I’ll be honest — I ignored this project at first.
The price action after TGE was weak. There was no strength, no real attempt at forming a base. Just a slow bleed mixed with occasional relief bounces that faded quickly. Token unlock schedules didn’t help either — steady emissions, early holders exiting, and a general sense that supply would continue to outweigh demand for a while.
Sentiment followed the chart. Mostly negative. People weren’t discussing the product — they were discussing the unlocks.
From a market perspective, it looked unattractive.
So I moved on.
Why I Came Back
What pulled me back wasn’t hype — it was a mismatch.
At some point, I noticed that while the token was under pressure, the underlying idea didn’t feel trivial. In fact, it felt like the kind of infrastructure that usually gets priced later, not early.
That disconnect made me curious.
Not bullish — just curious enough to take a second look.
What SIGN Actually Does (In Simple Terms)
At its core, SIGN is trying to solve a very practical problem:
How do you prove something about yourself — without exposing everything about yourself?
Think of it like this:
Input: A real-world credential (education, identity, ownership, eligibility, etc.)
Process: That credential gets verified by a trusted issuer
Output: You receive a cryptographic proof that you can present anywhere
Instead of repeatedly sharing raw data (IDs, documents, records), you carry verifiable proofs that confirm specific claims.
For example:
“I am over 18”
“I hold a valid license”
