When I first came across the phrase “verifiable compute,” my reaction was honestly relief.
At last. Evidence instead of claims. A system that can actually demonstrate how the work was done.
Then the obvious question showed up and immediately spoiled that feeling.
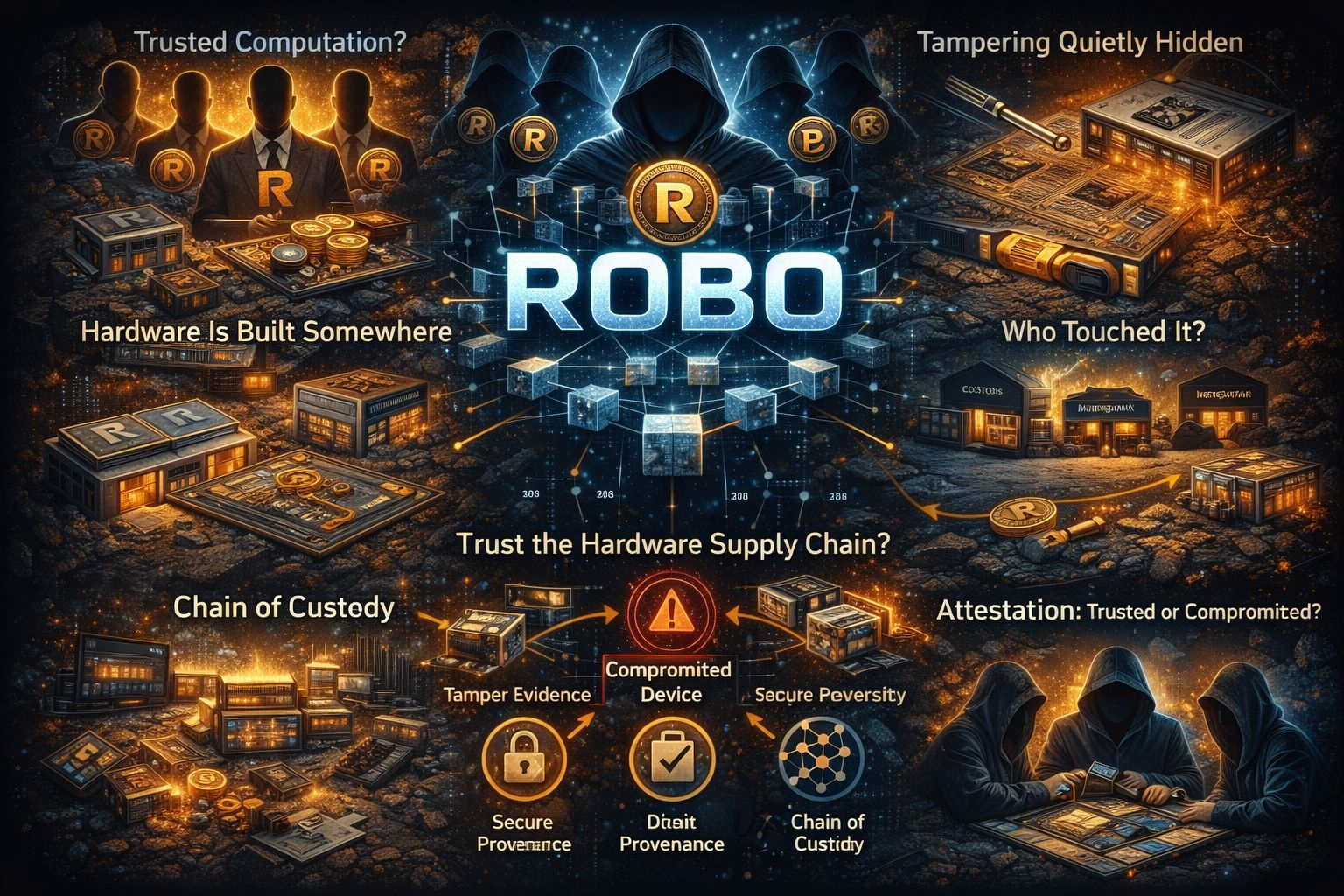
Verifiable… but based on which hardware?
Because if Fabric Foundation depends on VPUs and attestation, the foundation of trust doesn’t really begin on-chain. It begins inside a factory. It begins inside a shipping package. It begins with whoever had physical access for a few minutes and the right tools.
This is the part people tend to gloss over because it sounds like dull operational detail.
That’s amusing. Operations are exactly where real security lives.
Attestation is only as reliable as the root it depends on. If the device itself is compromised, the proofs don’t simply become “a bit unreliable.” They become confidently incorrect. The worst kind of failure. The kind that still looks perfect in the logs and passes every check while something broken sits underneath.
So the real issue isn’t “can Fabric verify computation.”
The real issue is: can Fabric trust where the verifier actually comes from?
Who built the unit? Where was it put together? Who had access to the attestation keys? Were those keys created safely? Were they ever duplicated? Was the firmware installed in a controlled environment or somewhere improvised? Did the device ship straight to its destination, or did it sit in a warehouse where supposedly “no one touched it”?
And during the journey to the customer, how many people handled it?
Hardware passes through a lot of hands. Distributors. Integrators. Contractors. Repair centers. Customs officers. Storage facilities. Any one of those points creates an opening. Not necessarily for some brilliant attacker either. Sometimes all it takes is someone with enough time and opportunity.
A compromised device doesn’t have to break in an obvious way. It only has to deliver convincing lies.
That’s why the question “who verifies the verifier?” isn’t some abstract idea. It’s the core of the whole trust model.
If Fabric wants VPUs to function as real infrastructure, it has to tell a clear story about where they come from. There needs to be a provenance trail. A record of custody. Signs that tampering would be visible. And a plan for recovery when something inevitably breaks, because at some point it will.
Provenance means you can follow the origin of a unit and confirm what it actually is. Not through marketing language, but through things that can be checked. Manufacturing logs. Signed certifications. A hardware identity that can’t simply be issued again without scrutiny.
Chain of custody means there’s a record of who handled the device and at what time. Not because everyone behaves perfectly. Because people are people. Incentives exist. Errors happen. So the system has to make the phrase “we have no idea what happened” both rare and costly.
Tamper evidence means there’s a clear distinction between a device that’s clean and one that raises questions. Secure components. Physical seals. Recorded measurements. Remote attestation capable of spotting unexpected changes in state. The objective isn’t to make tampering impossible. The objective is to make it visible enough that the network can isolate the device before it starts acting like a trusted source of false information.
Then there’s certification.
Who actually decides that an attestation key is valid? If a single vendor controls approvals behind closed doors, it may speed up adoption but it slows down decentralization. On the other hand, a completely permissionless attestation registry basically invites counterfeit devices and clone factories.
Which brings everything right back to that awkward middle ground.
Some form of registry. Some kind of onboarding process. Some type of trust anchor. And then the question of who actually controls it.
This is where many “verifiable” projects quietly collapse. Not because the cryptography fails. Because the real world refuses to stay neat. Hardware carries momentum. Supply chains drift out of control. And the simplest way to break a proof system is to compromise the device that generates the proofs.
If Fabric Foundation manages to solve this, it probably won’t look impressive. It’ll look like dull standards. Audits. Manufacturing partners. Revocation lists. Key rotation policies. Quarantine procedures. A system that can say “this unit is trusted,” and also say “this unit is no longer trusted,” without bringing the entire network down.
That’s what real infrastructure looks like.
Because in the end, verifiable compute isn’t only a software challenge.
It’s a logistics challenge dressed up in cryptography.
@Fabric Foundation #ROBO $ROBO
