been thinking about cross chain observability for a few days and the problem it surfaces is one midnight doesnt fully escape even with everything private state does right 😂
when a user moves assets between midnight and another chain the transaction on the counterpart chain is fully public. the receiving address, the amount, the timing - all visible to anyone watching. midnight controls what happens on its side of the bridge. it cannot control what the counterpart chain exposes on the other side.
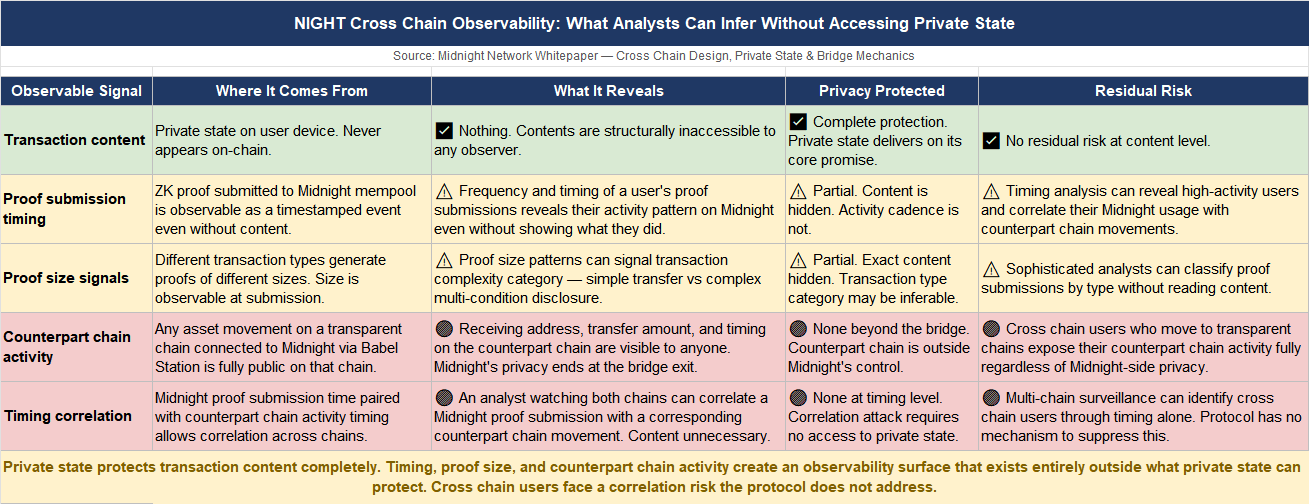
but the observability problem runs deeper than the bridge exit point.
an analyst watching multiple chains simultaneously can build a correlation picture that individual chain privacy cannot prevent.
if a large proof submission appears on midnight at a specific time and a corresponding asset movement appears on a transparent chain shortly after, the timing correlation is meaningful even without reading the midnight transaction content. the proof size, the submission frequency, the gap between midnight activity and counterpart chain activity - all of these signals exist at the chain level, visible without touching private state at all.
what midnight gets right is that this is a fundamentally harder problem than most privacy chains acknowledge. building genuine transaction privacy at the single-chain level is a solved problem in principle. building privacy that holds against a sophisticated analyst monitoring multiple chains simultaneously is a different order of difficulty. midnight at least does not pretend the cross-chain problem does not exist.
but i kept coming back to where the design leaves things unresolved.
the cross-chain invariant M.U + C.U ≤ S enforces supply consistency. it does not suppress observability signals on counterpart chains. nothing in the protocol design described in the whitepaper addresses traffic analysis across chains as a distinct attack surface.
the assumption appears to be that users who require cross-chain privacy beyond what the bridge boundary provides will manage that through their own operational choices - which chain they bridge to, how they time their movements, how they structure their counterpart chain activity.
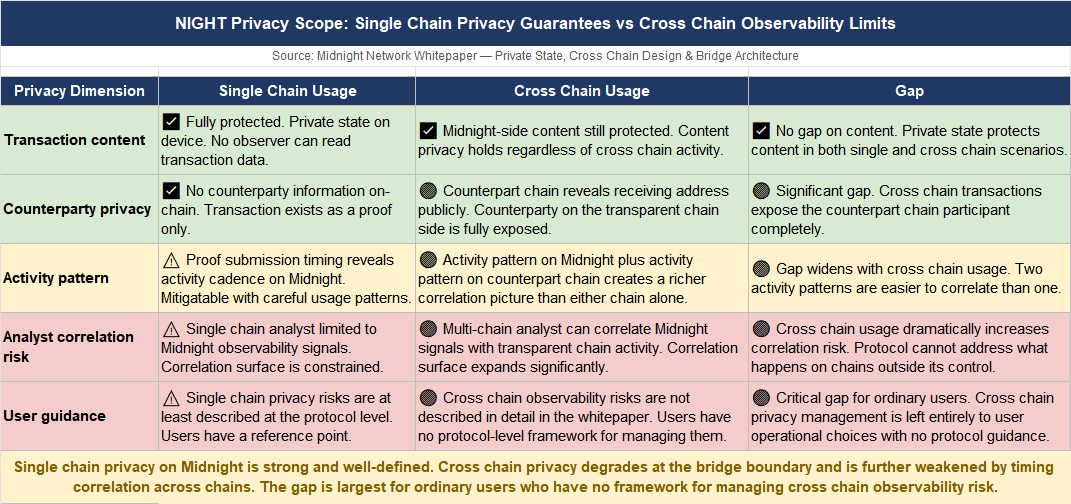
that is a reasonable assumption for sophisticated users.
it is a significant gap for ordinary users who have no framework for managing cross-chain correlation risk and no protocol-level guidance on what their counterpart chain activity reveals about their midnight usage.
honestly dont know if cross chain observability is a residual risk that sophisticated users can manage and ordinary users will simply accept or a structural gap in the privacy model that becomes more visible as cross-chain usage of midnight grows and analysts develop better correlation tooling.
privacy that holds within midnight or a model that stops at the bridge and leaves everything beyond it to the user to figure out?? 🤔
#night @MidnightNetwork $NIGHT
