I have been down a rabbit hole thinking about the oracle problem on Midnight for the past few days and I think it is one of those challenges that sits so quietly underneath everything else that most people don't even realize it exists until they try to build something real and suddenly hit a wall they didn't see coming 😂
let me explain what I mean because this one requires some careful setup before the interesting part arrives.
oracles are the mechanism by which blockchains learn things about the real world. a smart contract on its own is a closed system. it knows what is on the chain. it knows its own state. it knows what other contracts tell it. but it has no native way of knowing what the price of an asset is on an external exchange or whether a flight was delayed or what the weather is or whether a specific real world event occurred.
oracles solve that problem by bringing external data onto the chain in a verifiable way. a trusted data provider or a decentralized network of data providers observes something in the real world, signs that observation, and posts it on chain where smart contracts can read it and act on it.
that mechanism is well understood. it has been implemented extensively across the Ethereum ecosystem. Chainlink alone has processed an almost incomprehensible volume of real world data feeds that DeFi protocols depend on for pricing, liquidations, settlement, and a dozen other critical functions.
the problems with oracles on transparent chains are also well understood. the oracle is a trust assumption. the data provider can lie or be compromised. a decentralized oracle network reduces but does not eliminate that trust assumption. oracle manipulation has been a significant attack vector in DeFi — manipulating the price feed an oracle provides can allow an attacker to drain a lending protocol or manipulate a prediction market outcome.
these are real problems. the ecosystem has developed partial solutions to them. the oracle problem on transparent chains is not solved but it is at least legible. you can see the oracle data. you can audit it. you can design systems around the specific trust assumptions it introduces.
Midnight's oracle problem is different. and it is different in ways that I think are genuinely underappreciated.
here is the core tension.
Midnight applications operate on private state. the whole point is that the data inside the shielded environment is not visible to outside observers. a healthcare application stores private patient data. a confidential financial application stores private transaction records. a shielded identity system stores private credential information.
but those applications don't exist in isolation from the real world. they need to respond to real world conditions. a private insurance application needs to know whether a policyholder's medical event actually occurred. a confidential financial instrument needs to know the current market price of an underlying asset. a shielded identity system might need to verify that a credential issued by a real world authority is still valid and has not been revoked.
those are oracle problems. they require real world data to enter the shielded environment.
and here is where the privacy complication arrives.
on a transparent chain an oracle posts data publicly. the price feed is visible to everyone. every contract that reads it sees the same data. the oracle's output is a public good that any application can consume without revealing anything about itself by consuming it.
on Midnight an application consuming oracle data inside a shielded environment has a problem. if the oracle posts its data publicly — on the public chain where it is visible to everyone — then the fact that a private application consumed that data becomes potentially visible through the boundary crossing event I wrote about before. an observer watching the public chain sees that a shielded application pulled a specific piece of oracle data at a specific time and can start making inferences about what the private application was doing.
the medical insurance application that queries an oracle for a policyholder's medical event data at a specific timestamp has just told an observer that something medically significant happened at that time even if the specific content of the query remains private.
the private financial application that queries a price oracle at a specific moment has revealed the timing of its private position adjustment even if the position details remain hidden.
real world data entering a privacy-preserving system is inherently leaky at the entry point. the same entry-exit correlation problem that affects asset bridges affects oracle data feeds. the moment you pull real world data into a shielded environment you leave a mark on the boundary.
the theoretical answer is the same as it always is in ZK systems. proofs. an oracle that generates a ZK proof alongside its data attestation allows a private application to prove that it consumed the oracle data without revealing when or in what context.
but that theoretical answer requires oracles that are designed to produce ZK-compatible attestations. not just signing their data with a regular cryptographic signature but generating proofs in a format that Midnight's proving system can consume and compose with private application logic.
that is a significantly higher technical bar than what today's oracle networks do.
