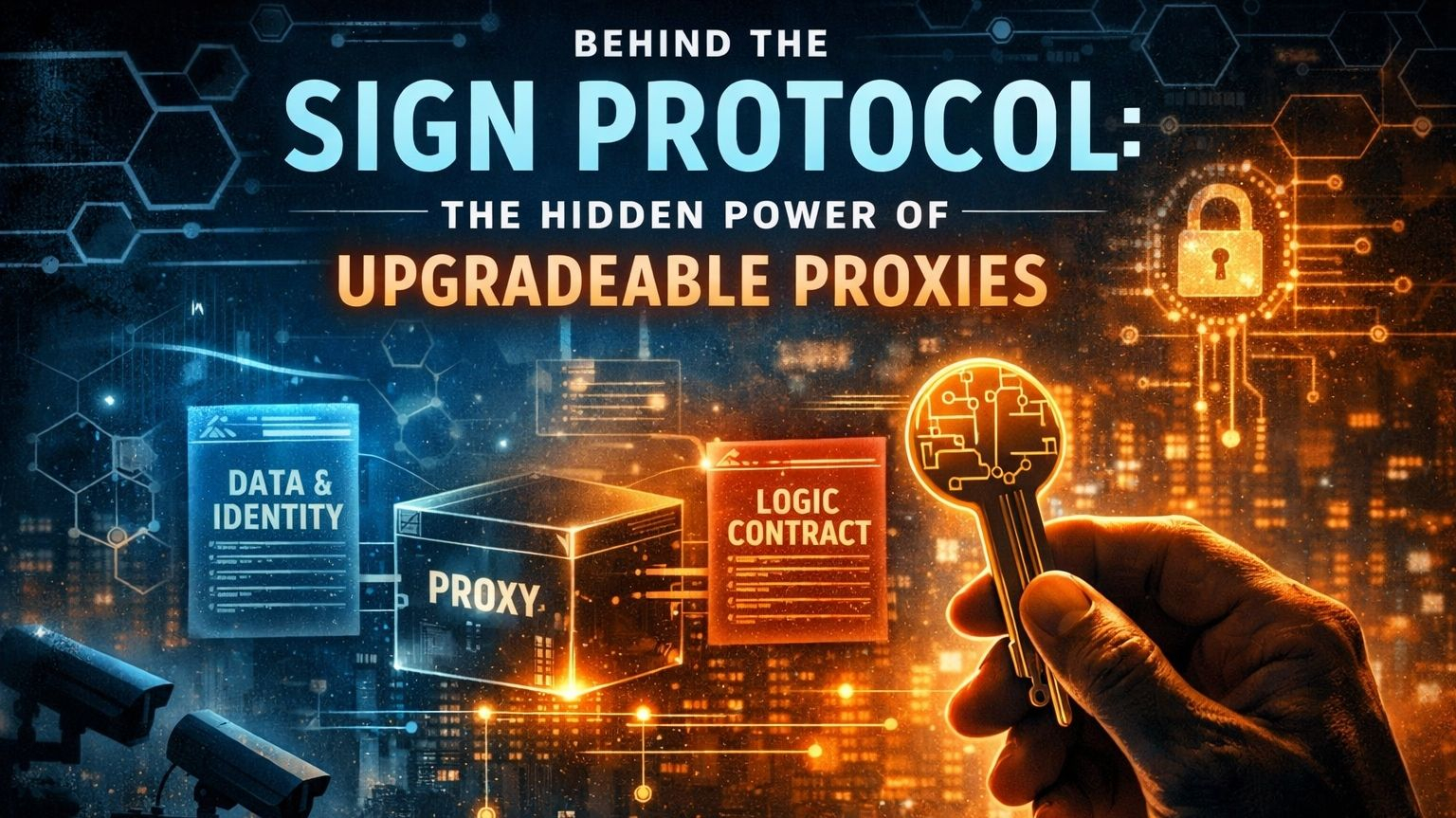
Most people ignore proxy contracts because they sound technical, but they quietly define who holds control. In systems like @SignOfficial , upgradeable proxies separate data from logic. You interact with one address, while the underlying rules can change without you noticing.
The structure is simple. One contract stores identity and history. Another defines the rules. The proxy connects them. But the critical detail is this: the logic contract can be replaced. Same account, same interface, different behavior.
Upgrades solve real problems. Bugs happen. Systems evolve. Migrating millions of users is not practical. But this convenience introduces a deeper question — who controls the upgrade key?
Because whoever holds that key doesn’t just maintain the system, they control it. They can modify permissions, filter transactions, or redefine access without visible disruption. Nothing breaks on the surface. Everything still looks normal.
When identity layers like Sign Protocol are involved, the impact goes further. Upgrades don’t just change code, they can influence who is allowed to participate and how trust is assigned.
This is where the tension sits. The system can appear decentralized, but still contain a central control point. Not obvious, not loud, but always present.
Upgradeable design is not inherently bad. Without it, many protocols would fail over time. But it is not neutral either. It shifts power from fixed code to whoever manages change.
Small teams, companies, governments — each brings a different level of risk. Because upgrades are not just technical actions, they can become policy decisions executed through code.
And that’s the part most people miss. It doesn’t look like control. It looks like maintenance.
So before trusting any protocol, one question matters more than anything else: who controls the upgrade key? #SignDigitalSovereignInfra $SIGN