I used to believe that if an idea was important enough, adoption would eventually follow.
In crypto, that assumption felt almost natural. If something improved transparency, reduced trust assumptions, or enabled better coordination, it should find its place. Identity systems, in particular, seemed inevitable. Every system, at some point, needs to answer the same questions: who acted, under what authority, and whether that action can be trusted.
But over time, that belief started to feel incomplete.
I noticed that identity solutions were often present, but rarely essential. They appeared as dashboards, credentials, badges, elements that looked meaningful but didn’t shape actual behavior. People interacted once, maybe twice, and then disengaged.
The idea felt necessary. The usage didn’t reflect it.
Looking closer, the issue wasn’t just adoption, it was structure.
Many systems that positioned themselves as trust minimized still relied on fragmented verification. Data wasn’t portable. Context wasn’t preserved. Approval processes existed, but their authority wasn’t always clear outside a single platform.
And more importantly, users weren’t required to return.
There was a kind of quiet friction. Not in the interface, but in the logic. Systems asked users to care about identity without embedding it into workflows that demanded it. It felt like infrastructure designed to be seen, rather than infrastructure designed to be depended on.
That’s where my perspective began to shift.
I stopped evaluating systems based on how compelling their ideas were and started focusing on how they behaved under repeated use.
The question changed.
Instead of asking, “Is this valuable?” I began asking, “Does this operate without requiring attention?”
The systems that endure tend to disappear into the background. They don’t ask to be understood. They just need to work, consistently, quietly, and across contexts.
Payments do this well. Most people don’t think about settlement layers or clearing systems. They trust the outcome because the process is embedded.
Identity, I realized, hasn’t reached that stage.
That’s when I started thinking less about identity as a feature, and more about identity as an evidence layer.
Not a profile. Not a static credential. But a structured record of actions that can be verified, referenced, and reused across systems.
This is the lens through which I began looking at @SignOfficial and the $SIGN Token ecosystem.
At first, it didn’t seem radically different. Concepts like schemas and attestations exist across various frameworks. But what stood out wasn’t novelty, it was consistency.
A system designed to answer, in a standardized way:
Who approved what.
Under which authority.
When it occurred.