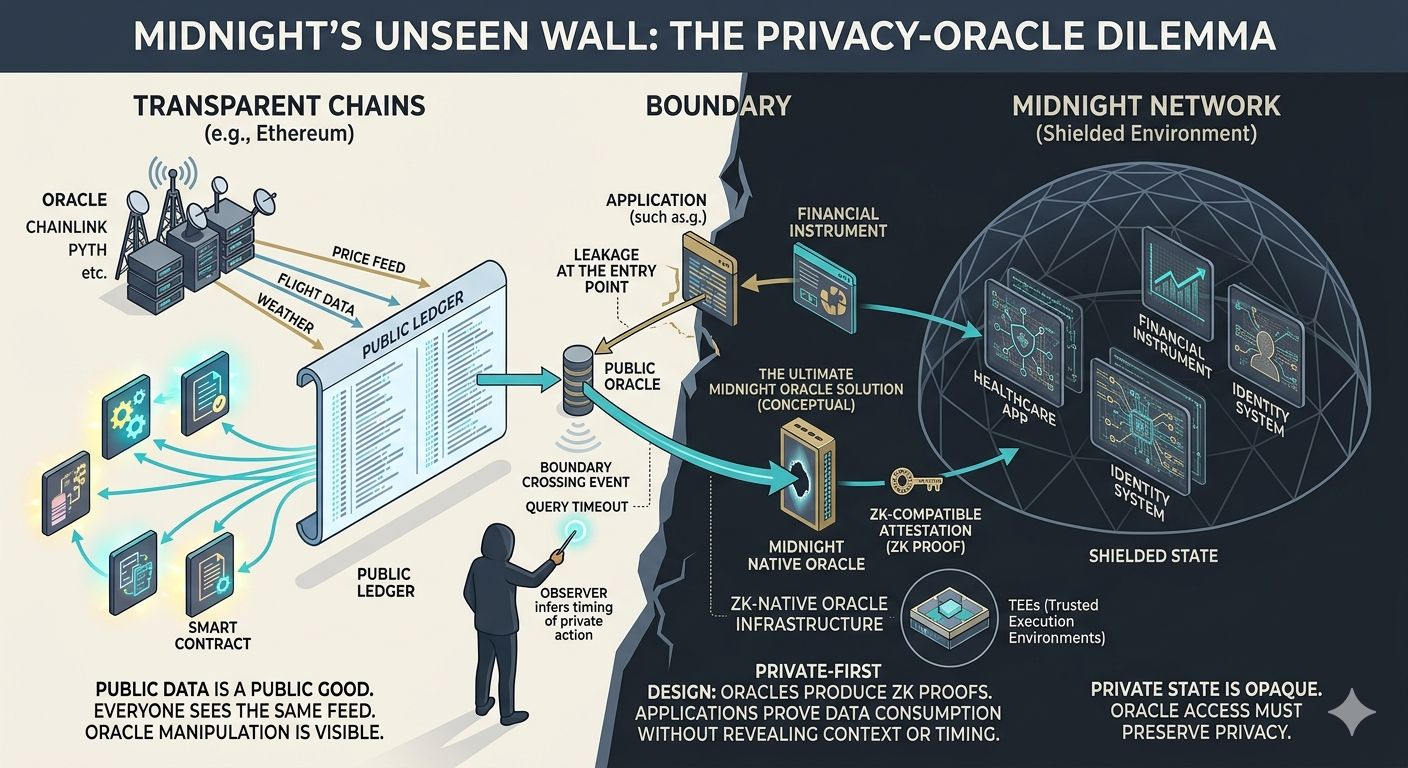
Chainlink and Pyth and the other major oracle providers are not currently producing ZK proofs of their data attestations in formats compatible with arbitrary private application proving systems. they are producing signed data feeds designed for transparent chain consumption. the signing cryptography is different. the attestation format is different. the trust model is different.
getting real world oracle data into a Midnight application in a way that preserves privacy and maintains the integrity of the data requires either adapting existing oracle providers to produce ZK-compatible attestations or building new oracle infrastructure specifically designed for privacy-preserving consumption.
