They navigate warehouses.
They assist in delivery networks.
With this growth the question of trust rises.
How does a system know that a robot is genuine.
How does a system ensure that a robot follows a policy.
Mira addresses these questions.
They can be stolen during transmission.
A robot that shows a certificate can be impersonated if the certificate is copied.
Zero knowledge proofs offer a different path.
They allow one party to prove a statement without revealing the underlying data.
The prover can demonstrate possession of a secret without sending the secret.
This property matches the privacy needs of robot identity.
It supports private channels.
It enables confidential transactions.
It runs smart contracts called chaincode.
These chaincode modules can enforce business rules for robots.
Mira uses zero knowledge proofs inside Fabric chaincode.
When a robot joins the network it creates a cryptographic credential.
The robot then generates a proof that it knows the secret tied to that credential.
It submits the proof to the chaincode.
The chaincode validates the proof using the verification algorithm.
If the proof checks out the chaincode records the robot as authenticated.
No secret is ever stored on the ledger.
No secret is ever exposed to network peers.
Step one involves robot registration.
The robot contacts a trusted registrar.
The registrar issues a secret key pair.
The robot keeps the private key.
The public part is recorded on the ledger.
Step two is proof generation.
The robot uses the private key to create a zero knowledge proof of identity.
The proof is small and can be sent over low bandwidth links.
Step three is proof submission.
The robot sends the proof to a Fabric peer.
The peer invokes the identity chaincode with the proof.
Step four is verification inside chaincode.
The chaincode runs the mathematical verification.
If it succeeds the transaction is committed.
The robot is now recognized as a valid participant.
Step five is credential usage.
The robot can sign subsequent transactions with the same credential.
The network can verify each transaction without learning the secret.
The approach gives strong privacy.
Observers cannot learn the robot’s private key.
The ledger never stores raw credentials.
The system remains auditable because each proof verification is recorded.
The architecture is scalable.
Proof verification is computationally light compared to full encryption.
The solution is interoperable.
Any robot that can run the zero knowledge algorithm can join the network.
Mira can support heterogeneous robot platforms from drones to arm robots.
In a warehouse the fleet of autonomous vehicles can pick items.
Each vehicle proves its identity before receiving a pick order.
The manager can trust the vehicle without exposing its internal software.
In a manufacturing line robotic arms can exchange parts.
Each arm proves it is certified to handle a specific component.
The proof prevents a rogue arm from inserting faulty pieces.
In a delivery network drones can claim they have completed a route.
The proof assures the dispatcher that the mission was executed without revealing the exact flight path.
Generating zero knowledge proofs requires extra computation.
Resource constrained robots may need hardware acceleration.
The size of proofs can affect communication latency.
Chaincode execution must be optimized to handle many concurrent proofs.
Consensus in Fabric adds a delay that must be accounted for i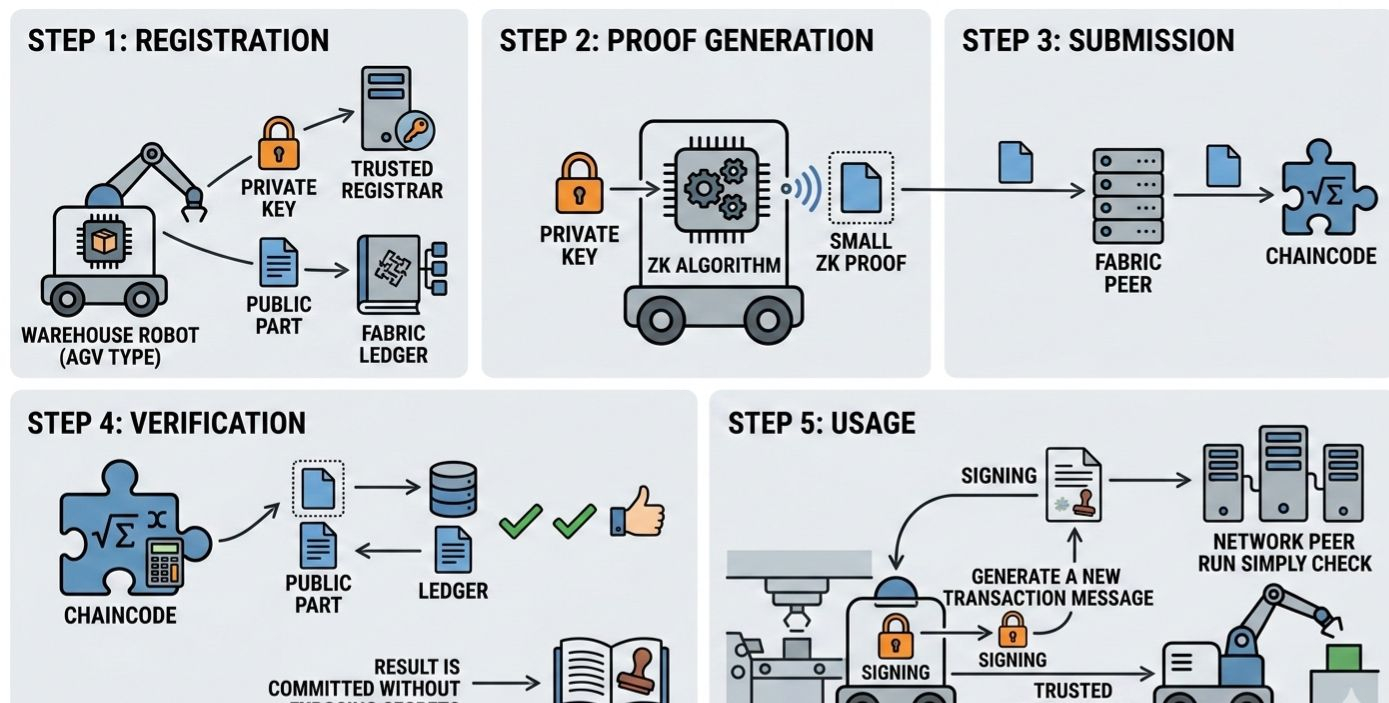 n real time applications.
n real time applications.
Managing secret key rotation is another concern.
Mira includes mechanisms to update keys without breaking existing proofs.
The next phase of Mira focuses on proof size reduction.
Researchers are exploring succinct proof systems that shrink the data payload.
The team is also integrating edge cryptographic modules to speed up proof creation.
Another goal is to enable cross network verification.
Robots could prove identity on Fabric and later on another blockchain without re registering.
Finally the project plans to open an SDK for developers.
The SDK will abstract the cryptographic details and let engineers focus on robot behavior.
Mira shows how zero knowledge proofs can protect robot identity.
It shows how Fabric can host privacy preserving authentication.
The combination creates a trust fabric for autonomous systems.
As robots become more prevalent the need for secure identity will grow.
Solutions like Mira will be essential to keep networks safe and efficient.