Market was kind of boring today. Nothing moving, nothing breaking, so I ended up down a rabbit hole I didn't expect to spend three hours in.
I was looking at $SIGN — not the token price, not the roadmap — specifically the verification flow. How an attestation actually moves from creation to the moment someone trusts it. I wasn't planning to write anything. I was just curious in that directionless way you get when charts aren't giving you anything to react to.
And then something clicked in a way that I'm still turning over.
I thought the security story in Sign was about the cryptography. Signatures, on-chain anchoring, schema hashing. That stuff is real and it works. But the more I traced the actual flow — from the moment an attacker might try to insert something false to the moment a downstream system decides to accept it — the more I realized the cryptography isn't where the exposure lives.
The exposure lives in a step most people skip entirely when they think about how verification works.
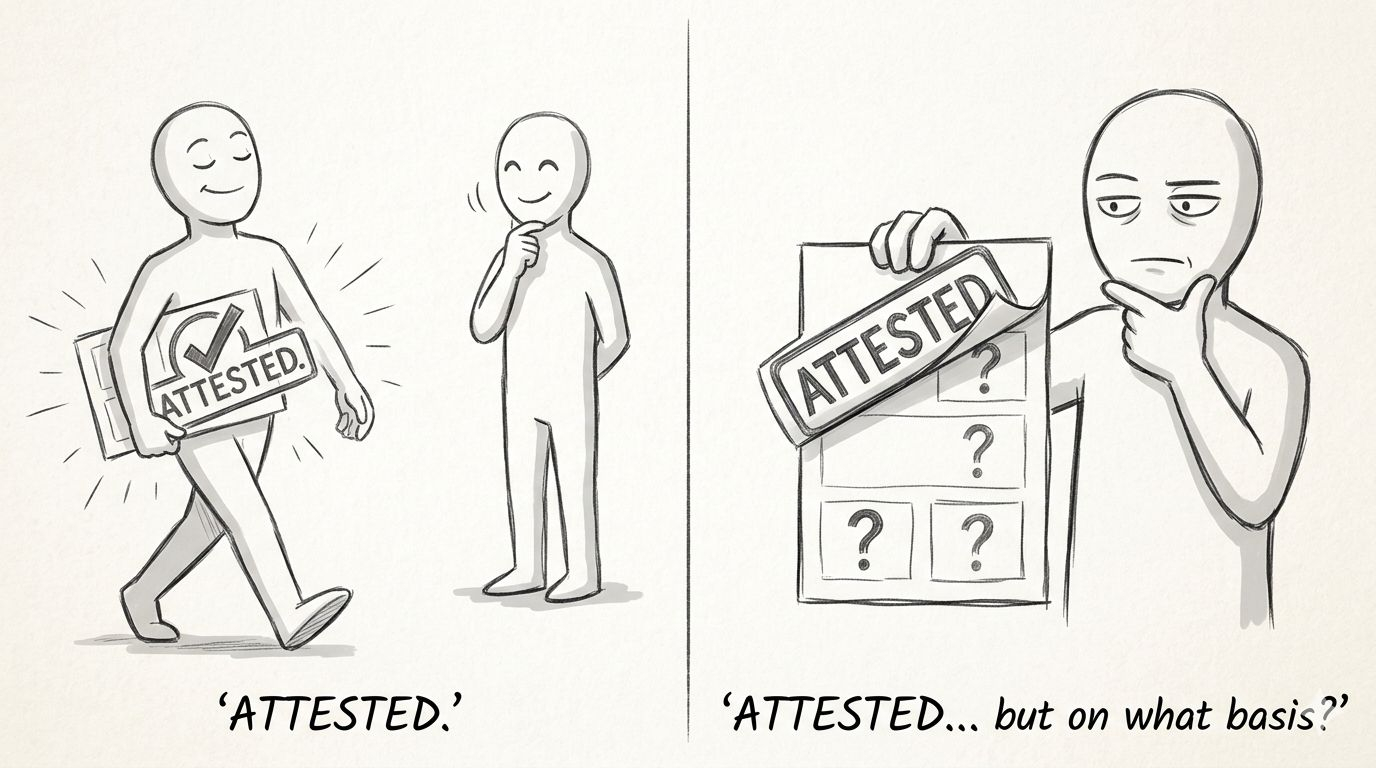
Here's what I mean. When Sign produces an attestation, it's cryptographically sound. The claim is signed, the schema is referenced, the record exists on-chain. A downstream system — an app, a protocol, a wallet — receives that attestation and makes a decision based on it. The decision is almost always binary: attested, or not attested.
That's the gap.
The downstream system is trusting the attestation. It is almost certainly not inspecting the schema the attestation was built on. And the schema is where the meaning lives. Two attestations can both be cryptographically valid, both exist on-chain, both pass every technical check — and carry completely different levels of real-world trustworthiness depending entirely on who wrote the schema and under what conditions.
An attacker who understands this doesn't touch the signing layer. They don't need to. They publish a schema that mimics the structure of a credible one, issue technically valid attestations against it, and wait for a downstream consumer to treat those attestations as equivalent to ones issued on a schema with actual social legitimacy behind it.
The protocol did nothing wrong. The cryptography held. The attack happened in the gap between what "verified" means technically and what people assume it means in practice.
But here's the part that bothers me.
I'm not sure Sign can close that gap at the protocol level. The whole value of an open attestation system is that anyone can define schemas. The moment you start gatekeeping schema creation, you've reintroduced a trust hierarchy that the system was partly designed to move past. There might not be a clean technical fix here. The defense probably has to come from the ecosystem — aggregators, reputation layers, maybe curation markets for schemas — none of which exist yet in any meaningful form.
And that's uncomfortable to sit with, because it means the security model of Sign's verification flow is partially dependent on infrastructure that hasn't been built. Right now, a sophisticated consumer would need to manually evaluate schema provenance before trusting an attestation fully. Most consumers won't do that. Most consumers will see "attested" and stop reading.
I thought about this in terms of something simpler. It's like a notarized document. The notary stamp is real. The notary verified identity and signature. But the notary didn't verify whether the content of the document is true or whether the person presenting it had the authority to make that claim in the first place. The stamp is genuine. The document can still mislead.
Sign's attestation is the stamp. The schema is the document underneath it. Most people are only checking for the stamp.
I'm not saying this makes Sign broken. I think it makes Sign an interesting infrastructure bet — one whose security properties mature as the ecosystem around schema credibility matures with it. But I don't think that timeline is priced into how people are currently talking about the verification flow.
Anyway. Nothing resolved here. I'll probably spend tomorrow watching the same charts do nothing and thinking about this more than I should.
@SignOfficial #SignDigitalSovereignInfra