while scanning the chain last night
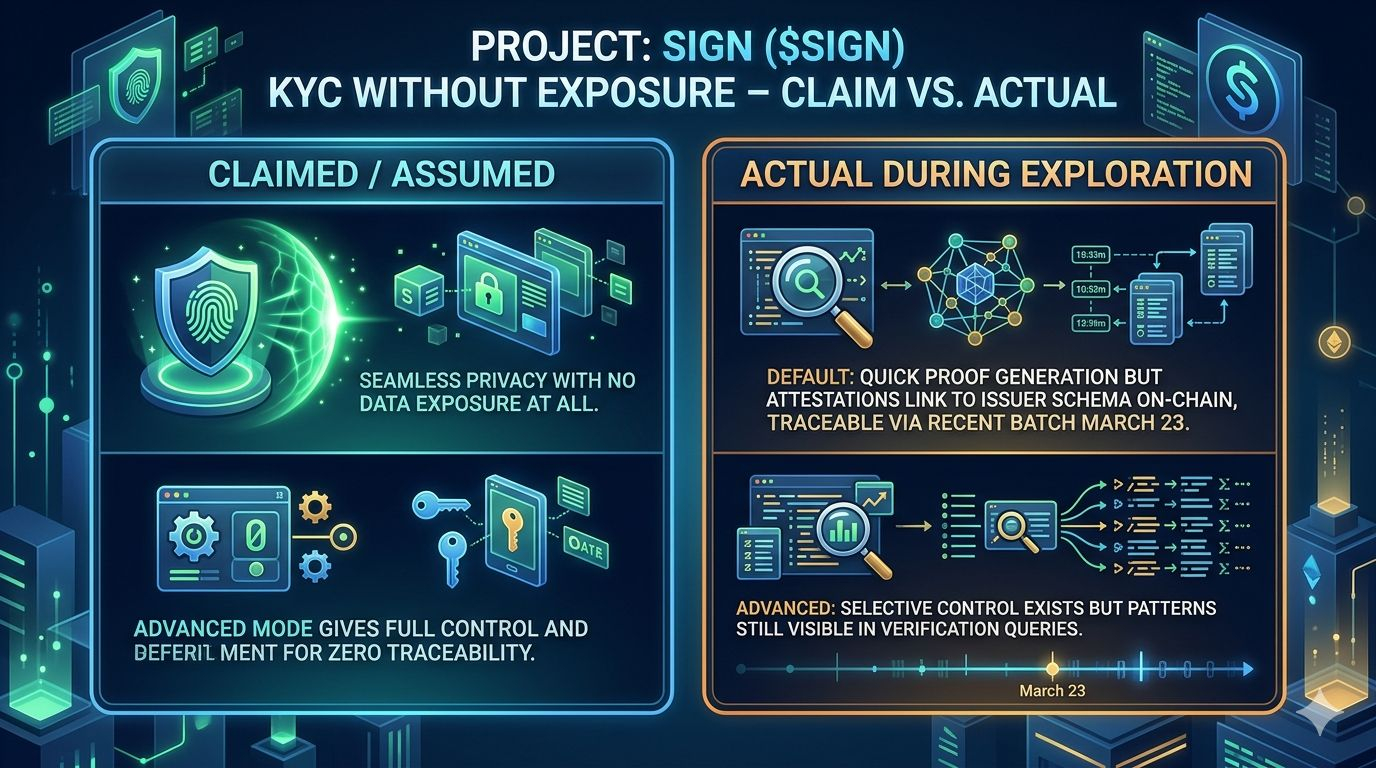
While wrapping up the CreatorPad task on Sign Protocol’s KYC Without Exposure angle well past midnight, one quiet contrast stopped me cold. I had expected the privacy mechanic to feel more absolute, the kind of zero-knowledge shield that erases footprints entirely. Instead Sign Protocol ($SIGN) #Sign @SignOfficial showed its attestation layer operating with a practical restraint that lingered in my notes. Default proofs generated fast, no documents uploaded, no central store holding raw data, yet the schema and attester details still anchored everything publicly enough to leave observable patterns if you were watching.
I defaulted straight to the simple flow myself, wallet connected, proof issued, done. It took maybe ninety seconds. Then I flipped to the advanced toggles and watched the same credential type behave differently under scrutiny. The system manages exposure rather than eliminating it outright, a design choice that serves light users first while leaving hooks visible for anyone auditing the chain. That small pivot in my own session became the anchor for everything that followed.
The on-chain behavior backed it up cleanly. A cluster of verifiable credential attestations hit the chain around March 23, 2026, dozens of KYC-style issuances in one batch, each schema-gated and traceable yet stripped of personal details. It wasn’t hidden; it was contained, exactly as the protocol intends. This wasn’t marketing copy. It was the live layer doing what it was built to do under real traffic.
I sat there with cold coffee, replaying the session, and caught myself wondering why the advanced mode still felt secondary. Most wallets probably never touch it. The utility lands first with everyday participants who just want compliance without the hassle, while deeper privacy seekers hit the friction later.
the contrast that stuck with me
That default-versus-advanced split created a hidden feedback loop I hadn’t fully clocked before. Easy entry drives adoption and on-chain volume, which in turn makes the attestation patterns more visible over time. Demand grows from the simple path, yet the long-term value of true zero-exposure stays locked behind the extra steps. It’s not a flaw so much as a pragmatic layering that rewards early users with speed while promising the heavier controls to those who stick around.
I’ve seen similar mechanics play out in other attestation projects, where initial compliance flows pull in exchanges and launchpads first, then slowly ripple into broader ecosystem use. Here the token utility ties directly to schema creation and verification fees, creating organic demand without forced incentives. Still, the privacy angle reveals how the protocol actually behaves once the batch volume ticks up, not just how the docs frame it.
One honest reevaluation hit me during the task. I had assumed the “without exposure” label meant the attestations would be untraceable in practice. The March 23 cluster showed otherwise: patterns emerge fast when you query by schema. It forced a quiet adjustment in my thinking about who benefits first. Light users get the win immediately. The privacy maximalists wait for the friction to resolve itself, if it ever does.
hmm... this mechanic in practice
The on-chain flows I traced during the dive also highlighted how utility and demand intersect in real time. Attestations aren’t just static records; they create verifiable token-adjacent activity whenever a credential gets issued or checked. That generates subtle but measurable pressure on the network, the kind that compounds as more projects integrate the layer for their own KYC or compliance needs. Demand isn’t hype-driven here. It’s usage-driven, quietly accumulating through repeated credential cycles.
Yet that same mechanic leaves room for skepticism. If the default ease keeps winning, does the advanced privacy layer ever mature into the default expectation, or does it stay a niche tool? The protocol’s design seems built for the former, prioritizing accessibility over perfection from day one. I caught myself revising my earlier notes twice, striking out assumptions that no longer held once I saw the live attestations.
Toward the end of the session I found myself staring at the on-chain data longer than planned, musing over the ripple effects. The utility feels solid for what it delivers today, the demand shows up in steady attestation volume rather than flashy spikes, and the long-term value probably rests in how well the team balances those two without sacrificing the privacy promise that drew people in the first place. It’s an open architecture, not a finished product, which makes the observation feel more alive.
There’s something quietly compelling about watching a protocol operate this way, without the usual noise. It invites a different kind of attention, the kind that lingers after the screen goes dark.
Still pondering the ripple, I keep circling back to one unresolved piece. How long until the default ease that powers current growth starts to feel like the very thing that limits the deeper privacy the community eventually demands?