@SignOfficial #SignDigitalSovereignInfra $SIGN
I was looking through some timestamps and caught something pretty interesting: an attestTimestamp that exactly matched the revokeTimestamp. Zero gap. That really shouldn't happen.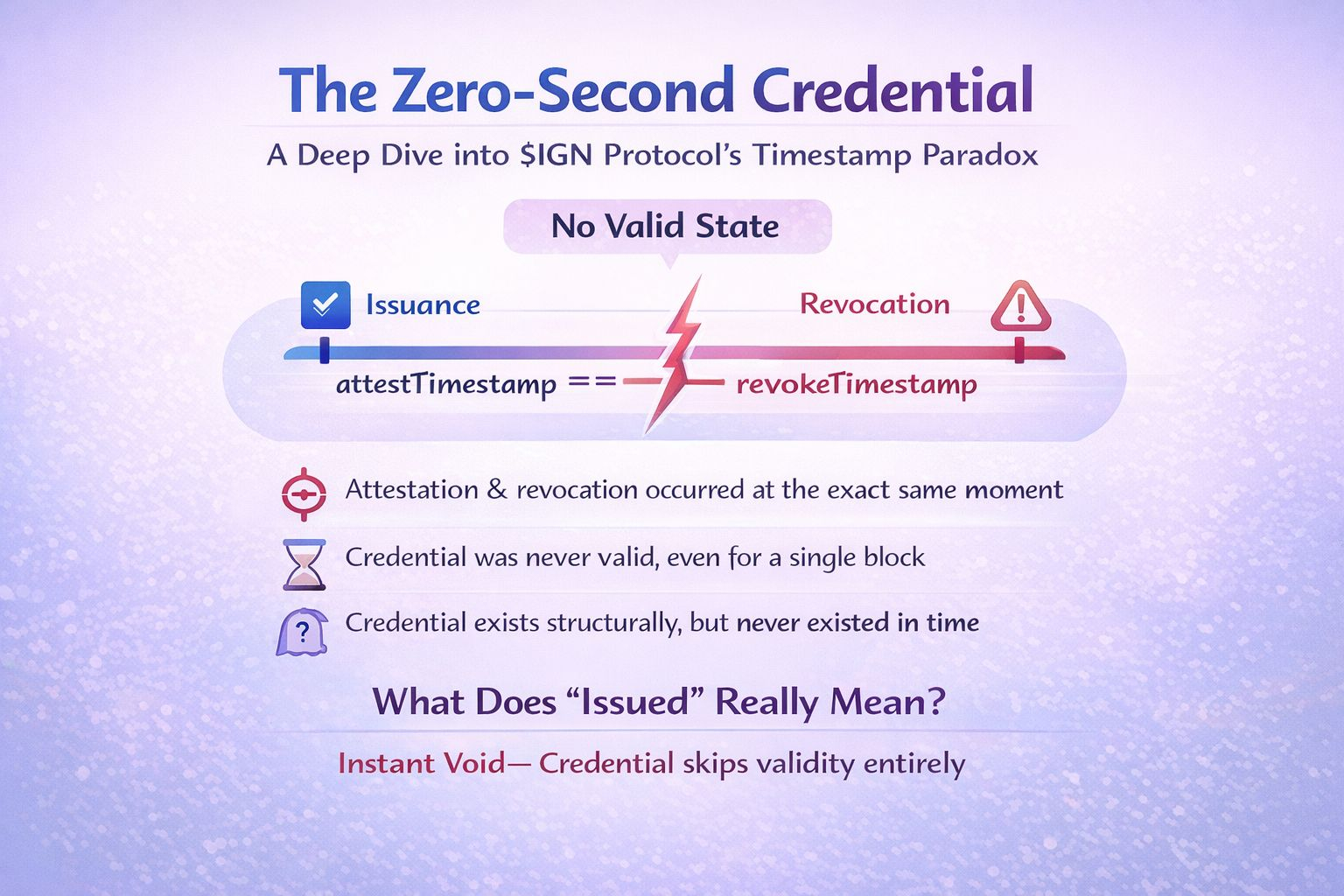
I checked another one from a completely different issuer and saw the exact same pattern. At first, I assumed it was just a timing quirk—like the revocation landed right after the issuance. But there was no "after." SIGN records both events independently, and they resolved to the exact same moment.
Basically, this means the credential never actually had a valid state. Not even briefly, and not even for a single block. There was zero window for any system to read it as valid. It wasn't just a revoked credential; it completely skipped validity. Instant void. It exists in structure, but it technically never existed in time.