“I’m eligible for this program”
Without revealing your full identity.
How the System Coordinates
There are a few moving parts:
Issuers → entities that verify and issue credentials (institutions, governments, organizations)
Holders → users who receive and control these credentials
Verifiers → parties that need to confirm claims
Protocol layer → the infrastructure that standardizes how credentials are created, shared, and verified
The system doesn’t rely on constant re-verification. Instead, it creates portable trust.
Once something is verified, it can be reused.
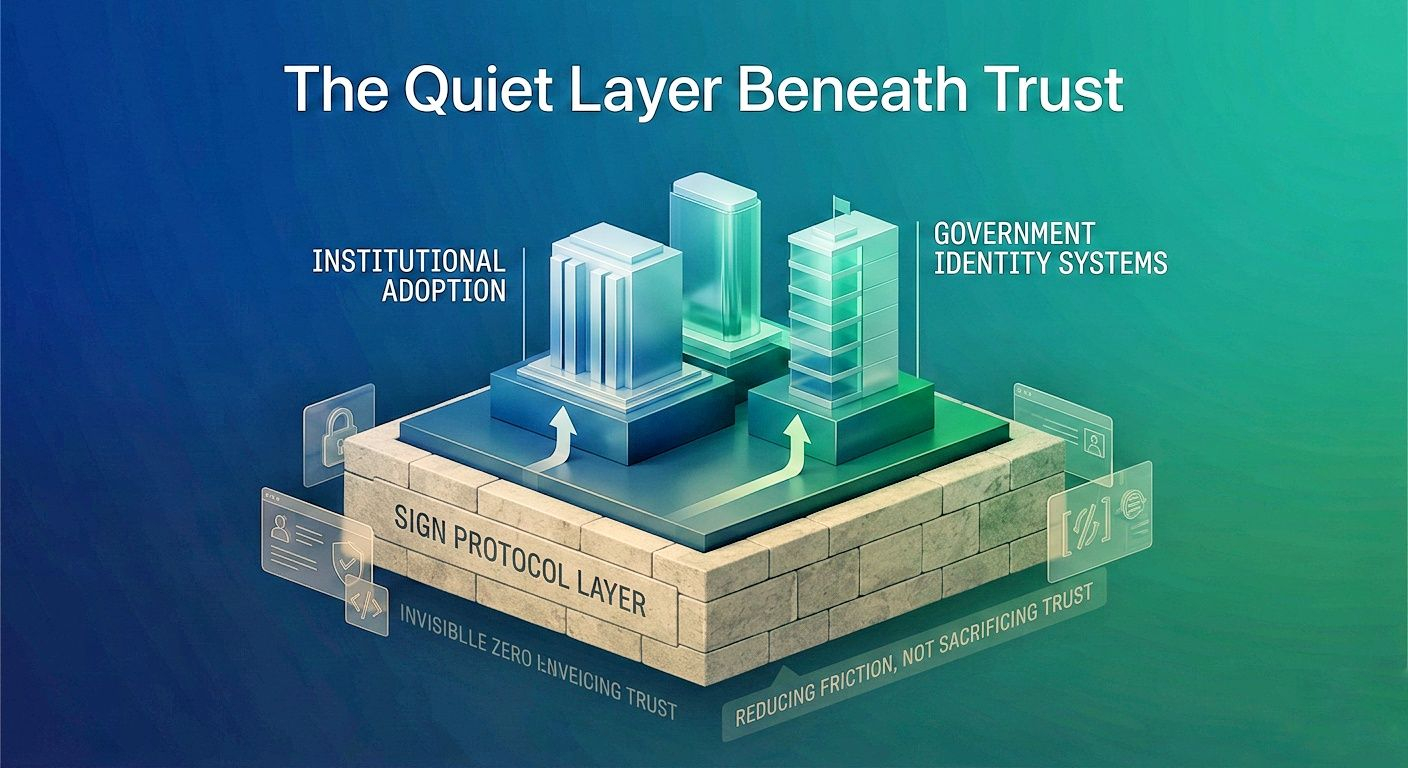
Where This Could Matter
This type of infrastructure isn’t flashy, but it’s foundational.
It matters most in environments where:
trust is required
coordination is complex
data privacy is critical
Examples:
government identity systems
cross-border compliance
institutional onboarding
digital credentials in education or employment
on-chain reputation systems
The idea is simple: reduce friction without sacrificing trust.
If it works, it becomes invisible infrastructure — the kind that everything else quietly depends on.
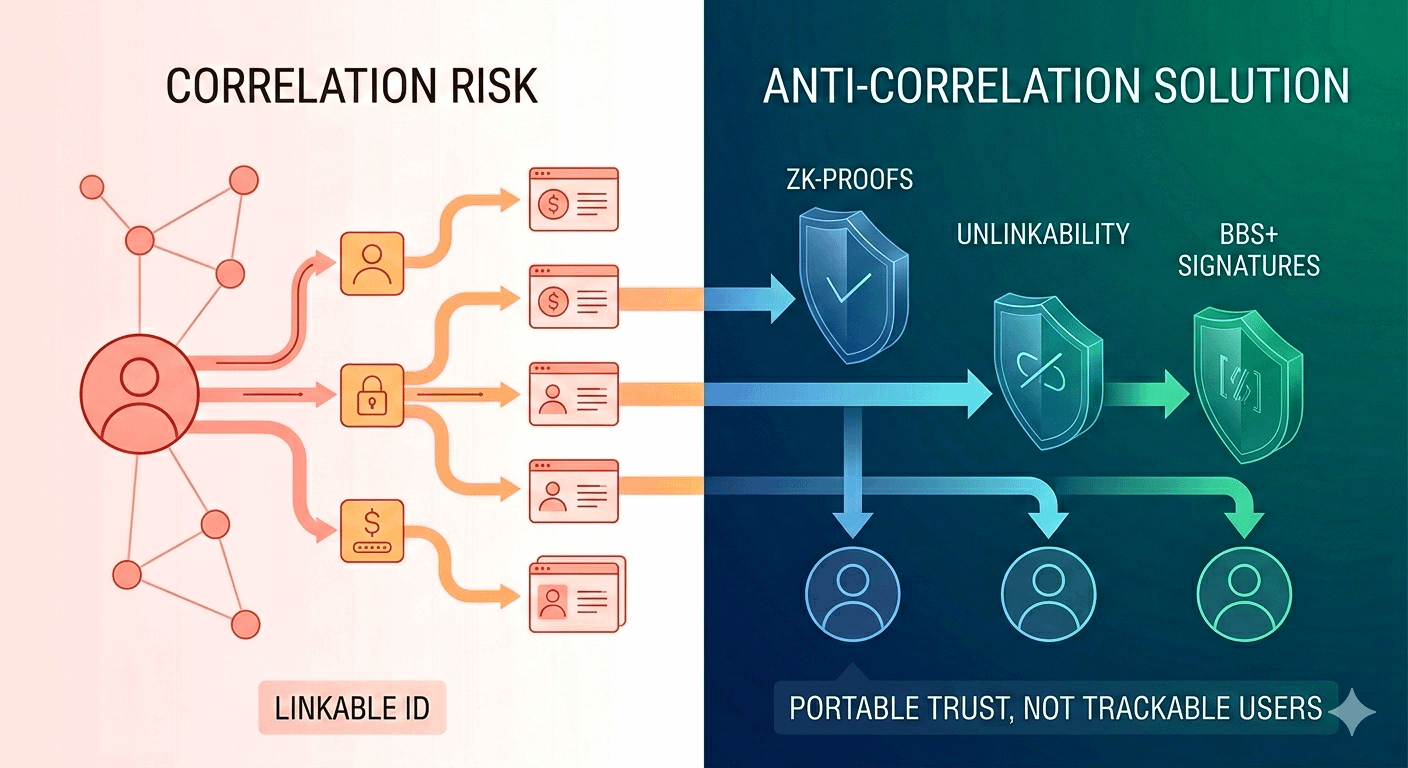
The More Interesting Problem: Correlation
But once I dug deeper, the real question wasn’t just verification.
It was correlation.
Even if you don’t reveal your identity directly, your activity can still be linked over time.
That’s where things get more technical — but also more important.
Preventing Correlation (In Plain Terms)
