The failure starts after the right number is already on screen.
The user opens the real site. The real page loads. The balance is there. The account status is there. The qualification is there. The approval team should be able to move. Instead the case stalls. Support asks for a screenshot. Compliance asks for a PDF. The user has to export a page the browser already saw because the next system still cannot use that fact in a form it can act on.
That is the ugly handoff. The truth is already visible in a normal HTTPS session, but the decision point lives somewhere else, so the workflow falls back into files, inbox threads, and manual notes. Now the operator is not approving a proven fact. The operator is approving an image of the page that contained the fact. The browser already did the seeing. The workflow still behaves as if nothing counts until someone uploads a document.
That is why this SIGN flow caught my attention. In its MPC-TLS plus zkProof setup, the verifier joins the TLS session without learning the plaintext, then the user and verifier jointly produce a zero-knowledge proof about the encrypted browser-visible data. The part that matters here is simple. The number on the page does not have to be turned into a screenshot just to survive the next step. The browser session itself can produce proof.
That still would not solve much if the proof only helped in that one moment. The stronger part is what happens after the browser step ends. Sign Protocol turns that validation result into a structured attestation. SIGN also says the captured TLS session and zk proof can be encrypted and permanently stored for later retrieval. So the useful object is no longer the page export. It is the attested result that came out of the session. The tab closes, but the evidence needed for approval is still available in a form another system can consume.
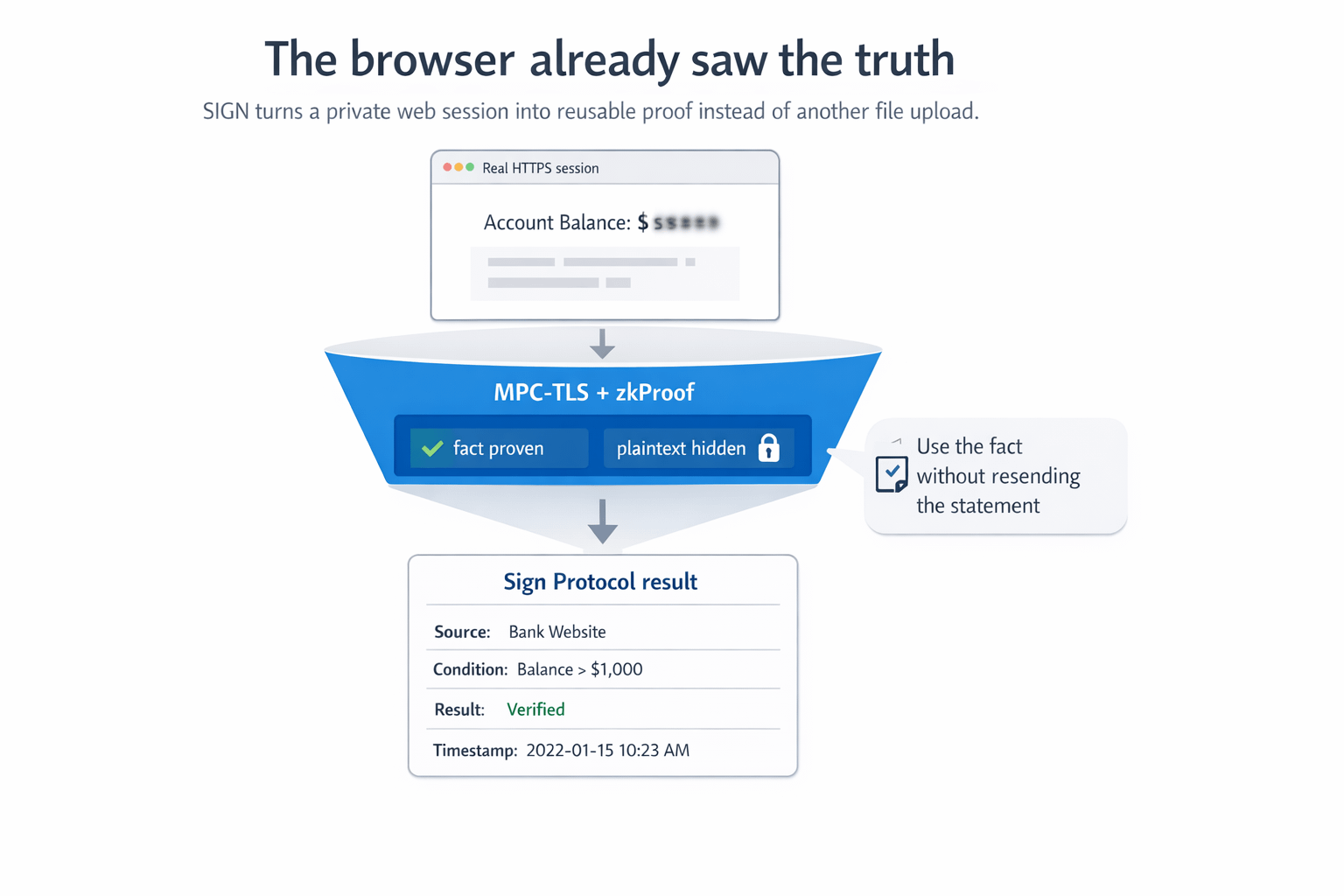
The schema detail is what makes this feel operational instead of decorative. The sample format includes fields like ProofType, Source, Condition, SourceUserIdHash, Result, Timestamp, and UserIdHash. That means the approval side is not looking at a vague badge that says verified. It can see what source was checked, what condition was tested, whether it passed, and when it was produced. SIGN also says smart contracts can access, correctly decode, and use those validation results. That is a very different approval path from reopening the raw statement and hoping each reviewer reads it the same way.
