I’ve sat through way too many digital identity presentations. You know the drill: gorgeous architecture slides, smooth credential flows, and a bunch of buzzwords about zero-knowledge proofs and seamless interoperability. On paper, it all looks perfect every single time.
But I always end up with the same nagging question: would I actually trust this with something important? Would real people and big institutions bet on it when it actually matters?
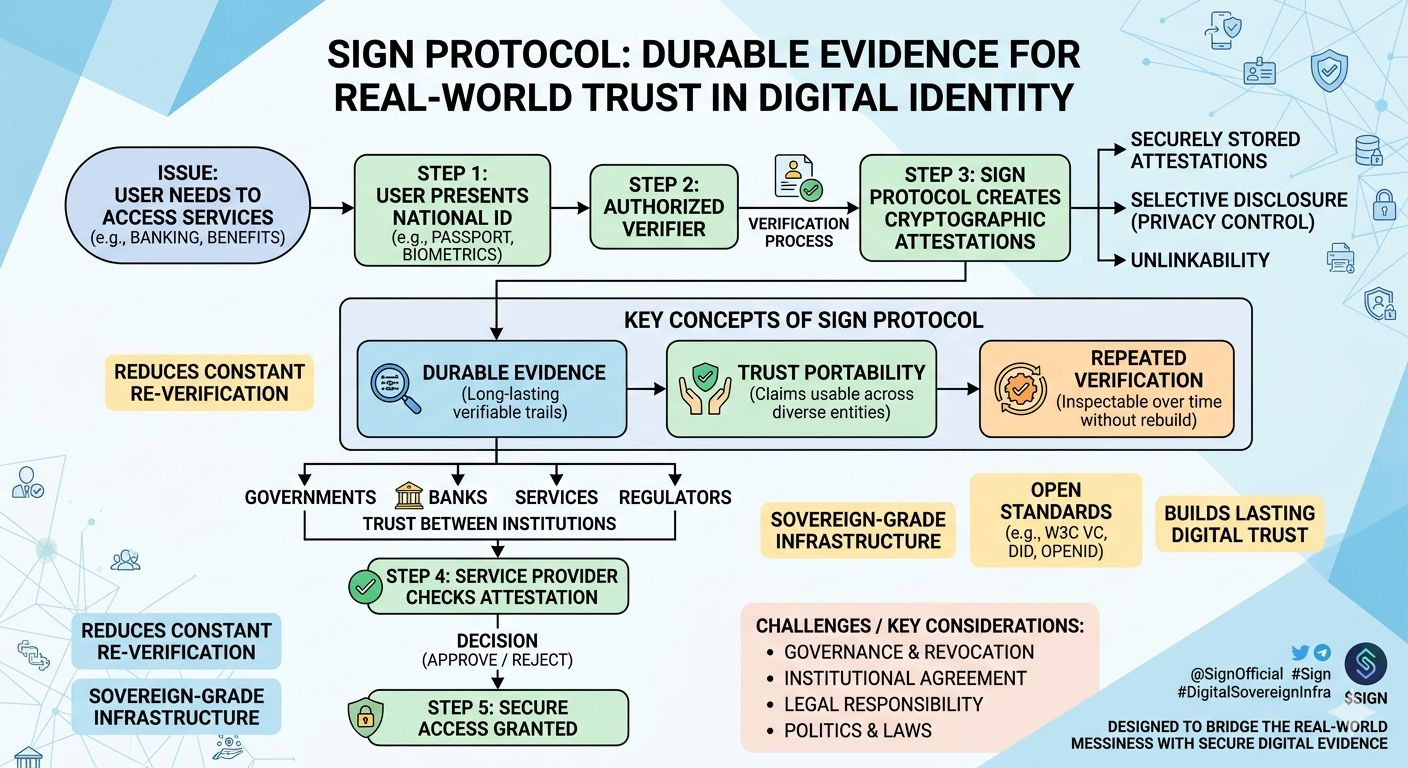
That’s the piece most projects quietly skip over. Sure, the tech can handle issuing credentials, selective disclosure, and revocation. The hard part is making trust feel solid as it moves between governments, banks, services, and across years without everything constantly falling apart or needing to be rebuilt from scratch.
Lately I keep thinking about Sign because it doesn’t seem to ignore that messy reality. Instead, it leans right into it.
Their docs don’t start with “look how fancy our stack is.” They keep coming back to something simpler and deeper: making trust something you can actually repeat, point to, and inspect later. Sign Protocol feels like a shared evidence layer for all those important claims approvals, verifications, eligibility decisions, authorizations. You define them once, sign them, link them, and then anyone who needs to can still check the trail years down the line: who said this, under what rules, and can we still prove it today?
That focus on durable evidence is what keeps pulling me back. Most identity talks get stuck arguing about on-chain versus off-chain, wallet UX, or which standard wins. Those things are important, don’t get me wrong. Sign covers a lot of that ground with W3C verifiable credentials, DIDs, OpenID flows, hybrid storage, and smart privacy tools like zero-knowledge selective disclosure. It even plays nicely with real-world stuff like passports and biometrics.
But honestly, the tech stack isn’t what makes it feel different. It’s the bigger idea of trust portability. Can one verified claim travel from a government benefits office to a bank to a regulator without everyone having to start the trust process all over again? Can that proof still hold up months or years later without digging into someone’s private database?
Sign calls itself sovereign-grade infrastructure for identity, money, and capital at a national level. Their New ID approach, for example, lets people present their existing passport or national ID to authorized verifiers, who then create cryptographic attestations. Those attestations become something portable you can actually use across different services, while still keeping privacy in check with minimal disclosure and unlinkability.
It feels pragmatic. Not overly idealistic about decentralization solving everything, and not stuck defending old closed systems either. It’s trying to bridge the two worlds with open standards and evidence that different parties can actually rely on together.
Of course, I’m not naive about this. Beautiful attestations on their own don’t create real trust. Institutions still have to agree on who the trusted issuers are, how governance and revocation actually work, who’s legally responsible, and whether the incentives line up. At national scale, those questions get even thornier politics, different laws, and clashing interests don’t magically disappear because the code is clean.
Even with those risks, Sign feels refreshing to me. It seems to get that the real fight in digital identity isn’t about who has the coolest diagrams. It’s about building verification that lasts long enough for trust to stop being a fragile, one-off assumption and start feeling more like actual shared infrastructure.
That’s a much harder, and honestly more honest, problem to chase.
Curious if anyone here has dug deeper into their evidence and attestation system or seen it working in the real world yet?
@SignOfficial #SignDigitalSovereignInfra
