i remember i did research methodology paper last semester. the professor would say the same sentence every day a claim with out a citation is an opinion is a claim with a peer-reviewed citation is at least falsifiable.
i started applying the test to in crypto white paper after that class and most intersting of them the fail is immediately.
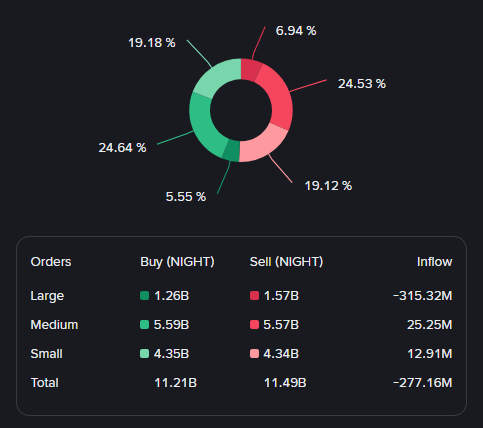
$NIGHT as today March 22/2026 NIGHT token is at this price $0.04363 and market cap is $724M or 16.61B circulating out of 24B max. Midnight trade detail link

The ZK architectur of Midnight is base on a research paper 'titled Kachina' published by researchers at IOG the research paper is "peer-reviewed" and "publicly available" the paper present a formal frame work of ZK smart contracts supporting public well as private state transition while ensuring a security properties in your data on chain.
i was able to reading is the abstract and introductin section the rest was beyond my current level is crypto graphy knowledge as the fact of that is the paper is peer review is good even i do not know how to evaluat the entire proof.
the design was submit to the academic scrutiny prior to the implemention of the production as a the claims were review by independent researcher aur this is the security properties are formally stated rather than being is asserted in a market document .
The problem with this is that there is a risk that academic security proofs do not necessarily translate well to production code a secure protocol can be insecurely implemented a paper does not discuss an audit of the implementation this is a separate requirement from reviewing a protocol in an academic setting. ZK proof for the new DUST spend .The cost of creating a ZK proof is much higher than the cost of verifying it , leading to a cost asymmetry ,self-inflicted upon the would-be attackers.
metric i am watching : a third - party security audit of the Kachina implementation , specificaly, and distinct from general smart contract audit .
how does the peer-reviewed academic basis affect your approach to evaluating the security claims made by a privacy protocol? drop in comments.
