There’s a quiet failure mode in digital systems that rarely appears in feature lists.
It’s not downtime.
It’s not low throughput.
It shows up in the handoff.
A person proves eligibility in one place, then has to prove it again somewhere else.
A project distributes tokens correctly, yet people still question why they received them.
A credential is valid, but only inside the system that issued it.
We don’t lack records. We lack portable meaning.
This is the coordination problem most systems encounter once they grow beyond their original environment. Records exist, signatures exist, transactions happen — but the moment proof has to travel, uncertainty appears.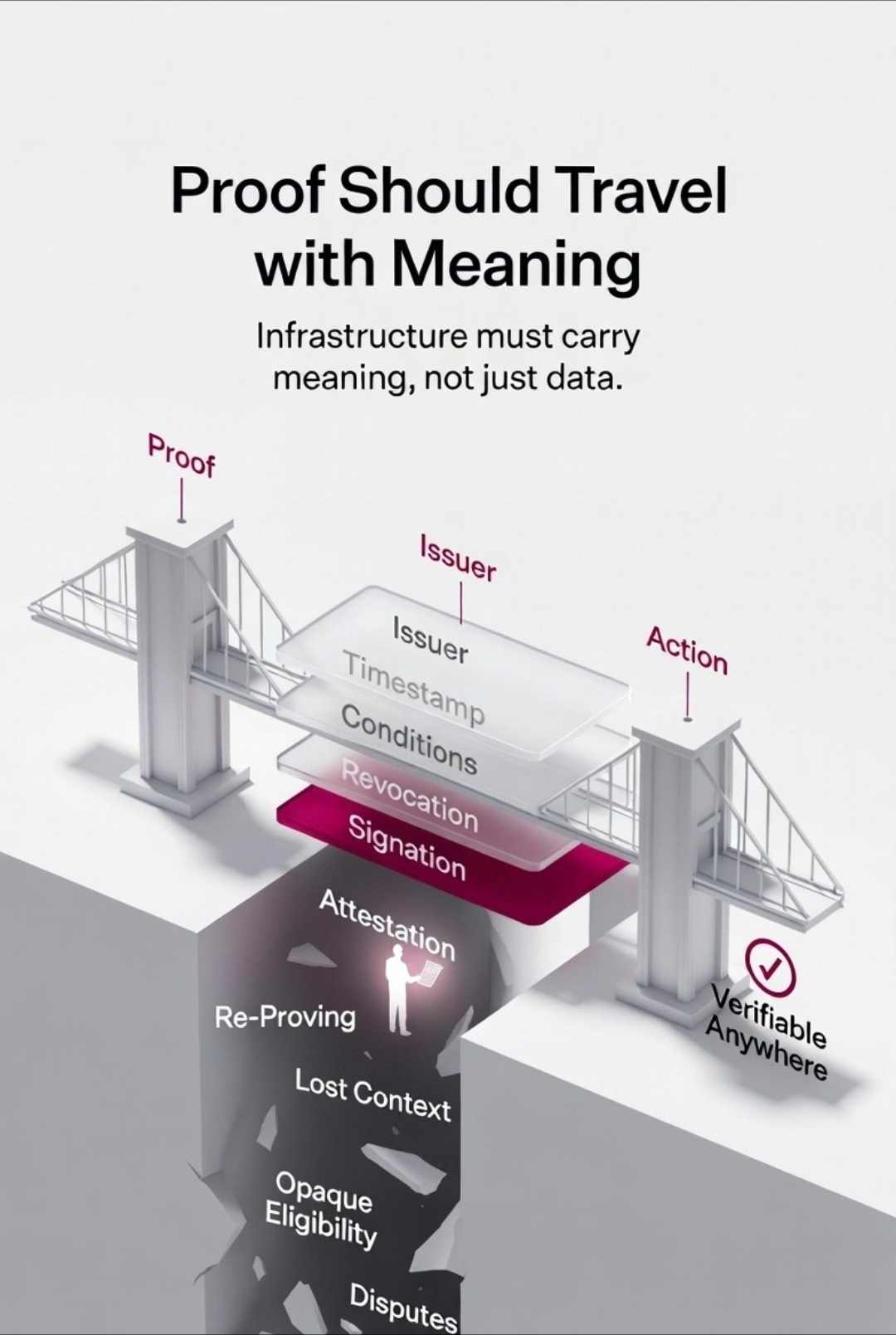
Who issued this?
Why should that issuer matter here?
Has anything changed since this was created?
Can I verify this myself without asking someone?
That’s where infrastructure reveals what it was optimized for: presentation or consequence.
What makes Sign Protocol interesting is that it focuses on a specific bottleneck underneath credentials, distributions, delegation, and even stablecoins:
Make signed attestations the common language across environments.
A credential becomes a signed statement with context.
A token distribution becomes a signed statement of eligibility acted upon.
A delegated action becomes a signed statement of authorization.
A balance update becomes a signed statement of state.
Viewed this way, even on-chain money looks different. Stablecoins, balances, transfers — they are collections of signed claims about who owns what and why that ownership is valid.
Trust doesn’t come from believing the system.
