There is a subtle cost in crypto markets that I sometimes call informational drag. It’s the friction that appears when a system claims decentralization but quietly centralizes the most important resource: data visibility. Traders may hold their own keys, validators may run across continents, and blocks may propagate quickly. Yet if the meaningful information about positions, identities, and execution paths is concentrated in a few observable datasets, the network begins to behave less like a decentralized market and more like a transparent surveillance grid. When I look at Midnight Network and its native asset NIGHT, what stands out to me is the attempt to reduce that informational drag through the application of Zero-knowledge proof systems. Not by hiding everything, but by letting verification exist without unnecessary exposure.
That distinction matters more than it might appear at first glance. Crypto markets are shaped as much by psychology as by code. A trader executing a leveraged position on a decentralized exchange is not simply interacting with a contract. They are interacting with a field of observers. Bots scanning liquidation thresholds, analysts mapping wallet clusters, arbitrageurs tracking cross-chain liquidity. Transparency, while philosophically appealing, often amplifies competitive asymmetry.
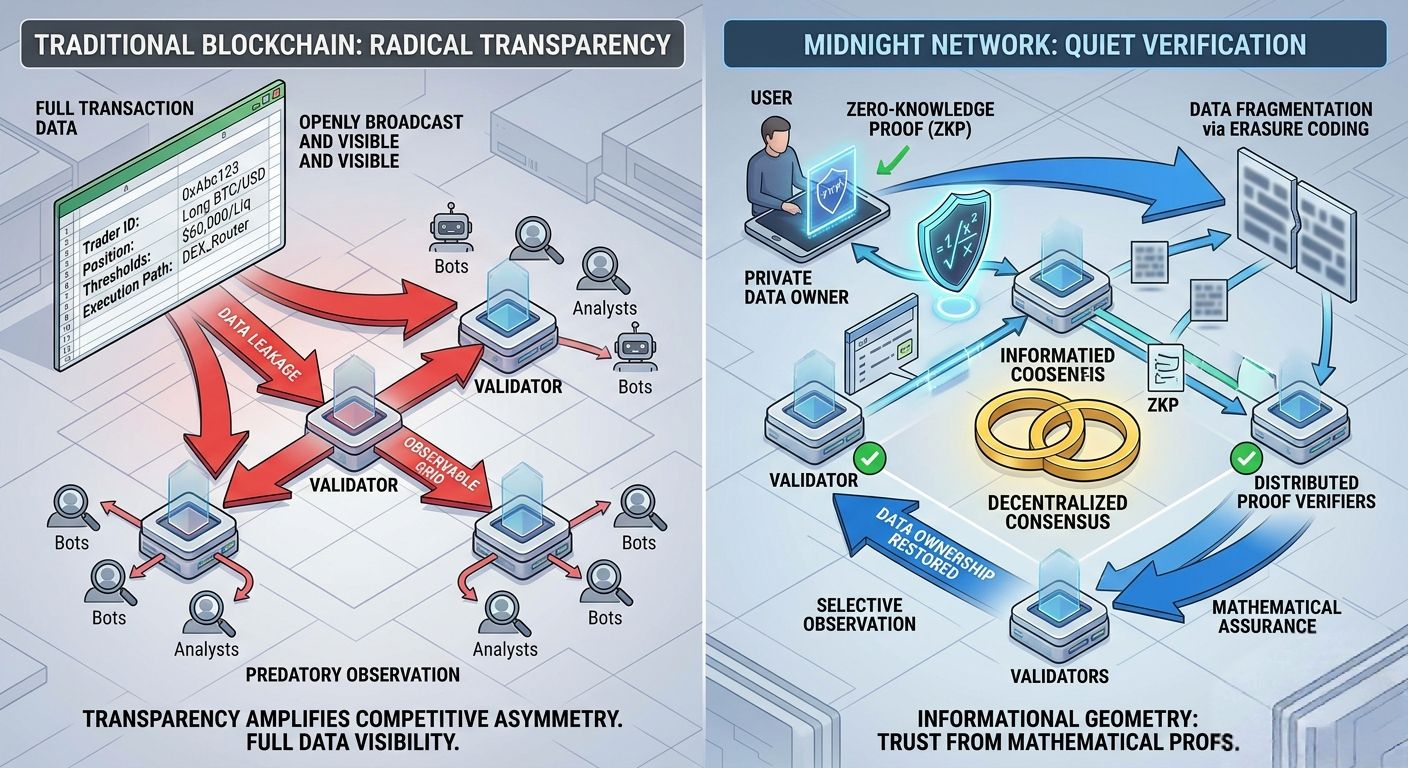
I’ve watched liquidation cascades unfold during volatile sessions where the sequence of events becomes almost mechanical. A large wallet’s collateral ratio becomes visible on-chain. Monitoring systems detect it within seconds. When the market price approaches that liquidation threshold, opportunistic actors begin to position themselves ahead of the event. The result is a kind of predictive predation. The liquidation was inevitable, perhaps, but the path toward it becomes accelerated by information exposure.
