The market felt weirdly quiet again this afternoon, that slow-burn kind of flat where even the degens in the chat have gone silent and you start refreshing the same three tabs out of habit. I was supposed to be catching up on some yield positions, but instead I found myself back in that half-finished CreatorPad task on Sign Protocol, poking at the verification flow like it was a loose thread I couldn’t stop pulling.
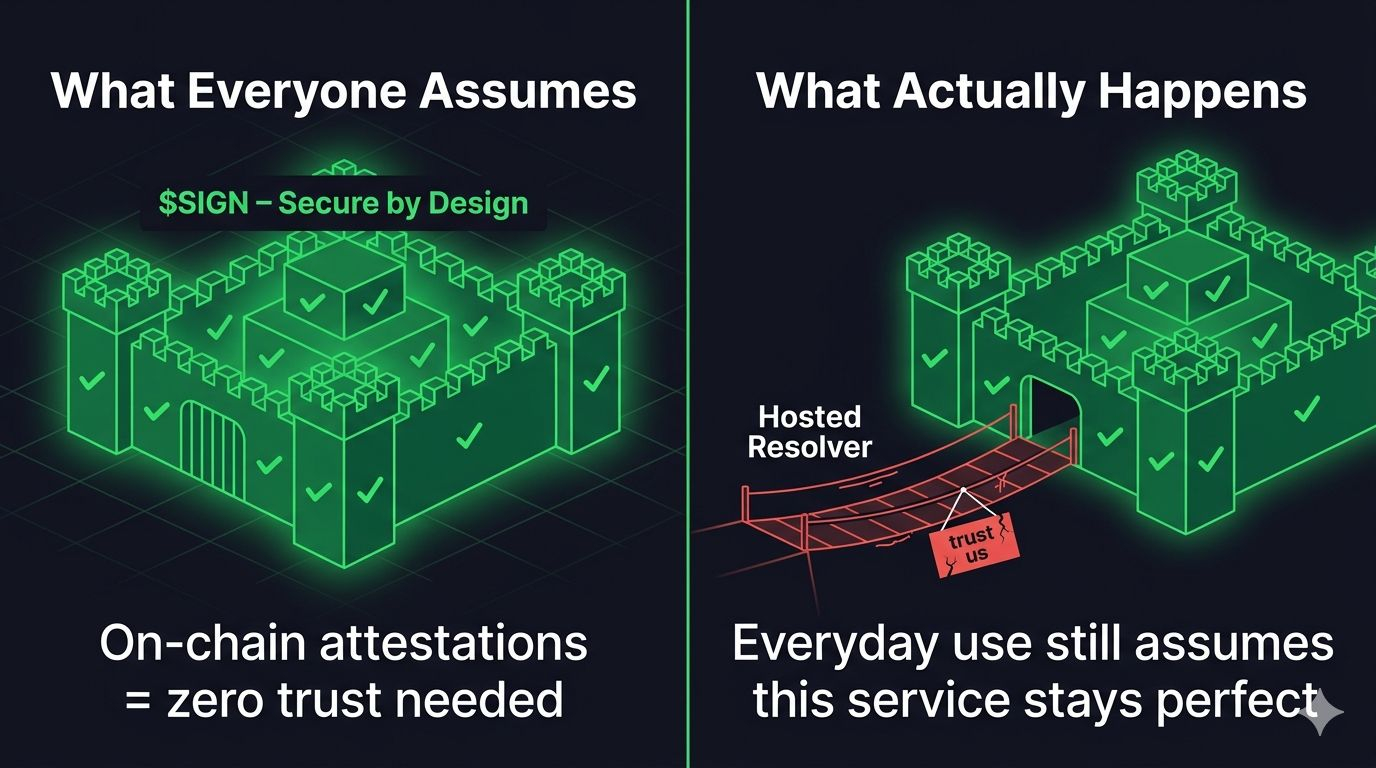
That’s when the click happened. We keep hearing how $SIGN is this beautifully engineered, sovereign security layer—on-chain attestations that nobody can mess with, zero trust needed once it’s written. I bought into that story too at first. But after running a couple of edge-case tests on the credential pipeline, something uncomfortable settled in: the whole thing only feels secure because we’re all quietly assuming the off-chain resolver will always do exactly what it’s supposed to. The on-chain part is rock-solid, sure. The moment the query leaves the chain and hits the recommended SDK path, though, the security model flips from “proven by design” to “hoping the service stays honest and online.”
I even caught myself re-running the same test three times, thinking maybe I’d configured it wrong. But no—the raw contract call returned the attestation instantly with cryptographic proof intact. The default integration, the one every tutorial points to, just assumed the hosted resolver would return the right result without any extra guardrails. It worked fine under clean conditions, but the second I simulated a brief delay or partial outage, the whole verification step hung in this awkward limbo where you’re left wondering if the data is still trustworthy or if you’re now trusting an assumption instead of code.
Here’s the part that still bothers me. If the big promise is true digital sovereignty and trust minimized to the blockchain itself, why does the everyday security experience still rest on the assumption that one service layer won’t become the single point of failure? I’m not fully convinced the design holds when real pressure shows up—say, during a coordinated attack window or when traffic spikes and the resolver starts throttling. It feels like we’re celebrating the fortress walls while quietly ignoring that the front gate still has a “trust us” sign on it.
That gap matters most to the teams actually shipping dApps right now, the ones who can’t afford to tell users “just assume the resolver is fine today.” The average holder probably won’t notice until some project they’re in suddenly can’t prove its credentials cleanly and the community starts asking hard questions. But when it does surface, it might quietly separate the projects that built for real security from the ones that built for the narrative.
I thought walking away from the task I’d feel more confident about $SIGN . Instead it left me staring at the same flat charts, wondering if we’re all still grading these protocols on assumptions rather than the friction we actually hit in practice. Anyway, the market’s still doing that same nothing-burger dance it was doing three hours ago. I’ll probably just keep watching how this one plays out.
@SignOfficial #SignDigitalSovereignInfra