neither of those is a small ask.
adapting existing oracle providers means convincing organizations with large existing infrastructure investments to modify their attestation systems to support a new proof format for a new chain whose user base is currently small. the business case for that investment is not obvious in the near term even if it is compelling in the long term.
building new oracle infrastructure means starting from scratch with a critical piece of ecosystem infrastructure that has to be trustworthy and decentralized and resistant to manipulation at the same time as it is ZK-compatible. the existing oracle providers took years and hundreds of millions of dollars in development and incentive spending to reach the level of reliability and decentralization the DeFi ecosystem depends on today.
and underneath both of those options is the oracle trust problem that exists even on transparent chains. whoever is producing the real world data attestation is a trust assumption. the ZK proof proves that the data was attested in a specific format by a specific signer. it does not prove that the signer was telling the truth about the real world event they are attesting to.
on a transparent chain oracle manipulation is at least observable after the fact. the manipulated data is on the public chain. researchers and auditors can identify it. the ecosystem can respond.
on Midnight oracle manipulation inside a shielded environment is potentially invisible even after the fact. if the oracle provides false data to a private application and that data influences the application's private state the manipulation happens inside the ZK environment where outside observers cannot see it. the consequences of the manipulation propagate through the private application's logic without leaving a legible trace on the public chain.
that asymmetry between transparent chain oracle manipulation and private application oracle manipulation matters because it changes the incentive structure around oracle honesty.
on a transparent chain an oracle provider that manipulates data faces reputational and legal consequences because the manipulation is visible. the accountability mechanism depends on transparency.
on Midnight that visibility is exactly what the privacy model eliminates. the accountability mechanism for oracle honesty has to be built into the cryptographic design rather than depending on the transparency of the chain.
I keep thinking about what private-first oracle design actually looks like. not adapting transparent chain oracles to work in a privacy context but designing oracle infrastructure from the ground up for the specific requirements of a private computation environment.
the most interesting direction I have come across is the concept of trusted execution environments as an oracle mechanism. a hardware-enforced secure computation environment that can attest to the fact that a specific computation was performed on specific inputs without revealing those inputs. if an oracle runs inside a trusted execution environment it can produce attestations that something happened in the real world without necessarily revealing the details of what happened in a way that leaks application context.
that is a promising direction. it is also a trust assumption in itself. trusted execution environments have been broken before. the hardware manufacturers who produce them are themselves a trust dependency. and the intersection of hardware security guarantees with ZK cryptographic guarantees introduces a layer of complexity that has not been extensively battle tested in production privacy applications.
the more I sit with the oracle problem on Midnight the more I think it is one of those foundational infrastructure challenges that will quietly constrain what applications can be built until it is properly solved.
the applications that don't need real world data are fine. a purely on-chain private financial instrument that only ever interacts with other on-chain state can exist in the shielded environment without ever needing an oracle.
but the applications that make Midnight's privacy guarantees most valuable in the real world are almost all oracle-dependent. private healthcare applications need real world medical data. confidential insurance applications need real world event verification. shielded identity systems need real world credential validity. private financial applications need real world price data.
the use cases that most justify building a privacy network are the ones that hit the oracle problem hardest.
and right now I don't see a clear path to solving that problem at the infrastructure level that doesn't require either trusting existing oracle providers with access to private application data or building entirely new ZK-native oracle infrastructure from scratch.
both of those paths are long. both require significant investment and coordination beyond what any single application developer can accomplish on their own.
the cryptographic foundation supports the vision of private applications that respond intelligently to real world conditions.
but the infrastructure that connects the real world to that cryptographic foundation in a way that preserves the privacy guarantee and maintains the integrity of the data and holds oracles accountable for honesty without depending on transparency to enforce that accountability — that infrastructure doesn't fully exist yet.
and until it does the most compelling Midnight applications remain theoretical rather than buildable. 🤔