When I look at Midnight Network through that lens, I see an attempt to change the informational geometry of decentralized systems. The premise is deceptively simple: transactions and state transitions can be proven valid without revealing the underlying data that produced them. Instead of broadcasting every detail, the network broadcasts mathematical assurances that those details satisfy certain rules.
That shift changes the nature of trust.
In traditional blockchains, trust emerges from radical transparency. Every node observes everything. Every transaction becomes public knowledge. This approach is powerful, but it also creates a world where data ownership becomes ambiguous. Users technically control their assets, yet the behavioral data surrounding those assets becomes permanently exposed.
Midnight Network’s architecture tries to restore a sense of ownership at the informational level. Verification remains decentralized, but observation becomes selective.
When I think about the practical implications of this design, my mind goes immediately to execution realism. Markets are not abstract environments. They are systems full of timing sensitivities, delays, and friction points.
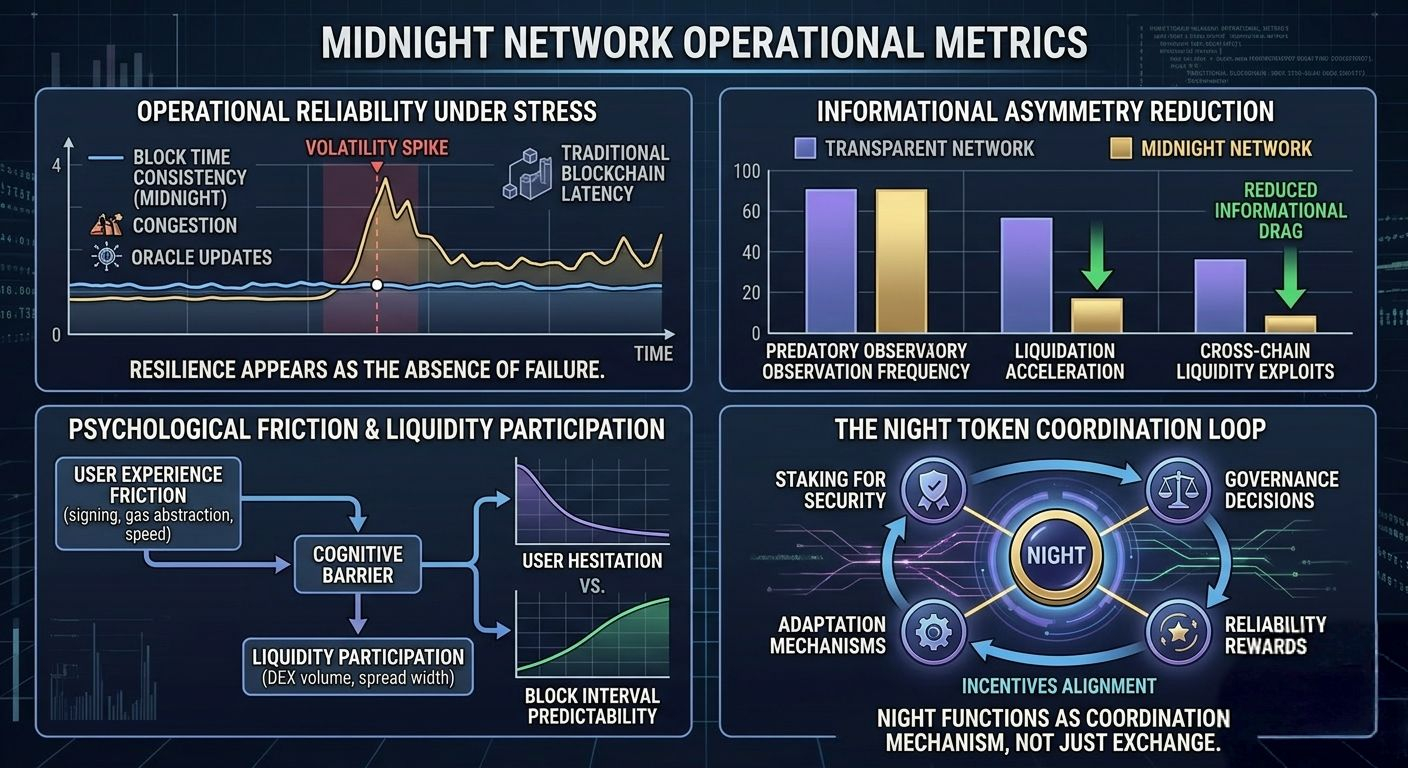
A small delay in an oracle update can trigger unintended liquidations. A congested block interval can cause orders to execute several seconds later than expected. These moments are not rare anomalies. They are everyday realities in decentralized markets.