To reduce tracking and linking of user activity, systems like SIGN explore tools such as:
Unlinkability
Each interaction should look independent. No obvious way to connect them.
Zero-knowledge proofs
You prove something is true without revealing the underlying data.
Rotating identifiers
Instead of one persistent identity, you use changing identifiers across contexts.
BBS+ signatures
A more flexible way to prove selective parts of a credential without exposing the whole thing
The goal is simple:
Let users prove things — without becoming trackable.
But There Are Trade-Offs
This is where things get less clean.
1. Preventing Correlation vs Long-Term Trust
If identities constantly rotate, how do you build reputation over time?
At some point, systems need continuity.
2. Unlinkability vs Usability
The more private a system becomes, the more complex it often is.
Users — and institutions — tend to prefer simplicity.
3. Decentralization vs Coordination
Even “decentralized” systems still depend on:
issuers
registries
policy frameworks
Someone still decides what counts as valid.
So the question becomes:
Where does trust actually live?
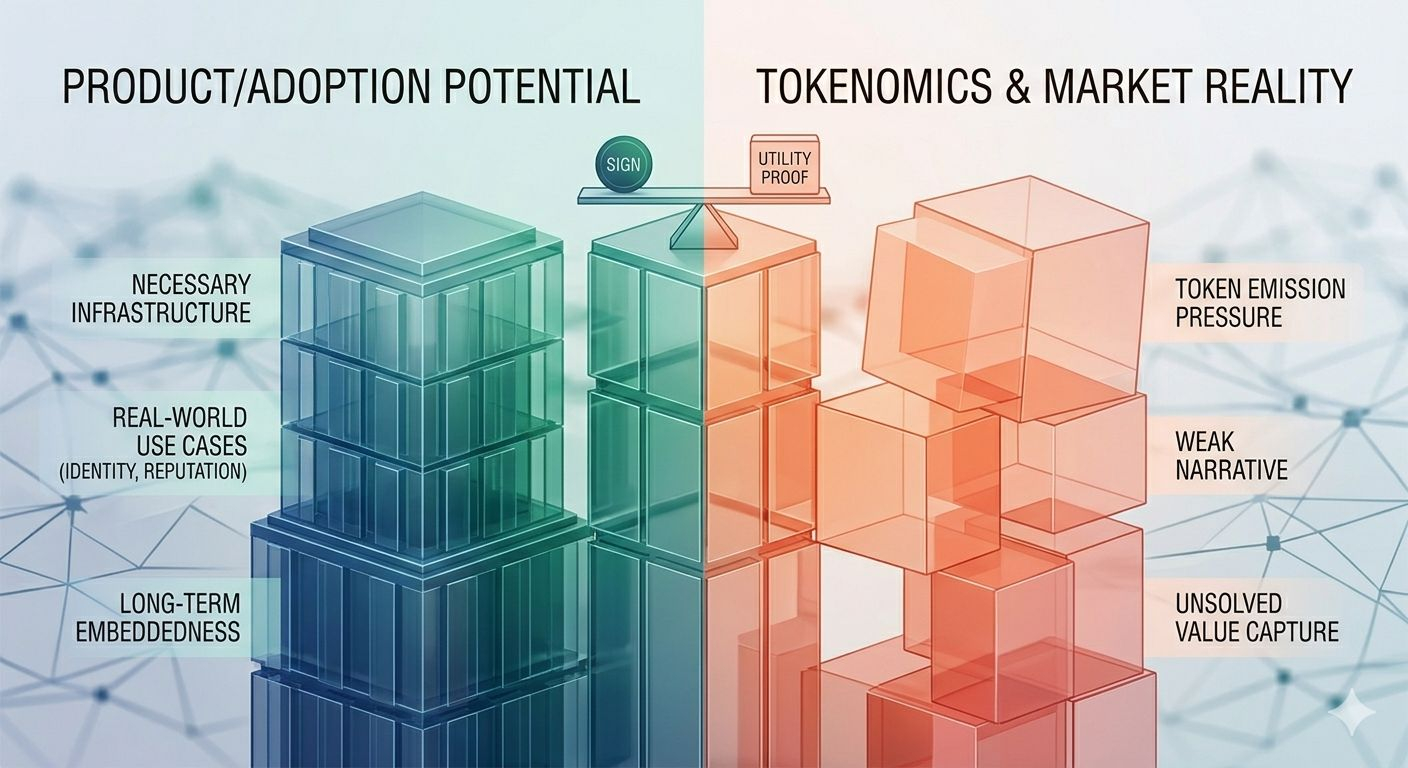
The Dual Reality
This is where my view splits into two tracks.
On One Side:
The product makes sense.
There is real infrastructure here.
It addresses a problem that will likely grow over time.
And if adoption comes, it could become deeply embedded.
On The Other:
The token structure is… difficult.
ongoing unlocks
emission pressure
unclear value capture
