while scanning the chain last night
While I was knee-deep in the CreatorPad task last night, pulling up Sign Protocol’s attestation architecture and tracing $SIGN token flows, something quiet but stubborn caught me off guard.
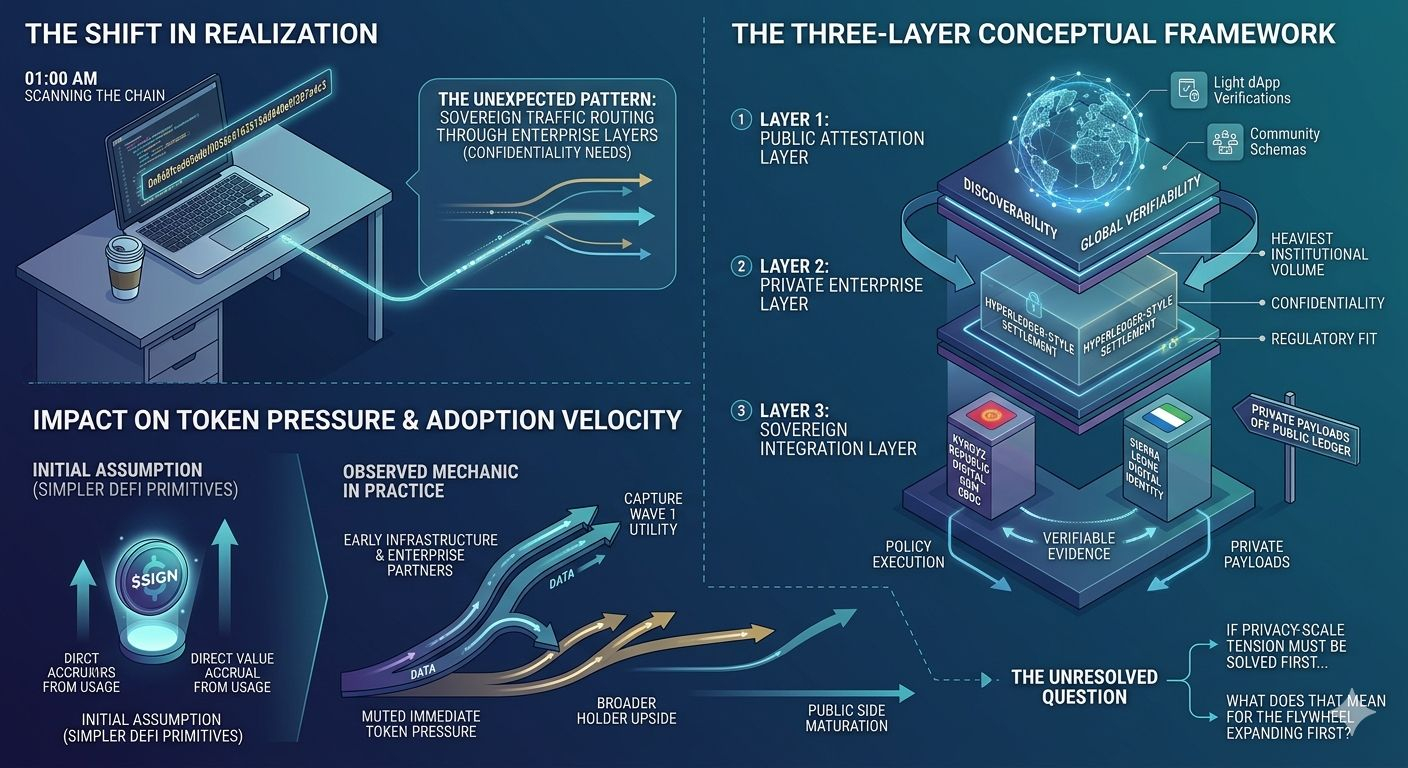
The whole promise of verification systems has always sounded clean on paper — attest once, verify everywhere, let the chain handle the rest. Yet here was the actual mechanics unfolding in my simulation: heavy sovereign-scale traffic quietly routing through private enterprise layers instead of lighting up the public omni-chain the way the narrative suggests.
