I remember watching the market react to the first wave of privacy-focused chains years ago. The pattern was almost predictable. Tokens would list, liquidity would surge for a few weeks, and the narrative would revolve around secrecy to hidden balances, invisible transfers, the promise that users could finally escape the surveillance culture of transparent blockchains. At first I assumed that privacy itself would be the product. But over time that assumption started to look incomplete. The real question was never whether people wanted privacy. The question was whether privacy could become something economically useful inside a network rather than just a feature.
What caught my attention with Midnight is that it quietly pushes the conversation in a slightly different direction. Instead of treating privacy as an absolute state, either public or hidden to the system frames it more like a negotiation layer. Data doesn’t disappear. It becomes something you can selectively reveal, prove, or withhold depending on the situation. At first that sounds philosophical, almost academic. But if you think about it like a market participant rather than a protocol designer, the implications start to look more like economic infrastructure than cryptography.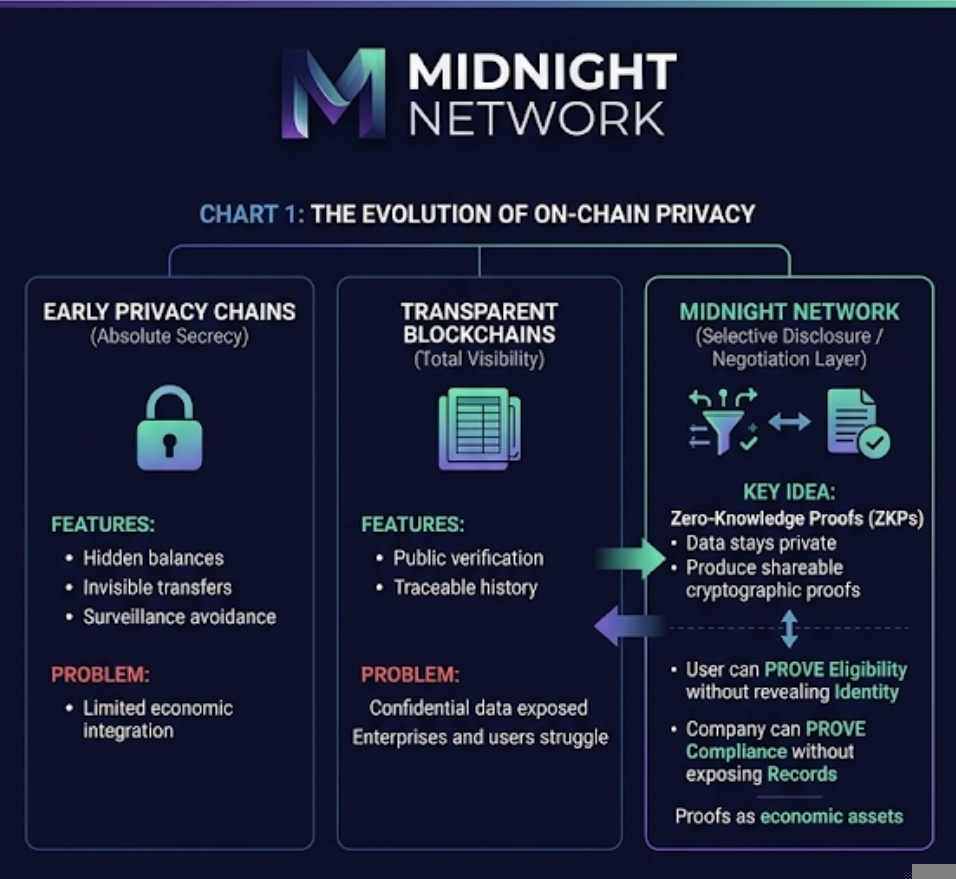
Blockchains have always struggled with a basic contradiction. Public ledgers are great for verification but terrible for sensitive information. Enterprises want their verifiable systems but rarely want their operational data visible to competitors. Users wants to control but still need to prove things about themselves. Midnight’s model tries to bridge that gap through zero-knowledge proofs and selective disclosure. Instead of exposing a raw data, participants produce cryptographic proofs about the data. A company could prove a compliance with a rule without exposing the internal records. A user could prove the eligibility for a service without revealing their identity. The data stays private, but the proof becomes shareable.
Once you look at the system through that lens, something interesting happens. Proofs begin to behave like economic assets. They’re not exactly data, but they represent verified information that someone else might want to trust. That’s where the idea of a negotiation layer starts to make sense. Data owners don’t just hold information. They hold the ability to generate proofs about that information.
I remember thinking about this while watching a small infrastructure token rally last year. The narrative was about “data ownership,” which sounded good on paper but never translated into actual demand. People owned their data, sure, but there wasn’t a clear mechanism that turned that ownership into economic activity. Midnight feels slightly different because the value is not the raw data itself. It’s the ability to produce verifiable statements about the data.
The operational flow of the network reflects this idea. Developers build privacy-preserving applications using Midnight’s programming environment. Users interact with those applications while their underlying data remains hidden. When a transaction or verification event occurs, cryptographic proofs validate that the rules of the system were followed without exposing the inputs.
Validators or network operators still participate in maintaining consensus and verifying these proofs. Fees flow through the system whenever proofs are generated or verified, which creates a potential usage loop. In theory, every time someone needs to prove something to compliance, identity attributes, credentials, transaction legitimacy to the network processes that proof.