I remember a trade during a sharp volatility spike where a lending protocol was still referencing an oracle price that lagged behind centralized exchange feeds by nearly fifteen seconds. The price had already dropped further on most trading venues, but the protocol hadn’t updated yet. Liquidation bots exploited the discrepancy immediately. Some users were liquidated not because their positions were fundamentally unsafe, but because the system’s information pipeline moved slower than the broader market.
That experience tends to stay with you.
So when evaluating a network like Midnight, the cryptographic elegance of zero-knowledge proofs is only one part of the picture. The other part is operational reliability. Proof systems introduce computational overhead. Generating and verifying them requires time and infrastructure. The network must ensure that this additional layer of privacy does not create new bottlenecks during moments when speed matters most.
From an infrastructure perspective, the architecture leans toward modularity. Execution environments can process transactions while the data necessary for verification is encoded and distributed in fragments across the network. Instead of forcing every validator to store complete datasets, the system can distribute encoded segments through techniques similar to erasure coding. Enough fragments allow reconstruction and verification, while incomplete fragments reveal little about the original data.
This approach addresses two persistent pressures in blockchain systems: storage expansion and privacy leakage.
As networks mature, the volume of historical data grows continuously. Full replication becomes increasingly burdensome for nodes with limited resources. Fragmented storage models allow networks to maintain availability without requiring every participant to carry the entire historical burden.
At the same time, fragmentation protects sensitive information by preventing any single node from reconstructing the entire dataset. Privacy emerges not only from cryptographic proofs but also from how data itself is physically distributed across the network.
But infrastructure choices always come with trade-offs.
Parallel execution environments can increase throughput and efficiency, yet they introduce complexity in transaction ordering and state synchronization. Validator topology also shapes performance in subtle ways. A geographically concentrated validator set can produce faster communication but increases correlated failure risk. A globally distributed validator network improves resilience but introduces propagation latency.
These decisions are rarely visible to everyday users, yet they shape their experience indirectly. Block time consistency becomes more important than peak performance claims. A trader interacting with a decentralized exchange cares less about theoretical capacity than about whether confirmations arrive predictably.
Psychology follows infrastructure.
If confirmations vary unpredictably between two seconds and thirty seconds, users hesitate. Liquidity providers widen spreads. Arbitrage opportunities become harder to capture. The network may remain technically functional, but the market environment becomes less efficient.
User experience also plays a surprisingly large role in shaping participant behavior. Signing transactions, managing gas fees, and interacting with wallets are small mechanical actions that accumulate into psychological friction. When systems introduce gas abstraction or simplified signing flows, they are not merely improving convenience. They are lowering the cognitive barrier between intention and execution.
That reduction in friction influences liquidity participation. It encourages experimentation. It makes decentralized applications feel less like specialized tools and more like everyday infrastructure.
Yet privacy layers must integrate smoothly with these experiences. If proof generation delays become noticeable or if transaction confirmation becomes unpredictable under load, users will quietly migrate elsewhere. Markets reward reliability above ideology.
