When I first started exploring how national digital systems actually work behind the scenes, I expected complexity, but not this level of structured precision. My turning point came the day I tried to understand why governments, central banks, and regulators insist on a system that is private for the public yet fully auditable for lawful authorities. That was when I first encountered the reference architecture for SIGN, and honestly, it changed how I think about digital money, identity, and state-level infrastructure.
What struck me immediately was how intentionally balanced the system is. SIGN is built around controllable privacy, the idea that ordinary people stay private by default, but authorized institutions can audit actions with clear evidence. For someone like me who always wondered how large-scale systems maintain both privacy and compliance, this felt like the missing explanation.
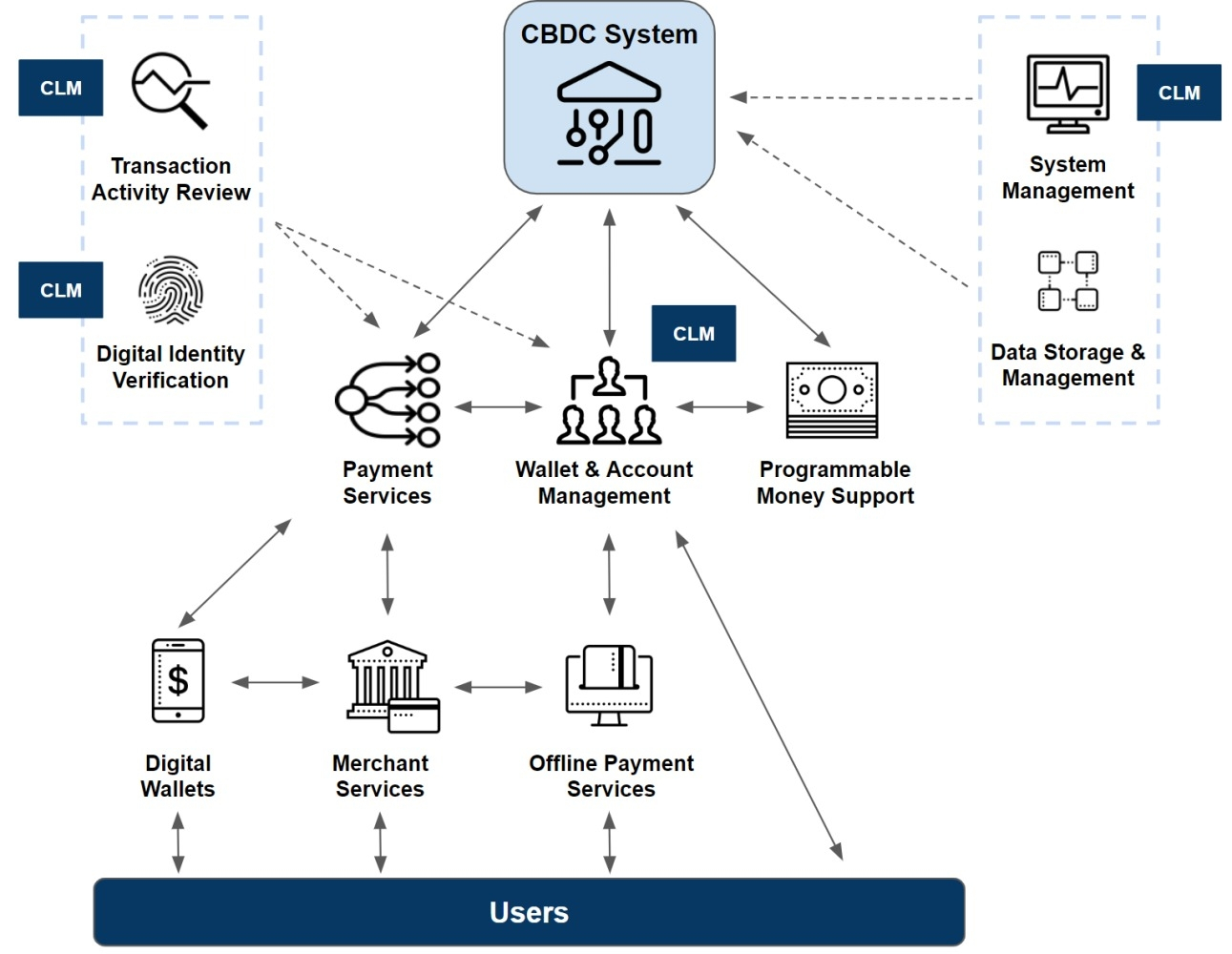
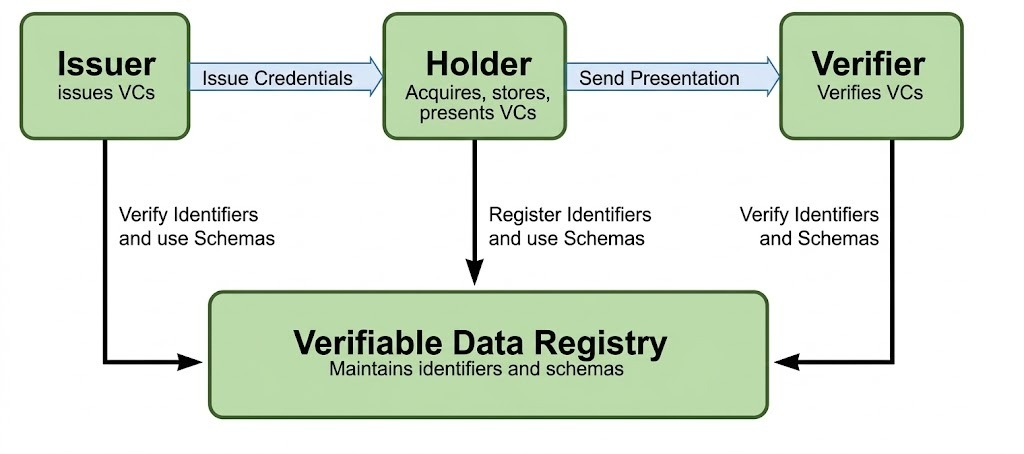
Then I moved deeper into the national performance layer. It’s designed for millions of users, multi-operator environments, strict SLAs, basically the scale at which countries actually operate. Suddenly it made sense why sovereign deployments cannot rely on vendor-locked, opaque systems. Everything must be standards-aware: ISO 20022 for payments, W3C VC/DID for identity. The more I learned, the more it felt like seeing the blueprint of how modern states could run securely and efficiently.
