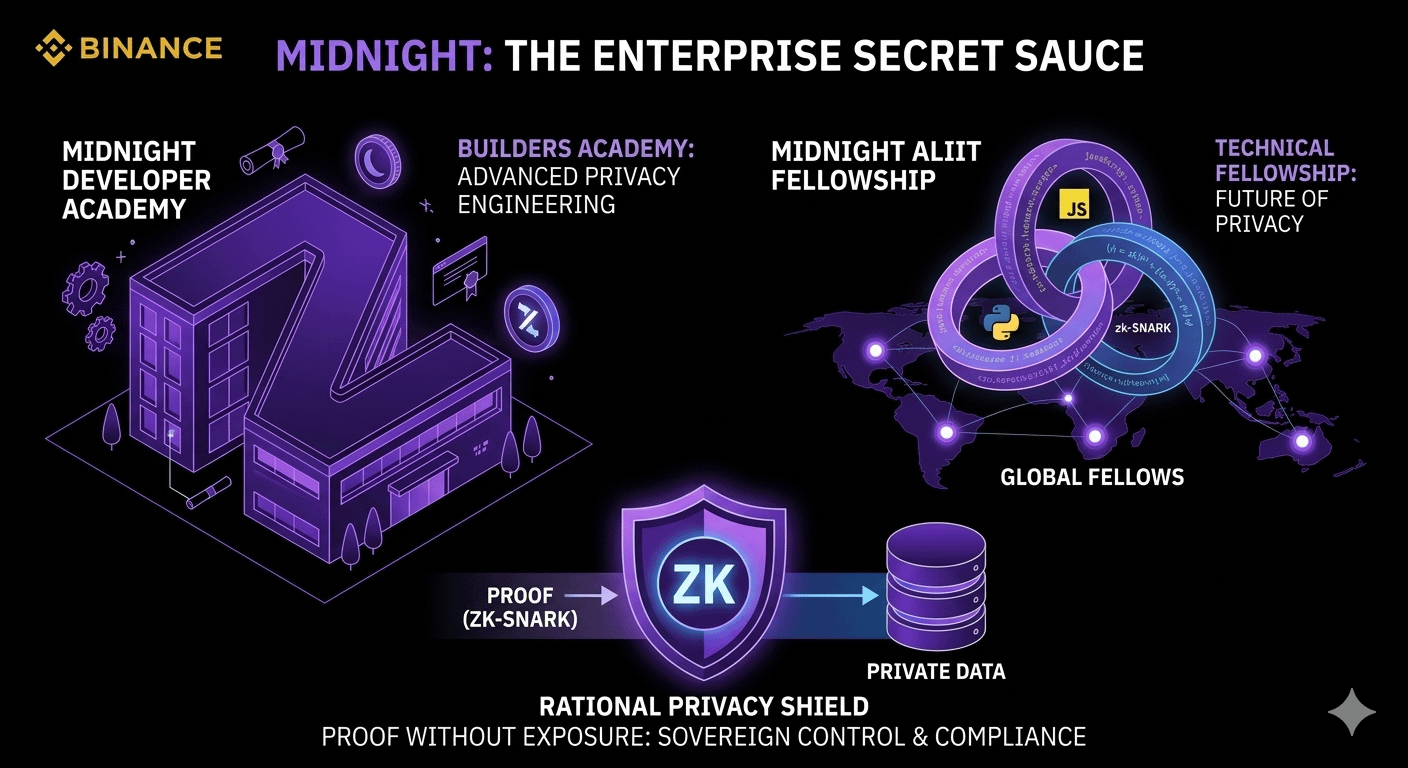
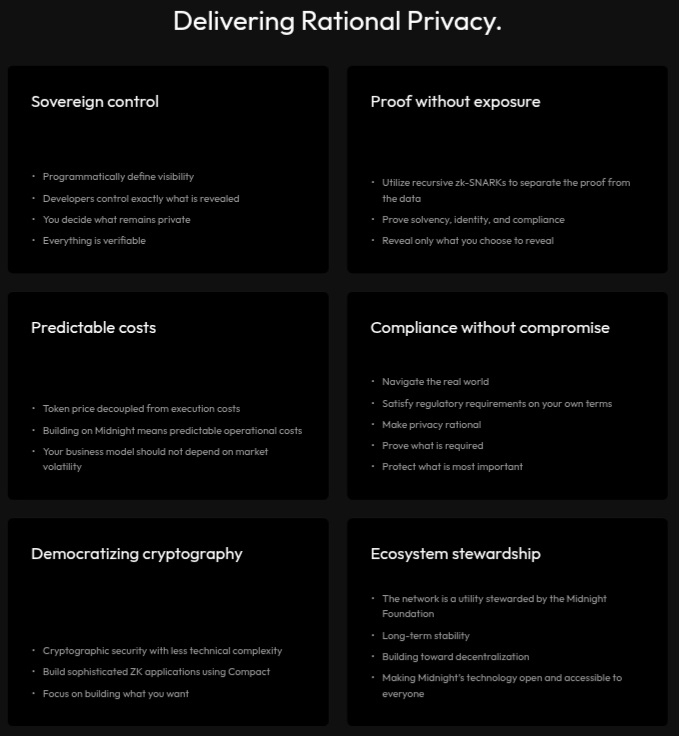
The industry has been obsessed with "Total Privacy" (which regulators hate) or "Total Transparency" (which enterprises hate). @MidnightNetwork is carving out a third path called Rational Privacy. After digging into the Midnight Developer Academy and the Aliit Fellowship, it’s clear: this isn't just another L1—it’s a data-sovereignty machine.
The Architecture of Selective Disclosure
Most chains leak data like a sieve. If you’re a business running payroll on-chain, everyone sees your salaries. $NIGHT uses recursive zk-SNARKs to solve the "Privacy vs. Compliance" paradox.
Sovereign Control: Unlike other chains, developers programmatically define visibility. You decide what stays private and what is verifiable.
Compliance Without Compromise: You can satisfy regulatory audits (AML/KYC) without exposing your entire user database to the public. It’s "Proof without Exposure."
The NIGHT/DUST Model: The dual-token system decouples execution costs from market volatility. This is the "Predictable Cost" model that makes the chain actually usable for real businesses.
Midnight Aliit & Developer Academy: The Brain Trust
The Midnight Aliit isn't just a fancy name; it’s a selective fellowship for builders who understand cryptography. Combined with the Developer Academy, they are training a generation of "Privacy Engineers." They’re moving builders from basic consensus concepts to advanced zero-knowledge technology. If you are a dev, this is where the "Alpha" is being built.
Pro-Tips & Workflow Tricks
To truly master the Midnight ecosystem, you need to think like a Privacy Architect, not just a trader. Here is the enterprise secret sauce:
The "Compact" Shortcut: Use the Compact language to build sophisticated ZK applications without needing a PhD in math. It simplifies cryptographic complexity.
Decouple your Execution: When building, always calculate your operational costs using the DUST model. It protects your business model from #night price swings.
Recursive zk-SNARKs: Leverage recursive proofs to keep your data footprint small. It separates the "proof" from the "data," ensuring speed without sacrificing security.
The future isn't about hiding everything; it’s about revealing only what is required. That is the rational choice.

