while scanning the chain last night
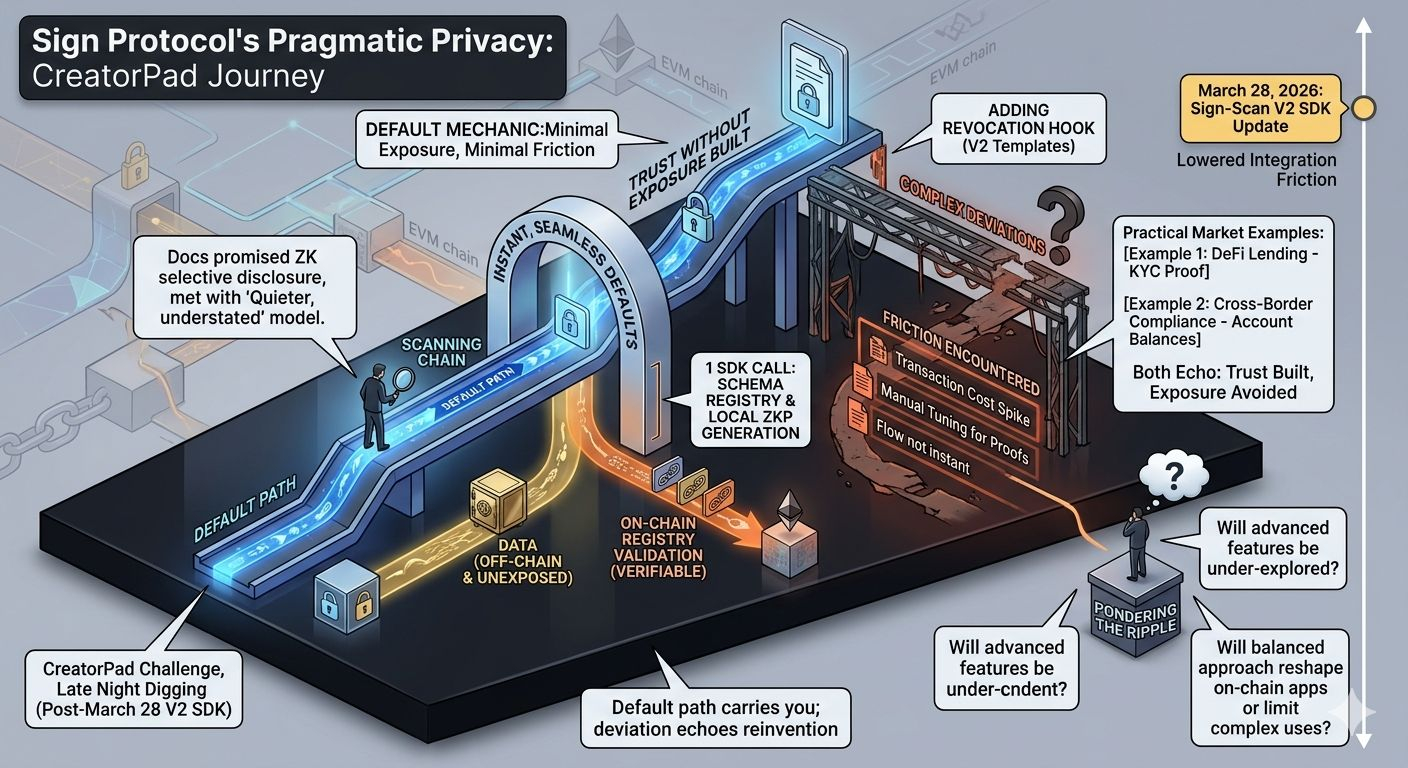
While digging into a credential issuance flow during the CreatorPad challenge late last night, Sign Protocol’s privacy model ($SIGN #SignDigitalSovereignInfra @SignOfficial ) caught me off guard in a way the docs never quite prepared me for. I had expected the usual zk layer that promises selective disclosure without ever leaking the full picture. Instead, what unfolded was quieter, almost understated. The system let me build an attestation that proved a claim’s validity while keeping the underlying data completely off-chain and unexposed, yet the verification still landed on public registries across EVM chains.