Which rules applied.
What evidence supports it.
And what confirms execution.
This isn’t just identity. It’s structured accountability that can travel.
The deeper question that emerged for me was:
Can identity become part of execution, rather than something attached to it?
Because if identity remains optional, it remains unused. But if it becomes embedded in how systems make decisions, who gets access, who qualifies, what settles, it stops being interacted with directly and starts becoming unavoidable.
That shift changes everything.
At a system level, the design is more practical than it first appears.
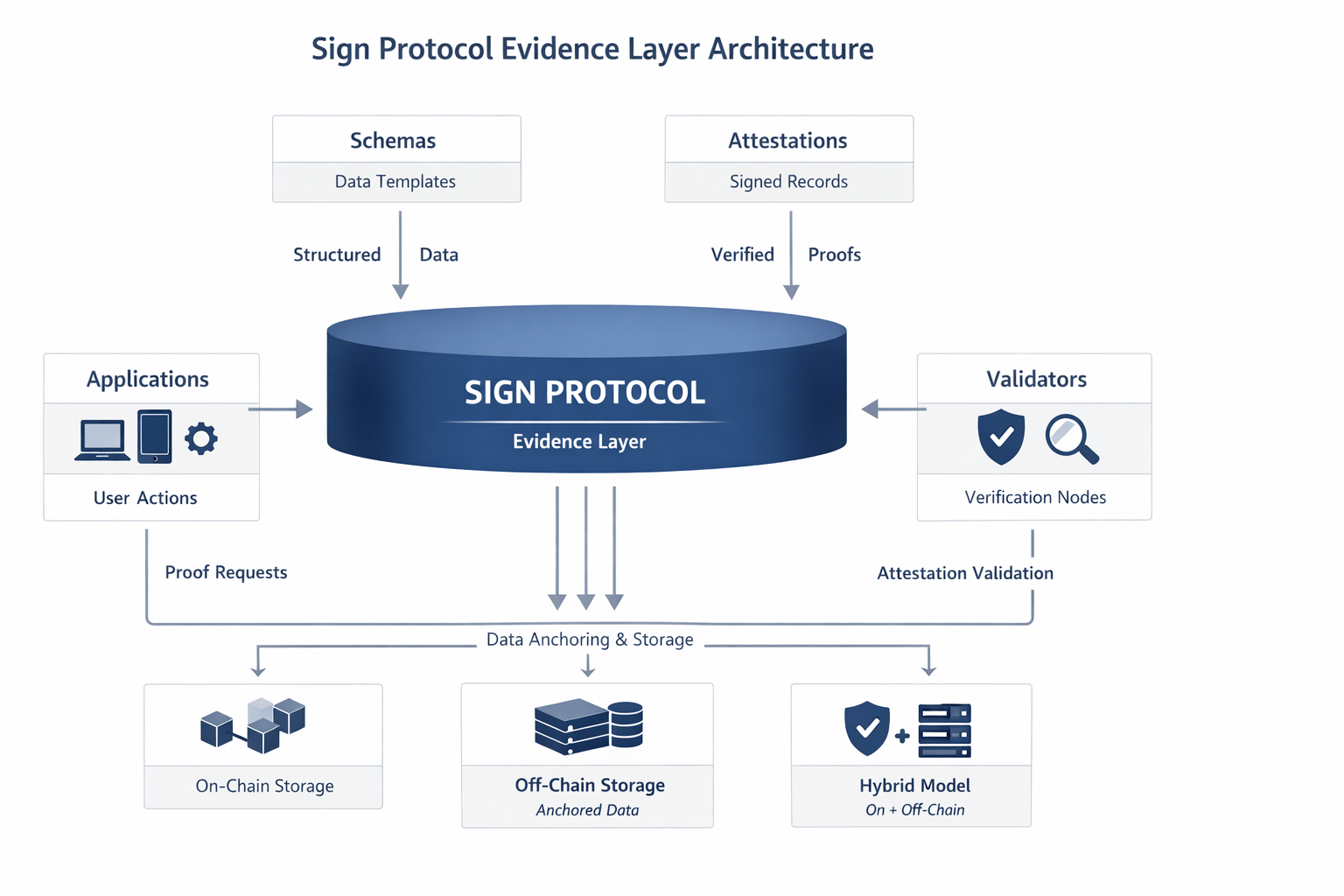
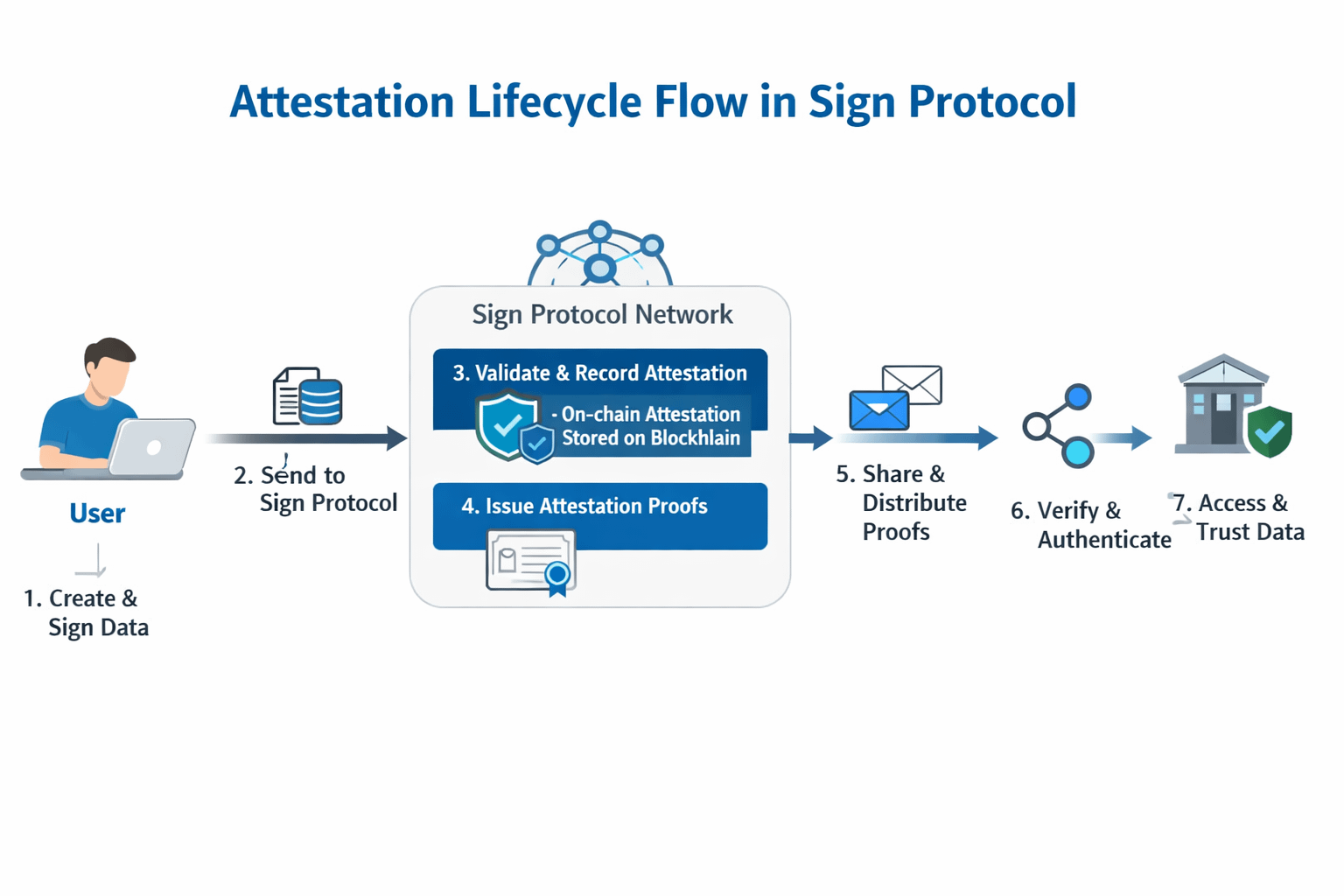
Schemas define how structured data is represented. Attestations are signed records that conform to those schemas. Together, they create a consistent way to encode actions along with their context.
But what makes this usable is not just how data is created, it’s how it’s stored and accessed.
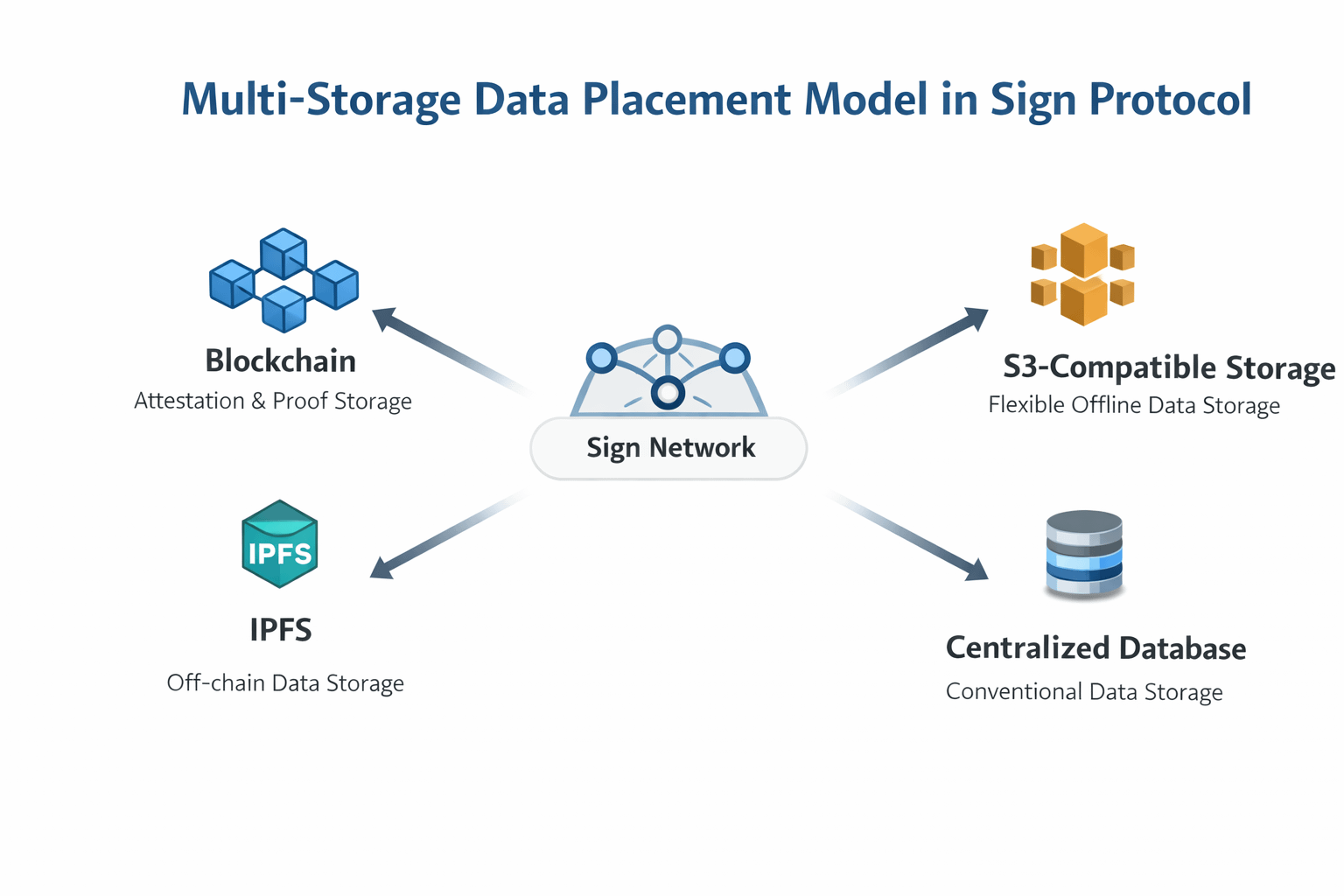
Sign Protocol supports multiple data placement models. Some attestations are fully on chain, ensuring transparency and immutability. Others exist off-chain with verifiable anchors, which allows systems to handle larger or more sensitive data without sacrificing trust. Hybrid approaches combine both, balancing cost, scalability, and accessibility.