This brings us to incentives.
The NIGHT token functions as a coordination mechanism within Midnight Network rather than simply a medium of exchange. Validators stake it to secure the network. Participants rely on it for governance decisions that adjust parameters as the system evolves. Developers build applications that integrate the token into operational feedback loops.
What matters here is alignment. Incentives must reward honest participation while discouraging behavior that undermines the system’s informational integrity. Staking rewards, governance influence, and network participation all become part of a long feedback cycle that determines whether the network remains decentralized in practice rather than only in theory.
Governance, in this sense, resembles adaptation more than authority. Distributed systems inevitably encounter unexpected conditions. Fee models may require adjustment. Validator incentives may need recalibration. Privacy parameters might evolve as new cryptographic techniques emerge.
A resilient network treats governance as a mechanism for gradual correction rather than centralized control.
Liquidity and oracle systems add another dimension to the picture. Blockchains do not exist in isolation. Prices originate from external markets. Assets move across bridges connecting multiple networks. Liquidity providers arbitrage differences between ecosystems.
Each connection introduces structural assumptions.
Oracles must deliver accurate price data quickly enough to prevent manipulation yet cautiously enough to avoid false signals. Bridges must secure large pools of assets while maintaining efficient withdrawal mechanisms. Liquidity flows must remain deep enough to absorb large trades without destabilizing prices.
If any of these components fails, the consequences propagate through the system.
Imagine a period of market stress. A sudden macroeconomic shock pushes crypto markets into rapid decline. Trading volumes surge across exchanges. Oracles begin updating more frequently to track price volatility. Meanwhile, users rush to move assets across chains, creating congestion in bridge systems.
In such a scenario, the structural question becomes simple. Does the network maintain composure?
Proof generation pipelines must continue verifying transactions without introducing excessive delays. Validators must remain synchronized despite increased data throughput. Transaction queues must grow gradually rather than collapsing under sudden demand.
Designing for these moments requires acknowledging that failure conditions are not rare events. They are predictable phases in the life cycle of financial networks.
This is where Midnight Network’s focus on informational verification rather than raw transparency becomes interesting. By reducing the exposure of sensitive transaction details, the system potentially reshapes how adversarial actors exploit market stress. Without immediate access to full position data, opportunistic liquidation strategies may become less predictable.
Of course, obscuring information can also complicate risk analysis. Market participants often rely on transparent data to assess systemic exposure. Striking the balance between privacy and observability remains one of the most delicate design challenges in decentralized finance.
When I compare Midnight Network with other high-performance blockchains, the difference feels philosophical rather than purely technical. Many networks emphasize raw execution metrics and ecosystem expansion. Midnight appears more concerned with the structure of verification itself.
It asks a quieter question.
Can decentralized systems maintain trust without requiring total transparency?
If the answer is yes, the implications extend beyond trading environments. Identity systems, enterprise data coordination, and privacy-sensitive applications could all benefit from networks capable of verifying outcomes without exposing the data that produced them.
But ideas alone are never enough in crypto infrastructure. Systems earn credibility through sustained operation under real market conditions.
The real structural test for Midnight Network will not arrive during calm periods of moderate usage. It will arrive during moments of stress. Congestion spikes, oracle delays, cross-chain liquidity surges. Those chaotic windows reveal whether a network’s design choices translate into resilience.
And resilience is quiet.
It does not produce headlines or dramatic narratives. It appears instead as the absence of failure. Blocks continue arriving on schedule. Transactions confirm within predictable intervals. Validators maintain consensus without visible strain.
Infrastructure, when functioning properly, becomes almost invisible.
That invisibility is the paradox of well-designed systems. The more reliable they become, the less attention they receive. Yet within that quiet stability lies the true measure of decentralization.
For Midnight Network, the question is not whether privacy technology works. The mathematics behind zero-knowledge proofs has already proven itself. The deeper question is whether a privacy-preserving architecture can operate at the scale and unpredictability of global markets without drifting back toward centralized informational control.
In other words, can the network preserve both verification and ownership of data as participation grows?
If it can, the system may quietly redefine what decentralization actually means. Not just distributed consensus, but distributed knowledge.
@MidnightNetwork #night $NIGHT
