Midnight stands out because it does not treat privacy as a slogan or a cosmetic feature. It treats privacy as a missing layer in blockchain design. Most chains were built on the assumption that transparency is always good, that every wallet action, balance change, and transaction trail should remain visible forever. That model works for open verification, but it breaks down the moment blockchain touches ordinary business, personal identity, sensitive data, or financial activity that should not be exposed to the public by default. Midnight is built around a different belief: people should be able to prove what matters without revealing everything else. That idea sits at the heart of the project, and it gives the network a much clearer purpose than many chains that simply add zero-knowledge technology and call themselves private.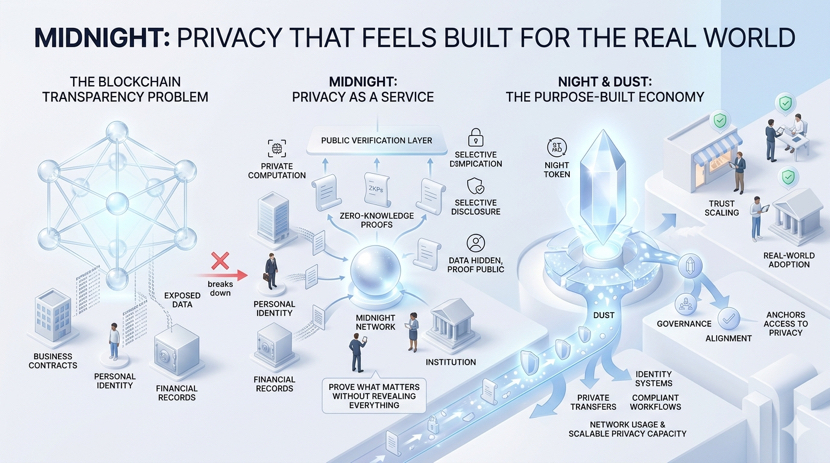
What makes Midnight interesting is that it does not chase privacy in the old, absolute sense. It is not trying to make everything invisible. It is trying to make privacy usable, selective, and practical. That distinction changes the whole shape of the network. Instead of pushing total concealment, Midnight is designed for situations where information needs to stay protected, yet proofs still need to remain valid, portable, and trustworthy. That is a more mature direction. In the real world, most users and institutions do not need permanent secrecy for everything. They need control. They need the ability to keep personal or commercial information hidden while still showing compliance, ownership, eligibility, or truth when required. Midnight understands that better than most projects in the privacy category.
The architecture reflects that seriousness. This is not just a blockchain where transactions are obscured. It is a system built for private computation with public verification. Sensitive data can remain off-chain or shielded, while the network verifies that the outcome is correct through zero-knowledge proofs. That matters because it shifts privacy from being a transfer feature into being an application layer feature. Midnight is not only asking how value can move discreetly. It is asking how logic, credentials, conditions, and decisions can be processed without exposing the raw information behind them. That opens a much larger design space. It makes the chain relevant not just for private transfers, but for identity systems, business workflows, financial products, confidential automation, and any application where trust and discretion have to exist at the same time.
One of Midnight’s strongest qualities is that its token system actually supports its philosophy instead of distracting from it. NIGHT is not framed as a standard gas token that gets burned every time someone uses the chain. It plays a deeper role. NIGHT is the core asset that generates access to the network’s private execution capacity. That capacity is expressed through DUST, which acts as the shielded resource used for transactions and smart contract activity. This separation is one of the most thoughtful choices in the whole design. It allows the network to keep its main token visible and economically legible while pushing privacy into the operational layer where it matters most. In effect, Midnight separates long-term value from short-term usage. That is a smarter structure than the usual model where one token tries to carry speculation, governance, fee payment, and security all at once.
The result is a token economy that feels more intentional than most. NIGHT is important because it controls access to renewable network capacity, not because it is constantly consumed in small amounts. That gives it stronger economic identity. It becomes the asset tied to participation, governance, and long-term alignment, while DUST handles the mechanics of private activity. I think this is where Midnight becomes genuinely original. A lot of token models sound clever in theory but do not solve any real product problem. Midnight’s model solves several at once. It reduces friction for users, makes it easier for applications to subsidize activity, and avoids forcing every transaction to become a visible expression of the token itself. More importantly, it gives the project a believable answer to a question many chains struggle with: why should the token matter beyond speculation? In Midnight’s case, the answer is clear. NIGHT matters because it anchors access to privacy-preserving computation.
That design also says something important about how the project sees adoption. Midnight does not appear to believe that the future of crypto belongs only to users who want radical transparency or pure anonymity. It is aiming for the much larger middle ground where privacy needs to be present, but accountability cannot disappear. That is why the project feels more aligned with serious long-term use cases than with short-term narrative cycles. It is built for environments where open ledgers are too exposed, but closed systems are too rigid. In that sense, Midnight is not really selling privacy as rebellion. It is selling privacy as infrastructure.
The broader economics reinforce that impression. The fixed supply of NIGHT gives the asset scarcity, but the more important point is how value is meant to circulate around network usage. The system is designed so that demand for private execution can support the importance of NIGHT without forcing the token to function like a simple metered fee coin. That creates a more durable relationship between network growth and token relevance. If Midnight attracts real applications, the token does not benefit just because people are trading it. It benefits because access to private computational capacity becomes more valuable. That is a far healthier foundation than models that depend only on transaction count or narrative hype.
Recent progress matters here because Midnight is no longer just an abstract design story. It has moved into a phase where architecture, economics, and timing have to prove they belong together. The project is approaching the point where its ideas must become visible in live usage, developer activity, and ecosystem formation. That is the real test. A project like Midnight does not win by sounding advanced. It wins by making developers feel that private applications are finally realistic to build, and by making users feel that privacy no longer has to come at the cost of usability. The closer it gets to that threshold, the more relevant NIGHT becomes, because the token is tied directly to the system’s ability to turn privacy into a working economic layer.
What I find most compelling about Midnight is that it feels like a correction to a long-standing mistake in blockchain thinking. For years, the industry acted as if full transparency was inherently virtuous and privacy was something suspicious or secondary. That assumption made blockchains powerful in some areas, but unusable in many others. Midnight starts from the opposite intuition: that privacy is not the enemy of trust, but one of the conditions for trust to scale into real life. That is a much more grounded way to think about the future of decentralized systems.