But this is where I start to get cautious, because the economics only work if those proofs are generated regularly. Infrastructure tokens often suffer from what I think of as the retention problem. The technology works, the architecture is elegant, the token trades well during the narrative phase. Then the usage curve flattens. Developers experiment but don’t stick around. Users interact once but don’t build habits.
If Midnight actually becomes a negotiation layer for data proofs, then recurring demand might appear in places we don’t normally think about as crypto activity. Financial compliance checks. AI agent interactions. Enterprise credential systems. Machine-to-machine verification. These are repetitive processes that happen constantly in traditional systems. If they move on-chain, the network could process thousands or millions of proof events.
Still, markets tend to front-run these ideas long before the infrastructure proves it can sustain them. Token supply dynamics start to matter quickly. Circulating supply versus fully diluted valuation becomes relevant because infrastructure narratives often trade at large future valuations before the usage arrives. If unlock schedules accelerate faster than adoption, early liquidity can absorb the pressure only for so long.
I’ve seen that pattern too many times to ignore it. A promising infrastructure network launches, the FDV climbs into the billions, and the assumption is that future demand will eventually justify the valuation. Sometimes it does. Often it doesn’t.
Another risk sits in the verification layer itself. Proof systems sound secure in theory, but real networks attract creative behavior. Low-quality applications could generate meaningless proofs simply to farm incentives. Developers might create activity loops that inflate usage statistics without representing real economic work. Even verification markets can suffer from coordination problems if incentives aren’t aligned properly.
There’s also the narrative trap. Crypto markets often price stories faster than they price infrastructure. If the idea of “data negotiation layers” becomes fashionable, traders might chase the theme without paying attention to whether the network is actually processing meaningful proofs.
So when I look at Midnight from a trading perspective, I try to separate the elegance of the architecture from the signals that matter in practice. I’d want to see developer activity that produces real applications rather than demo environments. I’d watch the growth rate of proof generation across the network. Not just transactions, but actual verification events that represent useful work.
Bonded participation would matter too. If validators or operators have meaningful capital locked into the system, it suggests long-term commitment rather than opportunistic activity. Supply absorption also becomes important. If token unlocks hit the market but prices remain stable, that usually means usage demand is quietly absorbing the distribution.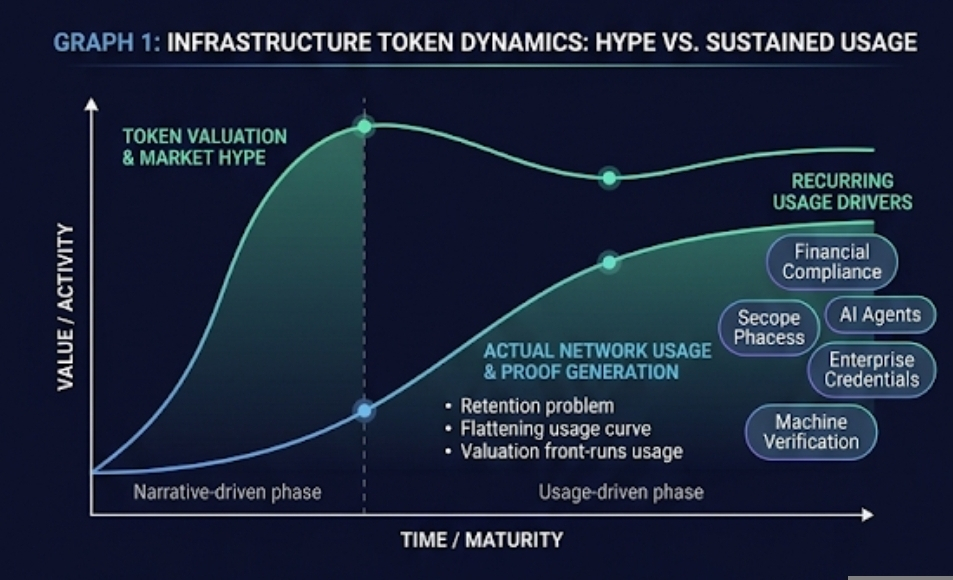
On the other hand, if the story keeps expanding while the underlying activity stays flat, that’s usually when I start getting cautious. Infrastructure tokens rarely fail because the technology breaks. They fail because the usage loop never forms.
I still find the concept of a data negotiation layer fascinating. The idea that information doesn’t have to be public or private, but instead becomes something people can prove selectively, could change how digital systems operate. But markets don’t reward possibilities forever.
In the end, traders would probably be better off watching behavior instead of narratives. If Midnight becomes a place where proofs are generated constantly because real systems depend on them, the economics will eventually show up in the data. If not, the market will move on to the next infrastructure story.
Articolo
The Data Negotiation Layer: How Midnight Could Turn Privacy Into a Negotiable Asset
Disclaimer: Include opinioni di terze parti. Non è una consulenza finanziaria. Può includere contenuti sponsorizzati. Consulta i T&C.
0
10
369
Esplora le ultime notizie sulle crypto
⚡️ Partecipa alle ultime discussioni sulle crypto
💬 Interagisci con i tuoi creator preferiti
👍 Goditi i contenuti che ti interessano
Email / numero di telefono