I traced how the system handles it, and it actually resolves. The schema loads, the issuer checks out, and everything passes on the surface. You'd only catch the issue if you read the timestamps directly.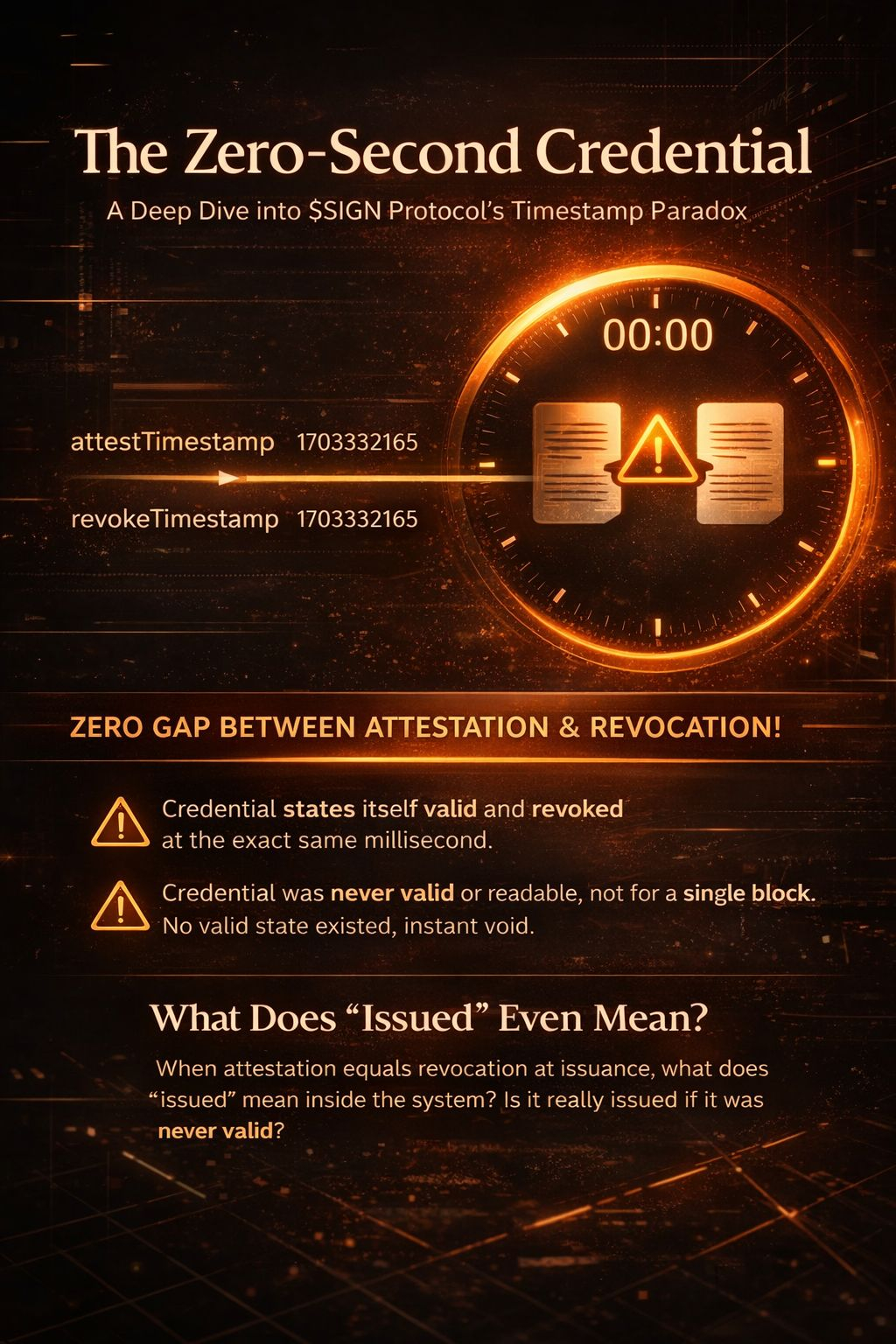
This is where $SIGN really starts to matter. It only matters if the protocol can actually distinguish between an attestation where attestTimestamp == revokeTimestamp and one that was actually valid before being revoked later. Because right now, both resolve the exact same way.
So it brings up a bigger question: if the issuance process can produce something that was never valid for even a split second, what exactly does “issued” mean inside the system?
#SignDigitalSovereignInfra #Sign $SIGN

