The Cold Start Paradox of Verified Systems
→ How does $SIGN bootstrap trust when no one initially has verifiable credentials?
Good Morning Binancians,, @Gajendra BlackrocK from here ,,,, There’s something weird about systems that claim to verify truth from day one. They sound solid… until you ask a simple question: verified by who?
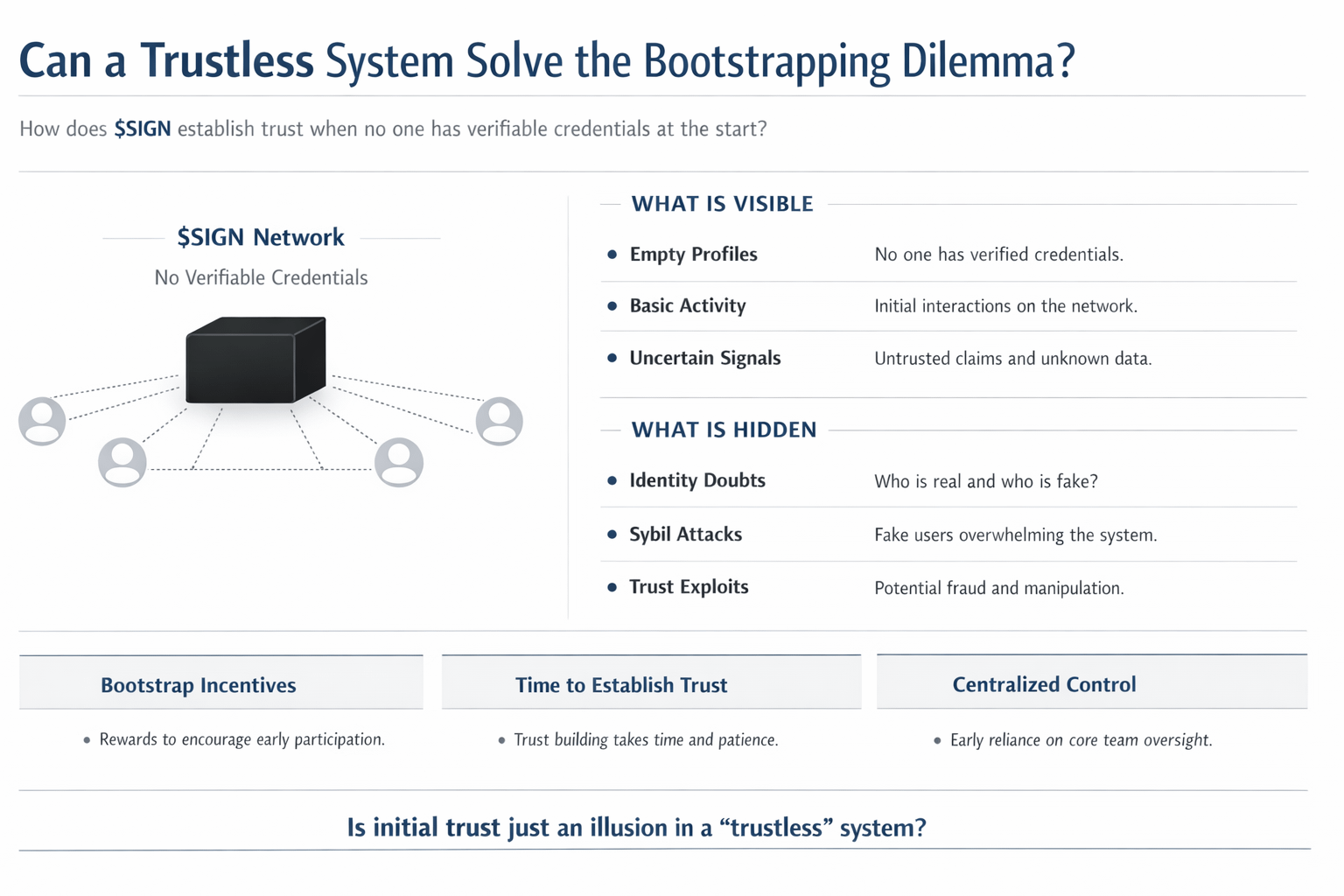
That’s the uncomfortable starting point for something like SIGN. A system built around credentials and trust signals runs into a brutal paradox early on nobody has credentials yet, but the system needs credentials to mean anything. It’s like launching a job platform where every employer demands experience, but no one’s been hired before.
That’s not just a UX issue. It’s structural.
Most current systems fake their way through this. They either rely on centralized anchors (a few trusted issuers) or they dilute standards early just to get users in. Think of early social networks everyone gets a blue tick equivalent, so it feels like something is happening. But over time, that signal collapses. If everyone is “verified,” then no one actually is.
The deeper problem is that trust doesn’t scale linearly. It compounds. Early signals matter disproportionately because they shape how everything downstream is interpreted. If the foundation is weak, the entire graph becomes noisy.
Now, what SIGN seems to be doing and this is where it gets interesting is not trying to solve cold start by pretending trust already exists. Instead, it leans into who is allowed to define trust first.
Two mechanisms stand out.
First, constrained credential issuance. Not everyone can mint credentials freely. Early issuers are either curated or emerge from existing networks with some off-chain credibility. This isn’t decentralization in the pure sense it’s more like controlled ignition. You don’t let anyone light the fire because a bad start ruins the entire system.
Second, composability of credentials. A credential in SIGN isn’t just a badge; it becomes a building block. Other protocols, communities, or systems can reference it, stack on top of it, or reinterpret it. So instead of one monolithic “trust score,” you get layered signals that evolve.
This creates a strange dynamic. Early participants aren’t just users they’re defining the grammar of trust for everyone else. And that’s a lot of power concentrated in a small group.
Here’s where the shift happens.