But the real clarity came when I understood how Sign Protocol and TokenTable fit into this architecture. Sign Protocol serves as the trust and evidence layer, the part that emits durable, inspection-ready proofs of who authorized what, under which rules, and when. TokenTable, on the other hand, becomes the engine that turns policy into action: eligibility checks, distributions, scheduling, asset tokenization. Together, they create a bridge between public and private rails, letting a country run transparent financial programs on an L2 while keeping sensitive citizen data on a confidential CBDC rail.
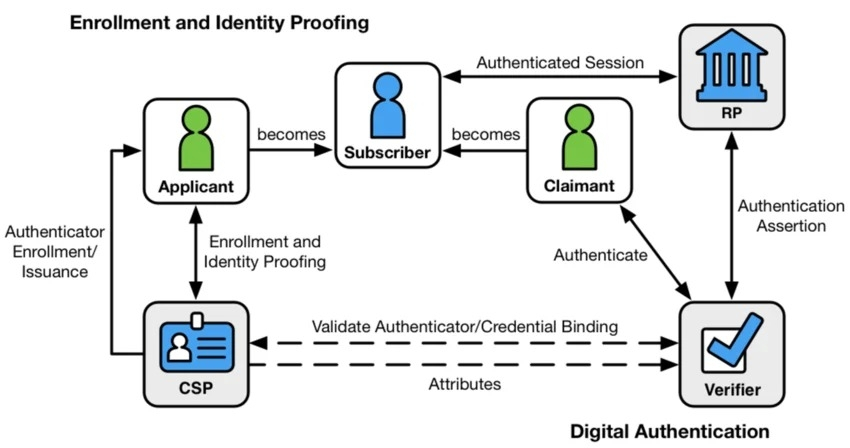
The trust model also fascinated me. Everything is separated: sovereign authority defines policy, issuers provide credentials, operators run infrastructure, auditors reconcile evidence. No single actor holds excessive power, and every step leaves a verifiable trail.
What truly impressed me, though, was the data-placement model. It finally answered the question I had for years: what goes on-chain, and what stays off-chain? Sensitive PII remains off-chain, cryptographic commitments go on-chain, and hybrid patterns anchor integrity without leaking private information.
By the time I finished studying the end-to-end flows,
eligibility → distribution → audit, cross-rail CBDC↔stablecoin conversion, and RWA registry updates,
I realized I wasn’t just looking at a technical architecture. I was looking at a blueprint for digital sovereignty. And experiencing that understanding firsthand was one of the most eye-opening moments in my journey through digital infrastructure.
@SignOfficial #SignDigitalSovereignInfra $SIGN