Privacy isn’t treated as an afterthought either. With private and zero knowledge attestations, verification doesn’t necessarily require exposure. That introduces a more realistic model for compliance, one where systems can prove something is valid without revealing everything behind it.
What makes this structure actually usable, though, is the query layer.
Through SignScan, attestations are not just stored, they are accessible. Developers can retrieve structured data through APIs, query across chains and storage layers, and integrate verification directly into application logic.
This is where the system shifts from passive recording to active utility.
Because once attestations become queryable, they can influence decisions in real time.
Access control, eligibility checks, compliance validation—these are no longer external processes. They can be embedded directly into how applications function.
At that point, identity is no longer something users manage. It becomes something systems reference.
This also clarifies the role of the #SignDigitalSovereignInfra Token.
At first, it’s easy to view tokens as detached from real usage. But in this context, the token operates more as a coordination layer.
It aligns incentives across participants, those creating attestations, verifying them, and building systems that rely on them. It helps maintain integrity, encourages participation, and supports the network effects required for an evidence layer to function at scale.
Not as speculation but as alignment.
Looking beyond crypto, the relevance becomes clearer.
We’re entering a phase where trust online is increasingly fragmented. Systems either expose too much or verify too little. Users are asked to choose between privacy and credibility, often without a middle ground.
At the same time, digital infrastructure is expanding rapidly in regions where formal trust systems are still evolving. In these environments, verifiable records—portable and structured, can become foundational.
Not as an innovation, but as a necessity.
What matters isn’t that it’s blockchain-based. What matters is that it works consistently across contexts where trust is otherwise difficult to establish.
But even if something makes sense structurally, adoption isn’t guaranteed.
Markets often confuse attention with usage.
Tokens can attract volume. Narratives can attract visibility. But real systems depend on repetition. They depend on users returning, not because they want to, but because the system requires it.
And most identity systems haven’t reached that point yet.
This is where the challenge becomes more concrete.
For Sign Protocol to move from concept to infrastructure, it has to cross a usage threshold.
Applications need to require attestations as part of their core logic. Developers need to integrate verification into decision-making, not just display it. Users need to encounter identity as a condition, not an option.
Without that, interaction remains occasional.
And systems built on occasional interaction rarely sustain themselves.
There’s also a deeper layer that’s easy to overlook.
Technology can structure trust, but it doesn’t generate it on its own.
People respond to systems based on how they feel to use. If something feels intrusive, it gets avoided. If it feels unnecessary, it gets ignored. If it feels natural, if it fits into existing behavior, it gets adopted without resistance.
That’s the balance identity systems have to find.
Too visible, and they create friction. Too invisible, and they lose meaning.
The systems that succeed will likely be the ones users don’t think about but rely on anyway.
So what would actually build conviction for me?
Not announcements or theoretical integrations.
I’d look for applications where attestations are required for participation. Systems where removing the identity layer would break functionality. Patterns of repeated use, across users, across time, across contexts.
I’d watch for sustained activity around verification, not just creation.
Because that’s when something starts to resemble infrastructure.
At first, identity in crypto felt like a missing feature waiting to be perfected.
Now it feels more like a coordination layer that only works when everything else depends on it.
Sign Protocol doesn’t just attempt to solve identity,it reframes it as something systems can rely on without exposing users unnecessarily.
I’m still cautious about how quickly that transition can happen.
But the structure feels closer to reality than most approaches I’ve seen.
Because in the end, the difference between an idea that sounds necessary and infrastructure that becomes necessary is repetition.