It reminded me of an old project I worked on two years back, where every credential attempt forced either full transparency or clunky off-chain workarounds. Here, the default path just… worked. One SDK call to the schema registry, a zero-knowledge proof generated locally, and the attestation ID appeared on scan.sign.global without a single sensitive field hitting the ledger. The March 28, 2026 Sign-Scan V2 SDK update made this possible. You can still see the fresh schema templates rolling out there, verifiable by anyone checking the explorer. That update’s present-day weight feels real because it directly lowered the integration friction I hit in the task. No more reinventing the privacy wheel.
The contrast hit harder than I admitted at first. On paper, the narrative sells omni-chain trust with perfect privacy. In practice, the privacy model behaves like a careful gatekeeper. It defaults to minimal exposure for everyday attestations, then layers in programmable hooks only when you explicitly ask. I watched the on-chain behavior during one test run. The attestation hash anchored to Ethereum mainnet carried no raw data, just the proof and a schema reference. Verification queries returned true or false without ever surfacing the subject’s details.
the contrast that stuck with me
This design choice feels deliberate, almost protective. Early users—solo builders like me in CreatorPad—get the quick win of trust without exposure right away. The deeper ecosystem effects, the ones promised for institutions or regulated flows, sit further out. It is not that the advanced features are missing. They are just gated behind schema extensions that demand you understand the interplay between public hooks and private payloads.
I found myself sketching a simple conceptual framework on a notepad around 2 a.m. Three interconnected layers: the public schema registry that everyone can query, the private data vault that stays off-ledger or in zero-knowledge form, and the verification loop that ties them together without ever merging them. The model does not hide the fact that something happened. It simply refuses to broadcast what that something was unless the attester chooses to reveal it. That feels like the real innovation, not the marketing copy about sovereign infrastructure.
Still, the on-chain reality introduced a small friction I had not anticipated. When I tried to add a conditional revocation hook tied to the new V2 templates, the transaction cost spiked and the selective disclosure proof needed manual tuning. Nothing broke, but the flow was no longer instant. It behaved exactly as if the protocol prioritizes default privacy first, then invites complexity only for those willing to pay the gas and the mental overhead.
Two timely market examples came to mind while I stared at the explorer logs. In one recent DeFi lending pool integration, protocols using similar attestation patterns avoided the usual KYC dumps by proving creditworthiness through zero-knowledge claims alone. In another, a cross-border payment pilot on Base leaned on Sign’s model to confirm compliance without exposing account balances. Both cases echoed what I saw in the task: trust built, exposure avoided.
hmm... this mechanic in practice
Actually—there was a moment of honest skepticism. I paused midway through the second test and wondered if this privacy model would hold once real regulatory pressure arrives. The zero-knowledge proofs are elegant, the selective disclosure seamless in the default lane, yet the underlying schema registry remains fully public. Anyone can see that an attestation exists. They just cannot see inside it unless invited. Is that enough when auditors or governments start asking harder questions? I caught myself reevaluating my own assumptions about what “without exposure” truly means in a world that still loves immutable logs.
The introspection ran deeper than the code. I have spent enough nights watching other protocols chase perfect privacy only to ship half-measures that later required painful upgrades. Sign Protocol feels different because it does not overpromise the impossible. It gives you privacy as a practical default, not a theoretical guarantee. That quiet pragmatism lingered with me more than any flashy demo.
There is something almost humble in how the mechanics play out. The system does not force you to trust its cryptography alone. It lets you verify the proof yourself, on-chain, with the schema ID from the March 28 update serving as the anchor point. No grand ceremony. Just a clean handoff between private intent and public evidence.
still pondering the ripple
This leaves me turning the same thought over in my head during quieter moments today. How many builders will stay comfortably in the default privacy lane because it is simply good enough? And what happens to the long-term ecosystem when the advanced hooks remain under-explored? The model seems engineered to reward careful, incremental use rather than rapid, all-in experimentation.
I keep coming back to the personal side of it too. In the CreatorPad task, that single successful private attestation felt like a small but genuine relief. No data leaks, no extra compliance theater, just verifiable trust delivered cleanly. It shifted how I think about building credential flows going forward.
The ripple feels ongoing, unfinished. The privacy model works beautifully in the lanes I tested, yet it still carries this subtle invitation to go further if you are willing to accept the added complexity. I am not sure yet whether that invitation will pull most developers deeper or keep them safely at the surface.
What lingers most is the open question of whether this balanced approach—trust without unnecessary exposure—will quietly reshape how entire categories of on-chain applications get built, or whether the friction in the advanced paths will keep the deeper use cases reserved for a smaller circle of teams.