cryptography class ma current semster. professor explained zero knowledge proofs with pasword example all student use. prove you know pasword with out any revealing it. i got my math on my 3 attempt. wrote it don. moved on. filed it undr "exam hoal topic i will never see in real life. hahaha"
that assumption did not survive last week.
i was reading through the Sierra Leone deployment details in Sign Protocol's docs. national residency cards on-chain. fine, i had seen that headline. but i kept rereading one specific section. the ZK attestation part. something about it did not click immediately.
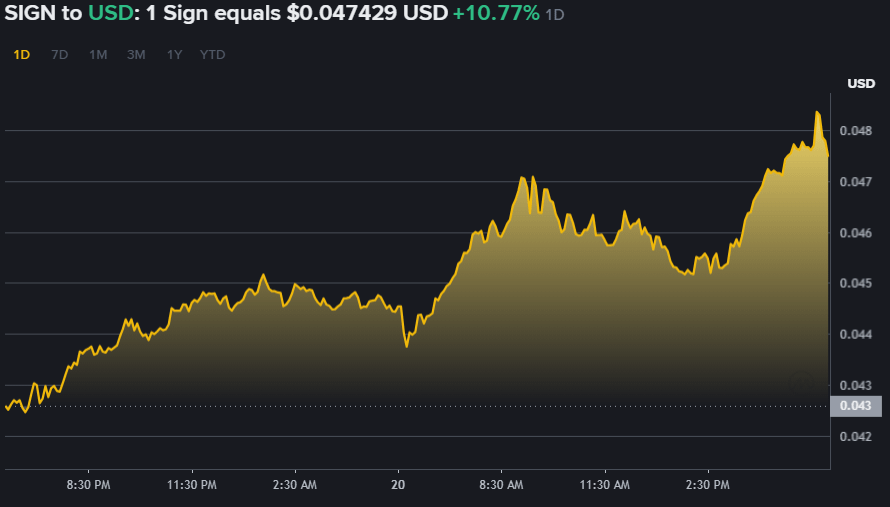
$SIGN is at $0.047429 today. market cap $74.16M. 1.64B circulating out of 10B max. 69.58% below ATH. Date: March 20, 2026.Today SING CHART

here is the thing that finally clicked. most attestation systems give you two options and only two. the data is fully public and anyone can verify it. or the data is private and nobody can verify it without calling the original issuer directly. that second option is not really privacy. it is just obscurity with an extra step.
ZK attestations do not fit either option. you prove a specific claim is true from an existing attestation without showing the attestation or the data underneath it. the proof travels. the data does not.
the over-18 example from the docs made it concrete for me. government issues a national ID attestation to a citizen. citizen needs to prove they are over 18 somewhere. under a normal attestation the service provider sees the full record. name. address. ID number. date of birth. everything. every single time. across every service the citizen uses. under ZK attestation the citizen generates a proof that satisfies the over-18 condition specifically. service provider verifies it. they learn one thing. the person is over 18. the name does not travel. the address does not travel. the ID number does not travel.
i kept thinking about what the difference actually means at scale. a government issuing national credentials that citizens use across dozens of different services. under normal attestion every one of those services slowly bulds your profile of that citi zen's activity. not because any one intend it. just because that is what happen and when full records get passed around. under ZK attestation each interaction produces a fresh proof for one spacific claim. no correlation between sessions. no profile building.
the part i genuinely have not resolved. ZK proof generation is computationally expensive. if a citizen's phone is generating the proof at verification time, low-end devices are going to struggle. if proof generation moves to a server to solve the device problem, you just reintroduced a trust assumption the ZK proof was supposed to remove. i looked through the current docs twice and did not find a clear answer on how Sign handles this for actual consumer deployments. maybe i missed something. maybe it is not documented yet.
March 31 unlock is coming. 8.07 billion tokens still locked out of 10 billion max. same supply pressure as everything else with $SIGN right now.
one more government deployment using ZK use aunder in 2026 changes the conversation signficantly. i can not tell you if that happ this year or next year. the whitepaper can not tell you either.
do you want think ZK attestations get adopted for private government credentials first or enter prise KYC first? and does the proof generation problem on low-end devices actually get solved before either of those? tell me in comments.
#SignProtocol #SignDigitalSovereignInfra $SIGN @SignOfficial
