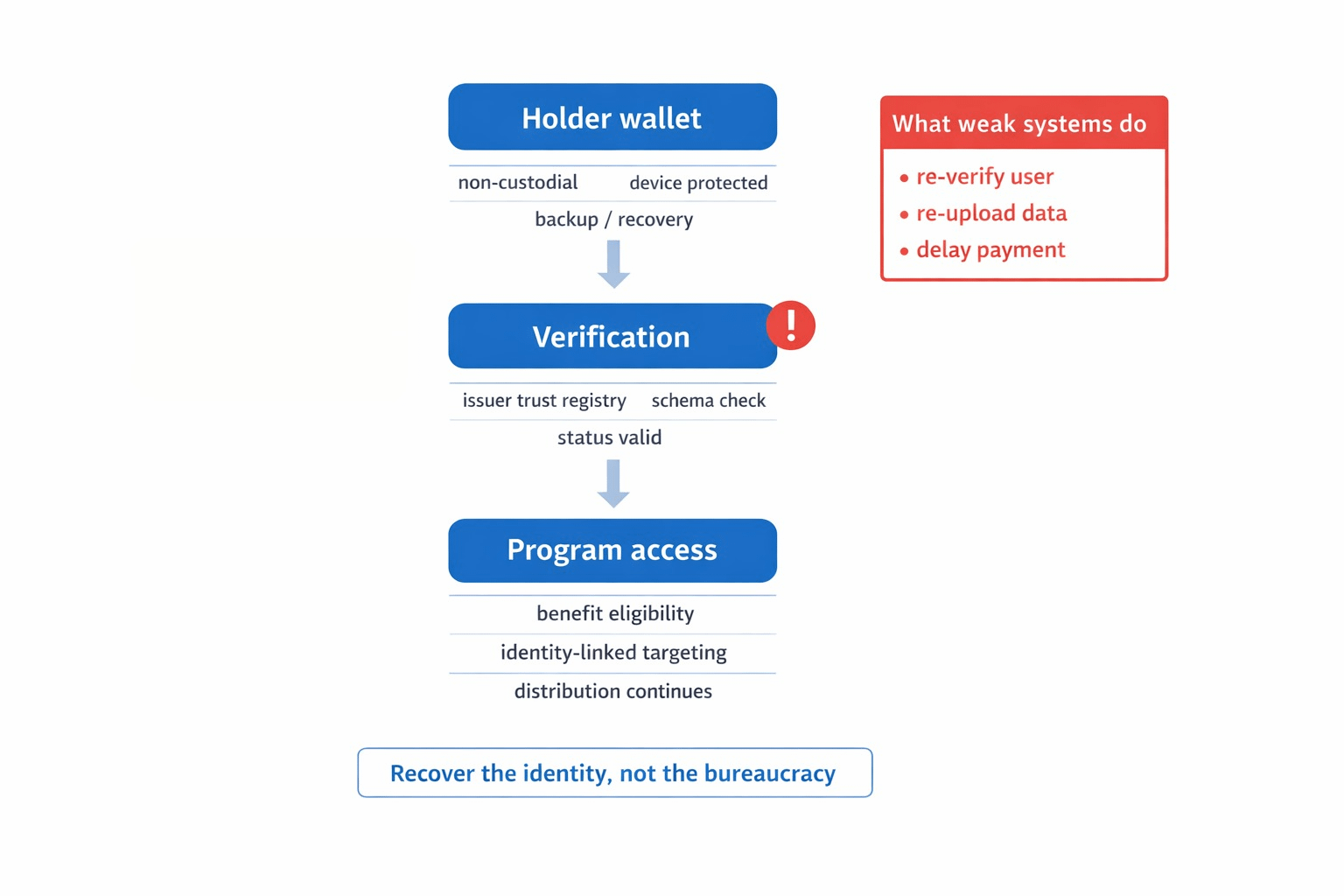
I still think this is where a lot of systems quietly fail. They solve issuance, demo the presentation, then leave recovery and cross-system continuity as somebody else's mess. SIGN at least seems to treat that mess as part of the system. The harder question is whether real deployments will honor that promise when people hit ugly moments in the wild. When a phone is gone and the money is waiting, does the identity layer actually carry the user through, or does the whole thing collapse back into "upload everything again"? That is the line I would watch hardest.
#SignDigitalSovereignInfra $SIGN @SignOfficial