It wasn’t flashy. Just a design choice that reshaped everything downstream.
I caught myself thinking back to a late-afternoon call I had months ago with a compliance lead at a regional government pilot; they kept circling back to confidentiality needs that no pure on-chain setup could touch without leaking sensitive policy data. That memory landed differently now.
The first actionable insight hit early: Sign Protocol (@Sign #SignProtocol) doesn’t fight the privacy friction head-on like some attestation layers do. It builds a deliberate hybrid path that lets nations anchor integrity publicly while keeping the sensitive payloads off the main public ledger. The second insight followed right after — this approach buys real adoption speed but quietly throttles the immediate on-chain token pressure most holders are quietly banking on.
the contrast that stuck with me
The contrast that stuck with me wasn’t some grand betrayal of the roadmap. It was subtler, almost mundane.
You see the public marketing around omni-chain attestations and how $SIGN will capture fees as usage explodes across chains. Then you run the numbers in a growth scenario and watch the heaviest institutional volume slip into those private Hyperledger-style settlements for compliance reasons. The public chain stays active, sure — community schemas, lighter dApp verifications, the occasional cross-chain proof — but the real volume that could move the needle stays contained.
I spent a solid hour mapping it out, actually. Three interconnected layers emerged as the conceptual framework that explained the behavior: the public attestation layer for discoverability and global verifiability, the private enterprise layer for confidentiality and regulatory fit, and the sovereign integration layer that ties policy execution to verifiable evidence without exposing the underlying data.
The on-chain behavior I kept returning to was straightforward. Even with the architecture in front of me, the token transfers and staking signals haven’t yet reflected the kind of surge you’d expect if every government attestation flooded the public side. It’s not broken — it’s intentional.
Two timely market examples made the point land harder. First, the Coinbase listing roadmap update for $SIGN on 24 March 2026, which lit up retail interest and speculation around future utility. Second, the quiet institutional pilots — Kyrgyz Republic’s Digital Som CBDC integration and Sierra Leone’s national digital identity rollout — where Sign’s hybrid model is already handling real policy flows without forcing everything onto public chains.
Both show momentum, yet both reinforce the same pattern: adoption is arriving, just not through the pure public flywheel many assumed.
hmm... this mechanic in practice
Hmm… this mechanic in practice forces a kind of honest skepticism I didn’t expect to feel.
I went into the task assuming the token’s value accrual would follow usage directly, the way it does in simpler DeFi primitives. What I saw instead was a deliberate delay baked into the architecture itself — early infrastructure builders and enterprise partners positioned to capture the first waves of utility while broader holder upside waits for the public side to mature.
It made me reevaluate my own priors, actually. I had been treating attestation protocols as straightforward utility plays. Sign Protocol operates more like a quiet infrastructure standard that prioritizes sovereign-scale viability over immediate token velocity.
That shift left me sitting with the laptop open longer than planned, scrolling through schema examples and wondering how many other projects are making similar quiet trade-offs right now. The personal story that kept resurfacing was simpler than I thought it would be — just me, coffee gone cold, realizing that the very thing making verification systems workable at nation-state level is the same thing muting the explosive token narrative I’d half-expected.
There’s a certain calm that comes with that realization, though. No hype cycle to chase, no forced narrative to defend. Just the architecture doing what it was built for in the real world.
still pondering the ripple
Still pondering the ripple, I keep coming back to the longer arcs.
Forward-looking, the hybrid design could let Sign Protocol embed itself into global digital public finance without the usual chain bloat or privacy scandals that sink other attempts. It might quietly become the evidence layer that governments actually trust enough to use at scale.
Another reflection: the early community and dApp users are essentially stress-testing the public side while the bigger sovereign integrations mature behind the scenes. That separation feels sustainable, even if it frustrates short-term expectations.
And then there’s the human side I keep circling — how many builders out there are quietly making these same layered choices, trading immediate token upside for durable real-world fit.
The whole dive left the question hanging, unresolved.
If verification systems only become truly valuable once they solve the privacy-scale tension in practice, what does that mean for the holders who signed up expecting the flywheel to spin first?
@SignOfficial
#SignDigitalSovereignInfra