spent the last couple days on the security and privacy section and one phrase kept stopping me cold 😂
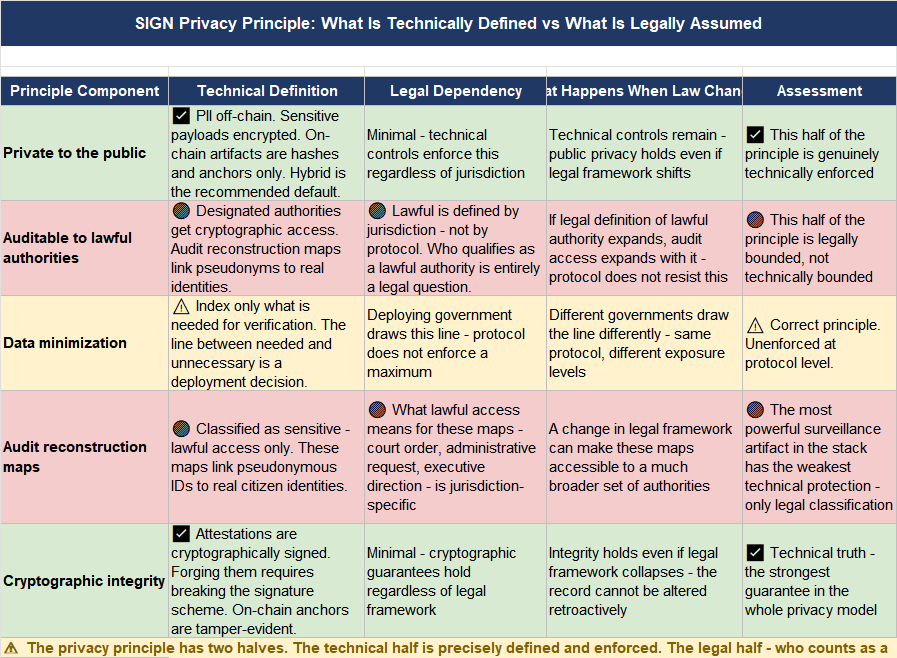
honestly? its the design principle the whole stack is built on. "private to the public, auditable to lawful authorities." five words that sound like a clean answer
the more i pulled at them the more i realized they are actually a question dressed up as a solution.
here is the thing.
private to the public
that part is technically defined. PII stays off-chain. sensitive payment details dont go on the public ledger. on-chain artifacts are proofs and anchors only. schema IDs. attestation hashes. revocation registry references. rule version hashes. the docs are specific about what belongs where. that half of the principle has a real technical implementation behind it.
auditable to lawful authorities - this is where i got stuck.
lawful is not a technical property. it is a legal one. and it changes. what counts as lawful authority in one jurisdiction isnt lawful in another. what a government can legally access today it may not be able to access after an election, a court ruling, a constitutional challenge. the protocol doesnt define lawful. it assumes that definition exists somewhere outside itself and builds toward it.
the data placement model makes this concrete. the docs recommend hybrid as the default - sensitive payloads off-chain encrypted, integrity anchors on-chain, index only what is needed for verification. clean architecture
but the line between what is needed for verification and what crosses into unnecessary exposure is drawn by the deploying government
not by the protocol.
i kept thinking about the audit reconstruction maps specifically. same as i kept watching SIREN and PIPPIN chart
the docs classify them as sensitive - lawful access only
these are the maps that link pseudonymous identities to real ones. the most powerful surveillance artifact in the whole stack. the protocol says lawful access only. it doesnt say who decides what lawful means in practice
that decision sits entirely outside the technical layer.
what the design gets right is the separation itself. keeping PII off-chain is the correct call. building integrity anchors rather than full records on-chain is the correct call. the architecture is genuinely privacy-forward compared to systems that default to full public transparency.
the gap is that the privacy guarantee is only as strong as the legal framework that defines its outer boundary. a government deploying SIGN in a jurisdiction with strong data protection law gets one version of this principle. a government deploying it somewhere with weak or nonexistent privacy law gets a technically identical system with a completely different real-world privacy outcome.
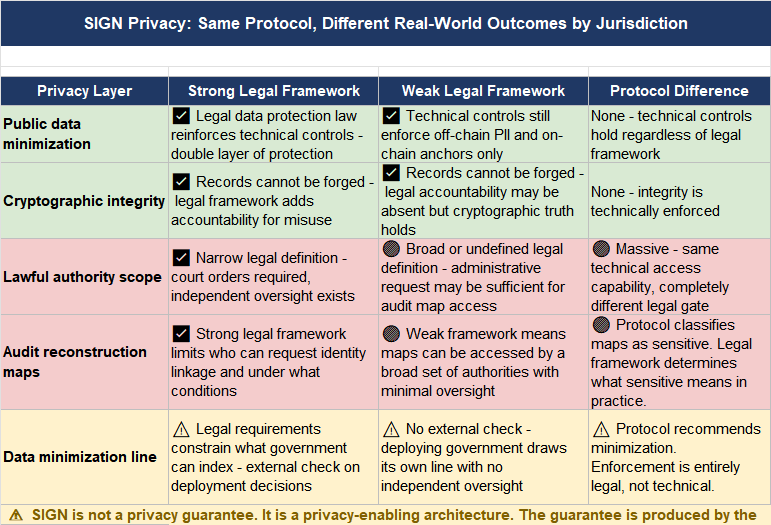
the protocol is the same. the protection isnt.
honestly dont know if "private to the public, auditable to lawful authorities" is a genuine privacy architecture or a technically sound framework that quietly outsources its hardest guarantee to legal systems it has no control over.
privacy principle that holds across deployments - or a design that is only as protective as the jurisdiction it lands in?? 🤔
#SignDigitalSovereignInfra @SignOfficial $SIGN