Even if the system succeeds, it’s not obvious that the token benefits proportionally — at least not in the short term.
Why the Market Might Be Ignoring It
A few reasons stand out:
Complexity → hard to understand, harder to price
Weak narrative → not exciting compared to consumer-facing trends
Token design → supply overhang reduces urgency to buy
Timing mismatch → infrastructure often gets recognized late
The market tends to reward simple stories first.
This isn’t one of them.
Risks That Still Matter
There are still open concerns:
Will institutions actually adopt this model?
Can the system scale without reintroducing central points of control?
Does the token meaningfully capture value?
How dependent is it on external issuers behaving honestly?
Can privacy features hold up under real-world pressure?
None of these have clear answers yet.
Where I Stand Now
I’m not fully convinced.
But I’m no longer dismissive either.
What I’m watching:
real-world integrations
consistent usage growth
evidence of revenue or sustainable demand
improvements in token design or value capture
What would invalidate the thesis:
no meaningful adoption
continued token dilution without demand
reliance on centralized actors that undermine the core premise
Final Thought
The idea behind SIGN is compelling — not because it’s exciting, but because it’s necessary.
But necessity doesn’t always translate into immediate value.
And even if correlation is reduced at the surface…
is it truly eliminated — or just pushed deeper into layers we don’t easily see?
@SignOfficial #SignDigitalSovereignInfra $SIGN