What I find interesting about SIGN is that it doesn’t try to replace Web2 verification. It leans into it. Most systems in crypto want to rebuild identity from scratch but SIGN quietly assumes that verification already exists somewhere else. The real problem is execution. How do you take something verified off-chain and make it usable on chain without trusting a middleman?
That’s where SIGN starts to feel practical to me. Instead of storing identity it stores attestations. Someone trusted verifies something about you then issues a credential on-chain. It’s not your identity in full. It is a claim that can be checked and used. That small shift changes how the system behaves.
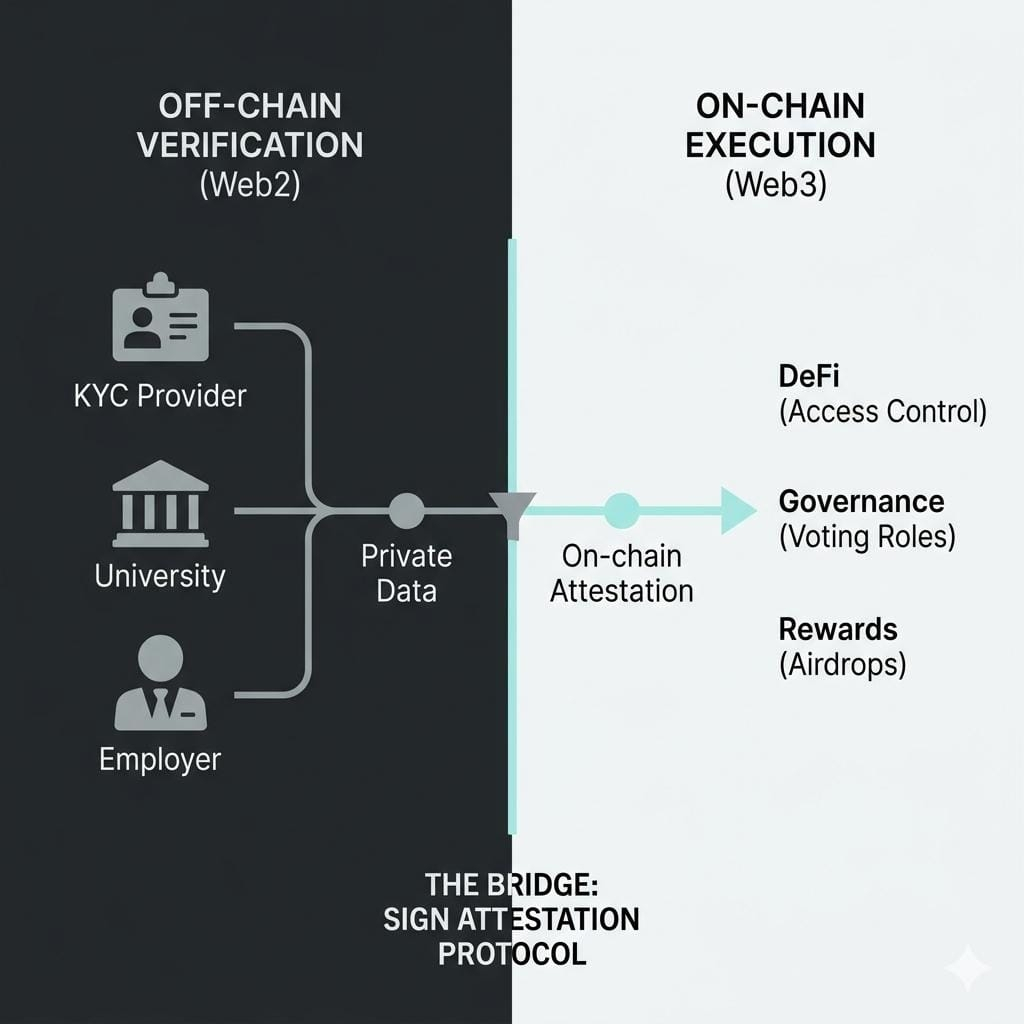
Think about KYC. Normally you submit documents to a centralized platform and they keep that data. With SIGN the verification can still happen off-chain, but the result becomes an on-chain attestation. The attestor confirms you passed KYC, but your personal data isn’t exposed. What matters is that a trusted entity signed off on you.
But this also raises a question I keep coming back to. Who decides which attestors are trustworthy? SIGN doesn’t remove trust. It redistributes it. If a weak or biased attestor issues credentials, the whole system downstream inherits that risk.
Educational certificates are another case where this design feels natural. A university can issue an attestation that you graduated. That credential lives on-chain and can be verified instantly. No need to email records or rely on manual checks. The logic is simple but the impact is real when you connect it to execution.
What makes SIGN different is that these attestations are not passive. They plug directly into actions. A protocol can check your credential and decide if you qualify for something. Access, rewards, roles. It all flows from that single verified claim.
I’ve seen this become more interesting with contributor proof. Instead of vague reputation you get specific attestations. You contributed to a project. You completed a task. You participated in governance. Each one is issued by an attestor who observed or verified that action. Over time, this builds a layered identity that feels more grounded than a wallet history.
But again, there’s a subtle weakness. Contribution is subjective. If attestors have incentives to over-issue credentials, the system can inflate trust artificially. SIGN gives you the tools, but it doesn’t fully solve human bias.
Event participation is where things get very tangible. Attend a conference join a campaign complete a program. Instead of a QR code or email confirmation that disappears, you receive an on-chain attestation. That proof can later unlock access or rewards. It turns moments into reusable signals.
This ties directly into token distribution, which I think is one of SIGN’s strongest use cases. Airdrops and rewards often struggle with Sybil attacks. Fake accounts, duplicated participation, manipulated activity. With SIGN, eligibility can depend on verified credentials instead of raw wallet behavior. It doesn’t eliminate Sybil risk completely, but it makes it harder to fake meaningful participation.
Still, I don’t think this is a perfect system. If attackers find ways to game attestors or create low quality verification loops, the protection weakens. The strength of SIGN depends heavily on how strict and honest the credential issuers are.
What I like is how everything connects back to trust between attestors and users. Users don’t need to expose everything. Attestors don’t control execution. And protocols don’t need to guess who is real. The attestation becomes the bridge.

In that sense, SIGN isn’t trying to decentralize identity fully. It is trying to make verified claims usable in a decentralized environment. That feels like a more realistic step forward.

