The more I read about Sign, the more I feel like it is pointing at a problem most of Web3 has started treating as normal.
And honestly, it should not be normal.
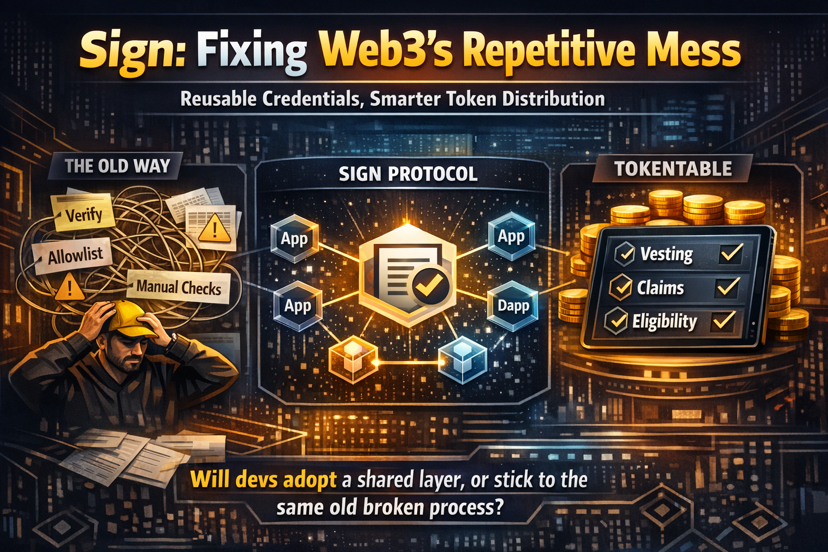
Right now, trust infrastructure across blockchain apps is still messy. The same verification steps get repeated from project to project. The same allowlists, the same anti-fraud checks, the same wallet checks, the same manual spreadsheets somehow tied to smart contract actions.
It is repetitive, inefficient, and often frustrating in ways users do not even fully notice.
That is what makes Sign interesting to me.
What Sign seems to understand is that the real issue is not verifying something once. The real issue is having to verify the same thing again and again across different products because systems do not talk to each other.
That is a bad developer experience, and it is also a bad user experience.
Sign’s answer to this is not just “identity” in the usual sense. What stands out more is the idea of reusable claims.
Think about it simply: a wallet has already been verified, a user is already eligible, or a contributor has already proven meaningful work. In most systems, that information ends up scattered across Discord roles, internal databases, dashboards, or random APIs.
With Sign Protocol, that information can exist in a clearer, reusable format that other apps can read too.
That is the part that really clicked for me.
Instead of rechecking the same thing every time, a product could just read an existing credential and move forward. That may sound like a small improvement, but it actually changes a lot. It reduces duplication, saves developer time, and makes the experience smoother for users.
And for developers, that is a huge plus.
Then there is TokenTable, which at first might look like just another token distribution tool. But token allocation at scale is rarely simple. Once spreadsheets, scripts, custom rules, and edge cases enter the process, things get messy very quickly.
Wrong amounts happen. Vesting schedules break. Claims become confusing.
What I find interesting is that Sign is trying to standardize that layer too tying allocations, vesting, and claims to verified credentials instead of relying on static lists alone.
So instead of saying, “send tokens to this wallet list,” the logic becomes more like, “send tokens to wallets that have proven eligibility.”
That is a meaningful shift.
I also think it matters that they are building this as an omni-chain system rather than keeping it tied to one ecosystem. And their use of encryption and zero-knowledge proofs makes sense too, because no one wants identity or credential systems to become a privacy nightmare.
Still, I think the biggest question is adoption.
The idea of a shared truth layer sounds strong in theory: fewer repeated checks, less fragmentation, better UX. But it only becomes truly powerful if enough projects use the same standards. Otherwise, it risks becoming just another layer in an already crowded stack.
That said, I like the direction.
Sign feels like it is solving a real infrastructure problem, not inventing a fake one for attention. And in my opinion, that is what makes it worth watching.
The real question is simple:
Will developers adopt a shared credential layer like this or keep rebuilding the same broken verification flow out of habit?
$SIGN @SignOfficial #SignDigitalSovereignInfra