It comes from being able to verify the signatures yourself.
This begins to close the gap between proof and action.
Most credential systems don’t fail because credentials are fake. They fail because the interpretation of those credentials breaks once they leave their birthplace. Most token distributions don’t create doubt because transfers fail. They create doubt because the eligibility logic was invisible until after value moved.
Delegation becomes risky not because cryptography is weak, but because later no one can clearly answer who authorized what and under which conditions.
These are not separate problems. They are the same problem wearing different clothes:
Proof exists, but it doesn’t travel well.
This approach suggests a different direction. If every meaningful state change is expressed as a signed attestation carrying its own context — issuer, timestamp, conditions, revocation status — then the handoff problem changes.
You stop asking, “Does this system trust that system?”
You start asking, “Can I verify this signature myself?”
That shift moves trust from relationship to verification.
It also changes how we think about coordination between public and permissioned environments. In a public chain, attestations are open and verifiable by anyone. In a permissioned network like Hyperledger Fabric, access is controlled, but participants are still signing state changes. The logic of truth remains the same even if the audience changes.
A balance update is still a signed statement.
A transfer is still a signed statement.
Eligibility is still a signed statement.
You’re not running two systems. You’re running one system of truth expressed in two environments.
This perspective also clarifies something about performance claims. High throughput makes more sense when transactions are treated as signed attestations to validate and order, rather than heavy computation to execute each time. But speed is secondary to a harder question:
Do the signed states remain consistent wherever they appear?
Because the real challenge isn’t scale. It’s syncing truth across contexts.
This kind of infrastructure matters most in ordinary situations, not dramatic ones. It reduces the repeated negotiation built into digital life.
Less asking users to re-prove the same facts in different formats.
Less reliance on private spreadsheets to justify distributions.
Less confusion when disputes arise about what happened.
And disputes are the real test of any system.
When a distribution is challenged.
When a credential is questioned.
When a delegated action is disputed.
A system built around portable attestations can respond with evidence, not escalation. Show the signature. Show the issuer. Show the conditions. Let participants verify without needing an internal investigation.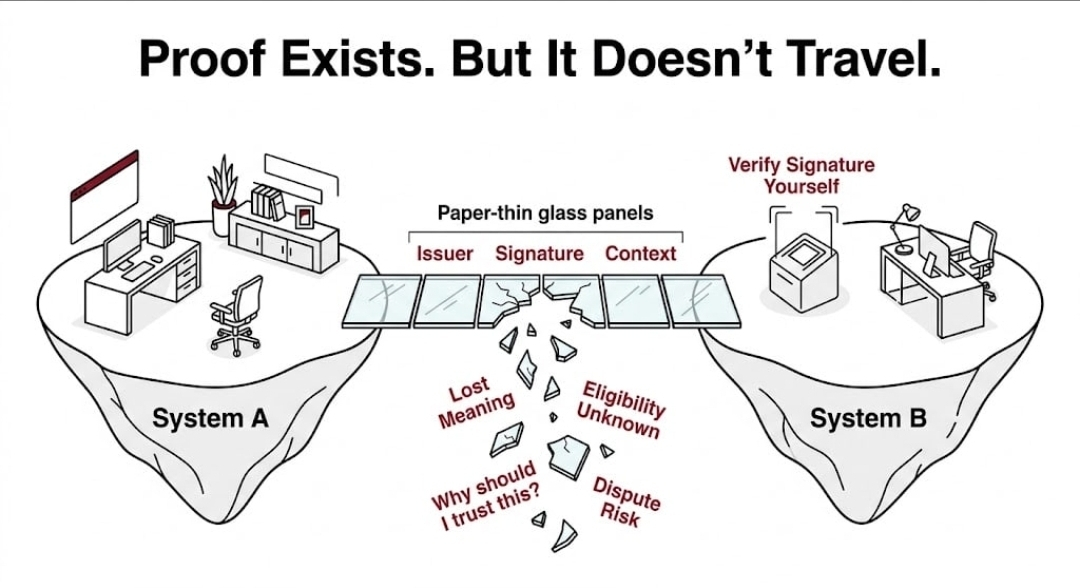
That is what infrastructure owes the people who rely on it.
Not just uptime.
Not just features.
But the ability to resolve uncertainty without friction.
There’s also a human layer here. People don’t just need systems to be secure. They need them to be understandable. A credential that is technically valid but impossible to interpret still creates doubt. A distribution that is accurate but opaque still feels suspicious.
So the goal becomes modest but difficult:
Make proof portable without making it abstract. Preserve meaning while reducing friction.
Most digital systems today fail not because they lack records, but because they fail in the spaces between records — in the translation, in the handoff, in the moment one system is asked to trust something it didn’t witness.
If proof can carry its meaning wherever it goes, coordination becomes less fragile. Credentials carry weight outside their birthplace. Distribution can follow verification without confusion attached. Delegation can be traced without guesswork.
This is not a loud ambition. It doesn’t announce itself as revolutionary.
But it quietly changes what becomes possible to build on top.
Because when proof travels well, systems stop negotiating the same facts over and over — and start acting on them with confidence.