I’ll be honest, I didn’t think much about proxy contracts at first. They sounded like one of those dry, behind-the-scenes technical things that only developers care about. But then I stumbled into how they actually work, especially in systems built around something like a sign protocol, and it completely changed how I look at certain blockchain projects.
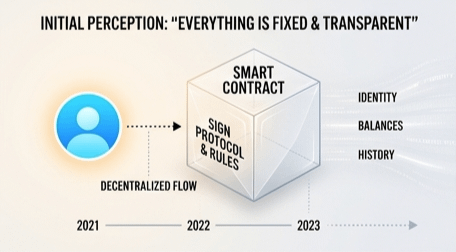
It started with curiosity. I was exploring a project that felt smooth, reliable, almost invisible in how it handled identity and permissions. Everything just worked. My account, my interactions, my history. It felt stable, like nothing could suddenly shift under me. But then I learned what was actually happening under the hood, and that’s when things got interesting.
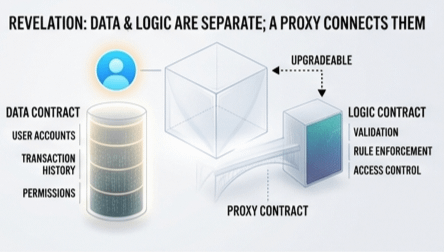
Instead of everything living inside one fixed smart contract, the system was split in two parts. One contract held all the important stuff, my data, balances, identity, and history. The other contract held the logic, the actual rules that define how the system behaves. And sitting in between was this thing called a proxy. I wasn’t interacting with the logic directly, I was interacting with the proxy.
At first, that didn’t sound like a big deal. But then I realized the key detail. The logic contract could be swapped out.
Same address. Same account. Same interface. But behind the scenes, the rules could change.
That’s the upgrade.
On paper, it makes perfect sense. Bugs happen. Systems evolve. No one wants to migrate millions of users every time something breaks or improves. From a developer and product perspective, it’s actually kind of brilliant. It keeps everything seamless. No disruption, no messy transitions. Just a quiet update in the background.
But the more I sat with it, the more I started thinking about control.
Because if someone holds the key to upgrade that logic contract, they don’t just maintain the system. They define it. Not later, not theoretically, but right now, at any moment.
And that’s where things start to feel different.
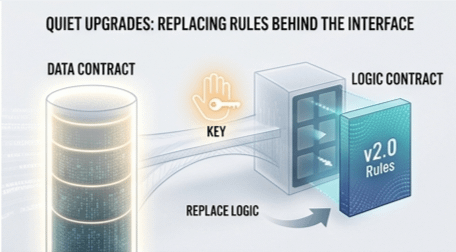
They don’t need to shut anything down. They don’t need to freeze accounts in some dramatic, visible way. All they have to do is push a new implementation behind the proxy. That’s it. From the outside, everything looks exactly the same. Same contract address, same interface, same user experience.
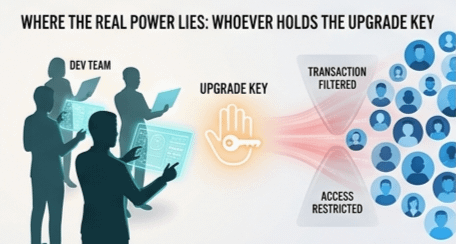
But suddenly, transactions could be filtered. Permissions could shift. Access could be restricted. Rules could tighten quietly, without warning. And I might still be interacting with it, thinking nothing has changed.
That’s the part that really stuck with me. It’s not loud control. It’s invisible control.
When I looked deeper into how the sign protocol layer fits into this, it added another layer of meaning. Now it’s not just about logic and upgrades. It’s about identity, approvals, and validation. Who is allowed to do what. Who gets access. Who is recognized by the system.
So upgrades aren’t just technical anymore. They can shape behavior, participation, even inclusion.
That’s when I started seeing the bigger picture. A system can feel decentralized on the surface. It can look open, transparent, even trustless. But if there’s an upgrade mechanism controlled by a small group, whether that’s a dev team, a company, or something bigger, then there’s a control lever built into the design.
And I’m not saying upgrades are bad. Honestly, without them, most systems would break, stagnate, or become useless over time. Flexibility matters. Innovation needs room to move.
But let’s not pretend it’s neutral.
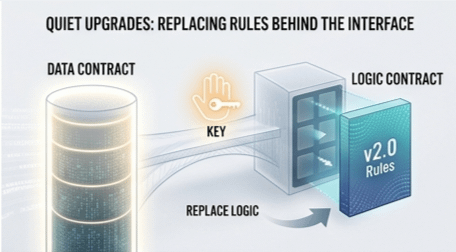
Whoever holds the upgrade key holds the real power. That’s just the reality.
If it’s a small dev team, that’s one kind of risk. If it’s a company, that’s another. If it’s something like a government or a centralized authority, then it becomes a completely different conversation. Because now we’re not just talking about fixing bugs or improving performance. We’re talking about policy being enforced through code.
And the strange part is, it doesn’t feel like control. It feels like maintenance.
That’s what makes it so easy to overlook.
I’ve started looking at projects differently because of this. Before trusting anything, I don’t just look at what the code does today. I look at who can change it tomorrow. Who controls the upgrade path. Who holds the keys behind the proxy.
Because that, more than anything, tells me where the real ownership lies.
The market, interestingly, doesn’t always price this in clearly. A lot of investors focus on hype, utility, partnerships, or tokenomics. And those things matter, of course. But control structures like this often sit quietly in the background, unnoticed until something goes wrong or changes unexpectedly.
And when that happens, it’s usually too late to ask questions.
So now I find myself thinking differently. I still appreciate the elegance of upgradeable systems. I see why they exist. I even respect the design. But I don’t blindly trust them anymore. Convenience always comes with a trade-off, and in this case, it’s permanence for flexibility.
And flexibility, in the end, always belongs to whoever is in charge.
So here’s the question I keep coming back to when I explore projects like this now: am I interacting with a system that’s truly decentralized, or am I just using something that feels decentralized until someone decides to change the rules?