Cold start in SIGN isn’t solved by scale. It’s solved by density. A small, tightly connected network of credible issuers and recipients can generate stronger signals than a massive, noisy user base. It’s closer to how academic citations work than how social media followers work. A paper cited by a few respected researchers carries more weight than one cited by thousands of unknown accounts.
But that also means growth becomes… awkward.
Because scaling too fast risks breaking the signal, while scaling too slow risks irrelevance.
And there’s a subtle trade-off people don’t talk about enough: early credibility often comes from existing power structures. If initial issuers are already influential (projects, VCs, established communities), then $SIGN might inherit their biases. The system doesn’t start neutral it starts anchored.
That’s not necessarily bad. But it’s not clean either.
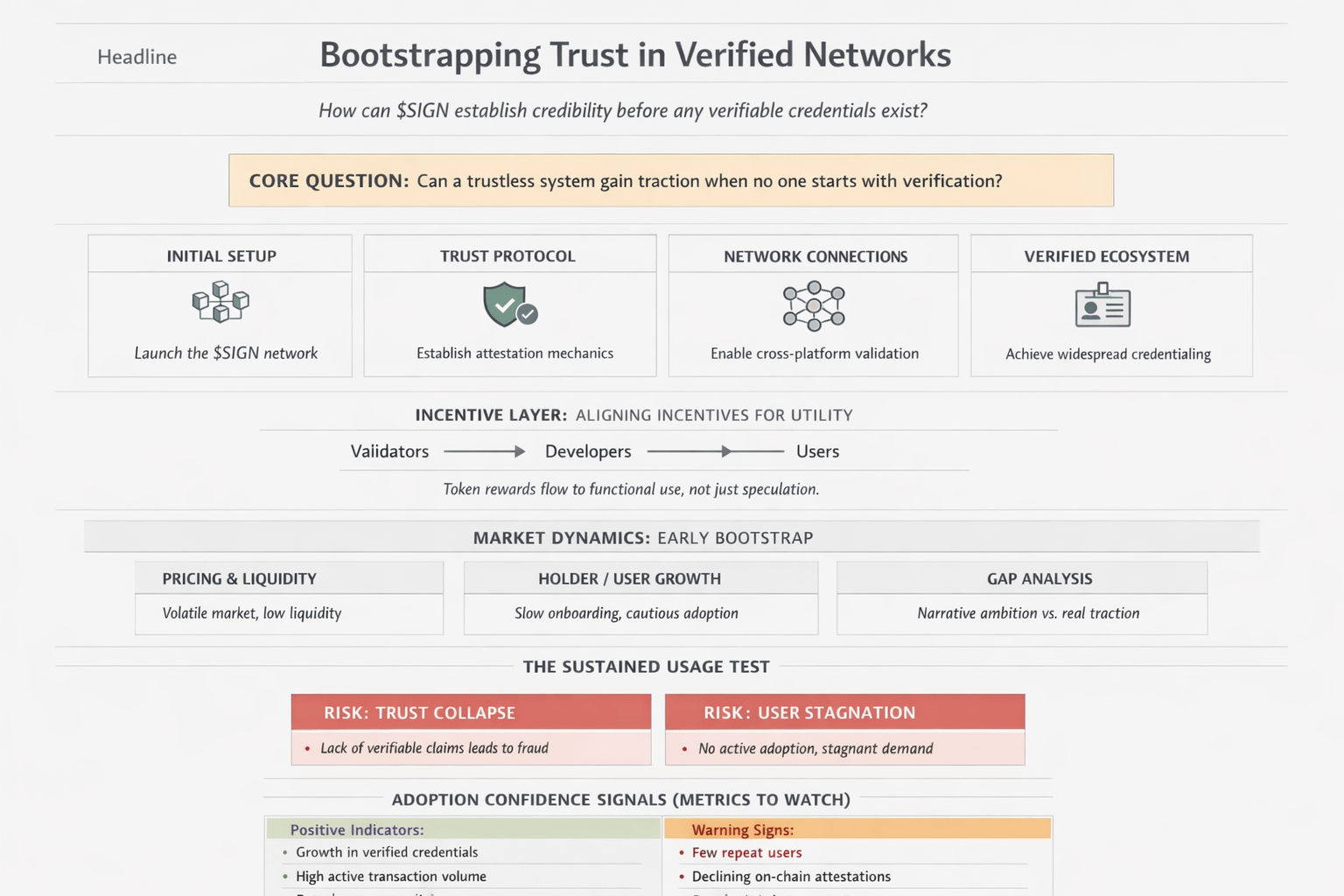
There’s also a behavioral layer here. Users don’t just react to credentials they optimize for them. If certain credentials unlock access, reputation, or financial upside, people will start gaming the pathways. Not immediately, but eventually.
It’s like airport security. The moment a rule becomes predictable, someone finds a way around it.
And in a composable system, gaming doesn’t happen at one layer it cascades. A weak credential upstream can propagate downstream into multiple systems that trust it blindly.
So the real challenge isn’t just bootstrapping trust. It’s maintaining signal integrity under pressure.

What I find most interesting is that SIGN doesn’t fully solve the cold start paradox it reframes it. Instead of asking “how do we get everyone verified,” it asks “whose verification matters enough to start with?”
That’s a more honest question. But also a more dangerous one.
Because once those initial trust anchors are set, they’re hard to unwind. Even if better signals emerge later, early narratives tend to stick. First impressions, but at protocol level.
So maybe the paradox isn’t something you eliminate. Maybe it’s something you choose to bias in a specific direction and then live with the consequences.
And if that’s true, then the real question isn’t whether SIGN can bootstrap trust.
It’s whether the first version of trust it creates is worth inheriting long term.
@SignOfficial #SignDigitalSovereignInfra
