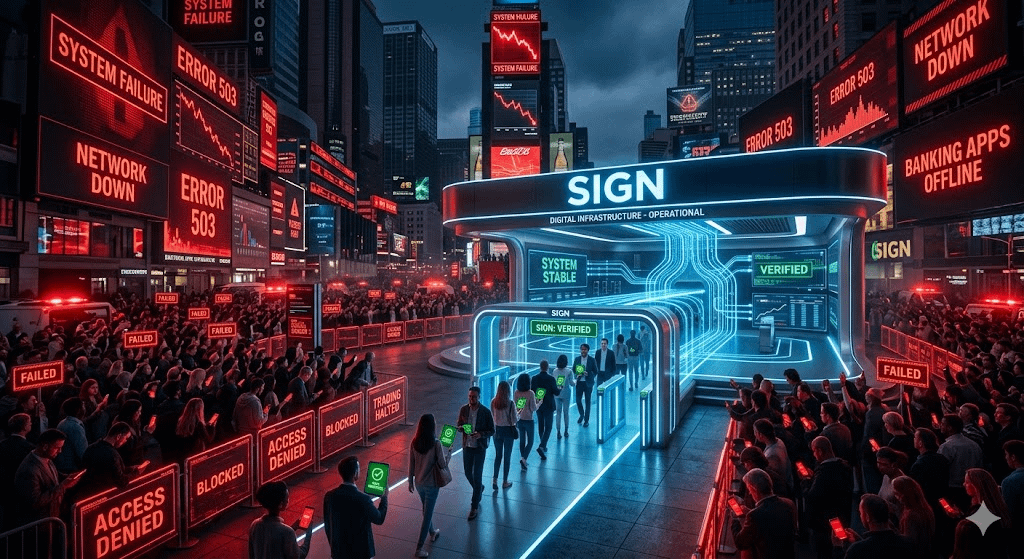
Most of the time, infrastructure doesn’t get tested when everything is running smoothly. It gets tested when something breaks. And in crypto, things break more often than people admit.
I’ve seen platforms freeze during volatility, access get restricted at the worst possible moment, and systems that looked solid suddenly fail when they were needed most. That’s usually when you realize the difference between something that works in theory and something that holds up in practice.
That’s the lens I ended up using when I looked at SIGN.
At first, it didn’t feel that different from other infrastructure projects. There’s always a narrative around verification, identity, or coordination. But what made me pay a bit more attention here was the focus on continuity. Not just proving something once, but making sure it doesn’t have to be proven again every time the environment changes.
That might sound like a small detail, but it adds up quickly.
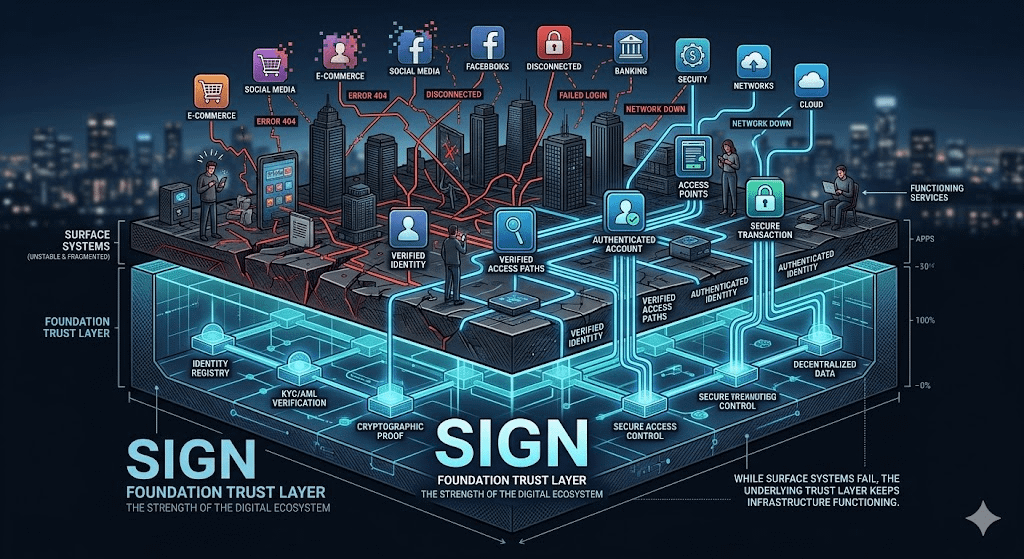
Think about how many systems rely on repeated checks. Every platform wants to verify you in its own way. Every network rebuilds trust from scratch. It works, but it’s inefficient. And more importantly, it becomes fragile under pressure. The more steps required to confirm something, the more chances there are for the process to slow down or fail.
What SIGN seems to be doing is shifting that pattern slightly. Instead of forcing constant re-verification, it creates a structure where credentials can be issued once and then reused across different systems. Not blindly, but in a way that preserves context.
From what I can tell, this is already being applied in areas like token distribution, onboarding, and basic access control. These are not headline-grabbing use cases, but they’re practical. They happen often, and they expose inefficiencies clearly.
And that’s where the idea of resilience starts to matter.
Because in stable conditions, almost any system can look reliable. The real question is what happens when those conditions change. When markets move fast, when platforms disconnect, or when coordination between systems starts to break down.
In those moments, repetition becomes a problem. Every extra step slows things down. Every dependency creates risk.
A system that can reduce those dependencies, even slightly, starts to feel more stable.
Still, I don’t think this is something to assume will work perfectly. Building infrastructure at this level is complicated. It’s not just about the technology. It’s about whether different systems are willing to rely on the same layer of trust.
That’s not an easy shift, especially in regions like the Middle East, where different frameworks and institutions operate side by side. Growth is happening quickly, but alignment doesn’t come automatically.
There’s also the question of scale. It’s one thing to support a few workflows. It’s another to become something that multiple systems depend on consistently.
So I find myself in a position where I can see the direction, but I’m not fully convinced yet.
What I do find interesting is that SIGN isn’t trying to compete for attention in the usual way. It’s focused on something quieter. Something that only becomes visible when things go wrong.
And maybe that’s the point.
Because when everything is working, infrastructure doesn’t stand out. But when something fails, you notice immediately what holds and what doesn’t.
I’m not making a strong call here. It’s too early for that.
But I am paying attention to how this develops, especially in real conditions, not just controlled ones.
Because in the end, it’s not about whether a system works when it’s easy.
It’s about whether it still works when it isn’t.
@SignOfficial $SIGN #SignDigitalSovereignInfra
