Been going through midnight’s materials and i keep getting stuck on where the “real” execution actually happens. at first glance it reads like a privacy-first chain — zk proofs everywhere, users keep their data, validators just verify. but once you start mapping flows, it feels less like a clean abstraction and more like a layered system where privacy is selectively injected.
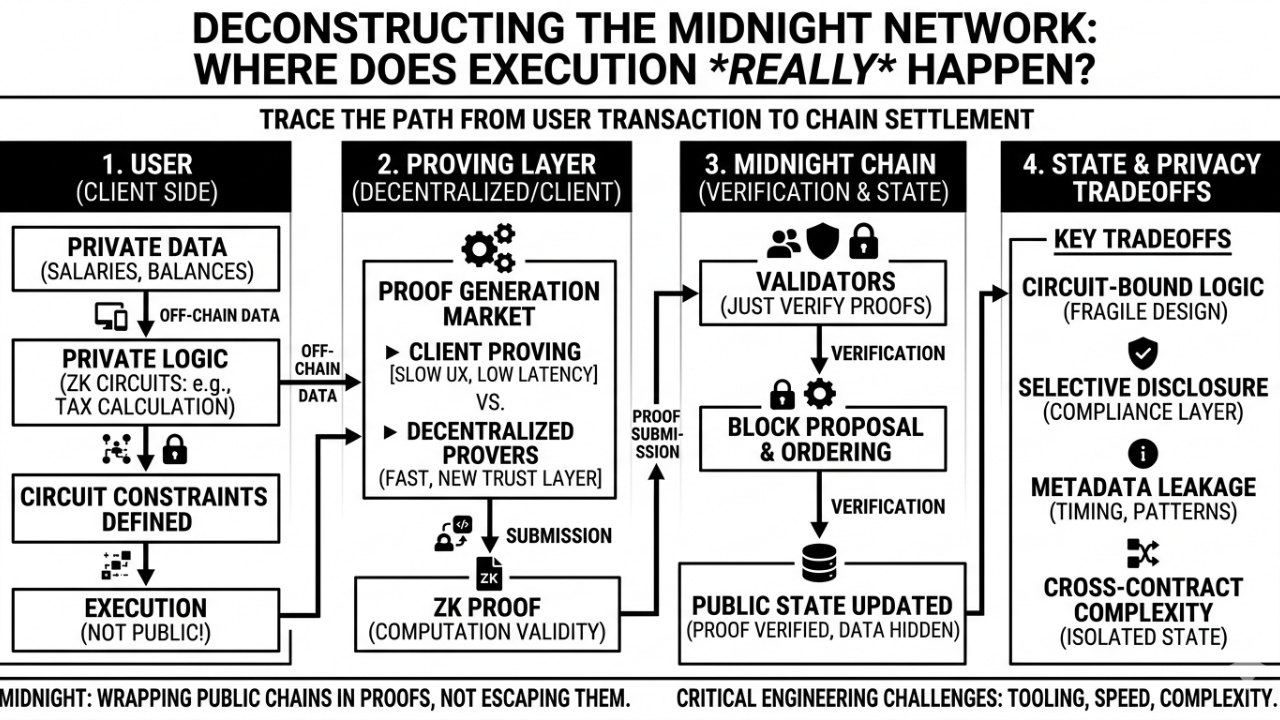
the simplified narrative people seem to hold is: midnight = private smart contracts by default. but that’s not quite accurate. what’s actually happening is that parts of the computation are proven off-chain and then verified on-chain, while the rest of the system — ordering, coordination, maybe even some state transitions — remains visible. so you’re not escaping the public execution model, you’re wrapping parts of it in proofs.
one core component is this idea of circuit-bound contract logic. instead of writing arbitrary code and letting the runtime handle it, you’re defining constraints that can be proven. that’s a big shift. it means contract design is no longer just about correctness and gas efficiency, but also about circuit size and proving feasibility. and honestly… that introduces a different kind of fragility. small design choices can have outsized effects on proving cost.
then there’s the role of validators. they don’t execute private logic — they verify proofs. that part is efficient and aligns with zk-first architectures. but it also means the chain’s security depends heavily on the correctness of the circuits themselves. if a circuit is flawed, validators won’t catch it as long as the proof is valid. so you’re moving trust from execution to specification, which feels subtle but important.
another piece is how users (or the system) generate proofs. i’m still not entirely clear if midnight expects a decentralized proving market, dedicated relayers, or mostly client-side proving. each path has tradeoffs. client-side proving can be slow and hardware-intensive. relayers or provers introduce a new dependency layer — maybe not fully trusted, but still critical for liveness. if proof generation becomes a bottleneck, the whole “private execution” story starts to degrade.
selective disclosure is also part of the design — users can reveal certain data when needed. that’s useful, especially for compliance-type use cases. but it assumes robust key management and clear policies around what gets revealed and when. and here’s the thing… once you allow partial disclosure, you open the door to correlation attacks if different pieces of data are revealed over time. i haven’t seen a strong story around that yet.
what’s not being talked about much is how tightly coupled all these layers are. circuit design affects proving time, which affects UX, which affects whether users rely on external provers, which in turn affects decentralization. it’s not modular in the way people might assume. also, composability becomes awkward. if contract A holds private state and contract B needs to interact with it, you either reveal something or construct cross-contract proofs, which quickly gets complex.
there’s also the assumption that hiding data is enough. but metadata — transaction timing, interaction frequency, contract call patterns — still leaks unless explicitly handled. so privacy is partial. not weak, but not absolute either. and depending on the use case, that distinction matters a lot.
the tension i keep coming back to is around readiness. a lot of the architecture seems to rely on future improvements — faster proving systems, better circuit abstractions, maybe specialized hardware. without those, building anything beyond simple patterns feels heavy. not impossible, just… costly in terms of engineering effort.
a concrete example: a private payroll system. you’d want to prove that salaries are calculated correctly without revealing amounts, maybe allow auditors to verify totals. midnight can support that pattern, but as soon as you add dynamic conditions (bonuses, taxes, multi-party approvals), the circuits grow and proving time increases. it works, but it’s not lightweight.
watching:
* how proof generation is actually handled in production (client vs network)
* whether developer tooling meaningfully abstracts circuit complexity
* how metadata leakage is addressed beyond basic zk guarantees
* real applications that sustain multi-step private interactions
i’m still trying to figure out if midnight is optimizing for a narrow set of privacy-critical use cases or aiming for general-purpose computation with privacy as a default layer. those are very different goals, and right now it feels like the system is balancing between them without fully committing to either.
$NIGHT @MidnightNetwork #night