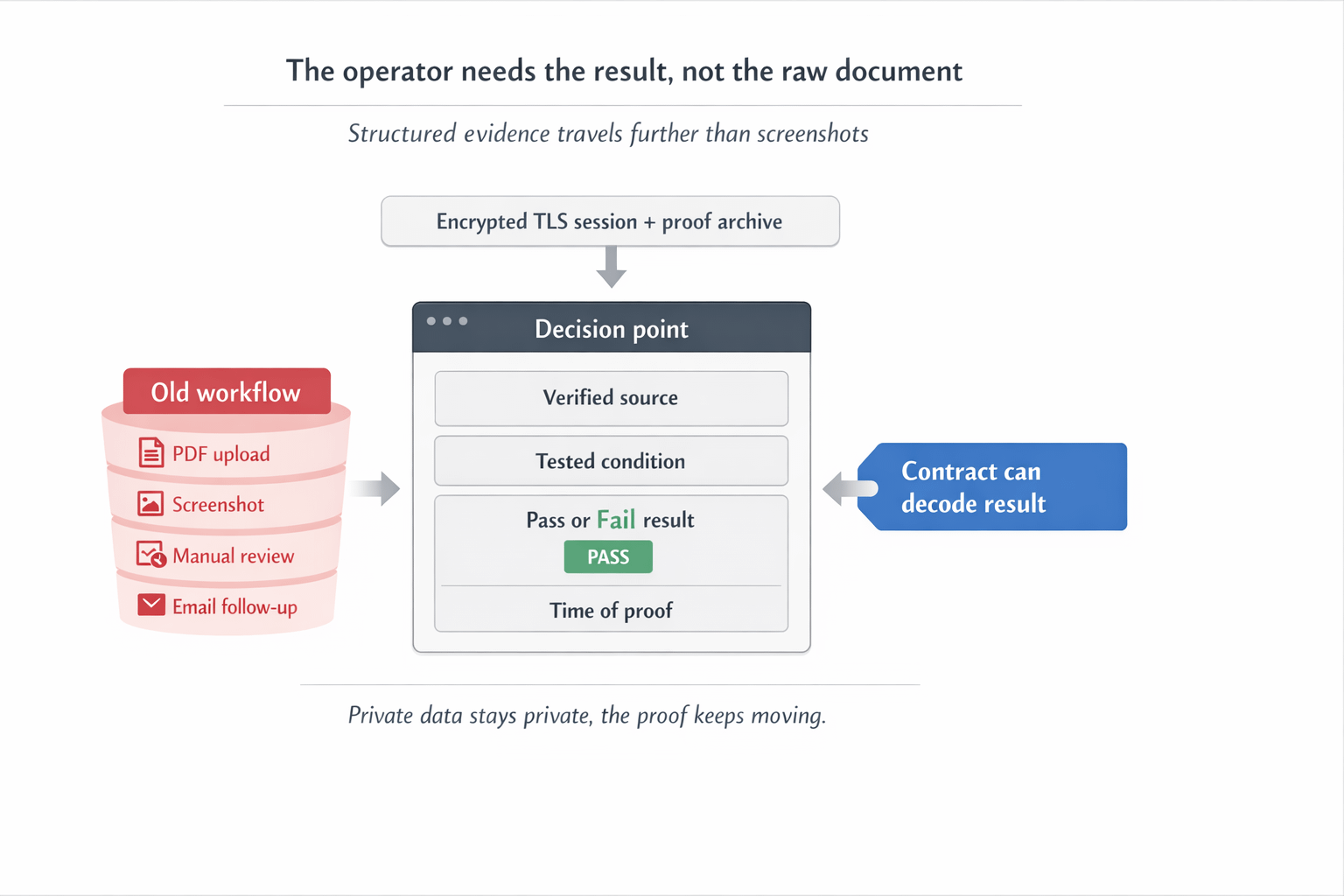
This is where the operator friction becomes real. Imagine the balance check already happened in the browser, but the final approval sits inside a different system. Without reusable evidence, the case pauses anyway. Support asks the user to upload the statement. The operator attaches the screenshot to the file. Someone adds a note explaining what was checked. If the case is reviewed later, the team has to defend why that image was enough. The user already proved the balance once, but the workflow acts like proof only existed inside the browser session that created it.
With the attestation in place, the approval step can use the result instead of asking for the page again. The operator no longer has to rebuild trust from a screenshot and a comment thread. The decision can move on the structured evidence itself. That is the difference that stayed with me. The workflow stops treating the raw document as the thing that travels forward. The proven fact becomes the thing that travels forward.
That is also why this feels more useful than a generic claim about offchain verification. The server does not need to change for the MPC setup. The proof comes from a normal HTTPS session. Then the result can be archived, queried, and consumed after the session instead of dying inside the original browser moment. SIGN names PADO and zkPass here, which makes the target clear: real offchain facts that usually break at the handoff between the page that showed them and the system that still needs them.
For me, that is the real test. Not whether the browser saw the truth. Not whether a proof was technically generated. The real test is whether approval still stops and asks the user for the original page again. If the answer is yes, then the workflow is still built around screenshots. If the answer is no, and the attested result can move forward on its own, then the proof finally did more than create one private verification moment. It fixed the handoff that usually breaks the decision.
#SignDigitalSovereignInfra $SIGN @SignOfficial
